Twitter private tweets bug and Cisco phone router vulnerabilities
Twitter admits security bug disclosed private Circle tweets, Cisco warns of a critical flaw in phone adapters and the Android FluHorse malware. Catch all this and more in this week’s edition of Cybersecurity Weekly.
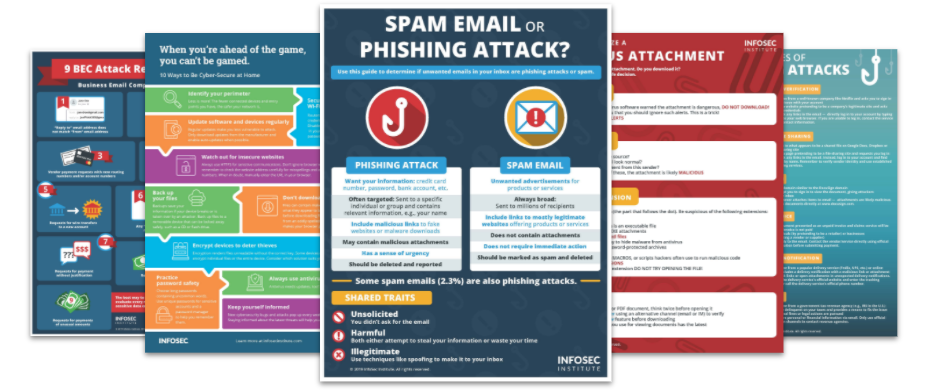
Top Security Awareness Posters
1. Twitter says a bug caused private Circle tweets to become public
In a recent disclosure, Twitter revealed a security incident that caused private tweets sent to Twitter Circles to be displayed publicly to non-Circle users. Twitter Circles is a privacy feature that allows users to send tweets to a select group of people while keeping them private from the public. The incident occurred in April 2023 and affected several users. Twitter has notified impacted users and has stated that their security team immediately fixed the issue. The social media company did not provide further details about the incident.
2. Cisco confirms the presence of a severe vulnerability in specific phone adapters
Cisco has warned of a severe security flaw in its SPA112 2-Port phone adapters that could allow remote hackers to execute arbitrary code on vulnerable devices. The flaw is rated 9.8 out of 10 on the CVSS scoring system and is caused by a missing authentication process within the firmware upgrade function. Cisco has no plans to issue a fix due to end-of-life status but recommends migration to a Cisco ATA 190 Series Analog Telephone Adapter. The company has reported no evidence of the flaw being exploited maliciously.
3. New Android FluHorse malware steals 2FA codes, passwords and more
Check Point Research has discovered a new malware called FluHorse, which targets Android devices in Eastern Asia. The malware is spread via email and steals sensitive data like credit card information, passwords, and 2FA codes. Victims receive links to fake versions of legitimate apps, including a Taiwanese toll-collection app and a Vietnamese banking app. As soon as they install any of these apps, the malware requests SMS access to steal 2FA codes. The malware then copies the user's information, including credit card data. Check Point warns that this is an ongoing threat and users should be cautious about sharing personal information online.
4. Ransomware gang hijacks university’s emergency alert system, issues threats
Bluefield University, a private university in Virginia, was recently targeted by the Avos ransomware gang. The group hijacked the university's emergency broadcast system, RamAlert, to inform students and staff that their data had been stolen and would be released if the university did not pay a ransom demand. The gang also threatened to leak thousands of students' personal data on a dark web blog. Bluefield University claimed there was no evidence of financial fraud or identity theft but admitted their emergency alert system had been hacked. The use of the alert system is a novel extortion method by ransomware groups.
5. Cybercriminals using double DLL sideloading to prevent detection
Sophos’ researchers have spotted APT hacking group Dragon Breath using complex variations of the classic DLL sideloading technique to bypass detection. The new attack vector utilizes applications like WhatsApp and Telegram to sideload second-stage payload and then sideload a malicious malware loader DDL. The campaign targets Chinese Windows users in Japan, China, Taiwan and other Asian countries. Using “double DLL sideloading” techniques, the APT group can evade detection and obfuscate their attacks, making it challenging for defenders to adapt to their attack patterns and secure their networks effectively.
Phishing simulations & training
![]()





