The real dangers of vulnerable IoT devices
The landscape of the Internet of Things (IoT) devices has been explored strongly by criminals in the last few years, causing enormous constraints for home users and companies from the cybersecurity perspective.
Criminals are abusing these kinds of devices to attack, but there are ways to protect assets against attacks of this nature.
IoT threats
The damage caused by flaws in IoT devices is tremendous as criminals take advantage of weakness to get access and take control of the devices many times available on the internal network face. These vulnerabilities are a foothold to bypass internal firewalls, gain access to private networks and steal sensitive and critical information as it travels across connected device environments. In terms of risk, criminals compromised devices and are able to spread malicious payloads or pivot to other networks, maintaining persistence for a large period of time the detection and monitorization of anomalous activity on these devices are still seen as a big challenge.
The big challenge
The set of IoT vulnerabilities are grouped in several sectors from lack of device management to critical flaws on hardware or software. For instance, in this article, it’s possible to learn about a vulnerability tracked as CVE-2021-31251, a flaw on the telnet protocol, which can be exploited to get a remote privileged session. In detail, an overflow can be abused to take control of the IoT device and as a result, used as an initial entry point to access the internal networks.
In sum, smart devices are vulnerable due to the lack of the necessary built-in security to face emerging threats. Some of the reasons why IoT devices remain vulnerable are:
- Limited computational resources and hardware limitations:the devices have a limited set of resources due to their nature and don’t guarantee security mechanisms to fight external threats as well as data protection routines to avoid data compromising.
- The usage of different technology: these devices use different technology; a point that makes difficult the creation of standard protection methods and protocols.
- Vulnerable components:many components used in these little devices are vulnerable and are affecting millions of deployed devices.
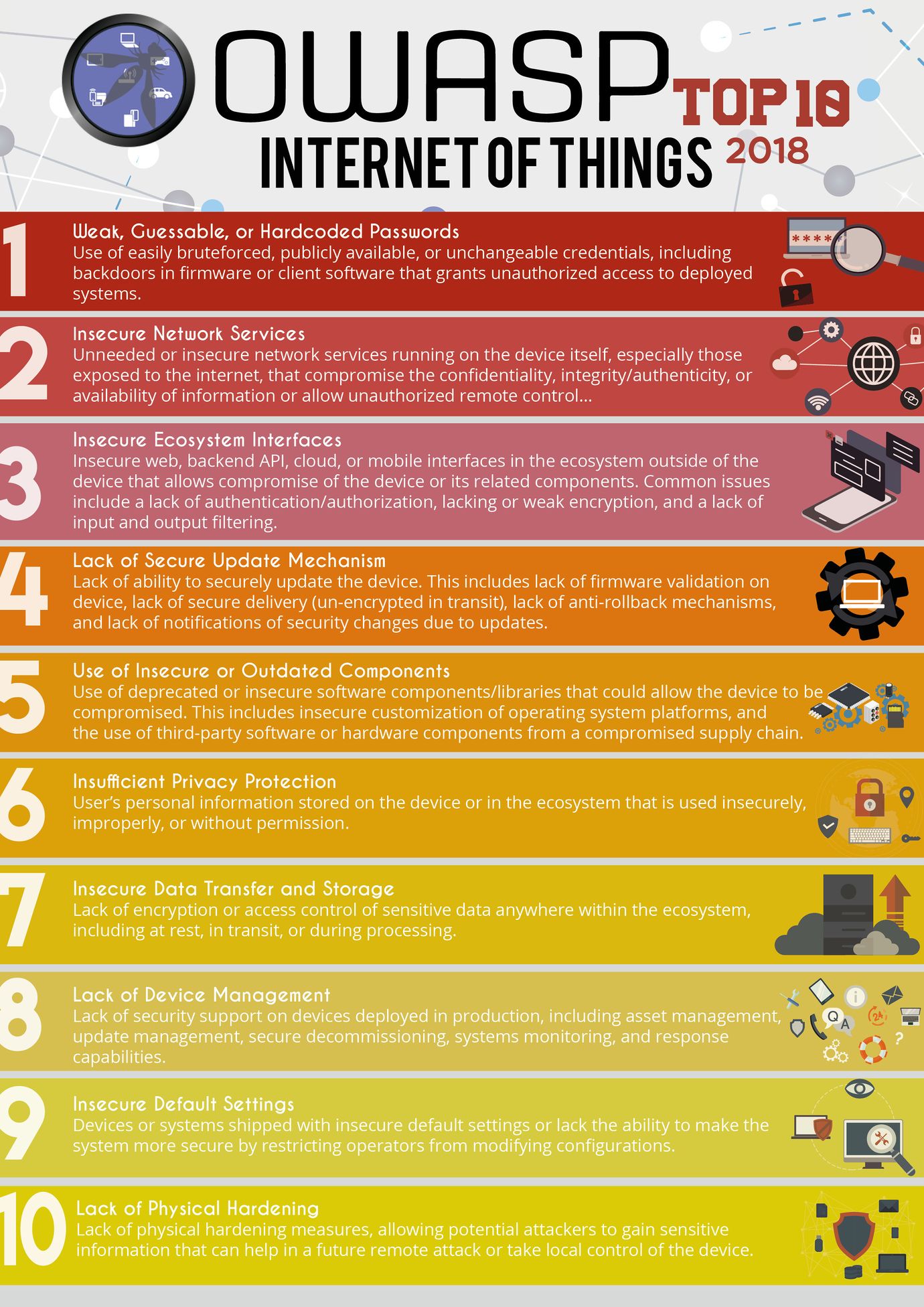
Nowadays, attackers are using IoT vulnerabilities to penetrate or establish an initial foothold for their massive attacks, which reinforces the importance of security by design methodology. In this sense, below we are going to describe some important vulnerabilities present in the IoT field. The image below presents the TOP 10 IoT devices provided by OWASP.
There is no perfect way to avoid vulnerabilities, as part of IoT devices are vulnerable to a wide range of flaws due to the limited computational abilities and hardware limitations. The most important vulnerabilities impacting IoT devices are described below.
Lack of a secure update mechanism
“Lack of ability to securely update the device. This includes lack of firmware validation on the device, lack of secure delivery (un-encrypted in transit), lack of anti-rollback mechanisms and lack of notifications of security changes due to updates.”
From this point, it’s necessary to create an efficient and secure update mechanism. For instance, sensors or smart devices should be equipped with timely updates and using SSL protocol everywhere.
Lack of device management
“Lack of security support on devices deployed in production, including asset management, update management, secure decommissioning, systems monitoring and response capabilities.”
One of the most challenging tasks to minimize risks is managing all of the devices and closing the perimeter. Scanning and profiling devices allow security teams to gain visibility of their IoT devices on the networks, considering, thus, their risks, behavior, activity and so on.
Insecure data transfer and storage
“Lack of encryption or access control of sensitive data anywhere within the ecosystem, including at rest, in transit or during processing.”
Network and communication layers have a crucial role in IoT devices as they are the bridge between different parts, facilitating the sharing of information and real-time interaction with the devices.
A clear example to enforce this problem is, for instance, the usage of a CA responsible for certifying and validating the communication chain. On the other hand, data tokenization should be considered as a way of protecting sensitive data that only authorized devices can access.
Weak, guessable or default passwords
“Use of easily brute-forced, publicly available, or unchangeable credentials, including backdoors in firmware or client software that grants unauthorized access to deployed systems.”
A popular flaw in the IoT landscape is the weak and default passwords. In this sense, poor management of these kinds of devices opens the doors to potential attack vectors such as brute force.
Insecure network services
“Unnecessary or unsafe network services that run on the devices, particularly those that are exposed to the internet, jeopardize the availability of confidentiality, integrity/authenticity of the information and open the risk of unauthorized remote control of IoT devices.”
IoT devices are part today of the internal network infrastructure, and they can communicate with a large group of smart devices, such as smoke alarms, proximity sensors, or optical devices. In that way, unneeded open ports and services which transmit information on their networks should be inspected and consider removing or disabling as a security measure (if not necessary).
Insufficient privacy protection
“User’s personal information stored on the device or in the ecosystem that is used insecurely, improperly or without permission.”
In many cases, the user’s data is stored directly on the devices or even sent to Cloud services managed by the provider. In this case, the provider must be responsible for ensuring the best security practices and ensure that all the parties delete the users’ data when requested.
Assessing the impact of IoT
The impact of vulnerabilities in the IoT landscape affects indirectly the security of the internet. In this way, it’s necessary to guarantee these devices are secure by design and shared responsibility with stakeholders and all the interesting parts. For instance, manufacturers need to address known vulnerabilities, release patches for the existing flaws and report the end of life and support for older products.
As a general security measure, it’s strongly recommended to protect network access to devices with appropriate mechanisms. Moreover, isolating IoT devices from other critical assets in the network makes it difficult to explore and increases the criminal’s tasks in case of illegitimate access by exploring weaknesses on those smart devices.
Let’s take IoT security seriously because this field has been used massively by criminals in this decade to gain access to internal networks.
Sources
- IoT Top 10 vulnerabilities, OWASP
- Security challenges of IoT devices, ISSSource
- IoT - The most important vulnerabilities, KeyFactor
- Dancing in the IoT, Segurança-Informática




