The Nightmare of Car Hacking
In the recent weeks, the discussion about car hacking is becoming even more popular. Newspapers and TV shows every day propose transmissions and articles related to the possible hack of cars and its components.
In this post, I wrap up the latest news about car hacking discussing the possible attack scenarios, possible risks and mitigation strategies.

What should you learn next?
In the beginning it was the hack to Jeep made by Fiat Chrysler
As detailed in my previous post on the car hacking, Charlie Miller and Chris Valasek demonstrated how to hack a car by accessing its internal network. They presented the findings of their tests to the security community anticipating further studies to sensitize the automotive industry on the possible risks related to a cyber-attack.
Modern cars are complex systems composed of sophisticated components that exchange a huge quantity of information; hackers can manipulate them in order to gain the control of a vehicle.
Miller and Chris Valasek, in order to demonstrate the feasibility of a cyber-attack on a connected car, exploited weaknesses in an automobile system with cellular connectivity to hack the vehicle. The experts hacked the Uconnect automobile system, which is installed in many connected cars, including nearly 471,000 vehicles in the US. Charlie Miller and Chris Valasek demonstrated the attack by hacking a Jeep Cherokee equipped with the Uconnect system.
The duo asked the popular journalist Andy Greenberg to drive a Jeep while they were attempting to hack it remotely.
"To better simulate the experience of driving a vehicle while it's being hijacked by an invisible, virtual force, Miller and Valasek refused to tell me ahead of time what kinds of attacks they planned to launch from Miller's laptop in his house 10 miles west. Instead, they merely assured me that they wouldn't do anything life-threatening. Then they told me to drive the Jeep onto the highway. 'Remember, Andy,' Miller had said through my iPhone's speaker just before I pulled onto the Interstate 64 on-ramp, 'no matter what happens, don't panic.'" wrote Greenberg.
The Uconnect is the connected car system chosen by Fiat Chrysler for its vehicles in the US market. This system allows the owners of the connected cars to interact with the vehicle remotely; it uses the Sprint cellular network to remain connected to the Internet. Car owners control their vehicle by using their Smartphone, a mobile application allows them to remote start the engine, retrieve the location of the vehicle, and activate the anti-theft features.
Charlie Miller and Chris Valasek have exploited vulnerabilities in the connected car system in the Fiat Chrysler model that could allow hackers to scan Sprint's cellular network for Uconnect-equipped vehicles to obtain car identification information and its location.
The two researchers used these data to attack the connected car system, by knowing the IP address assigned to the car they were able to turn the engine of the car off, activate and de-activate the brakes, take remote control of the vehicle's information display and entertainment system, and activate the windshield wipers.
The experts were able to control various components of the a 2014 Jeep Cherokee, including the steering, braking, the engine, the car signals, windshield wipers and fluid, and door locks, as well as reset the speedometer and tachometer and the control of the transmission.

Figure 1 - Experts Miller and Valasek hacked a Fiat Chrysler Jeep
Miller and Valasek also discovered that they could remotely control the steering of the Jeep Cherokee.
"As the two hackers remotely toyed with the air-conditioning, radio, and windshield wipers, I mentally congratulated myself on my courage under pressure. That is when they cut the transmission. Immediately my accelerator stopped working. As I frantically pressed the pedal and watched the RPMs climb, the Jeep lost half its speed, then slowed to a crawl. This occurred just as I reached a long overpass, with no shoulder to offer an escape. The experiment had ceased to be fun. " continues Greenberg.
The hack has shocked the automotive industry and public opinion. For the first time, researchers demonstrated that hackers could exploit the flaws (now patched) in the Uconnect connected car system to control any vehicle from practically everywhere.
On July 16, Fiat Chrysler informed its customers of the vulnerability affecting its Jeep models by publishing a notice on its website.
A few days later, the Fiat Chrysler recalled 1.4 million vehicles in the US possibly open to cyber-attacks due to the presence of a vulnerability in the UConnect infotainment system.
Fiat Chrysler recalled 1.4 million vehicles, including:
- 2013-2015 MY Dodge Viper specialty vehicles
- 2013-2015 Ram 1500, 2500 and 3500 pickups
- 2013-2015 Ram 3500, 4500, 5500 Chassis Cabs
- 2014-2015 Jeep Grand Cherokee and Cherokee SUVs
- 2014-2015 Dodge Durango SUVs
- 2015 MY Chrysler 200, Chrysler 300 and Dodge Charger sedans
- 2015 Dodge Challenger sports coupes
"You can develop that most advanced vehicle that has all of the latest safety features and high tech gadgets in it, but if it can be bricked by remote exploits, you are going to have wary consumers who may choose the next brand of vehicle because they put more emphasis on security," says Ken Westin, senior security analyst for Tripwire. "The automotive industry understands the importance of security and they are not only working with researchers, but also each other to help develop standards and best practices for more secure vehicles and the work that researchers are doing like Miller and Valasek is actually helping to make our vehicles more secure in the future."
The company initially invited customers to download and install the update themselves from a USB drive or take the car to a dealership.
Not sure that this is an operation that any customer is able to do autonomously.
Fortunately, the FCA later announced that it is conducting a voluntary safety recall to update software in roughly 1.4 million vehicles in the United States.
"The recall aligns with an ongoing software distribution that insulates connected vehicles from remote manipulation, which, if unauthorized, constitutes criminal action," FCA said. "Further, FCA US has applied network-level security measures to prevent the type of remote manipulation demonstrated in a recent media report. These measures – which required no customer or dealer actions – block remote access to certain vehicle systems and were fully tested and implemented within the cellular network on July 23, 2015."
New hacks, old and well-known problems
Despite this, Car hacking has reached a peak of popularity due to the recent hack of the Fiat Chrysler Jeep, groups of experts are working on the matter for a long time.
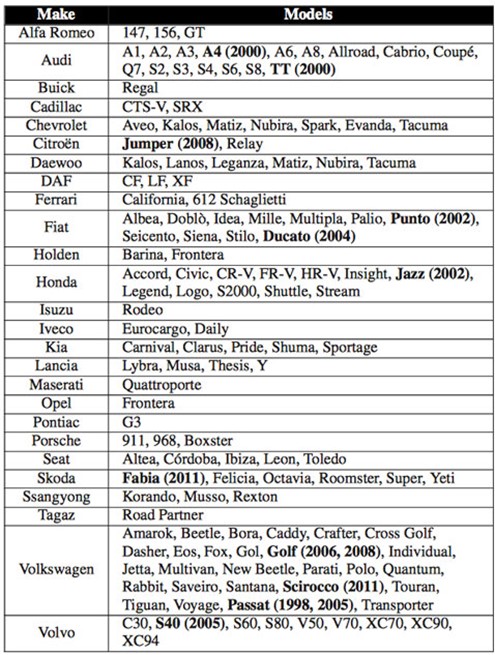
Recently, a duo of European experts revealed the presence of security flaws in the Megamos Crypto transponder used in more than 100 cars manufactured by principal automakers.
Models of popular brands, including Audi, Ferrari, Fiat, Cadillac, and Volkswagen adopt the flawed transponder. Hackers can exploit the flaws to start the cars without needing to use the key.
The surprising news is that the same couple of researchers tried to present their findings at the 22nd USENIX Security Symposium in 2013, but they were prevented from doing so by Volkswagen, who won an injunction by the UK High Court of Justice prohibiting them from publishing key findings of their discovery.
The experts reverse-engineered the firmware of the transponder analyzing the security mechanisms it implements. The researchers elaborated three different attacks against the transponder that they described with the following statements:
"Our first attack consists of a cryptanalysis of the cipher and the authentication protocol. Our second and third attack not only look at the cipher but also at the way in which it is implemented and poorly configured by the automotive industry." reads the paper.
"Our second attack exploits a weakness in the key-update mechanism of the transponder. This attack recovers the secret key after 3 × 216 authentication attempts with the transponder and negligible computational complexity. We have executed this attack in practice on several vehicles. We were able to recover the key and start the engine with a transponder emulating device. Executing this attack from beginning to end takes only 30 minutes.
"Our third attack exploits the fact that some car manufacturers set weak cryptographic keys in their vehicles. We propose a time-memory trade-off which recovers such a weak key after a few minutes of computation on a standard laptop.""
The experts explained that their first attack, which works with all vehicles using Megamos Crypto, exploits the following weaknesses:
- The transponder lacks a pseudo-random number generator, which makes the authentication protocol vulnerable to replay attacks.
- The internal state of the cipher consists of only 56 bits, which is much smaller than the 96-bit secret key.
- The cipher state successor function can be inverted, given an internal state and the corresponding bit of cipher-text it is possible to compute the predecessor state.
- The last steps of the authentication protocol provides and adversary with 15-bits of known plaintext.
In one attack scenario, the experts have been able to recover the key in just 30 minutes and start the engine with a transponder-emulating device.
Another attack requests that the attacker have access to both the car and the transponder for a period of time; a circumstance that can occur when the attacker takes a car for rent or the victims parks the vehicle.
"It is also possible to foresee a setup with two perpetrators, one interacting with the car and one wirelessly pickpocketing the car key from the victims pocket," explained the researcher. "Our attacks require close range wireless communication with both the immobilizer unit and the transponder."
Figure 2 - Vulnerable car models
This year the experts had the opportunity to present their findings at the 24th USENIX Security Symposium.
"Although two years have passed, this work remains important and relevant to our community," Sam King, USENIX Security '13 Program Chair, and Casey Henderson, USENIX Executive Director, noted in the foreword added to the research paper.
Three years have been passed since the first discovery of the flaws made by the experts, but according to the news circulating in these days in the car hacking the security issues are still very actual in a number of components present in modern connected cars.
The experts highlighted once again the disk related the Internet of things devices that lack security by design. Researchers like this one must encourage the automotive industry to seriously considering the security as a mandatory requirement for the safety of car owners.
The OwnStart Attack
A few days ago, the popular hacker Samy Kamkar presented to the press a new gadget he designed to hack GM Cars. The tool is able to locate the vehicles, unlock, and start them.

Figure 3 - Samy Kamkar presented to the press a new hacking gadget, the Ownstar
Before introducing the Ownstar we need to know what the OnStar is (do not confuse the names), using the words of used by The Register website:
"OnStar is a cellular service that piggybacks AT&T's cellphone network to connect vehicles to the internet: equipment in the car connects to the 'net via the OnStar service, and sets up a Wi-Fi network inside the vehicle so people can browse Facebook on the move, or whatever. OnStar's RemoteLink mobile app is used to connect to the car remotely from a smartphone, and control the vehicle's systems." states The Register.
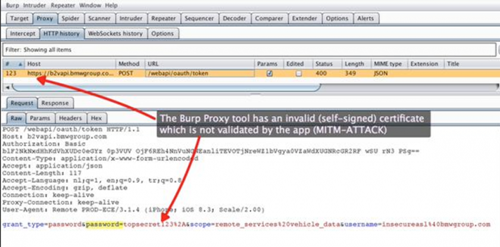
Ownstar is a hacking kit quite similar to a computer board; it is equipped with some antennas and some controller circuit boards. The wannabe thief needs to use it to launch a sort of Man-In-The-Middle Attack in range of someone using the OnStar app.
This Ownstar attack has the goal of intercepting communication and discovering the location of the car and the model. Basically, Kamkar has built a gadget, based on a Raspberry Pi, to intercept the traffic from nearby mobile devices running a specific app that could control some features of the vehicles.
"After a user opens the RemoteLink mobile app on their phone near my OwnStar device, OwnStar intercepts the communications and sends specially crafted packets to the mobile device to acquire additional credentials then notifies me, the attacker, about the vehicle that I indefinitely have access to, including its location, make, and model," Kamkar explained in a video PoC of the Ownstar attack.
When the car's owner leaves the perimeter, the attacker can use the intercepted info to disguise as the Onstar app, and unlock the car, start the engine by impersonating the legitimate owner.
"If I can intercept that communication, I can take full control and behave as the user indefinitely," says Kamkar.
"From then on I can geolocate your car, go up to it and unlock it, and use all the functionalities that the RemoteLink software offers. I suggest not opening the RemoteLink app up until an update has been provided from OnStar," he added.
The expert highlighted that even if the owner is inside the car and the engine is on, he cannot drive the vehicle because it requires the key.
"GM takes matters that affect our customers' safety and security very seriously. GM product cybersecurity representatives have reviewed the potential vulnerability recently identified," General Motors stated.
"In working with the researcher, we moved quickly to secure our back-office system and reduce risk. However, further action is necessary on the RemoteLink app itself. We take all cyber matters seriously, and an enhanced RemoteLink app will also be made available in app stores soon to fully mitigate the risk."
Let me suggest you to give a look to the presentation video of the Ownstar provided by Kamkar:
GM told to WIRED that it has now fixed the vulnerability that Kamkar's device exploited, with no action necessary for OnStar users.
While GM reassured its customers, other car models manufactured by other automakers, including BMW, Chrysler and Mercedes-Benz, result vulnerable to the Ownstar attack.
Kamkar discovered the apps BMW Remote, Mercedes-Benz embrace, and Chrysler Uconnect apps all are vulnerable to the Ownstar attack. In addition, in this case, the mobile apps fail to validate SSL certificates allowing the attacker to impersonate the legitimate owner once launched a Man in the Middle attack.
Kamkar will not be releasing the updated code for the OwnStar attack for at least 30 days to give time the automakers fix the security issue. Let us hope other automakers will carefully analyze their systems searching for similar flaws.
How to manage security flaws in the automotive industry
We cannot avoid the presence of software flaws in modern connected cars; however, it is important to properly managing their disclosure and the patch management process.
We will analyze together a few cases that demonstrate a different approach to the problem of different automakers.
Let us start with the Kamkar'Autostar attack. The expert reported the flaws he discovered to the principal automakers, but it seems that despite BMW was already aware of them for months before the researcher presented it to the press hasn't yet fixed it.
According to Han Sahin, co-founder Securify firm, he reported the vulnerability to the BMW on April 22, 2015. The BMW CISO confirmed receiving the bug report the next day, but Ownstar attack still works on My BMW Remote app for iOS.
Figure 4 - The Ownstar attack
"Securify has reported identical issues in the past to various organizations; ranging from small organizations to enterprises. Most organizations take these issues seriously and update their apps in a timely fashion. In our opinion, three months should be enough to resolve issues like this," Sahin told SecurityWeek.
"At the time of writing the BMW iOS app is still vulnerable to man in the middle attacks. We've informed BMW more than 120 days ago. We have yet to receive a formal response from BMW," the expert added. "We think BMW has had enough time to resolve this issue. Had they done so, they would not have been affected by the OwnStar attack."
BMW sent Wired an official comment on August 15, refusing the possibility an attacker could run MITM attack
BMW confirmed that its apps "conform to the same industry standards as other apps that use SSL-encrypted communication with a backend, such as online banking apps." The company also noted that "a man-in-the-middle attack on client-server communication can never be completely ruled out, but is virtually impossible to carry out and the probability of such a specific attack in everyday life is highly unlikely."
It is needless to hide our surprise when we learn this news. BMW is a company always attentive to the safety of its customers, but obviously, something went wrong in the management of loopholes exploited in the Ownstar attack.
Neither the lack of public disclosure of the flaw, nor a lack of prompt fix of the flaw surprises the security experts. Unfortunately, other cases that show a disputable management of the security flaws in the connected cars occurred in the recent months.
Let's examine, as an example, the case that we have described previously related to the discovery of a team or European experts that since 2012 is aware of the presence of security flaws in the Megamos Crypto transponder. The transponder is used in more than 100 cars manufactured by principal automakers, but the researchers were prevented from doing so by Volkswagen.
Fortunately, this year the experts had the opportunity to present their findings at the 24th USENIX Security Symposium.
Let me suggest that you read the report carefully. Despite the fact that three years have passed since the first discovery of the flaw, the security issues are still very common in a number of components present in modern connected cars.
Sometimes the things go better for the car owners and the security flaws in their connected cars are promptly fixed by the automakers, as happened in the case of Tesla Company.
Tesla Motors Inc. has recently announced that it had distributed a software update to fix security vulnerabilities in the Tesla Model S sedan. According to the company, an attacker by exploiting the flaw could take control of the Tesla vehicle.
The Financial Times reported on Thursday that a group of security researchers had taken control of a Tesla Model S and turned it off at low speed. Among the vulnerabilities discovered by the researchers, there is a flaw that could be exploited to control the vehicle as confirmed by the company.
"The hackers had to physically access the Tesla first, which made it more difficult than many other hacks. Once they were connected through an Ethernet cable, they were later able to access the systems from a far, this allowed them to take control of the screens. They were able to manipulate the speedometer to show the wrong speed, lower and raise the windows, lock and unlock the car and turn the car on or off." states the Financial Times.
Tesla admitted the existence of the flaw and informed the press that it has already issued a software patch. In an official statement, Tesla clarified that the hackers did not turn off the car remotely, but from inside the vehicle.
"Our security team works closely with the security research community to ensure that we continue to protect our systems against vulnerabilities by constantly stress-testing, validating, and updating our safeguards," stated Tesla.
The duo of experts Kevin Mahaffey (Chief technology officer of cybersecurity firm Lookout) and Marc Rogers (Principal security researcher at Cloudflare) decided to test a Tesla vehicle due to the high reputation of the company in security matter. Tesla Motors is considered by the hacking community one of the companies that spent the greater effort to produce safe and secure cars.
"We shut the car down when it was driving initially at a low speed of five miles per hour," Roger explained to the Financial Time. "All the screens go black, the music turns off and the handbrake comes on, lurching it to a stop."
Tesla confirmed that it has distributed the patch through an over-the-air update.
In April 2014, a security researcher reported a series of security issues to the Tesla Company related to the S model that could be exploited by attackers to locate and unlock the vehicles.
Well, I consider the approach of Tesla very effective. The company immediately recognized the importance of the flaws and its experts promptly solved the problems.
Very efficient also the way Tesla has distributed the patch to its customers by choosing an over-the-air mechanism for its customers that doesn't requested any effort to them.
In this way, the company controlled the deployment of the patch reaching almost every car owner, a situation quite different from the approach chosen by Fiat Chrysler.
In order to produce even more secure vehicles, Tesla launched a bug bounty program paying around $10,000 per vulnerability, embracing the security community and improving its cars.
Conclusions
The number of connected cars is growing each year. These vehicles are equipped with automatic notification of crashes, notification of speeding and safety alerts, but recent studies demonstrated that they are prone to hacking. Experts speculate that automakers have not taken measures to adequately protecting their connected cars from cyber-attacks.
Hackers could hack the vehicles for sabotage or to steal the owner's data managed by its components.
Cloud services, e-mail, text messages, contacts, and other personal, financial, and work data are vulnerable to hackers. Burglars could determine vehicle location provided by these sources
Connected cars can share information with other vehicles in a C2C (car-to-car) or a C2I (Car-to-Infrastructure) connections in real-time. Cars are becoming part of IoT (Internet of Things), sophisticated nodes of the global network that manage a huge quantity of information. Experts predict that IOT risks are going to increase drastically this year; this means that we need to approach the implementation of cyber security for these devices in a different way.
A recent study published by the IBM Institute for Business Value, "Driving Security: Cyber Assurance for Next-Generation Vehicle," they have identified three areas for automakers and partners to focus on when creating connected car features:
1. Design Secure Cars: Security starts with the car. The design process should be focused on security, which means outlining and testing the risks and threats for each component, subsystem, and network that the connected vehicle will be exposed to once it leaves the car marker's production line.
2. Create Safe Networks: Communications should be encrypted; this means that all the organizations providing services that connect roadways, cars, and devices need to protect their networks and monitor transactions to detect suspicious activity.
3. Harden the vehicle: These connected cars should be security hardened at all levels:
- Encryption of data at rest and data in motion.
- Implementing proper cloud security controls.
- Access control mechanisms
- Securing the operating system.
- Penetration testing of the apps.
Researchers must encourage the automotive industry to consider seriously the security as a mandatory requirement for the safety of car owners; most important is that car owners in the next future will chose their cars also based on security features implemented by the automakers.
References
http://securityaffairs.co/wordpress/38739/hacking/connected-car-hacking.html
http://securityaffairs.co/wordpress/38844/hacking/jeep-cherokee-hack-fiat-recall.html
http://securityaffairs.co/wordpress/39453/hacking/crack-car-transponder.html
http://securityaffairs.co/wordpress/35204/hacking/connected-cars-risks.html
http://securityaffairs.co/wordpress/39375/hacking/ownstar-attack-bmw-chrysler-mercedes.html
http://securityaffairs.co/wordpress/39500/hacking/bmw-ownstar-attack.html
https://resources.infosecinstitute.com/car-hacking-safety-without-security/
http://securityaffairs.co/wordpress/38999/hacking/hack-gm-cars-ownstar.html
http://www.wired.com/2015/07/hackers-remotely-kill-jeep-highway/
http://www.wired.com/2015/07/gadget-hacks-gm-cars-locate-unlock-start/
http://www-935.ibm.com/services/us/gbs/thoughtleadership/automotivesecurity/
http://securityaffairs.co/wordpress/39453/hacking/crack-car-transponder.html
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.
http://securityaffairs.co/wordpress/39173/hacking/tesla-motor-patch.html