How Security Awareness Training Can Prevent a Ransomware Situation
I. What is Ransomware?
Ransomware is a type of malware that locks users out of their computer systems or/and files and demand ransom to restore the status quo ante. Typically, an on-screen alert notifies the user about the fact that he will not be able to regain access to his information/system unless the ransom is paid in full within a short period of time. As a whole, it is a successful strategy that thrives on a motley mixture of emotions: surprise, shock, anger, sense of urgency, and sometimes even of outright panic. Therefore, ransomware is much more successful when the victim is caught off-guard, unprepared and in a state of sheer confusion.
There are two main attack vectors with respect to ransomware:

Two year's worth of NIST-aligned training
Deliver a comprehensive security awareness program using this series' 1- or 2-year program plans.
- Social engineering – innocuous-looking emails lure potential victims into clicking on attachments that appear legitimate (e.g., images, invoices, word and pdf files), but which have malware under the hood.
- Drive-by exploits/Malvertising – here users are prompted to click on a legitimate-looking URL that leads to infected websites, which in turn, transfer a malicious payload to the users' machine. In a variation of that type of compromise, users visit an infected website by their volition, of course without knowing about the lurking threat. Many websites nowadays experience, for instance, malvertising problems that may potentially expose every visitor to various dangers, ransomware being one of them. As FBI Cyber Division Assistant Director James Trainor explains, "criminals have evolved over time and now bypass the need for an individual to click on a link. They do this by seeding legitimate websites with malicious code, taking advantage of unpatched software on end-user computers." /Source: https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise/

Other ways through which a ransomware attack could sift through are the web-based instant messaging applications and vulnerable web servers.
a) Types of ransomware:
- Scareware
It is a combination of rogue security software and a tech support scam. A message will appear on your screen, claiming that your  computer system is plagued with every commonly known type of malware to convince you to pay a small fee to "fix the problem." Self-explanatory, the real problem here is the scareware itself, which bombards you with these fake virus alerts; however, a simple scan from legitimate security software should be able to save you from such a nuisance.
computer system is plagued with every commonly known type of malware to convince you to pay a small fee to "fix the problem." Self-explanatory, the real problem here is the scareware itself, which bombards you with these fake virus alerts; however, a simple scan from legitimate security software should be able to save you from such a nuisance.
- Screen Lockers
 Usually accompanied by the FBI or U.S. Department of Justice seal, a full-size window appears upon turning on your device, stating that these institutions have detected illegal activities on your device, your device is now "locked," and you must pay a fine to regain access.
Usually accompanied by the FBI or U.S. Department of Justice seal, a full-size window appears upon turning on your device, stating that these institutions have detected illegal activities on your device, your device is now "locked," and you must pay a fine to regain access.
Well, this is not a message from the FBI or whoever else it claims is from. The real FBI would not lock your screen just like that if you are involved in online criminal activities, such as child pornography, the real FBI would lock you up if that is the case.
That being said, you need to have recourse to a full system restore or a scan from a bootable USB drive to reclaim control over your device.
- File-encrypting Ransomware /Crypto-ransomware/
 This is the heavy artillery. It is a specific kind malware that snatches up your unprotected files and encrypts them, demanding payment to decrypt and return them back to you. The reason why this type of ransomware is so dangerous is that once cybercriminals get hold of your files, no security software or system could help you restore them – what is done by the file-encrypting ransomware cannot be undone … easily or at all. Kiss your precious documents goodbye, because unless you pay the ransom, your encrypted information is gone for good. Moreover, even if you do pay, there is no guarantee that you can get those files back. The focus of this paper is on encryption ransomware
This is the heavy artillery. It is a specific kind malware that snatches up your unprotected files and encrypts them, demanding payment to decrypt and return them back to you. The reason why this type of ransomware is so dangerous is that once cybercriminals get hold of your files, no security software or system could help you restore them – what is done by the file-encrypting ransomware cannot be undone … easily or at all. Kiss your precious documents goodbye, because unless you pay the ransom, your encrypted information is gone for good. Moreover, even if you do pay, there is no guarantee that you can get those files back. The focus of this paper is on encryption ransomware
b) Names of popular strains of ransomware:

TeslaCrypt was the most commonly encountered crypto-ransomware in 2016; however, CryptoLocker is perhaps the most famous type of ransomware. Once deployed, it is in hot pursuit of files that are likely to contain valuable data, for instance, PDFs, Microsoft Office file formats, and image files. Next stage begins immediately afterward, by creating a pop-up window whose purpose is to inform the victim that his files are locked, and he must quickly pay. Otherwise, the decryption key will be destroyed, rendering the files literally unusable.
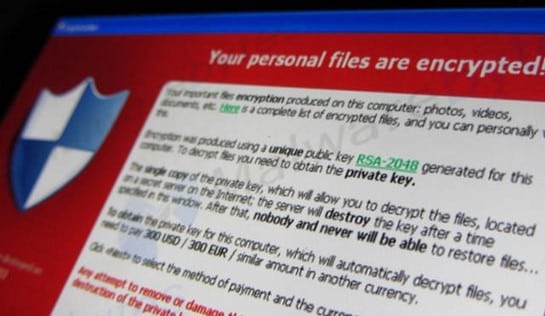
Photo by Christiaan Colen / CC BY-SA 2.0 /changed/
The most sophisticated strains of ransomware not only go after files on individual PCs but also attack attached drives, online backup repositories (e.g., clouds), and corporate core servers. For example, a type of ransomware called MSIL/Samas, armed with strong encryption capabilities (RSA-2048), hunts and deletes network backups.
In addition to doing so, Locky – another popular ransomware — attempts to locate and erase Volume Shadow Copy files. These files are a feature in Windows-based systems whose purpose is to backup copies of files automatically during the time when are being opened by the user.
Locky is a special kind of ransomware – a hybrid of conventional ransomware infections and malware designed for cyber exploitation and data breaches – as it is capable of taking out an entire network. With the help of extra tools, such as backdoors and keystroke loggers, attackers could steal administrative credentials and progressively advance through the targeted network /i.e. lateral movement/. Locked up file-share servers is what follows next. "You do not have to lock an entire network," explains the CEO of the security firm KnowBe4 Stu Sjouwerman. "You just need to find where are the critical files in a network—what servers are serving up the millions of files that most workers use... Moreover, you only need to lock maybe two or three file servers to essentially block the whole network." /Source: https://www.wired.com/2016/03/ransomware-why-hospitals-are-the-perfect-targets/ /. The bad news ceases not: the criminals could use those shared files as a means of spreading the malware infection to every individual who accesses them.
Samas uses the more targeted approach as it does not lie in ambush for careless people to open an attachment. Instead, the cybercriminals behind Samas exploits vulnerabilities in Java servers and not sufficiently protected RDP credentials to sneak into corporate networks and hijack as many computers as possible, often placing the ransomware manually.
Both Locky and Samas were observed to cause havoc in the health care industry throughout 2016.
II. Ransomware Statistics & Trends
A McAfee report confirms everyone's concerns: Ransomware is on the rise. By the first half of 2015, the number of ransomware samples jumped 5.3 times compared to a year earlier. The FBI report that the first three months of 2016 alone amounted to the staggering $209 million regarding monetary losses inflicted on the victims, whereas this figure was $24 million in all of 2015. Also, the agency mentions another worrisome concomitant tendency, namely the fact that "less than 1 in 4 ransomware incidents are reported to the authorities."
Not only ransomware attacks proliferate rapidly month after month, but they also have become more sophisticated. For instance, while not long ago their main hunting ground was in the realm of spam emails, the ransomware strains of today rely on spear-phishing, thus targeting specific individuals. Also, small businesses tend to be more vulnerable as they may not pay enough attention to adequate backups and bookkeeping.
Cases of ransomware-related corporate incidents became more frequent during 2015, according to law enforcement. However, why corporations? The main reason, of course, is money – cyber attacks against organizations bring more profit compared to targeting the man on the street (the Internet, in fact). Grayson Milbourne, Security Intelligence Director for cyber security firm Webroot, sees a surge in focus on ransomware attacks against corporate entities. His interpretation of this trend is:
"The value of my personal files and pictures caps off somewhere. But [if] I encrypt the back-end of your corporate system and prevent you from processing payments, that has a tremendous value. And if the hacker can recognize the value of what he has, the ransom can be more dynamically set based on the content of the data."
Source: http://www.pcmag.com/news/343547/the-growing-threat-of-ransomware /
In certain cases, more than the others, especially when we consider the matter at a corporate level, the inability to access vital data can be devastating and materialize in very tangible negative consequences, such as disruption of normal operations, loss of sensitive and proprietary information, financial and reputational harm. An excellent exercise on whether not paying the ransom outweighs the negative consequences is presented based on statistics collected by the Aberdeen Group, a consultancy, which calculates that an hour of inactivity due to a ransomware caused outage costs an average of $8,581. If we make a comparison with what a Datto's survey estimates to be the range of three-quarters of the firms paid the ransom in 2016, it appears that lost productivity is the bigger concern by a wide margin.
Pursuant to a Trend Micro report, the average ransom demanded totals up about $722, and the majority of victim organizations end up paying it despite that three-quarters of the interviewed organizations which had no close contact with this ubiquitous scourge claimed that they will never cave in to the cybercriminals' demands. Apparently, many people are susceptible to a sudden change of heart when the things get real.
III. Real-world cases of ransomware
In the notorious article How My Mom Got Hacked published in January 2016, Alina Simone, a singer and writer, tells the ransomware misadventures of her mother and her. Long story short: the personal computer of Simone's mother was infected with the said malware, and the daughter tried to help her pay the $500 ransom in Bitcoin. Due to the volatile nature of the exchange rates of the cryptocurrency, however, the payment was $25 short. In the end, Simone's mother did not meet the payment deadline, but she pleaded with the criminals, and they decrypted her stolen data. What is perhaps interesting in this story is the fact that according to Simone, having to pay the ransom in Bitcoin, "gave it this extra level of terror [that] freezes your brain — it's just another thing to figure out."
"Let's stock up with bitcoin well in advance" seems to be the motto of some organizations nowadays, because purchasing Bitcoins may take up three to five days in the United States. Since cyber criminals trust this method of payment, almost all types of ransomware naturally go hand-in-hand with the most popular cryptocurrency. While this can be a real double-edged sword for the crooks themselves, the majority of victims will have to go through a crash course on how to deal with Bitcoin. Some of the cybercriminals act professionally and include 24/7 web-based tech support to assist victims who come across difficulties paying the ransom.

During the spring of 2016, a series of unrelated ransomware attacks happened within a couple of weeks. Firstly, Locky struck the Hollywood Presbyterian Medical Center in Los Angeles. With all computers being offline for more than a week, the hospital management raised the white flag and transferred $17,000 in Bitcoin.
Then, Methodist Hospital in Henderson, Kentucky was the next victim of Locky. This attack prevented health care providers from accessing medical records of patients. Nevertheless, the state of emergency declared by the Methodist officials lasted only several days due to the administrators being able to restore the encrypted data from backups successfully.
Lastly, MedStar Health, a major healthcare provider in the Maryland/Washington, DC area became a victim of a virus, which many experts believe to be ransomware because of numerous reports by employees and onlookers about pop-up windows on computer screens demanding payment in Bitcoin. In response to this cyber attack, the medical provider shut down immediately significant portions of its network. MedStar was reluctant to comment on the incident.
Obviously, attacking hospitals is a new trend in the ransomware evolution. With their job dedicated to the provision of critical care facilitated by constant access to patient records and surgery directives, all medical facilities seem to be the ideal mark for such a type of cyber extortion. It is one thing to sell vegetables and have no access to the inventory, but it is a completely other matter if you need to access medical records of living people urgently – "[i]f you have patients, you are going to panic way quicker than if you are selling sheet metal," says along the same lines Stu Sjouwerman.

Photo by NEC Corporation of America with Creative Commons license
IV. Should I Pay or Should I (Let It) Go
Ransomware present the same moral dilemma as any other extortion schemes. There is something else, however – the sums demanded in cases of ransomware are deliberately set to be affordable to the victim so that the payment per se to be the more enticing option to him than losing his precious files. Besides, victims are now aware that the only way to retrieve their encrypted information is to pay up.
Even an FBI agent is willing, at least unofficially, to admit total defeat in a situation of a severe ransomware infection:
"The ransomware is that good," complained Joseph Bonavolonta, the Assistant Special Agent in Charge of the FBI's. "To be honest, we often advise people just to pay the ransom." So be it. In February 2016, despite siding with the FBI, the police department in Tewksbury, Massachusetts gave in and made a $500 "donation" to the cause of the people behind the ransomware onslaught against it.
"I think that the FBI has not helped the situation at all by coming out and saying that people should pay the ransom. To me, that goes against everything we know about dealing with malware, bad guys, and cyber-crime. You do not want to keep funding them, and that's what paying the ransom does. And they keep putting more funding into development, which seems to be what they're doing right now," said G Data Software Security Evangelist Andrew Hayter.
Webroot's Milbourne concurs. "They set a precedent of that being the only option. It's a personal decision. …we don't believe what the FBI has told people to do is the right approach. That said, the hospital has a business to run. If it means people's lives, $17,000 is a reasonable price to pay to get your business back online. Does that mean it's a good precedent to be setting? No."
Source: http://www.pcmag.com/news/343547/the-growing-threat-of-ransomware /
No one will guarantee you a happy ending even if you decide to pay the ransom. The price may go up, or the encrypted data may be rendered permanently irretrievable. The president of GCS Technologies, an Austin-based IT support, and services company Joe Gleinser voiced a reasonable concern: "Paying the ransom is tricky business. You're dealing with criminals. Datto's survey found that 7 percent of IT professionals reported incidents where data was not restored even after a ransom was paid." Moreover, "[w]e've seen some clients who had paid the ransom and then immediately get attacked again," Gleinser said.
Source: https://www.theatlantic.com/business/archive/2016/09/ransomware-us/498602/ /

FBI's Trainor shares his stance on the matters:
"Paying a ransom doesn't guarantee an organization that it will get its data back—we've seen cases where organizations never got a decryption key after having paid the ransom. Paying a ransom not only emboldens current cyber criminals to target more organizations, it also offers an incentive for other criminals to get involved in this type of illegal activity. And finally, by paying a ransom, an organization might inadvertently be funding other illicit activity associated with criminals."
Source: https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise/
Through paying the ransom, victims often see the quickest way to compensate for a security lapse, which is often their own fault. Ransomware is rampant because victims pay. Ransomware is becoming more sophisticated because victims pay. As long as victims pay, ransomware will be rampant.
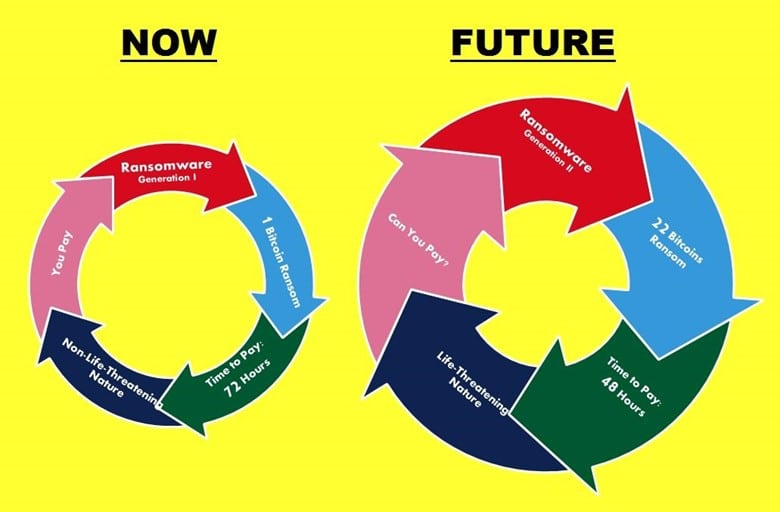
Perhaps it may be unreasonable to pay now. Later on, a newer strain of malware, whose R&D was financed with your money, may take quite a toll on your or somebody else's life.

V. Prevention through Education (Tips)
As mentioned earlier, there is nothing you can do in cases of encrypting ransomware once your files are encrypted. Thus in this situation, foresight is always better than hindsight. It is a simple conviction reaffirmed by Adam Kujawa, Head of Intelligence at Malwarebytes: "If any attack in the history of malware proves that you need protection in place before an attack happens, encrypting ransomware is it. It's too late once you get infected. Game over."
Source: https://blog.malwarebytes.com/101/2016/03/how-to-beat-ransomware-prevent-dont-react//
Prevention – in reality, one rarely does have any clue or time to react defensively the moment the infection takes places; hence, all necessary defense measures should be fortified in advance. Organizations will find their best solution against malware and other similar threats somewhere at the junction between security awareness training for employees and robust technical prevention controls.

Source: https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise/
*Security experts advise users to dispense with untrustworthy browser plugins such as Java and Flash, as they require, inter alia, frequent security updates. When a device with outdated browser plugins visits websites, it may fall prey to exploit kits, (i.e., a malicious program that takes advantage of hacked or malicious websites), which will install automatically and quietly malware into your system.
**Among the biggest risks associated with desktop users are insecure browser plugins, as well as corrupt Microsoft Office files and "macros" received via email under the guise of critical, time-sensitive documents.
Furthermore, with regard to mobile ransomware, it usually lurks into popular applications findable at app stores and other similar places. Thera are a large number of malicious copycats, so always download apps/games from the original source.
Business continuity plan – every respectable organization should have one. You have to act preemptively with pests like ransomware, but then again, you should have a workable business continuity plan in place to keep your business afloat in cases of ransomware-related incidents.
Bad things happen to everyone. Sometimes it is more important to know how to react even if your best prevention efforts cannot live up to their promises. "There's no one method or tool that will completely protect you or your organization from a ransomware attack. But contingency and remediation planning is crucial to business recovery and continuity—and these plans should be tested regularly," states Trainor.

Source: https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise/
So, don't be like a deer caught in the headlights and design your detailed post-breach response as soon as possible.

Even the latest and most advanced antivirus and specialized anti-ransomware products may not salvage you from a post-ransomware disaster if you as an individual inadvertently undermine your own security. For example, "There are a lot vulnerable systems. But primarily [ransomware proliferates] through web exploit kits and direct email campaigns that trick people into being dumb and infecting themselves," says Milbourne.
Consequently, regular security awareness training is an indispensable precondition for avoiding big troubles. Before each strain of ransomware to have the opportunity to gain a foothold on a targeted system, it first has to find its way in. That happens through social engineering, most likely through phishing emails that carry attachments loaded with hidden malware or phishing emails that prompt recipients to click on malicious URLs that will eventually install a piece of malware in a surreptitious manner. Good security awareness training is the key to increase your chances to differentiate between legitimate and bogus emails, among other things. The more practical that training is, the better results you will achieve. According to Sjouwerman, regular security awareness training may result in "a dramatic decrease [of] click-happy employees. You send them frequent simulated phishing attacks, and it starts to become a game. You make it part of your culture and if you, once and month, send a simulated attack, that will get people on their toes." If you follow this advice, you will be off to a good start in the continuous race with the criminal minds out there.
Reference List
Avast.com. Ransomware. Available on https://www.avast.com/c-ransomware
(22/01/2017)
Chandler, A. (2016). How Ransomware Became a Billion-Dollar Nightmare for Businesses. Available on https://www.theatlantic.com/business/archive/2016/09/ransomware-us/498602/ (22/01/2017)
csa.gov.sg (2016). [SingCERT] Ransomware. Available on https://www.csa.gov.sg/singcert/news/advisories-alerts/ransomware (22/01/2017)
FBI (2016). Incidents of Ransomware on the Rise. Available on https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise (22/01/2017)
Heater, B. (2016). The Growing Threat of Ransomware. Available on http://www.pcmag.com/news/343547/the-growing-threat-of-ransomware (22/01/2017)
Intel Security (2016). Ransomware and You. Available on https://securingtomorrow.mcafee.com/consumer/family-safety/ransomware-and-you/ (22/01/2017)
krebsonsecurity.com (2016). Before You Pay that Ransomware Demand… Available on https://krebsonsecurity.com/2016/12/before-you-pay-that-ransomware-demand/
(22/01/2017)
US-Cert (2016). Alert (TA16-091A): Ransomware and Recent Variants. Available on https://www.fbi.gov/news/stories/incidents-of-ransomware-on-the-rise (22/01/2017)
Zamora, W. (2016). How to beat ransomware: prevent, don't react. Available on https://blog.malwarebytes.com/101/2016/03/how-to-beat-ransomware-prevent-dont-react/ (22/01/2017)
Phishing simulations & training
Zetter, K. (2016). Why Hospitals Are the Perfect Targets for Ransomware. Available on https://www.wired.com/2016/03/ransomware-why-hospitals-are-the-perfect-targets/ (22/01/2017)




