Reddit’s employees phished, healthcare firms targeted and the new Screenshotter malware
Hackers phish Reddit employees to steal internal documents, North Korean hackers extort healthcare firms and the custom Screenshotter malware. Catch all this and more in this week’s edition of Cybersecurity Weekly.
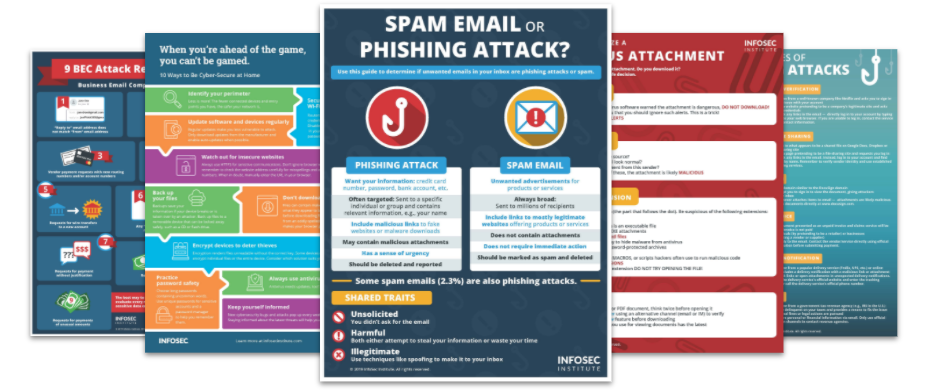
Top Security Awareness Posters
1. Reddit breach sees hackers access source code and internal documents
Reddit has disclosed that it fell victim to a cyberattack that enabled hackers to access its systems and steal source code and internal documents. The social news aggregation platform blamed the incident on a phishing attack targeting Reddit's employees and learned about it after an affected employee self-reported the breach. After investigation, the company says the stolen data includes limited details for existing and previous employees and company contacts. Additionally, it stressed that it didn’t find any evidence to suggest that its core production systems were breached.
2. North Korean threat actors target South Korean and U.S. healthcare with ransomware
State-sponsored hackers from North Korea are targeting the healthcare sector to fund their operations, according to a warning from South Korea and U.S. intelligence agencies. The ongoing campaign demands cryptocurrency ransomware in exchange for reinstating access to encrypted files. Additionally, the hackers work with foreign intermediaries and hide behind virtual networks to avoid being traced back to North Korea. Further, They use publicly available tools such as Deadbolt, BitLocker, and Ryuk in their attacks and sometimes portray themselves as another ransomware gang.
3. Hacker creates new Screenshotter malware to identify highly lucrative targets
A hacker has developed a new malware capable of taking screenshots of infected computers and identifying highly lucrative targets. Dubbed Screenshotter, the malware is thought to be used by a new threat actor nicknamed TA886 for targeting companies in the United States and Germany. Once the malware has taken the screenshots, the adversary carefully examines them to see if a target is worth continuing their attack on. It is believed that the threat actor’s main goal is to make a profit, carefully selecting their targets by evaluating the information they have access to.
4. New IIoT device vulnerabilities pose threat to critical infrastructure
38 security weaknesses have been found in wireless industrial internet of things (IIoT) devices from four different manufacturers, presenting a major vulnerability for potential attackers looking to target operational technology (OT) systems. Israeli cybersecurity firm Otorio warns that threat actors take advantage of these flaws to bypass security and infiltrate critical infrastructure networks. According to security researcher Roni Gavrilov, some of these weaknesses can be linked to provide external attackers with direct access to various internal OT networks via the internet.
5. Tor networks attacked in a massive DDoS campaign
The Tor Project has disclosed it has been suffering from various different DDoS attacks for the past seven months. Tor’s Executive Director Isabela Dias Fernandes said that the attacks impacted the network so severely at some points that users were not able to access onion services or load pages. She further stated that the company has not yet identified the goal of these attacks but is working hard to mitigate the impact and defend the network from threat actors.
See Infosec IQ in action
![]()




