Massive AT&T data breach and fake jobs targeting security researchers
AT&T data breach exposes 9 million user accounts, North Korean adversaries target security researchers with fake job offers and the IceFire ransomware. Catch all this and more in this week’s edition of Cybersecurity Weekly.
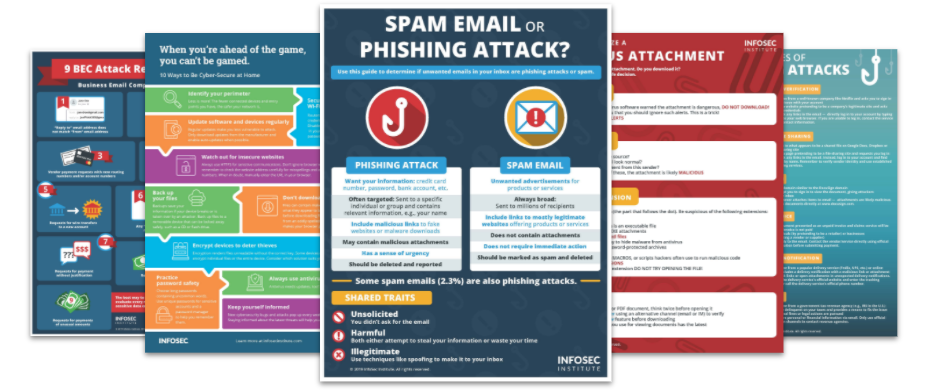
Top Security Awareness Posters
1. AT&T data breach affects 9 million customer accounts, notification issued
AT&T recently disclosed a data breach that impacted around nine million customers. The AT&T breach occurred at a vendor’s system, allowing attackers to access the Customer Proprietary Network Information (CPNI). CPNI is information that telecom companies acquire about subscribers, including services, payment and usage details. The carrier stated that the exposed data did not include financial or other sensitive information, but basic personal information such as customer names, phone numbers, and email addresses was exposed.
2. North Korean hacking group targets security researchers with fake employment offers
A North Korean hacking group, UNC2970, has targeted security researchers and media organizations in the U.S. and Europe using fake job offers. The adversaries use LinkedIn to lure their targets before moving to WhatsApp and sharing a malicious Word document with embedded macros. These macros fetch a trojanized version of TightVNC from compromised WordPress sites, and the attackers establish a foothold in the target's corporate environment using previously unseen malware. UNC2970 has previously targeted tech firms, media groups, and entities in the defense industry.
3. Enterprise Linux systems targeted by a new form of IceFire ransomware
Researchers at SentinelOne have observed a recent increase in ransomware attacks targeting Linux enterprise networks, marking a notable shift from a long-standing focus on Windows-only malware. This shift could be due to hackers perceiving Linux as an untapped market. Among the attackers targeting Linux systems is the IceFire ransomware, previously a Windows-based malware. The attackers' modus operandi is straightforward, with valuable data stolen before encryption to ensure payment. Linux-based systems are often used for critical applications and could yield higher returns, making them more valuable targets.
4. Acer discloses data breach after hacker lists 160GB trove of stolen data for sale
Acer has suffered a breach by a hacker claiming to have 160 GB of the PC maker’s data. The culprit is selling access to the stolen files on a hacker forum. The data reportedly includes confidential presentations, product model documentation, and data about the BIOS system used on Acer computers. Acer has confirmed the breach but claims there is no indication that consumer data was stored on the server. This is not the first time Acer has experienced a breach, with the company suffering at least a couple of hacking incidents in 2021.
5. Xenomorph Android malware has a new variant that can target 400+ banks
A new variant of the Android banking trojan Xenomorph has emerged, according to security researchers at ThreatFabric. The updated version, Xenomorph 3rd generation, incorporates Accessibility Services to perform fraud via overlay attacks. Xenomorph also has cookie-stealing capabilities, which allow cybercriminals to perform account takeover attacks. The malware is being distributed through Discord’s Content Delivery Network (CDN) and has expanded its target from 56 European banks to over 400 banking and financial institutions.
See Infosec IQ in action
![]()




