Introduction to TrueCrypt
While searching on the Internet for protecting our data and laptop, there are lots of software or tools available. Suppose you are using an Apple device, then it is not difficult to track your device. Now when we consider the security of our data / information then you must hear about Blackberry. The entire corporate environment uses Blackberry for only one purpose, and that is encryption and decryption techniques to protect data / information.
BitLocker is another of the known tools for encryption. If you really think about encrypting information then you must learn about TrueCrypt. If you're looking for a powerful way to encrypt everything from system drives/ HDD hard disk, TrueCrypt is an open-source tool that will help you to lock up your files. Read on as we show you how to get started.

What should you learn next?
What should you learn next?

TrueCrypt is tool that encrypts data or information using on-the-fly technique.. On-the-fly technique decrypts data when we have to use it and again encrypts data as soon as we are done with it. This entire process is without any user intervention.
When we copy from a mounted TrueCrypt drive / volume, this process is just like copying from one storage disk to another storage disk. At this time data decrypts and stores in temp storage in memory or RAM. After we use this data, the data encrypts and the memory becomes free for other uses.
Here I want to say that the whole set of data is not stored in RAM at one time. It is like bitwise data which we are using, or which is currently being used. For this process, we don't need extra RAM / memory.
Let's take an example that there is an abc.flv video file stored on a TrueCrypt disk. If the user provides the correct password / encryption key and mounts (opens) the TrueCrypt disk,then after the user double clicks on the icon of the video file, the operating system launches the program associated with the file type – most of the time media player/ VLC player. The media player/ VLC player then begins loading a small bitwise initial portion of the video file from the TrueCrypt-encrypted disk to RAM (memory) in order to play it. While the portion is being loaded in RAM, TrueCrypt is automatically decrypting it (in RAM). The decrypted portion of the video (stored in RAM) is then played by the media player or VLC player.
This process continues, as the portion is being played, the media player begins loading another small bitwise portion of the video file from the TrueCrypt-encrypted disk to RAM or memory, and the process repeats. That why this process is called on-the-fly encryption/decryption technique, and it works for all file types / information / data (not only for video files).
Note that TrueCrypt never saves any decrypted data to a disk – it only stores them temporarily in RAM / memory. Data is still encrypted even when the volume or disk is mounted. Suddenly when you restart Windows operating system or turn off your computer, the volume will be dismounted and files stored in it will be key protected or inaccessible and encrypted. Even when the power supply is suddenly interrupted without proper system shut down, files stored in the volume or virtual disk are inaccessible and encrypted or password protected. To make them accessible again, you have to mount the volume or disk and provide the correct password or encryption key.
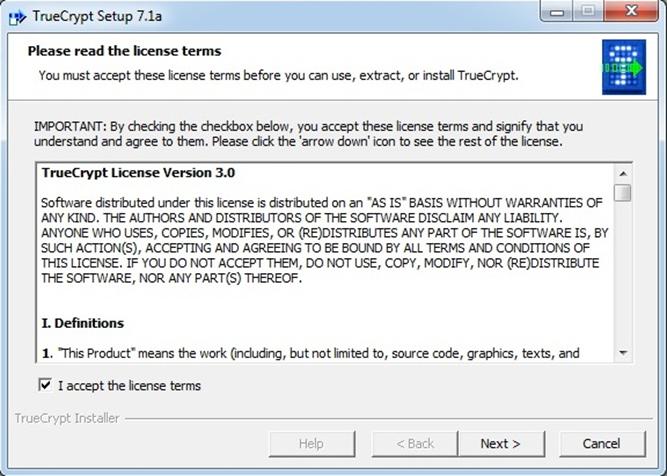
Now we install TrueCrypt on a Windows system:
Kindly accept the license and click the Next button at the bottom.
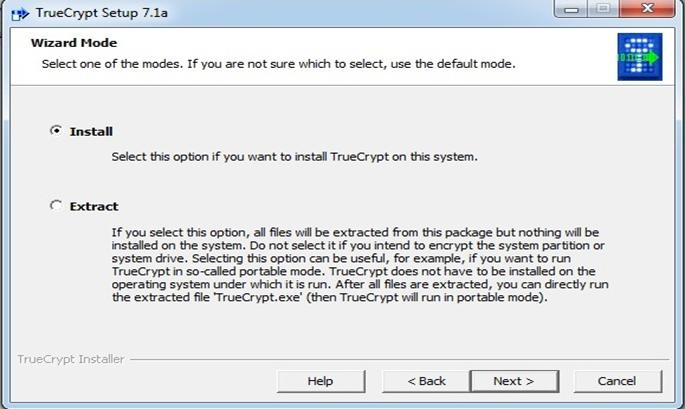
2. Then we get two options for wizard mode selection: the first one is Install and the other is Extract. We have to select one option, and we want to install TrueCrypt on our system, so, we select Install, and click Next..
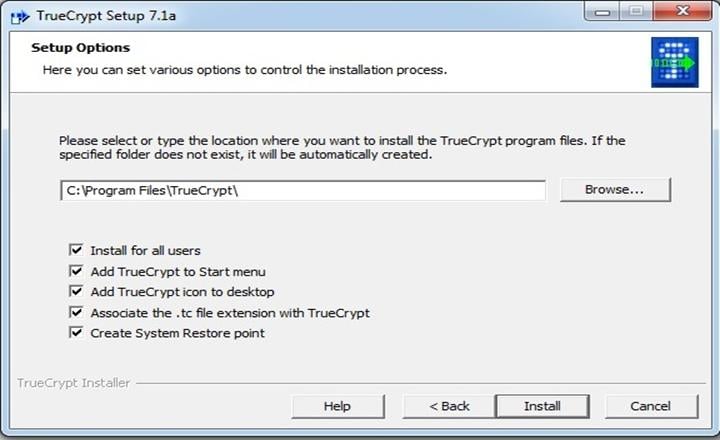
3. Then next step is Setup Options, and we are selecting the location where we want to install the TrueCrypt program files. If the specified folder does not exist, it will be automatically created.
At the same time we have some check boxes, such as Install for all users, Add TrueCrypt to Start menu, Associate the .tc file extension with TrueCrypt, and last but not least, an important option is Create System Restore point.
After selecting all check boxes, click on the Install button at the bottom.
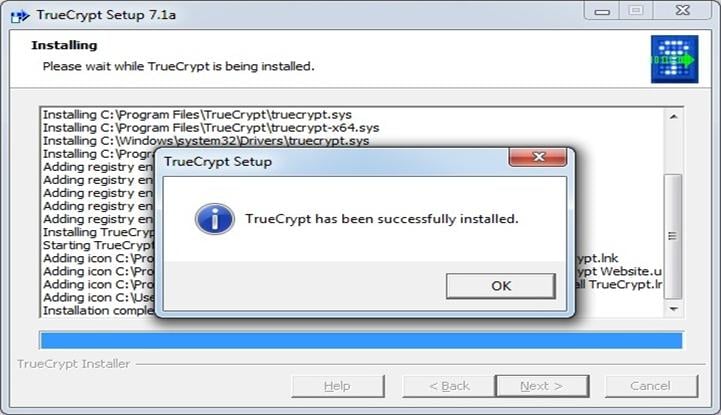
4. Please wait while TrueCrypt is being installed. After TrueCrypt has been successfully installed, click on the ok button, as shown in the figure below.
5. The main advantage of TrueCrypt is that it is an open source program/ tool. After installation we come to a Donate window, it totally depends upon you to make a donation or not.
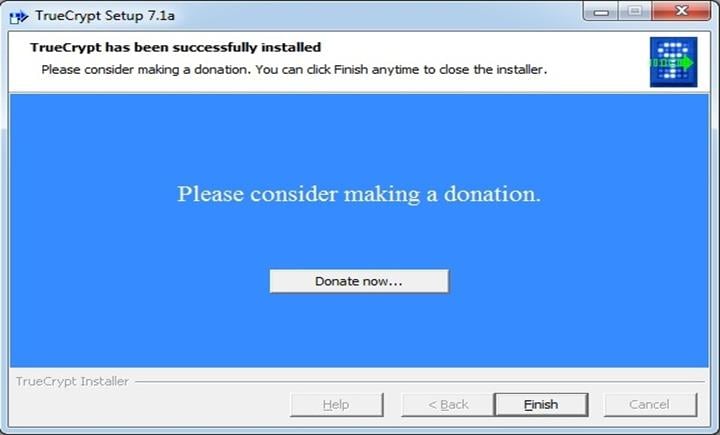
6. You can click on finish to end this setup.
7. At the last step you will get this message box, it gives you some information about using a beginner's tutorial in the TrueCrypt user guide and asks you to view the tutorial.

That's all for the installation part. But the next important part starts here, after installation….
How to Create & Use a TrueCrypt Container:
Now we will learn how to use TrueCrypt with step-by-step instructions.
The initial step to run TrueCrypt is very easy, just double click on its icon. The first thing we need to do is create a volume.
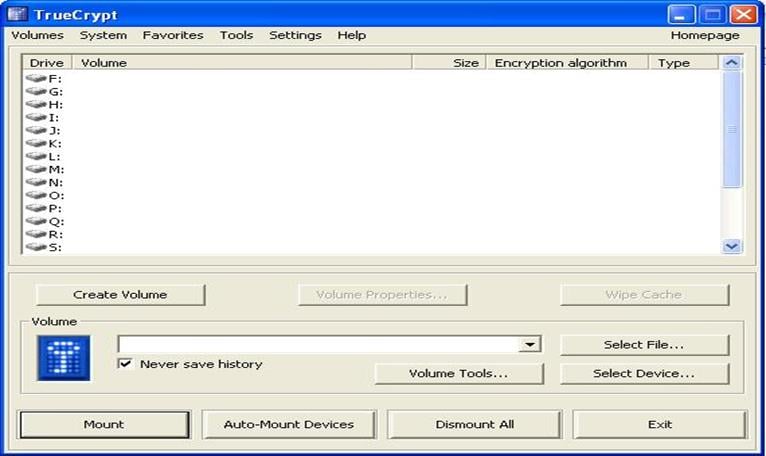
Click on the "Create Volume" button. This will launch the volume creation wizard and prompt you to choose one of the follow volume types:
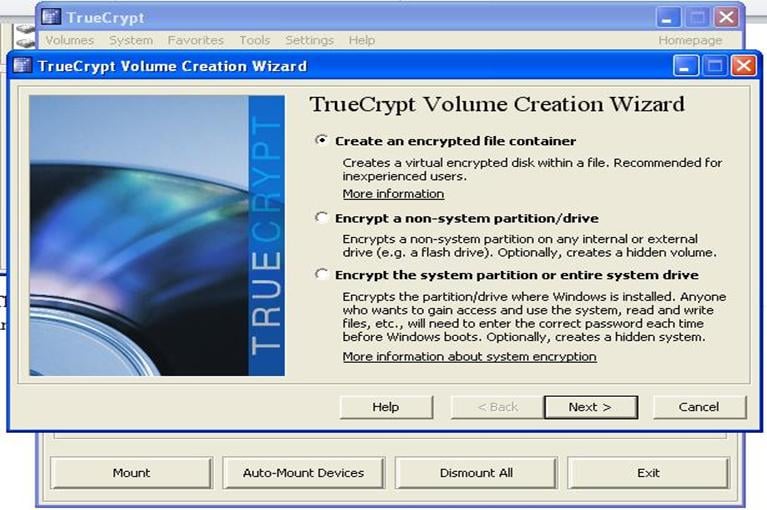
Select "Create an encrypted file container". Next the wizard will ask you for volume type.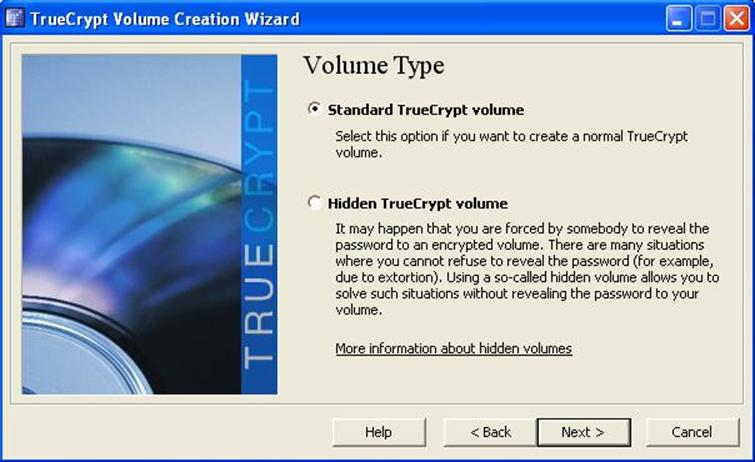
Volume type also provides some options. Go for standard TrueCrypt Volume. 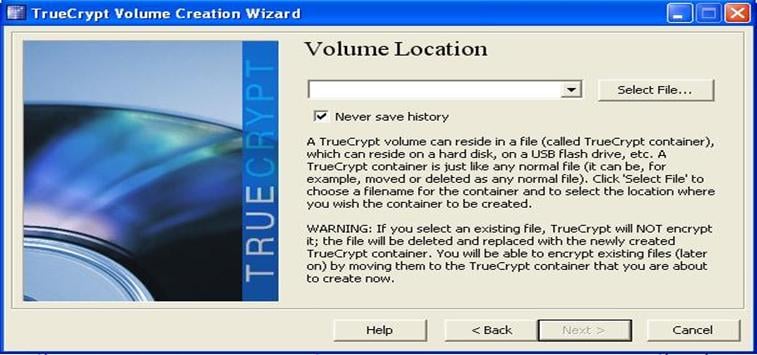
Select a location for your TrueCrypt volume.
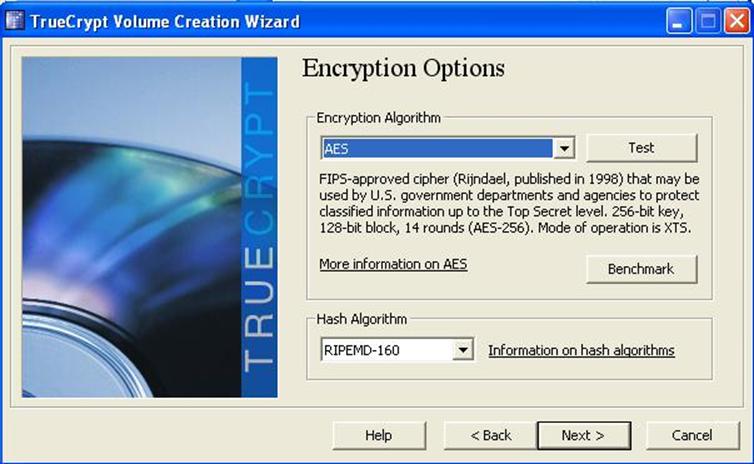
Now it's time to select an encryption algorithm. In 2008, the FBI spent over a year trying to decrypt the AES encrypted hard drives of a Brazilian banker involved in a financial scam. Even if your data-protection-paranoia extends to the level of acronym agencies with deep pockets and skilled forensics teams, you can rest easy knowing your data is secure.
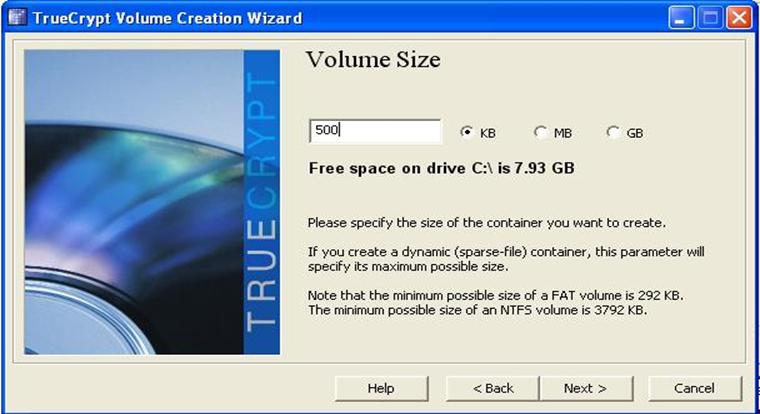
After selecting an encryption algorithm, the next step is to define volume size. It depends upon your choice. Specify the size of the container you want to create in KB, MB or GB. Here note that the minimum possible size of a FAT volume is 292KB. The minimum possible size of an NTFS volume is 3792 kb.
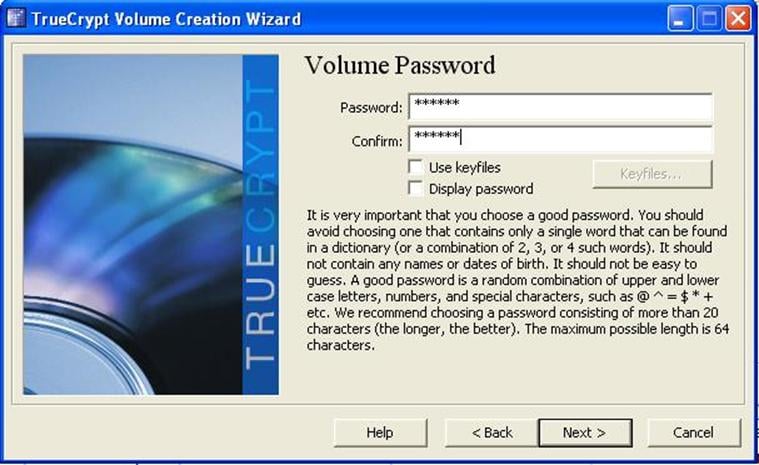
A very important step is volume password.
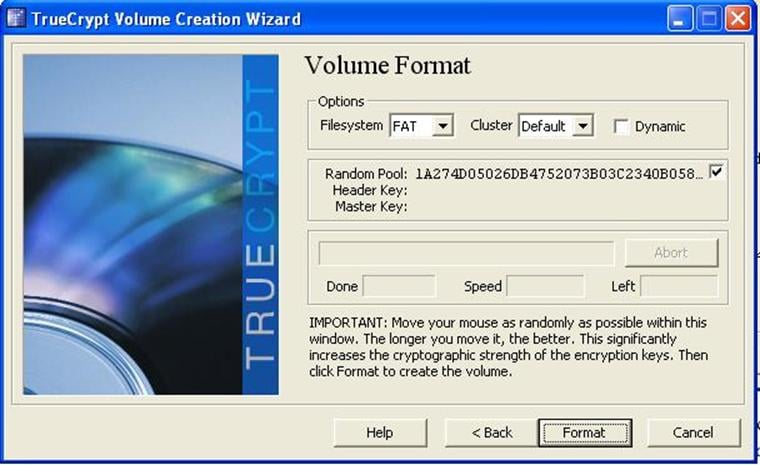
On the volume format screen, you'll need to move your mouse around to generate some random data.
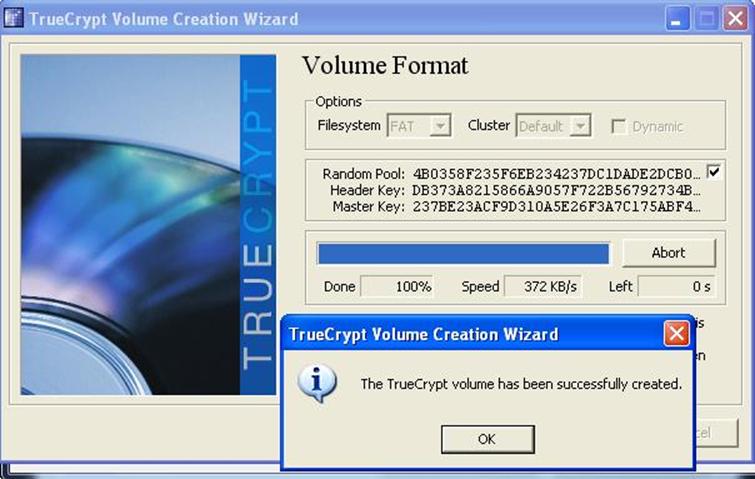
After clicking the Format button, the process is completed and it shows you message box. The TrueCrypt volume has been successfully created. Click on ok, and exit.
Once the format process is complete you'll be returned to the original TrueCrypt interface. Your volume is now a *.TC file wherever you parked it and is ready to be mounted by TrueCrypt.
Click the "Select File" button and navigate to the directory you stashed your TrueCrypt container in, and then mount it.
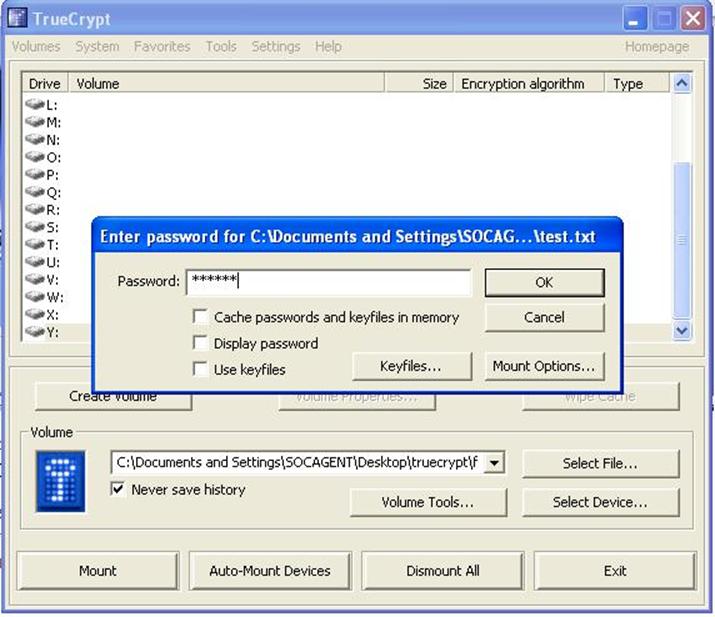
Enter your password. We're going to emphasize our short password. We picked a short one for testing purposes; if you're smart, yours will exceed 20 characters. Click OK.
Let's go take a look at My Computer and see if our encrypted volume was successfully mounted as a drive:

Success! One 225KB volume of sweet encrypted goodness, you can now open the volume and pack it full of all the files you've been meaning to keep from prying eyes.
Don't forget to securely wipe the files once you've copied them into the encrypted volume. Regular file system storage is insecure and traces of the files you've encrypted will remain behind on the unencrypted disk unless you properly wipe the space. Also, don't forget to pull up the TrueCrypt interface and "Dismount" the encrypted volume when you aren't actively using it.
Now enjoy TrueCrypt for hiding data from other persons, even the FBI. J
What should you learn next?


What should you learn next?
References:






