Improving SCADA System Security
Introduction
Supervisory control and data acquisition (SCADA) networks contain computers and software that perform critical tasks and provide essential services within critical infrastructure. They're considered by cyber strategists to be the backbone of any country. Critical infrastructure, and in particular control systems, require protection from a variety of cyber threats that could compromise their ordinary operation.
These systems are used to monitor the key parameters of production processes and to operate their control to ensure the proper provisioning of critical services.
Learn ICS/SCADA Security
Originally, these systems were designed in an environment with the sole intent to monitor processes without considering the security requirements and the needs to protect them from external threats. These systems have a life cycle of decades. Many of those critical components that operate today do so in a context that's completely different from the one they have been designed for. They're exposed on Internet with obvious security risks.
As a result, almost every SCADA performs well. They're reliable and flexible, but often lack security. The impairment of SCADA networks could cause interruption of critical services, process redirection, or manipulation of operational data that could have serious consequences for the population.
What are the best practices to implement to improve the security of SCADAs? What actions need to be taken to secure legacy systems? This article will provide a few suggestions to improve the security of SCADAs.
Current scenario
After recent events, many security firms have started designing solutions to address security problems of SCADA systems. But the major challenge for governments is the inclusion of protection for these critical components in their cyber strategies. Several audits executed by governments on their critical infrastructures have illustrated a dangerous scenario. They demonstrate the lack of security mechanisms for the many systems located all over the world. But what is really concerning is the absence of a precise census of SCADA systems for many industrialized countries.
Events such as the Stuxnet virus and last year's alleged incident of the water facility in Illinois have shown to the world that it's possible to conduct terrorist attacks on foreign states remotely. This has increased awareness of cyber threats, and the need to implement proper countermeasures to mitigate risk.
With defense mechanisms virtually absent, SCADA system components are often under the government of local authorities who don't deal with adequately trained personnel who operate with limited budgets. This means that these kinds of control devices are installed everywhere without being qualified in the installation phase. There are many systems deployed with factory settings, pre-set standard configurations, and they're common to entire classes of devices. Even those who maintain that they shouldn't exceed security, thus making it accessible for remote diagnostics without necessary attention.
Fortunately, something changed. Precise guidelines identify the best practices to follow in the management of SCADA systems, and operations groups monitor the operation of facilities around the country.
The last "INTERNET SECURITY THREAT REPORT" published by Symantec reports that in 2012, there were eighty-five public SCADA vulnerabilities, a massive decrease over the 129 vulnerabilities in 2011. Since the emergence of the Stuxnet worm in 2010, SCADA systems have attracted more attention from security researchers.
In a SCADA system, the programmable logic controllers (PLCs) are directly connected to infield sensors that provide data to control critical components (e.g. Centrifugal or turbines). Often the default passwords are hard-coded into Ethernet cards the systems use. Those cards funnel commands into devices, allowing administrators to remotely log into the machinery.
Hard-coded passwords are a common weakness built into many industrial control systems, including some S7 series of PLCs from Siemens. Because the systems control the machinery connected to dams, gasoline refineries, and water treatment plants, unauthorized access is considered a national security threat. They could be used to sabotage operation.
Doing a search on the Shodan server search engine, you can find what appear to be working links to several vulnerable Schneider models. It's very worrying, and reveals the need for radical change. Fortunately, the emergency has been noticed by most countries. The ENISA (European Network Information Security Agency), has produced recommendations for Europe and member states on how to protect Industrial Control Systems. The document describes the current state of Industrial Control System security and proposes seven recommendations for improvement. The recommendations call for the creation of national and pan-European ICS security strategies, the development of a Good Practices Guide on the ICS security. They would foster awareness and education, as well as research activities or the establishment of a common test bed and ICS-computer emergency response capabilities.
The case
Immediately after the Stuxnet virus, governments and intelligence agencies all over the world requested assessment of security for critical infrastructure of their countries. Much of the focus was on evaluating efficiency offered by defensive measures adopted to protect SCADAs and ICSes from cyber attacks.
After Stuxnet, debate on the use of software and malicious applications of information warfare have increased. Governments are investing to improve cyber capabilities working on both the defensive and the offensive side. Despite greater awareness of cyber threats, critical infrastructures of countries are still too vulnerable. Many security experts are convinced that an imminent incident caused by a cyber attack is likely soon.
Just a few days ago, Eugene Kaspersky, CEO of Kasperky Security, revealed that a staffer at the unnamed nuclear Russian plant informed him of an infection.
"The staffer said their nuclear plant network which was disconnected from the internet … was badly infected by Stuxnet. So unfortunately these people who were responsible for offensive technologies, they recognize cyber weapons as an opportunity."
Stuxnet had infected the internal network of a Russian nuclear plant, exactly in the same way it compromised the control system in Iranian nuclear facilities in Natanz. That's happening despite cyber threats being well known, and various security solutions are able to neutralize it.
Stuxnet infected the network within a Russian nuclear plant isolated from the Internet. Attackers probably used as USB or mobile devices to spread the malware. Russian Intelligence agencies in the past have already observed this infection mode to cross a physically separated 'air-gapped' network. For example, Russian astronauts had carried a virus on removable media to the International Space Station infecting machines there, according to Kaspersky.
"NASA has confirmed that laptops carried to the ISS in July were infected with a virus known as Gammima.AG. The worm was first detected on Earth in August 2007 and lurks on infected machines waiting to steal login names for popular online games. Nasa said it was not the first time computer viruses had travelled into space and it was investigating how the machines were infected. "
I mentioned the Stuxnet malware because it's considered a case study. The malicious agent is so notorious, it's still able to compromise networks and control systems within critical infrastructure. Let's try to figure out the effect of unknown cyber threats, developed by governments as cyber weapons, for example. In this article, I'll analyze major security issues related to SCADA systems, and best practices to follow to protect them.

Figure - Russian Nuclear Plant
According to the last "SANS SCADA and Process Control Security Survey" conducted by the SANS Institute, the awareness of cyber threats and the perception of the risks related to a cyber attacks are high. Nearly 70% of respondents believe the threat to be high (53%) to severe (16%). Recent reports from Computer Emergency Response Teams (CERT), government offices, and private companies confirm an escalating risk of cybersecurity events, specifically for the energy sector.
The survey indicates that the top threats for control systems are advanced zero-day malware such as Stuxnet, cyber operations conducted by groups of hacktivists, and hacking campaigns of cyber terrorists and state-sponsored hackers.
Recently, US CERT alerted to the continuous spear-phishing campaign that targeted the energy sector to gain remote access to control systems. SCADA system protection must be approached at different levels, defending control systems and educating operational and maintenance personnel.
"Training should include specific operational topics on spear-phishing, zero-day activities and managing internal threats."
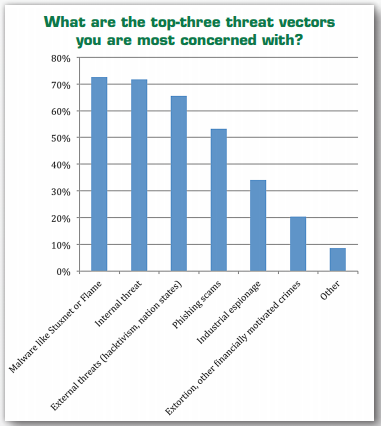
Figure - Top Threat Vectors SANS Institute Survey
SCADA network security
SCADAs are composed of the following subsystems:
- The supervisory system, responsible for data acquisition and for control activities in the process.
- Programmable logic controllers (PLCs), the final actuators used to as field devices.
- A human–machine interface or HMI is the component responsible for data presentation to a human operator, typically it composed of a console that make possible the monitor and the control of the process.
- Remote terminal units (RTUs) are microprocessor-controlled electronic devices that interface the sensors to the SCADA by transmitting telemetry data.
- Communication infrastructure connecting the supervisory system to the remote terminal units.
- Various process and analytical instrumentation
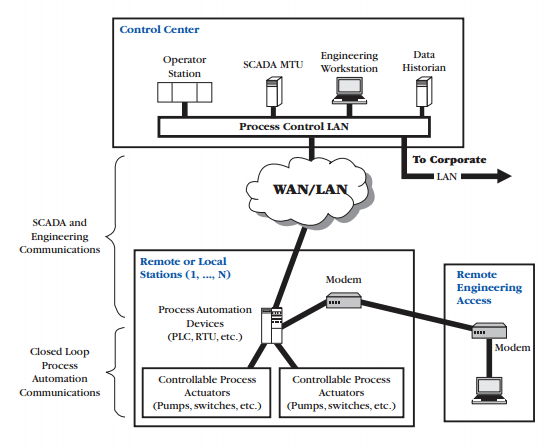
Figure - Overview of a Generic ICS
Attackers could target each of the above components to compromise a controlled process. For example, any supervisory system is usually a computer based on a commercial OS for which it's possible to exploit known vulnerabilities or zero-day vulnerabilities. SCADA systems could be infected exploiting attack vectors via mobile support (e.g. USB sticks) or the network connections.
Establishing and following a risk management framework is the most cost-effective approach to securing critical cyber assets. The NERC Cyber Security Standards sequentially leads each Responsible Entity through the following process:
- Identifying risks
- Implementing controls, mitigating risks
- Maintaining acceptable risk levels through evaluation and monitoring
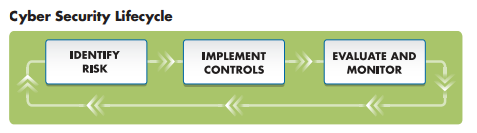
Figure - Cyber Security Lifecycle
Identification and Monitoring of connection to SCADA networks
To protect SCADAs, it's essential to identify each connection to the SCADA network, evaluating the risk of exposure to attacks and implementing all necessary countermeasures to mitigate them.
It could be useful to enumerate the overall connections, the end points of communication (e.g. system management, business partners, vendors), authentication mechanisms implemented, protocols adopted, the function served with the connection (e.g. Telemetry), adoption of encryption mechanisms, the type of communications ( e.g. Ethernet, Wireless network) and the defense systems deployed to defend them.
Any connection to another network introduces security risks, especially for Internet connections. To improve security, it's necessary in many cases to isolate the SCADA network from other network connections.
Use of "demilitarized zones" (DMZs) and data warehousing can facilitate the secure transfer of data from the SCADA network to business networks.
VA Network Connectivity Assessment must be conducted starting by mapping of all networked assets and the digital communication links that connect them. Detailed network maps are essential to identify mission critical assets, and the electronic links that may threaten their reliable operation.
Network connectivity audit results are a collection of written documentation that uniquely, clearly and accurately records all information about every networked asset. They contain the following components.
- Unique identifier (serial number or assigned tag number)
- Description of functionality
- Physical location
- Physical security mechanisms protecting the device (fences, locked cabinets, etc.)
- Network connections to/from the device
- Network addresses (MAC, IP, SCADA, etc.) assigned to the device
- All other available physical interfaces
Another important thing to consider is to carefully configure network appliances by avoiding the use of default configurations easily exploitable by attackers. Commissioning penetration testing and vulnerability assessments to third parties could provide an objective analysis of the level of security of a SCADA network.
It's important to adopt firewalls, intrusion detection systems (IDSs), and all the necessary defense systems at each point of entry. Organization management must understand and accept responsibility for the risks associated with any connection to the SCADA network.
Real-time threat protection
Recent attacks conducted against critical infrastructure are characterized by increased sophistication. A growing number of offensives could not be rejected simply with a proper patch management of the internal systems or maintaining access and service control. The trend is to implement a real-time threat protection, including network intrusion-prevention.
Real time protection could be implemented through a layered approach. Each layer of defense represents categories of system components that must be hardened.
- Perimeter Control
a. Internet or Corporate Perimeter Defense - Employees, Policies, Procedures
a. Business contingency, Disaster Recovery - Network Architecture
a. Firewalls, Routers, Switches, VPNs - Network Operating Systems
a. Active Directory, Domain Security, etc. - Host Security
a. Server and Workstation Operating Systems
Figure - SCADA Security Services Overview
Hardening of the SCADA environment - Protocol and services
Every SCADA system is based on commercial or open-source operating systems that can be attacked exactly in the same way as any other platform. It's crucial to assess all the services exposed, and the protocol adopted by removing and disabling unused services, and network daemons to reduce the surface of attack.
Every interconnection with other networks must be carefully analyzed, a risk assessment must include the analysis of possible impairment for exposed services. The system must be properly patched with updates provided by application providers to avoid the exploitation by hackers of known vulnerabilities.
In a service assessment the following services have to be carefully evaluated:
- Internet access
- Remote Assistance
- Email services
- Meter reading
- Remote billing systems
- FTP access
Numerous secure configuration guidelines for both commercial and open source operating systems are freely available online. They include documentation produced by the National Security Agency.
Another common approach to secure SCADA systems is the design and adoption of proprietary protocols for communications between control servers and field devices (e.g. Sensors, actuators). Unfortunately, secret communication protocols don't provide a great improvement in overall security. According to security experts, open protocols are more reliable and efficient, thanks to the support provided by numerous research environments that operate in the sector.
Security features and controls
An important aspect to manage during the life cycle of a SCADA system is the implementation of all security features proposed by SCADA vendors, in the form of updates or product patches.
Personnel in charge of SCADA maintenance and installation must be aware of the features enabled for their systems, and must be able to properly configure them. In many cases, it has been observed that newer SCADAs are deployed with basic security features, disabling security settings to ensure ease of installation, and to to provide maximum usability.
SCADA providers must be aware of the necessity of security features are mandatory to provide the maximum level of security and robustness of systems. Also, in these cases it's suggested that careful risk assessment of the consequences of reducing all the security features is needed.
Authentication and medium control
Investigation of past SCADA incidents demonstrated that mobile storage mediums are the main vectors used to infect control systems, despite that host networks are isolated from the Internet. Establishing strong controls on every medium used could prevent serious incidents and help to identify cyber threats in time.
Strong authentication must be implemented to ensure secure communication, and to allow personnel to access main functionalities provided by systems. The administration console for any network appliance must be protected. Wireless and wired connections to the SCADA network and remote sites must be properly defended. For example, in the effect of a successful "war dialing" or "war driving" attack, all radio and microwave links that are potentially exploitable must be secure.
It's necessary to identify and assess any source of information, including remote computer networks, phone lines, and fiber optic cables that could be tapped. For critical functions and the access to essential services, it's necessary to introduce outbound access mechanisms to commit requested operation.
To integrate the security of SCADAs, it's necessary to implement internal and external intrusion detection systems. The measure is necessary to mitigate cyber threats. It's desirable that malicious activities are quickly identified, and the proper response is applied to mitigate them. Incident response procedures must be in place, with knowledge shared with all personnel.
Another fundamental function is the auditing of system logs that must run on a daily basis to identify suspicious activities. The analysis could be supported by automated systems that are able to recognize patterns related to anomalous activities. The technical auditing of SCADA networks and devices are essential and it's possible to find numerous commercial open-source security frameworks to conduct audits of SCADA architectures.
SCADA vulnerabilities
Last year, the Pacific Northwest National Laboratory (PNNL), a federal contractor to the U.S. Department of Energy (DOE), in collaboration with McAfee have published an interesting report entitled "Technology Security Assessment for Capabilities and Applicability in Energy Sector Industrial Control Systems: McAfee Application Control, Change Control, Integrity Control."
[download]
The report provides an excellent picture of the current status of critical infrastructures, and the effort spent to identify and fix vulnerabilities. In particular, it analyzes the value and effectiveness of carefully integrated security solutions. They're necessary to support the national security mission to secure industrial control system environments.
This statement by Philip A. Craig Jr, Senior Cyber Security Research Scientist, a researcher within the National Security Directorate at the Pacific Northwest National Laboratory is very meaningful:
"When early critical infrastructure systems were created, neither security nor misuse of the interconnected network was considered"
"Today, we are still focused on enhancing the security of control systems. Outdated security methods that use a maze of disparate, multi-vendor, and stacked security tools will only delay a cyber attack, providing numerous opportunities for a more advanced and modern cyber adversary to attack cyber security postures throughout critical infrastructure."
The document proposes a list of principal vulnerabilities that have been identified for control systems environments:
- Increased Exposure: Communication networks linking smart grid devices and systems will create many more access points to these devices, resulting in an increased exposure to potential attacks.
- Interconnectivity: Communication networks will be more interconnected, further exposing the system to possible failures and attacks.
- Complexity: The electric system will become significantly more complex as more subsystems are linked together.
- Common Computing Technologies: Smart grid systems will increase use common, commercially available computing technologies and will be subject to their weaknesses.
- Increased Automation: Communication networks will generate, gather, and use data in new and innovative ways as smart grid technologies will automate many functions. Improper use of this data presents new risks to national security and our economy.
We've spoken of the possible vulnerabilities of control systems without considering the principal reason of concern for critical infrastructures, cyber warfare. Today, cyber attacks have evolved into sophisticated and carefully designed cyber weapons created with specific offensive intents. Stuxnet, Duqu and Flame are good examples.
Dr. Phyllis Scheck, Vice President and Chief Technology Officer, Global Public Sector, McAfee said:
"Infrastructures that control systems affecting our everyday lives, such as smart grids, are rising in adoption yet still lack the proper security needed to prevent sophisticated cyber attacks, "
"Achieving security by design is essential in securing critical infrastructure. Cybersecurity must be embedded in the systems and networks at the very beginning of the design process so that it becomes an integral part of the systems functioning."
What are the main solutions for preventing vulnerability exploitation?
After the discovery of government programs for the design of cyber weapons that are able to exploit vulnerabilities present in the control systems, many security firms and government experts have invested in projects for the defense of critical infrastructures. Today, there aren't cyber strategies that consider the strategic importance of cyber defense. To give an idea of the possible solutions implemented for defensive and preventive purposes, the PNNL report cites:
- Dynamic Whitelisting –Provides the ability to deny unauthorized applications and code on servers, corporate desktops, and fixed-function devices.
- Memory Protection – Unauthorized execution is denied and vulnerabilities are blocked and reported.
- File Integrity Monitoring – Any file change, addition, deletion, renaming, attribute changes, ACL modification, and owner modification is reported. This includes network shares.
- Write Protection – Writing to hard disks are only authorized to the operating system, application configuration, and log files. All others are denied.
- Read Protection – Read are only authorized for specified files, directories, volumes and scripts. All others are denied.
The identification of SCADA vulnerabilities is part of system management. It's important to implement proper countermeasures and take corrective actions as appropriate.
Security teams must be constantly updated on the bugs found for the specific model SCADAs, and must be aware of the availability of all necessary resources to exploit the flaws publicly available. I wrote about how easy it is for attackers to retrieve information on target SCADAs (e. g. Using Shodan search engine) and the malicious software to use for the attack.
Governments and private companies must be able to run simulations of attacks during exercises that have the intent of identifying potential attack scenarios and evaluating potential system vulnerabilities. The exercises must also consider the impact of accidental errors, and the effect of malicious insiders.
Physical security
Physical security is another aspect that must be properly managed. All plants that host SCADA systems and networks must be assessed. SCADA systems are usually distributed over large distances in multiple locations with different physical security measures. Their protection must be carefully evaluated. It's important to evaluate the overall infrastructure to identify weaknesses, evaluate defense measures to implement, and the expected benefits.
Best practices include the assessment of the physical security of remote environments that are directly connected to a SCADA.
"Any location that has a connection to the SCADA network is a target, especially unmanned or unguarded remote sites. Conduct a physical security survey and inventory access points at each facility that has a connection to the SCADA system."
Establish proper physical security through the adoption of defensive measures like guards and gates to protect equipment from unauthorized access and sabotage. Every external connection to the perimeter of the facility has to be assessed. It's suggested to use security products for perimeter protection that meet NIST FIPS standards.
Physical restrictions that could be applied to improve security to prevent incidents are:
- Restricted access to the site
- Restricted number of technicians responsible for maintenance
- No use of mobile support
- Segregated control network, no connection to other networks
- Each computer is locked in a restricted room or cabinet
Roles and responsibility – management
Management has a crucial role in security. Its primary task is to provide a strong commitment for the implementation of an efficient cyber strategy. That includes the assignment of cyber security roles, responsibilities, and authorities for personnel. Each employee needs to know their responsibilities to protect information and assets of SCADAs. Key personnel need to be given sufficient authority to carry out their assigned responsibilities. A detailed security policy must be in place that describes how management defines roles and responsibilities. Each employee must be informed of all procedures adopted to keep architecture secure.
The first goal of management is to define a structured security program with mandated requirements to reach expectations and provide personnel with formalized policies and procedures. Senior management must establish expectations for cyber security performance and hold individuals accountable for their performance.
Compliance with current security standards is necessary to provide a harmonious approach to cyber security. Policies and procedures need to be assigned to employees regarding specific security responsibilities. Guidance regarding actions to be taken in response to incidents and security policy must identify the critical systems within the SCADA network, their functions and classify the information they manage.
The security requirements must be identified within security policy to minimize cyber threats, including menaces from insiders. Personnel training is one of the most important responsibilities for management. Managers have to provide a strong commitment to organizing of training courses.
Training also helps to minimize the likelihood that organizational personnel will inadvertently disclose sensitive information regarding SCADA system design, operations, or security controls deployed.
Only the people involved explicitly need to have access to the above information. Personnel must be trained to recognize social engineering attacks made by hackers to gather sensitive information about a computer or computer network. Typically these attacks prelude more invasive and dangerous offensives. The more information revealed about internal configuration, the more vulnerable the network is. Keep secret data related to a SCADA network, including manufacturers, key people, computer operating systems and physical distributions of SCADA.
The responsibility of management is the definition of proper protection strategies, highlighting the risks related to cyber attackers and the necessary defense systems, for each component. The rapid and continuous evolution of cyber threats needs frequent revision of protection strategy to ensure it remains effective. Each risk must be evaluated, analyzing the probability of occurrence for the incident and the related severity. It's crucial that the identification of residual risk is accepted by management.
Configuration management processes and assessment
Configuration management is a critical component for the security of the infrastructure, for both hardware and software configurations. Each modification to the overall infrastructure could have a serious impact on its security. Changes could introduce vulnerabilities that undermine security.
"Configuration management begins with well-tested and documented security baselines for your various systems. Robust performance evaluation processes are needed to provide organizations with feedback on the effectiveness of cyber security policy and technical implementation. "
The impact of any modification of the infrastructure must be correctly evaluated with assessment processes conducted by both internal and external professionals. Routine vulnerability assessment and automated auditing of the network and systems must be part of the configuration management process.
The NSA document titled "Securing Supervisory Control and Data Acquisition (SCADA) and Control Systems (CS)" introduces the following suggestions for configuration management:
- Map out and document the entire CS network, including CS and infrastructure device configurations
- Prepare and configure new equipment off-line
- Sanitize old equipment before disposal
- Keep CS infrastructure security features current with device moves, additions, and decommissions
- Enable auditing features and periodically examine the resulting logs for signs of unusual activity
- Synchronize to a common time reference, so audit logs become more useful during incident response
- Develop a Disaster Recovery Plan (DRP) for the CS, and if possible test it!
System backups and disaster recovery plans
Recovery is the ability to restore a compromised system to its operational status. Establishing a disaster recovery plan is fundamental for rapid recovery from any incidents, such as cyber attacks.
System backups are an essential part of any plan and they allow rapid reconstruction of and network. Routinely exercise disaster recovery plans to ensure that the work and that all employees know the procedure to follow. Every change to the overall architecture has to trigger a review of the plan to apply the appropriate changes to disaster recovery plans.
Recovery plans usually include:
- Adoption of redundant hardware and fault tolerant systems
- Fallback mechanisms
- System backup procedure
The disaster recovery plan allows corporate to prepare for, respond to and recover from a disruptive event, including a cyber attack. The following criteria should be considered in case of a hardware failure:
- Determine and document the procedures for responding to a disaster that involves the SCADA center and its services.
- Acquire additional hardware for disaster recovery plan or locate current backup hardware to a different location.
- Periodically test the disaster recovery plan.
Related to software components, it's possible to follow the criteria below in case of malfunction:
- Determine ways to recover from any type of loss including historical data, installation media, application files, configuration files, documents, and software licenses.
- Establish a strategy to keep the system up-to-date.
- Evaluate the set of data and application to restore to its previous state in the event of a disaster.
- Create a centralized inventory of all software titles and licenses, evaluate the possibility to replicate it in different locations.
- Perform regular system backups and send copies of backup files to storage array networks off-site.
- Periodically test backup copied and restoring procedures operated by the personnel.
Conclusions
SCADA systems are increasing in complexity, due to the integration of different components, in many cases produced by different manufacturers. It's necessary to address the security level of each device and the overall environment. The design of SCADAs must totally change and have to take care of all the security requirements. That's done by considering their surface of attack and exposure to cyber threats that could arm the systems.
There must be a collective effort by all governments to produce continuous report on the security status of critical infrastructures and related SCADA systems. The overall security will pass through a global collaboration and information sharing on the possible cyber threats and the vulnerabilities of every device that is qualified in the market.
The security component must become part of the project of an industrial system. It must be considered a specific requirement. The overall security of critical infrastructures must be audited during the entire lifecycle of its components.
Recently the heads of the Federal Bureau of Investigation (FBI), Department of Homeland Security, and National Counterterrorism Center have declared cyber attacks are the most likely form of terrorism against the United States in the coming years.
"That's where the bad guys will go. There are no safe neighborhoods. All of us are neighbors [online]." FBI director James Comey said about cyberterrorism.
These words should make us think about the real importance of security for critical systems of our infrastructure, including SCADAs.
References
http://securityaffairs.co/wordpress/19604/malware/stuxnet-russian-nuclear-facility.html
http://www.sans.org/reading-room/analysts-program/sans-survey-scada-2013
http://energy.gov/sites/prod/files/oeprod/DocumentsandMedia/21_Steps_-_SCADA.pdf
http://www.oe.netl.doe.gov/docs/prepare/21stepsbooklet.pdf
http://news.bbc.co.uk/2/hi/7583805.stm
http://www.tsips.com/SCADA.htm
http://www.mcafee.com/us/resources/reports/rp-energy-sector-industrial-control.pdf
http://www.nsa.gov/ia/_files/factsheets/scada_factsheet.pdf
http://www.fortinet.com/sites/default/files/whitepapers/WP_SCADA.pdf
http://www.pnnl.gov/main/publications/external/technical_reports/PNNL-20776.pdf
http://www.nsa.gov/ia/_files/factsheets/scada_factsheet.pdf
Learn ICS/SCADA Security


