Google Hacking – For fun and profit - I
Google has been used ever since its beginning to find answers for most if not all of our questions from the beginning of the universe to even finding cure for common ailments. A BBC expert was found commenting that Google has the capability of finding your divorce lawyer to even the details of if you are pregnant. With so much intelligence built in to their systems, Google is surely a great information-gathering tool. As security analysts let's try to find out the proficiency of Google as a hacking tool in this article.
All of us have used Google for searching answers for our queries. What most of don't realize is the advantage of forming the search queries in Google to reveal sensitive information that we require to perform a successful attack. This can be accomplished by using the advanced operator features of Google. The basic syntax for using advanced operator in Google is as follows.

Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
Operator_name:keyword
The syntax as shown above is a Google advanced operator followed by a colon, which is again followed by the keyword without any space in the string. This put together becomes an advanced query to Google. The usage of advanced operators in Google is termed as dorking. The strings are called Google Dorks a.k.a Google hacks. Dorks come in two forms vis-à-vis Simple dorks and complex dorks. Using a single advanced operator as your search string is called as simple dork whereas multiple advanced operators put together in a single search string is called as advanced dork. Each keyword/advance operator has a special meaning to the Google engine. It helps you filter out the unwanted results and narrows your searches by a great margin when these dorks are used. Let's take few examples of simple dorks.
Simple Google Dorks:
Let's see an illustration as to what this really means. The following screenshot shall explain things in a better way showing a live example.
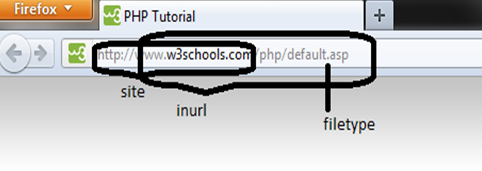
A single query can be used to get a particular result. But many single queries can be put in to one monster query and higher degree of filtration can be achieved resulting in the same particular page in your search results.
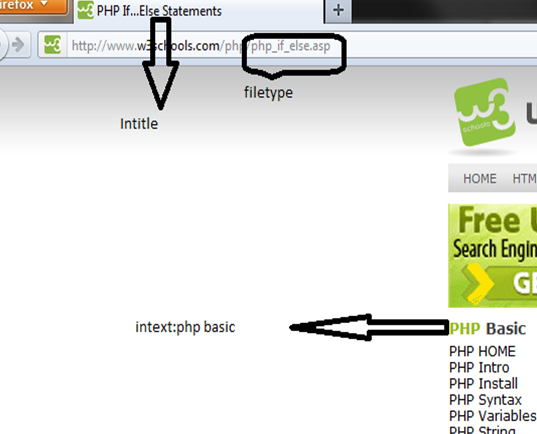
The above two diagrams illustrate few of the dorks in a pictorial manner. The same can be analogous to other advanced operators. So what can we find out using Google?
-
Admin login pages
-
Username and passwords
-
Vulnerable entities
-
Sensitive documents
-
Govt/military data
-
Email lists
-
Bank account details and lots more
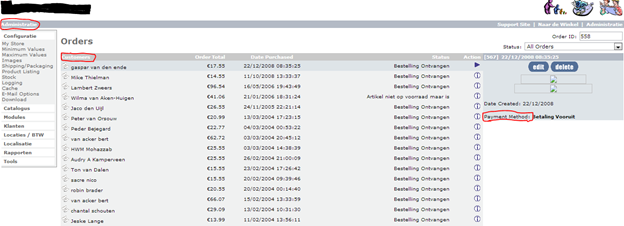
The list goes never ending. We shall try to explore few of these possibilities in this article. In the screenshot below, we are seeing an admin catalog with detailed information of the customer names, payment methods, and order amounts. This information can be handy when performing social engineering on random targets.
Dork: filetype:php inurl:catalog/admin/
This is an example of a simple query. Next, let's see some juicy stuff, which comes in handy due to the efficiency of Google crawlers.

Dork: inurl:group_concat(username, filetype:php intext:admin
In the above screenshot, we were able to tap in to some of the SQL injection results done by somebody else on the sites. Unfortunately, the residue is still left in the search results. We happened to get our hands on username and password combinations, one of the accounts listed with the md5 hashes had the hash cracked, and the following combination was uncovered. The combination is bcheramy : 130270
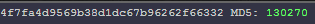
The search results took, 0.25 Google seconds to appear. Does this mean we hacked an account in 0.25 seconds Google time? ;)
By now, I am sure; you would have got an idea as to how dangerous a tool Google can be. The usernames and passwords got from here can be used to strengthen our dictionary attacks by adding these used passwords to the list we already have. This can also be used in user profiling which seems to be in demand in the underground market. The above queries where just simple dorks which gave out sensitive information.
When testing a target we would like to test it from all perspectives and try to gather information from all possible means. In this section, we shall see how Google can be used to troll email addresses across the internet. This gives spammers a huge list of emails that they need in succeeding their goals. In 0.21 seconds Google time, I was able to get a excel sheet with 1000 email ids. This was just one of the results. Imagine if I had checked all the results or if I had automated this process then I would have million email ids listed in no time!
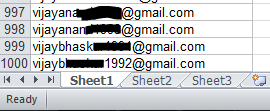
Dork: intext:@gmail.com filetype:xls
Other capabilities of Google include site crawling/Network mapping. We use few other keywords to achieve this feat. What is so special about site crawling/Network mapping i.e. enumerating domain and hostnames? Well, all this is done without any probing at the target. The target that you are trying to enumerate cannot get a hint that you have already started plotting your attack against it. Google APIs used with a script combined with search results can give a big boost in this part of your attack. Let's see some example for the same.
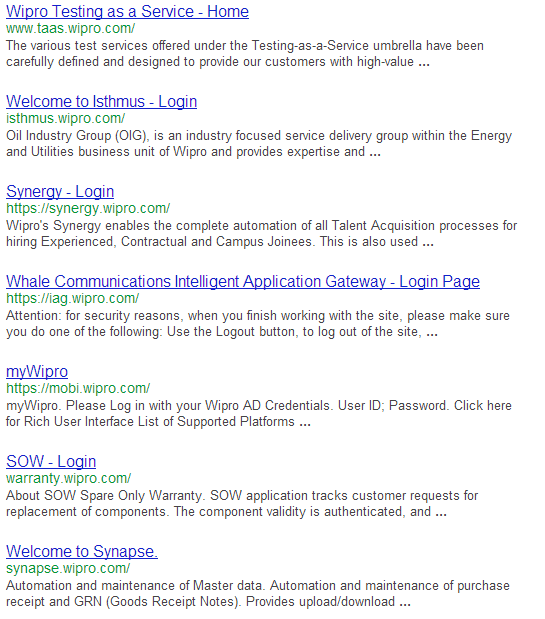
Dork:
In the above example, you can see the usage of multiple simple dorks. Well, this is the negation operator provided by Google. The negation operator helps you subtract unwanted results from the search. The explanation for the above dork is as follows: Search the site wipro.com excluding the main site (www.wipro.com) and also exclude the subdomain (careers.wipro.com). In the search results, we are able to see few login pages. As every one of us is aware that, an organization's security is as strong as its weakest link (quoted from a blackhat-euro presentation), finding these third party logins and links allows an attacker to gain trusted entry into the target if these have some loopholes in them!
Another key word that I want you to try would be the Link operator whose usage is similar to that of site. A link to a site doesn't really carry much importance to an attacker, but a link from a site would mean that there is some form of trust connection between the two sites. Link command in Google can be used for finding external links to a site from another site.
The possibilities for automation and network mapping using Google are infinite. Once you get used to using Google for mapping your targets I bet you will be amazed at the possibilities you have given birth to. :D
Crude port scanning by Google can be done by intelligent use of dorks in the search string. The following screenshots gives a fair idea as to how it can be achieved.
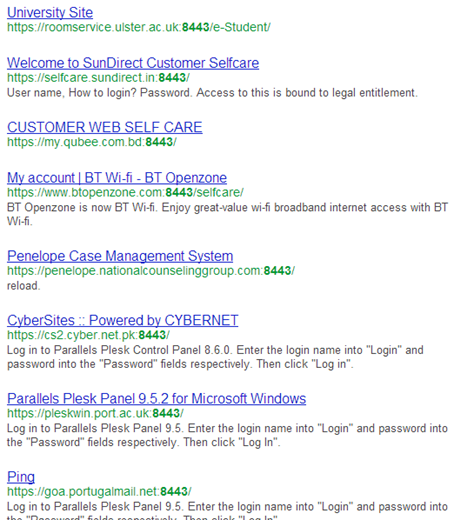
Dork: inurl:8443 -intext:8443
This dork lists all the sites running on port 8443. The query calls for sites with 8443 in the URL but excludes the redundant occurrence of 8443 in the text body thereby giving us URLs with respective ports. An automated scan on important ports can give interesting results.
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.
In this article, we have seen a few common uses and some uncommon uses of Google dorks in getting some sensitive information. As said earlier the possibilities with Google are limitless. The limit is given by your creativity. There are lots more interesting details that Google can provide you. But I am storing them for the next installment of the article on Google hacks! Until then happy Googling :D