Cybersecurity Weekly: "Nice guy" hacker attacks Tom's, programmer hacks hackers, 60,000 records breached after phishing incident
A hacker encourages others to spend more time outside. A hacked programmer retaliates by hacking hackers who hacked him. A phishing incident results in a leak of personal information for 60,000 patients. All this, and more, in this week’s edition of Cybersecurity Weekly.

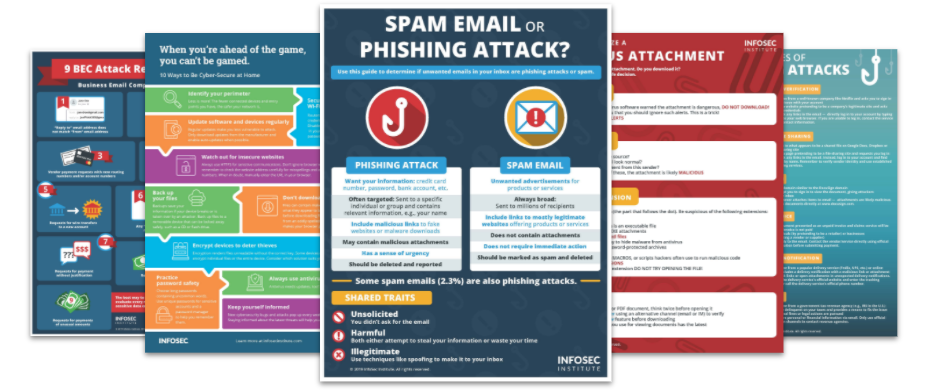
Top Security Awareness Posters
1. Toms Shoes' mailing list hacked to tell users to log off
A self-proclaimed "nice man" hacked Toms Shoes' email newsletter list last week. The hacker told journalists that the hack of Toms was easy, but shared no details about how it had occurred. What he did share was a strong message against those who hack with more malicious intent.
Read more »
2. Hackers bypassing some types of 2FA security
Last month, the FBI warned U.S. companies that some types of two-factor authentication (2FA) security are not guaranteed to keep attackers out. The most popular bypass is SIM swap fraud, where the attacker convinces a carrier to port the target’s mobile number, allowing them to receive 2FA security codes via text message.
Read more »
3. Iran-linked “Charming Kitten” touts new spearphishing tactics
An Iran-linked advanced persistent threat group tied to attacks on President Trump’s 2020 re-election campaign has added new spearphishing techniques to its arsenal. The group — dubbed “Charming Kitten” — has escalated its volume of phishing attempts, as well as adding four new impersonation vectors to its campaign.
Read more »
4. Hacked programmer retaliates by hacking hackers who hacked him
Germany-based programmer Tobias Fromel was affected by Muhstik ransomware a few months ago. In retaliation, he recently released around 3,000 decryption keys as well as the free decryptor software, which he acquired by hacking the hacker behind the ransomware. In an interview, he said he did this to help others who were attacked by the ransomware.
Read more »
5. Phishing incident exposes medical, personal info of 60,000 patients
Community-based healthcare system Methodist Hospitals from Gary, Indiana, disclosed that sensitive personal and medical information for 68,039 individuals may have been exposed. On August 7, a forensic investigation determined that two Methodist employees fell victim to a phishing attack that resulted in unauthorized access to their email accounts.
Read more »
6. Twitter users’ 2FA info found its way to advertisers
This week, Twitter disclosed that it gave advertisers access to email addresses and phone numbers that users had supplied to the social media platform for two-factor authentication purposes. The company is asserting that this practice was inadvertent, and that the company does not know how many people were impacted by this incident.
Read more »
7. Alabama hospitals pay up in ransomware attack
An Alabama hospital system has paid its attackers in a ransomware incident that knocked its systems offline on Oct. 1. Officials at the DCH Health System didn’t say how much they paid for the decryption key, but noted that they have started a “methodical” process of system restoration.
Read more »
8. Credit info exposed in TransUnion data security incident
An unauthorized person was able to gain access to a TransUnion web portal and pull consumer credit files from it. This was done by using credentials stolen from a TransUnion customer who had access to the portal. Starting last week, TransUnion began sending out data security incident notifications to consumers whose information was accessed via the unauthorized login.
Read more »
9. UNIX Co-Founder Ken Thompson's BSD Password Has Finally Been Cracked
A 39-year-old password of Ken Thompson, the co-creator of the UNIX operating system, has finally been cracked. It belonged to a BSD-based system, which was used by various computer science pioneers several decades ago. Thompson's password has been revealed as "p/q2-q4!a" — a notation in chess to describe the move "pawn from Queen's 2 to Queen's 4."
Read more »
Phishing simulations & training
10. RobbinHood ransomware using street cred to make victims pay
Operators behind the RobbinHood ransomware have updated language used in their ransom note to remove all hopes of free file decryption. In their message, the cybercriminals pointed to past incidents involving their ransomware, which ended in victims paying much more than the ransom demand.
Read more »




