Cybersecurity Weekly: Cybercrime-fighting dog, cancelled Netflix accounts hacked, TLS phishing bait
The Midwest gets its first cybercrime-fighting dog. Dead Netflix accounts are getting reactivated by hackers. Cybercriminals are now using green TLS padlocks as phishing bait. All this, and more, in this week’s edition of Cybersecurity Weekly.

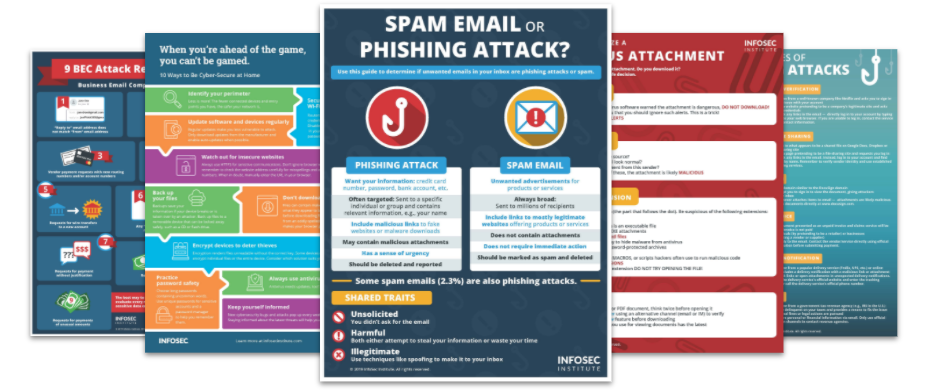
Top Security Awareness Posters
1. Midwest gets first cybercrime-fighting dog
Bellevue, Indiana hired the Midwest’s first ever cybercrime-fighting dog to the city’s police force last week. Officer Quinn, a two-year-old black Labrador, is responsible for sniffing out a certain chemical used in electronic storage devices. She can detect devices 18 inches under a wall and through 18 inches of water.
Read more »
2. Santa hacker speaks to girl via smart camera
Video showing a hacker talking to a young girl in her bedroom via her family's Ring camera has been circulating on social media this past week. Amazon said the incident was not related to a security breach. Instead, the incident was a result of a password stuffing attack, in which the hacker reused credentials found in an unrelated breach.
Read more »
3. Dead Netflix accounts reactivated by hackers
Hackers have exploited Netflix's data retention policies to reactivate cancelled customer subscriptions and steal their accounts. Former subscribers noticed a monthly fee months after cancelling their service. This is due to the streaming service storing customer data, including billing information, for ten months after cancellation.
Read more »
4. Green padlocks now used as phishing bait
Cybercriminals have started to find more elaborate ways to steal credentials, such as using free certificate issuing authorities like Let’s Encrypt to lull the victim into a false sense of security. To defend against this phishing tactic, users must not only look for the green TLS padlock but also at the URL to ensure familiarity with the site.
Read more »
5. Another ransomware will now publish victims' data if not paid
The operators of the REvil ransomware announced they will use stolen files and data as leverage to get victims to pay ransoms. While this has been threatened in the past, only recently have ransomware operators followed through. REvil goes on to say that this would be more costly to the victim than paying the ransom.
Read more »
6. Flaw in Elementor and Beaver addons let anyone hack WordPress sites
Security researchers discovered a critical authentication bypass vulnerability in the Elementor and Beaver Wordpress plugins. This vulnerability could allow a remote attacker to gain administrative privileges on a site without the need for a password. Some attackers have already started exploiting this vulnerability within two days of discovery.
Read more »
7. AirDoS attack could make iPhones, iPads unusable via AirDrop attack
The denial-of-service technique allows the attacker to remotely render any nearby iPhone or iPad unusable. It relies on the AirDrop feature that allows Apple users to share documents, photos and files with nearby devices via Bluetooth or Wi-Fi. Researchers demonstrated the possibility to use an AirDoS attack to “infinitely spam” all nearby devices with an AirDrop popup.
Read more »
8. The great $50 million African IP address heist
A top executive at the nonprofit entity responsible for distributing public IP addresses to African organizations resigned last week. This announcement follows accusations that he secretly operated several companies which sold tens of millions of dollars worth of IPv4 addresses to online marketers.
Read more »
9. Data leak exposes 750,000 birth certificate applications
Over 750,000 birth certificate applications have recently been exposed online, according to a report by a penetration testing company. The data was found on an unprotected AWS server, and included sensitive personal information such as name, date of birth, current home address, email and phone number.
Read more »
Phishing simulations & training
10. Ransomware targets healthcare and IT sectors in U.S. and Europe
Cybercriminals are using a new strain of ransomware dubbed Zeppelin against healthcare and IT companies in The United States and Europe. Zeppelin actors appear to have “carefully chosen” their targeted organizations in a campaign that dates back to at least November 6, 2019.
Read more »




