10 Benefits of Threat Hunting
Introduction
Organizations are constantly being challenged by an increasing number of cybersecurity threats. As the severity and frequency of attacks rise, there is a call for a more proactive approach: threat hunting.
Threat hunting incorporates tools-based and human-driven detection to fend off computer-related cyberattacks. This is rapidly becoming a key function for modern security operations centers (SOCs) that employ cybersecurity “hunters” to spot suspicious behavior within areas of a network and, through threat analysis, prevent or uncover security incidents or weaknesses that might otherwise go undetected.
Become a certified threat hunter
“Proactive threat hunting” is one of the newest offensive strategies that Managed Services Providers (MSPs) and enterprises alike are employing and is proving to be a great threat intel gathering method. Consequently, there are more organizations who now have a dedicated threat-hunting platform in place to address emerging cyber-related threats. In fact, the 2018 Threat Hunting Report from Cybersecurity Insiders (sponsored by Alert Logic) shows “60% of organizations surveyed are planning to build out threat hunting programs over the next three years.” Doing so, “more organizations are moving away from traditional reactive security while incorporating threat hunting techniques in their cybersecurity strategy.”
Threat hunting is quickly becoming a favorite in many companies’ security programs, as it ensures a level of situational awareness that other methods might not reach so quickly. Setting up a threat-hunting framework can be highly effective in protecting critical infrastructures against cyberthreats and any suspicious activity, incidents and vulnerabilities. Hunters can assess risks and test security controls.
If adding threat hunters to some team or training existing personnel is not an option, companies are also considering Threat Hunting-As-A-Service (THaaS) to reap the benefits of services such as “hunting health checks” without adding HR overheads. Getting started is often deemed as one of the toughest parts of hunting, so employing a THaaS vendor might be beneficial to help launch a program that involves both a manual and a semi-automated scanning of systems.
The Threat Hunting Advantages
Proactively Uncover Security Incidents
Threat hunting is used to become aware of hidden threats (e.g., malware) lurking in the background and, ultimately, identify perpetrators who are already intruding in the organization’s systems and networks. It can help to proactively identify adversaries who have already breached the defenses and found ways to establish a malicious presence in the organization’s network. Hunting is used to stop the current attackers.
Improve the Speed of Threat Response
Threat management remains the top challenge for SOCs, as per the Threat Hunting Report by Crowd Research Partners. Threat hunting’s course of action is searching through networks for indicators of abnormal behavior caused by potential attacks; this entails a human-driven process designed to look for the threats that automated systems or conventional detection methods might miss. Ad-hoc hunts can identify a particular activity or attack pattern that might already be present in an IT environment, and identify it more quickly .
And the quicker active threats are identified and communicated to an incident responder who will “have the knowledge and experience to quickly respond to the threat and neutralize it before more damage to network and data occurs,” the better the outcome.
Reduce Investigation Time
Threat hunting also allows a security team better insight on an incident, from understanding its scope to identifying the causes and forecasting the impact. An active approach, analyzing computer network traffic in search of malicious content with intent to investigate potential compromises and improve cyberdefenses, can help gather essential data to investigate after-the-fact incidents. This will assist in extracting lesson-learned tips and correcting possible issues.
Aid Cybersecurity Analysts in Understanding the Company
Threat hunting is not only an ideal strategy to intercept possible advanced persistent threats (APTs) or other external attacks that can leave an organization vulnerable to data breaches. It also gives IT analysts a much better overall picture of the current state of the organization’s security, and its expected resilience to a variety of attacks.
Through threat intelligence, it is possible to further anticipate identification of a specific threat, providing analysts and incident responders with actionable intelligence: information which is analyzed, contextualized, timely, accurate, relevant and predictive.
Help Achieve Appropriate Mitigation of Threats With an Improved Defense System
Threat hunting makes it possible for early detection of advanced threats (hidden, unknown, and emerging), and thus for cybersecurity teams to secure and defend their environments. Thanks to the deepened insight into the systems and the ways a threat found their way in, a good threat-hunting session also offers more information to improve the defenses of a company.
Forces the Company to Have Specialized, Skillful Professionals on Their Team
Once the decision is made to begin implementing threat hunting in-house, a company needs to look into employing professionals with skills and knowledge that go beyond basic IT. A threat hunter needs to be an expert in IR, forensics, cybersecurity or network engineering and security analytics as well as network protocols, malware management and reverse engineering. Moreover, they’ll have to be creative and possess critical-thinking and problem-solving skills, as well as much of the know-how and abilities that malicious hackers possess.
These professionals normally have a passion for learning and keeping abreast of the newest cybersecurity trends. They’ll in need to have advanced communication skills to communicate findings and write effective technical reports that non-technical management personnel can understand. An organization can only benefit from these additions to the IT team.
Brings SOCs Into the Future
An efficient threat-hunting platform includes valuable tools and is essential for security operations centers (SOCs). Tools like security information and event management (SIEM) software products or an intrusion detection system (IDS) may well be used to help identify anomalies, leading to more efficient identification of threats and giving the ability to counteract them. This will help prevent or minimize further damages.
A good platform, however, also includes quick and effective ways to transform raw data coming from a variety of sources into usable information. It can even save time for analysts by freeing them from having to manually correlate events; it can aggregate “feeds” coming from different sources in order to create actionable intelligence data.
Reduces False Positives and Improves SOC Efficiency
Hunting’s strength is that it is human-driven, proactive, iterative and analytical. This combination of tools, repetitive monitoring and behavior-pattern searching, together with the analysts’ ingenuity and ability to examine and evaluate data, means a reduction in false positives and time-wasting.
Reduces Damage and Overall Risk to the Organization
Threat hunting offers a faster response and a proactive approach, which normally means less possibility for malicious intruders and threats to damage to an organization, its systems and data.
Understanding the Organization’s Threat-Discovery Maturity
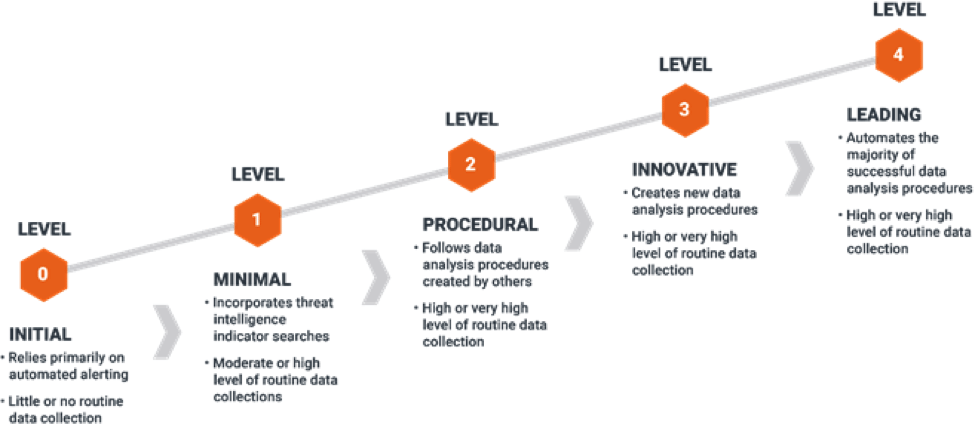
Sqrrl’s security technologist and hunter David Bianco has developed the Hunting Maturity Model (HMM), which describes the five levels of organizational hunting capability ranging from HM0 (the least capable) to HM4 (the most capable). A resource like this is a great way for a company to understand where they stand on the road to proactive resilience. “The HMM can be used both to measure their current maturity and provide a roadmap for improvement,” mentions Bianco. The diagram is shown below.
Conclusion
Threat hunting has proven itself to be very effective and is gaining momentum as companies look for better ways to increase their security posture and eradicate malware and persistent threats. As emerging and advanced persistent threats (APT) continue to challenge SOC staff, analysts are increasingly utilizing threat-hunting platforms to uncover attacks. Because 100% detection is impossible to achieve, and since existing security measures and solutions like IDS and SIEM are simply not enough anymore, there is a growing need to establish security teams who will actively “hunt” for threats targeting their organization.
Cyberthreat Intelligence activities, in particular, enable teams of analysts to focus their resources in order to achieve maximum effect, while they anticipate threat identification using a threat-hunting approach. It’s a strategy which is shifting from reactive (in response to attacks) to proactive, with companies looking for ways to deal with issues in a faster, more efficient way — and to gather enough data to prevent further issues and build stronger (albeit budget-conscious) defenses.
Sources
2018 Threat Hunting Report, Alert Logic
How threat hunting enhances cybersecurity, GCN
Successful Threat Hunting in ICS Networks, Cyber Resilience Blog
The Benefits and Challenges of Threat Hunting, Alert Logic
Threat Hunting Report, Crowd Research Partners
Threat Hunting: The What, Why and Who?, Demisto
The Hunter or the Hunted? Cybersecurity Threat Hunting 101, Herjavec Group
Cyber Threat Hunting, Elasticito
Threat Hunting: Fad or Essential Cyber Security Tactic?, Infocyte
Who wants to go threat hunting?, CSO Online
Hunt Evil: Your Practical Guide to Threat Hunting, ThreatHunting.net
Is Threat Hunting-As-A-Service (THaaS) for you?, Sqrrl
An Introduction to Cyber Threat Hunting, Sage Data Security
‘Threat Hunting’ On the Rise, Dark Reading
LIFARS. (n.d.). WHITE PAPER: CYBER THREAT HUNTING DETECT ADVANCED THREATS HIDING IN YOUR NETWORK. A guide to the most effective methods.
Become a certified threat hunter
Sqrrl Data, Inc. (2016). WHITE PAPER: A Framework for Cyber Threat Hunting. Retrieved from https://sqrrl.com/media/Framework-for-Threat-Hunting-Whitepaper.pdf