Security Assessment of Blackberry Applications:
Development of mobile applications have picked up really fast in the last couple of years. Much has been written about the security assessment of iOS & Android applications, however much information is not available for the security assessment of blackberry applications. The aim of this paper will be to understand different types of blackberry applications, give brief information on the technological platforms used to develop them and discuss security issues that can crop up in them.
We'll first understand more about technical platforms supported by blackberry for the development of software. Then we'll understand different types of blackberry applications.Additionally, we'll develop a little more understanding on how client-server applications work over HTTP, as these applications will be our area of focus.

11 courses, 8+ hours of training
Blackberry supports the following development platform:
- C/C++
- Java
- Adobe Air
- HTML-5
Additionally, it also supports some popular frameworks such as jQuery mobile, dojo, etc…
Blackberry applications (or any mobile app for that matter) can be categorized into two major categories:
1. Standalone Application:
Standalone applications are thick clients which, when installed on a blackberry device,functions independently on the device. These kinds of applications do not need network connectivity, as their sole function is to run independently on mobile device.Example of such applications can be games, calculators, notepads, etc.
Security Assessment of Standalone applications:
To perform a security assessment of a standalone application, one has to reverse engineerthe application's binary. Blackberry application's executable files are of proprietary format.Normally, blackberry applications have the extension *.cod. COD files are structured as per RIM's JVM specifications (which again is proprietary). Reversing a proprietary executable is out of the scope of this document.
2. Client Server Application:
These kinds of applications have the client portion of the application installed on the mobile device. This client application talks to main processing component which is hosted on remote server. The protocol of communication between the client and server may differ based on the technology used. Focus of this article will be on applications that use the HTTP protocol.
Security Assessment of Client Server applications using HTTP Protocol:
Pre-requisites:
We need to get our environment ready first.The following section will explain,in detail, what are the steps needed for setting the environment.
Setting up the environment:
We need one of the following installed on our machine to start with.
-
Blackberry Java Development Environment (JDE)
OR
- MDS Server & Blackberry Simulator
-
Blackberry JDE:
Blackberry JDE is a single shot solution for all our needs. If we set this up correctly, all our requirements are addressed. We will explain this step in detail.However, users can choose to install MDS & Blackberry Simulator individually as well, without much problem.This step has a dependency. Java Development Kit version 1.5 or above should be installed for Blackberry JDE to work. You can download the latest version of JDK here: http://www.oracle.com/technetwork/java/javase/downloads/index.html
The following steps will demonstrate how JDK needs to be installed
Installing JDK:
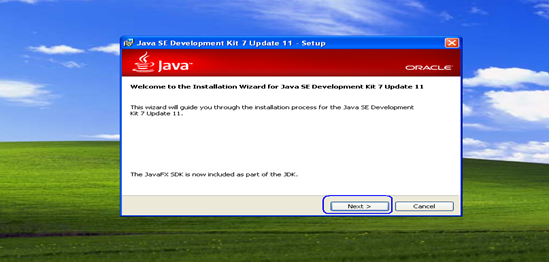
Step 1: Launch the JDK Installer
Once the JDK is downloaded from above mentioned URL, double click the executable to launch the installer. We should see the following screen, once the installer is launched.
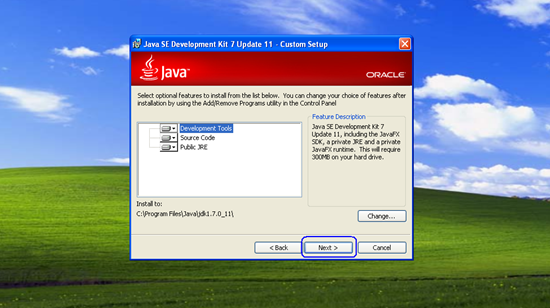
Step 2: Choose Features
We can choose what features we want to install. The right side pane provides more information on each feature. Clicking on the feature will open up a drill down and allow us to choose expected features.We will go with default configuration and click next to move to the next step.
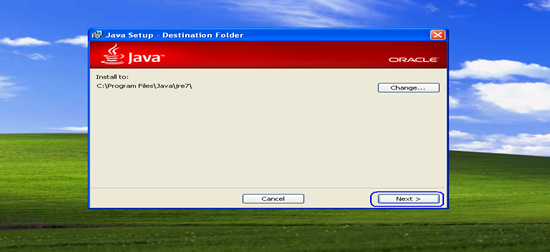
Step 3: Choose JRE (Java Run Time Environment) Installation Folder
A copy of JRE comes bundled with the JDK. In this step, we need to choose the directory in which JRE needs to be installed. You can leave default configuration and click next to move to the next step.
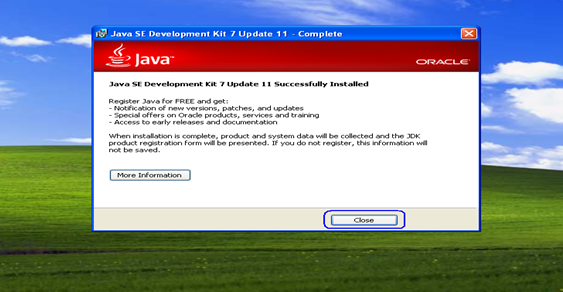
Step 4:Successful Installation
We will see the installer copying files on our destination directory and once the copying of files is completed, the JDK installation is completed and we should be able to see screen as follows:
Download Blackberry JDE:
Once the JDK installation is completed, download the blackberry JDE from here: https://developer.blackberry.com/java/download/#jde
Install Blackberry JDE:
Launch the installer and follow the steps below. The process is straight forward for XP users, however there have been problems reported for Windows 7 users.
The following steps demonstrates how to install Blackberry JDE:
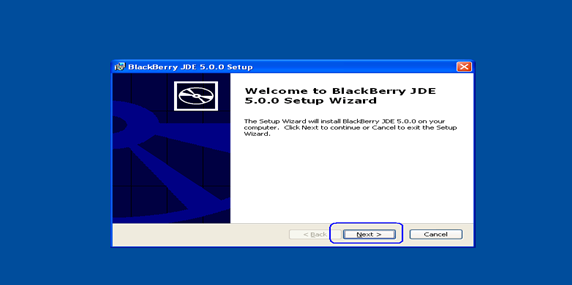
Step 1:Launch the Blackberry JDE installer
We will use Blackberry JDE version 5.0.0 for demonstration in this article, however you can use any other version. There may be additional dependencies if newer versions of JDE are chosen for installation.
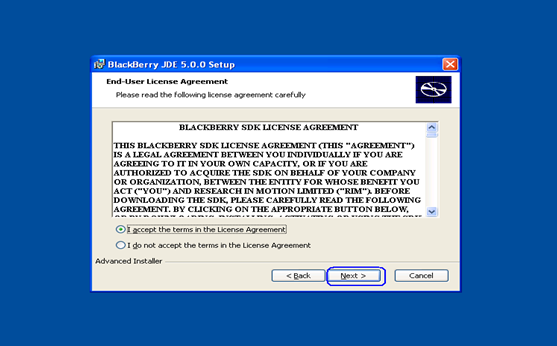
Step 2:Accept Terms & Conditions
Select the "I accept" radio button and click on next.
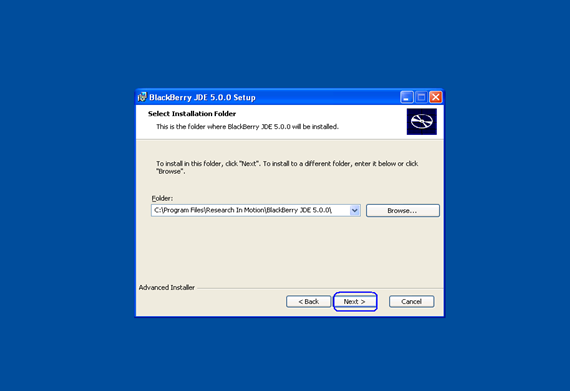
Step 3:Choose Installation Folder
Leave the installation path as defaultand click on next.
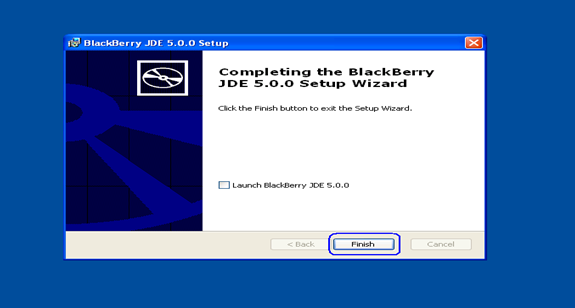
Step 4:Successful Installation
The installer will copy the files in the installation folder and once the copying is completed, our installation is completed. Click Finish and we are done with our environment set up.
Challenges for Win7 users:
I'd like to add some notes for Win 7 users here though – as I faced some challenges in getting the environment to work on Window 7.
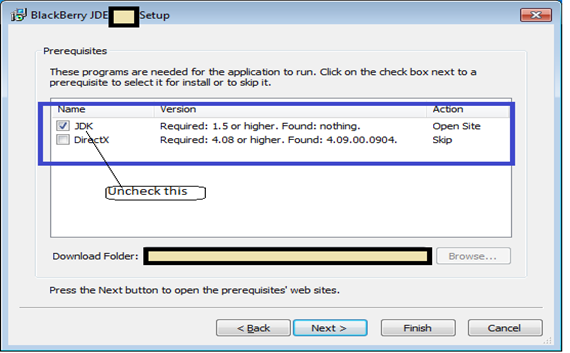
Windows 7 JDE installer, when launched, fails to identify the JDK even if JDK is installed on the machine and hence asks to download it from the website. You can skip that step as shown below, if the JDK is already installed on your machine, uncheck the checkbox in following figure and click on Finish.
Even after successfully installing the JDE, the MDS server just didn't work and quit as soon as I launched it. "Classpath" needs to be tweaked a little to get the MDS server to launch successfully. I faced some issues with installation on C: drive and migrated the entire installation set up on D drive, including the JDK. This did the job for me.
-
MDS Server & Blackberry Simulator
Since we have already covered the JDE installation in detail, we'll not explain installation of the MDS server and Blackberry simulators step by step. Downloading and installing these two components is straightforward and simple. Just ensure that JDK is installed as demonstrated in detail previously, as it is a dependency for MDS Server.
-
MDS Server:
Blackberry Mobile Data System (MDS) is a framework for application development. Applications can use MDS Connection Services component for sending HTTP Requests and handling the responses received. It supports TCP/IP as well.
-
Download and install a blackberry simulator on which the application can be deployed.
Intercepting HTTP Traffic between Simulator and Server:
The next step is to intercept the traffic. Blackberry applications security assessment is similar tothe security assessment of web applications, however,there are some differences. In web applications security assessment, the proxy configurations are done in the security auditor's browser when he access's the application, however in case of Blackberry applications, these changes have to be performed in the MDS server's configuration file.
Since MDS is used for opening network connections, the traffic is routed through MDS servers every time, hence setting the proxy server in the MDS server's configuration files will do the job. Blackberry Simulator's Browser will also use the MDS server to route the traffic. Therefore, once the proxy is configured, we can even trap browser traffic.
There are 2 major steps in intercepting the traffic. One is updating the MDS configuration file with the proxy details and second is to configure the local proxy to run on the appropriate port number.
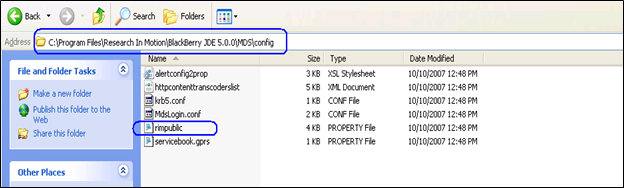
To configure the MDS server's configurations,navigate to the rimpublic.property file. You should be able to find it in following path if you installed the JDE on C: drive. The path should be something as follows:
"C:Program FilesResearch In MotionBlackberry JDE #.#.#MDSconfig"
In above path(s) - #.#.# stands for the version of the Blackberry JDE (e.g. 5.0.1). Your actually folder structure should be something like this:
Intercepting the traffic is a very important step and is easier said than done. At times,intercepting mobile application's traffic can be really painful.There have been situations where applications just bypass proxy settings and communicate with the internet directly.
In the "rimpublic.property" file, navigate to the section [HTTP_HANDLER] and addthe following lines at the bottom of existing configuration.
application.handler.http.proxyEnabled= true
application.handler.http.proxyHost= localhost
application.handler.http.proxyPort= 8888
An updated copy of "rimpublic.property"file should look like following:
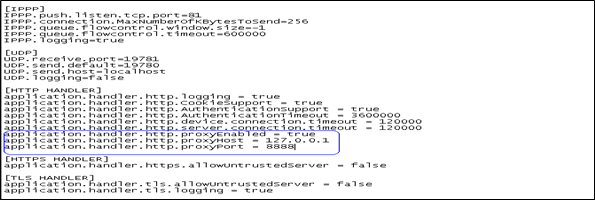
The syntax of above mentioned directives is case sensitive.
It should be noted that all proxies cannot handle mobile traffic. For example: Paros did not work for me, however burp did! Generally, it is a good idea to go with burp, as it handles most types of traffic.
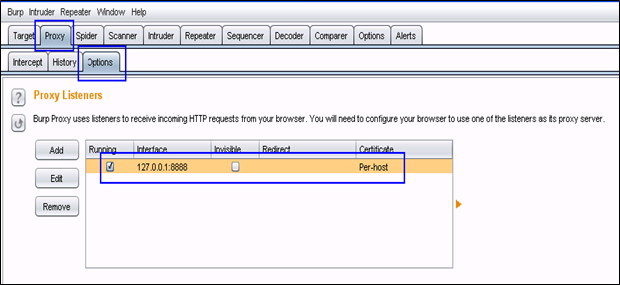
The second important thing to note is the port number on which we configure Burp. Burp runs on port 8080 by default andyou need to modify it to listen on 8888 in order for above configuration to work. The reason I prefer running burp on 8888 is because the MDS server will run on 8080. The operating system software does not permit running more than one service on a single port; hence attempting to run burp on 8080 can trigger errors if the MDS server is already bound to that port or vice versa; the MDS server may face issues if 8080 is occupied by burp. Running burp on 8888 will resolve this conflict.
Let's configure Burp to run on 8888. The figure below shows how the interface should look after it is configured to run on 8888. Incase Burp is showing port number as 8080 for you, click on Edit and update the port number field with 8888. Once you click OK, the listening interface should look something as it does here:
That's all – now we are all set. We can launch the blackberry MDS Server &Simulator and start our assessment. We should be able to trap all HTTP traffic, whether it is generated by browser or by the application installed on Blackberry simulator.
Start Burp and then launch the MDS server as shown in following figure:
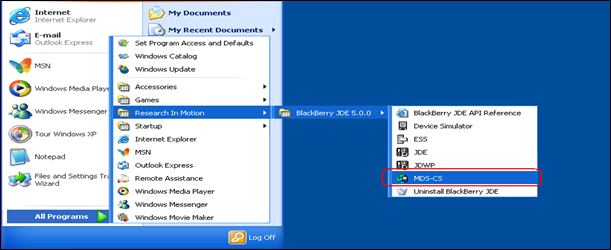
You can also invoke the MDS server by launching the "run.bat" file located in MDS folder. Make sure that "rimpublic.property" is updated before launching MDS server. Once successfully launched, the MDS server should look as follows:
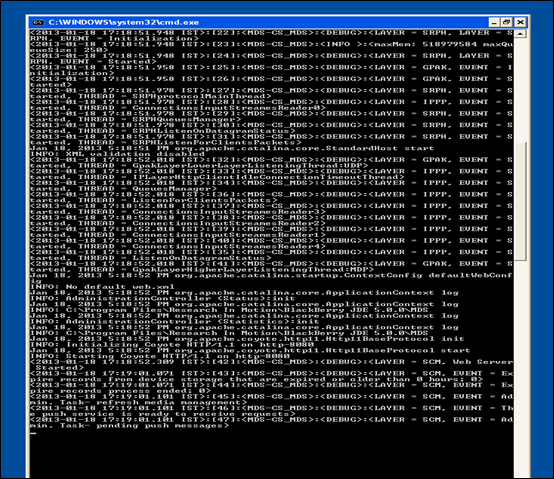
If you are unable to launch the MDS server successfully as shown above or if the command prompt quits unexpectedly, set the following environment variable, as this issue can be because of CLASSPATH.
To set the CLASSPATH environment variable,right click on the My Computer Icon appearing in the Start Menu& Click on Properties. Navigate to the Advanced Tab > Environment Variables > System Variables. Create a New Variable and key in the values as shown in the following figure. Click OK to create this variable. Launch the MDS server now and it should work as expected.

Now launch the simulator as shown in following figure:
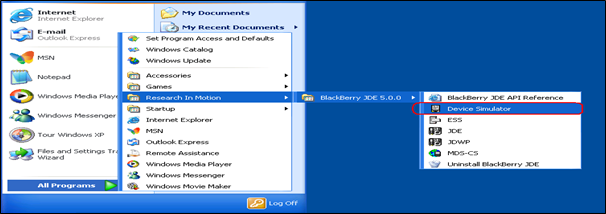
Once the simulator is successfully launched, open the browser to check if we are able to intercept the traffic between the simulator and the server. If we are able to intercept the traffic for the Simulator's Browser generated HTTP requests, it should work for applications as well (Unless the app uses TCP/IP or if it does not use MDS itself for connecting to the server).
Let us launch Google.com from the Simulator's browser to check if we are able to intercept the traffic.
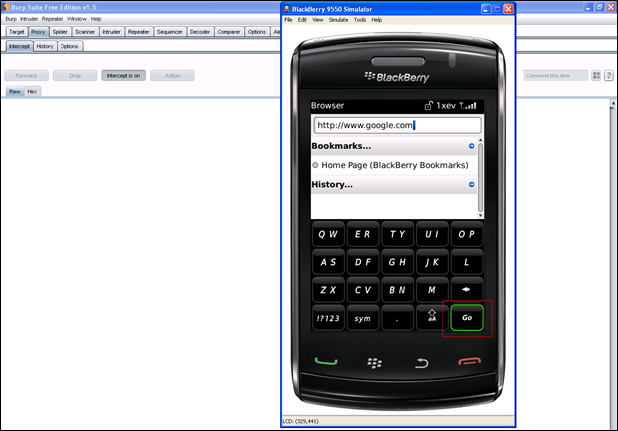
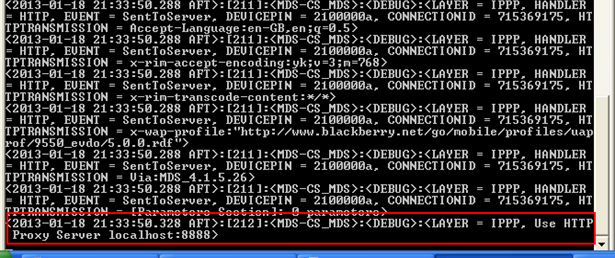
Click on GO button and keep Burp on "Intercept On" mode. We should be able to see it in the MDS server window when the HTTP request is transmitted to the proxy server. The following figure shows the snap shot of the MDS server, which shows a request is being sent to our Burp proxy:
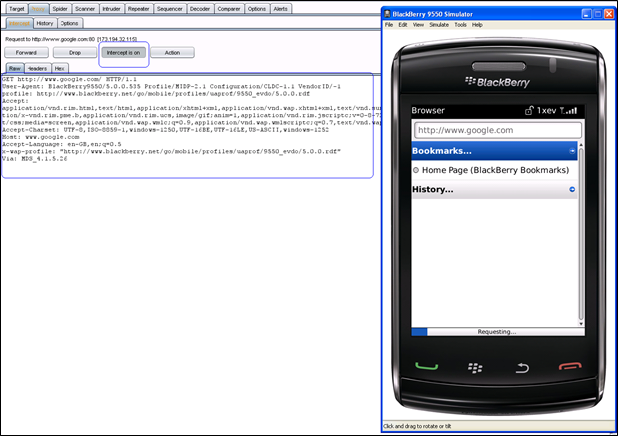
The following screenshot shows how that our request is trapped in Burp:
What next:
We can perform a security assessment of backend applications which cater to the mobile client or mobile browser's request. If the backend application is not performing input validation properly, security issues that affect normal web based applications can plague mobile applications. Vulnerabilities can include issues like SQL Injection, XML Injection,Cross Site Scripting, Cross Site Request Forgery, etc…

11 courses, 8+ hours of training
References: