MetaData and Information Security
Information security and penetration testing is not limited to find the vulnerabilities on the website and network; it is an interesting profession that covers every aspect to secure information. Penetration testing and vulnerability assessments are the parts of information security which also covers information gathering (intelligence gathering) in a broader aspect. Information gathering is generally the first step of ethical hacking and the more information that you have the more chances of success.
Information gathering is the process to find relevant information about the target. This information further helps to conduct successful tests on the target. It is an important step because every step is based on foundation. The method and procedure of information gathering is depends on the objectives of the test, sometimes we need to find the information about DNS (domain name system) and other times we need to find information about a person by using social networking websites, but have you ever thought that an image or a even a document can reveal so much important information? If no, than you need to redefine your strategy because you are missing an important point that might help you to get success, we can get a lot of important information from files by reading its metadata.

What should you learn next?
What is MetaData?
Metadata is a data that gives information about other data, and it describes the other data. The metadata of any data can give information about its characteristics, quality, creator information, time/date of creation, purpose of creation, procedure of creation, geographical location and the characteristic of the hardware.
Importance of MetaData in Information Security
Do we really need to care about metadata? This is the question that so many people ask and the answer is very clear – "Yes", but why?
This section describes the importance of metadata with some practical facts. Let's look back at history when the Iraq war was about to start and the United States (US) wanted the United Kingdom (UK) to join them, the administrator of the UK at that time had released a dossier on Iraq security and intelligence operations. The dossier was also addressed to the United Nations and the administrator made some mistakes. Because of the mistakes it has been discovered that the material has been copied from a US researcher. The administrator released the MS Word file of the dossier and the metadata of this document revealed some important information including the names of the people who have edited and the locations (directories) where the file was stored. This story is known as "Microsoft Word bytes Tony Blair in the butt".
Breasts lead to arrest of Anonymous hacker, it is not funny at all but this story is also describes the importance of metadata, FBI has arrested an anonymous hacker by using a picture that has been posted by him. The metadata of that picture contain GPS (Global Positioning System) information of where the picture had been taken.
So the importance of metadata is not the hidden truth anymore. The employees of every organization needs to learn about it and of course, if you are working on the position related to information security, than you need to make policies to protect the confidential information of your organization.
How to Find MetaData?
What are the techniques and tools that are helpful to find metadata of any file? The quick answer is that the techniques and tools depend on the nature of the file (whether it is a document or an image file). This section discusses different tools that are very helpful to accomplish the desired objectives.
ExifTool
It is one of the most interesting and famous tool that is available for multiple operating systems including Windows, UNIX and Mac. Exiftool is used to read, write and modify Meta information of different file formats.
There are two ways to use Exiftool; one is command line and the other is GUI (graphical user interface).
For windows users, kindly follow the tutorial:
- Download Exiftool from its official website http://www.sno.phy.queensu.ca/~phil/exiftool/.
- Extract it on your directory
- Double click on the executable file to read the documentation and other important information.
- The best way to get Meta information of an image is to just drag an image on the executable file.
- The executable file can read the metadata of an image and then it can display relevant information.
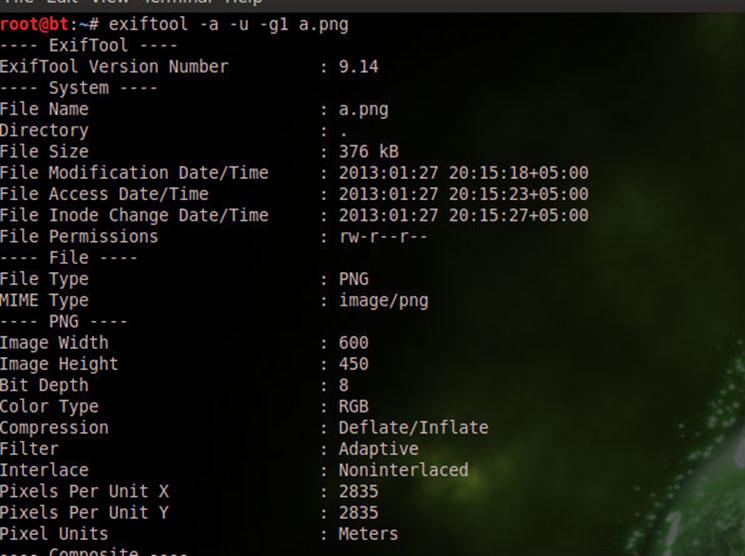
[caption id="" align="alignnone" width="604"]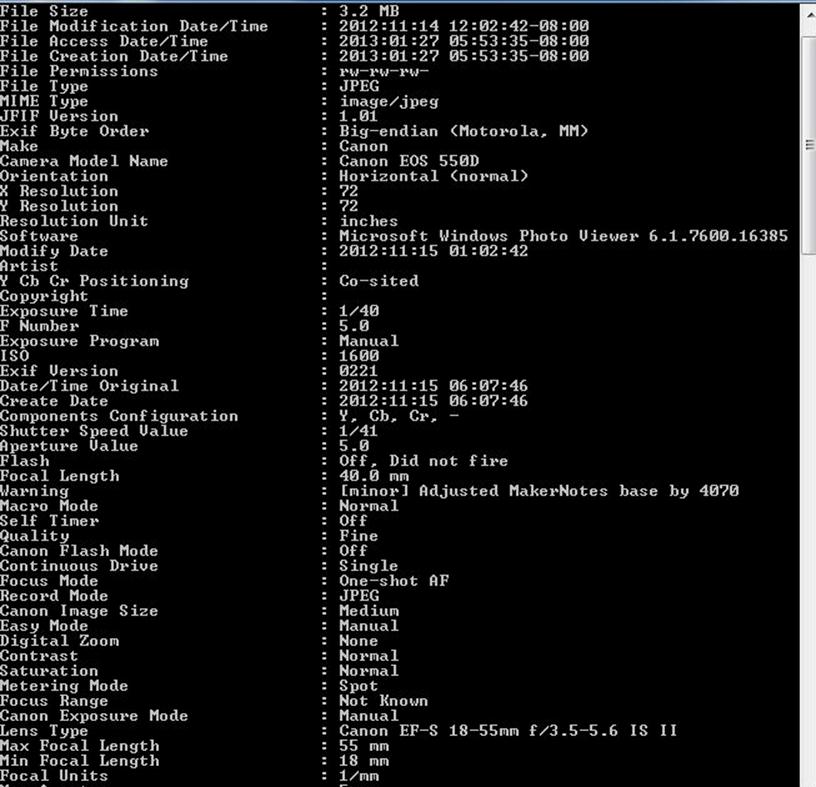 Click on image for a larger view[/caption]
Click on image for a larger view[/caption]
ExifTool GUI
The graphical user interface of ExifTool is a very user friendly and can also extract meaningful information from different file formats such as images and video files. The GUI of Exiftool is available for Windows operating systems only, and the procedure to configure the exiftool GUI is mentioned below:
- First of all, you need to rename the executable files that have been discussed above.
- There are two cases: one is with (.exe) and the other one is without extension. If the executable file that you have is exiftool(-k) rename it to exiftool (without ..exe extension). If the executable file is exiftool(-k).exe rename it to exiftool.exe (with exe extension).
- Copy the executable file (after rename) to the Windows directory (C:Windows).
- The next step is to get the ExifTool GUI version, you may download the latest version from http://u88.n24.queensu.ca/exiftool/forum/index.php/topic,2750.0.html
- Download it and unzip the GUI executable. It is not an installer; just open it and it is ready to work.
- Since the GUI is very easy to work with, so you can browse directories where the images and videos are stored. Just click on any file to get the metadata of that file.
- The right side of work place displays the Meta information of the file. There is another good option is to locate the physical location by using GEO tag and you can map it on Google Map.
[caption id="" align="alignnone" width="606"]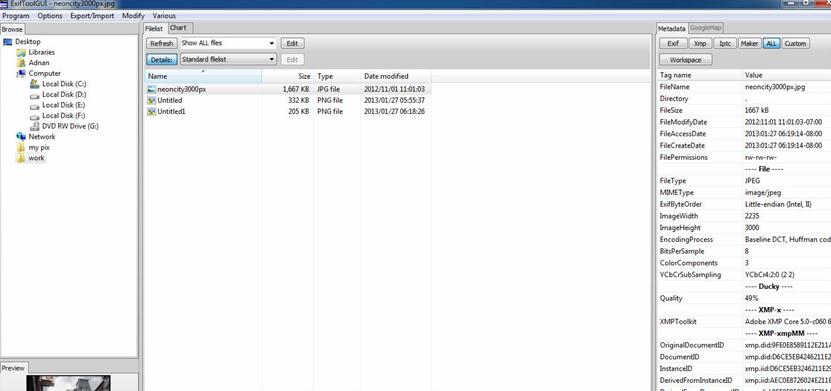 Click on image for an enlarged view[/caption]
Click on image for an enlarged view[/caption]
ExifTool Linux
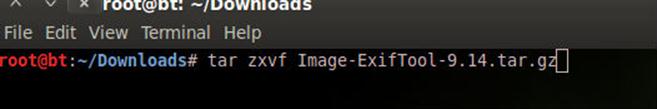
The procedure to configure Exiftool on Linux operating system is little bit different, but not difficult at all. Now download the latest version of Exiftool for Unix OS. The file will have an extension of .tar.gz
You can unzip it (and the procedure might be vary because there are many ways to do this), the possible technique is mentioned below:
- Unzip it by using this command (root@bt:~/Downloads# tar zxvf file name.tar.gz)
- After this, locate the directory and on the terminal type the following:
#perl Makefile.PL
#make test
#sudo make install
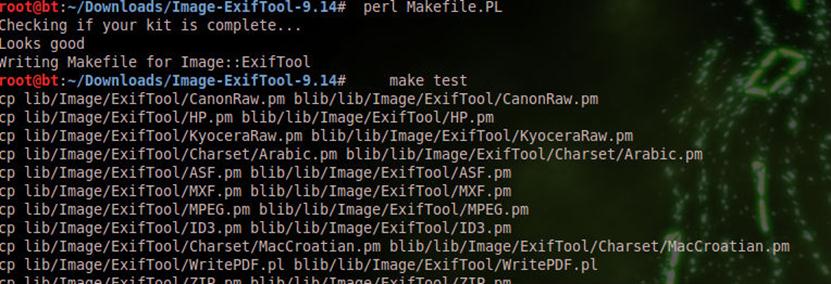
Exiftool is now configured and ready to use, make sure to remember the following synopsis:
exiftool [OPTIONS] [-TAG...] [--TAG...] FILE...
exiftool [OPTIONS] -TAG[+-<]=[VALUE]... FILE...
exiftool [OPTIONS] -tagsFromFile SRCFILE [-SRCTAG[>DSTTAG]...] FILE...
exiftool [ -ver | -list[w|f|r|wf|g[NUM]|d|x] ]
Some common usage of the tool is as follows:
#exiftool -a -u -g1 image.jpg
This syntax prints the Meta information of image; it includes the duplicate (-a) and unknown tags (-u).
#exiftool -common dir
Here dir means the directory, this syntax print Meta information of all the images in dir.
There are many other parameters that can also be implemented and it is based on the requirement. Beside Exiftool, there are so many other tools are also helpful to analyze the Metadata of a file. In actuality, Exif is a format or standard which stands for Exchangeable Image File Format. Exif can be found on different extension of images (JPG, PNG, TIFF and more) and videos (AVI or MOV). So Exif information of a file can be extracted by using tools other than exiftool.
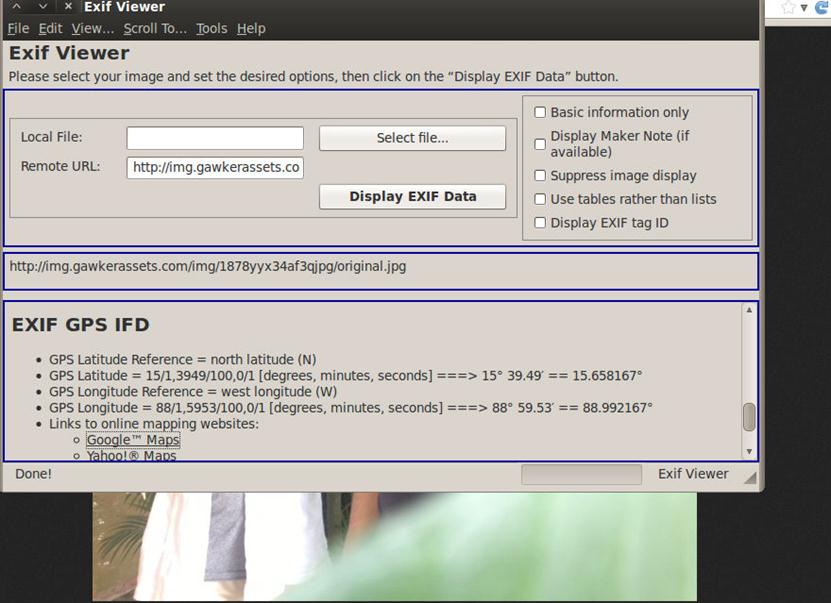
Exif Viewer
Exif viewer is just a plugin, and it is available for Firefox. It is an interesting plugin which displays the Exif and IPTC data in local and remote JPEG images. The limitation is very clear that it can only read JPEG format, so the other extension cannot be entertaind by Exif Viewer. It can also extract IPTC-NAA/IIM (International Press Telecommunications Council / Newspaper Association of America / Information Interchange Model), and IPTC Core (Adobe XMP, Extensible Metadata Platform) information from an image.
Install (https://addons.mozilla.org/en-us/firefox/addon/exif-viewer/) the plug-in on your browser and right click on any image, then click on "View Image Exif Data" to read the meta of an image.

FotoForensics
Foto Forensics is one the best web-based utilities that can extract meaningful data from the metadata of an image. Let's discuss a scenario:
The objective is to find out the geographical location by doing forensics , the image for this demonstration we can get from http://img.gawkerassets.com/img/1878yyx34af3qjpg/original.jpg. It is the image of John McAfee with Vice editor-in-chief Rocco Castoro.
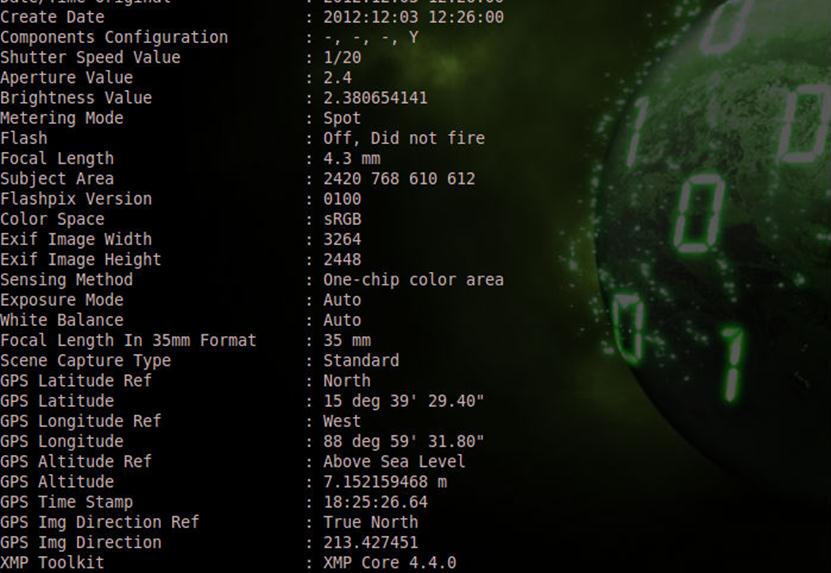
According to the ExifTool:
GPS Latitude Ref : North
GPS Latitude : 15 deg 39' 29.40"
GPS Longitude Ref : West
GPS Longitude : 88 deg 59' 31.80"
GPS Altitude Ref : Above Sea Level
GPS Altitude : 7.152159468 m
GPS Time Stamp : 18:25:26.64
GPS Img Direction Ref : True North
GPS Img Direction : 213.427451
Similar GPS information can be achieved by using the fotoforensics web based tool,
http://fotoforensics.com/analysis.php?id=4c366a3a81b184213d32bb4c646193eea712ba7c.132481
Aperture 2.4
GPS Altitude 7.1 m Above Sea Level
GPS Latitude 15 deg 39' 29.40" N
GPS Longitude 88 deg 59' 31.80" W
GPS Position 15 deg 39' 29.40" N, 88 deg 59' 31.80" W
GPS information that has been extracted by Exif Viewer is approx similar:
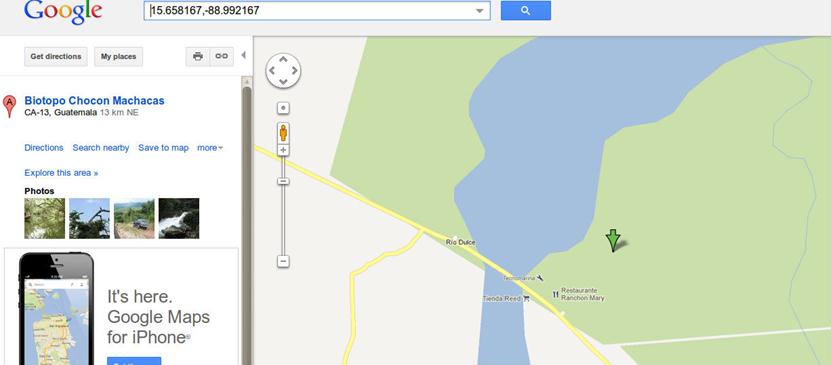
Now, according to these results we can easily map the location where the picture had been taken, information of hardware, date and time of creation, and so on.
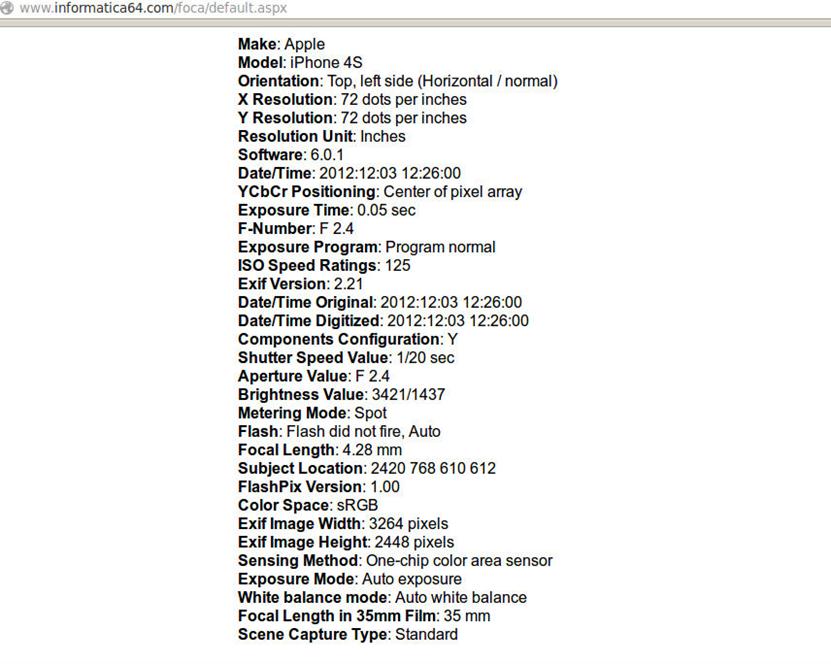
FOCA Online
FOCA online is another wonderful web based utility that can be used for a similar purpose to extract the metadata of a file. It is an online utility that support multiple formats including:
.doc .ppt .pps .xls .docx .pptx .ppsx .xlsx .sxw .sxc .sxi .odt .ods .odg .odp .pdf .wpd .svg .svgz .jpg
The procedure to analyze the file by using FOCA online is to upload any file from your computer and then press the analyze button, when analyzer finishes, it will give the result.
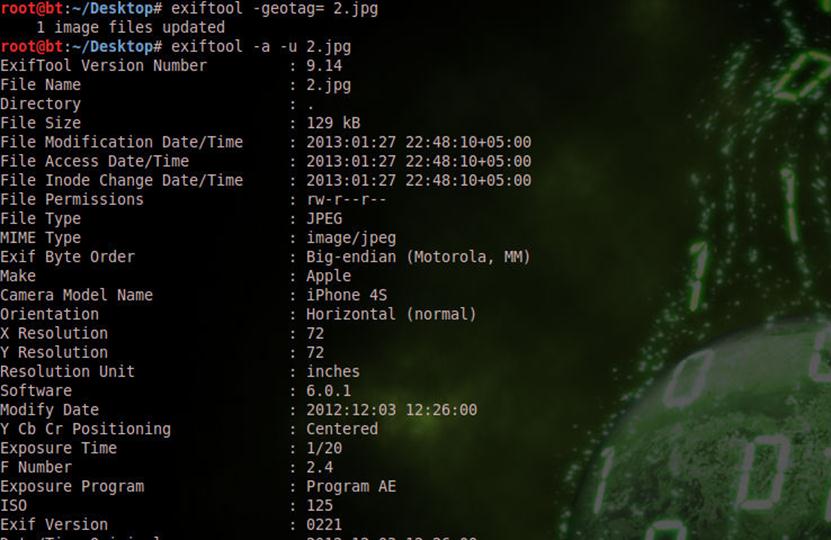
How to Remove MetaData?
The importance of metadata has been discussed above and it is very clear that the metadata of a file can reveal some important information and caused great harm. As an information security professional, you need to be very careful about it. You need to make policies of what your organization is uploading on the Internet, and before going to upload anything, make sure to remove its metadata.
The metadata of any file can be removed and modified, so it is always recommended to remove it but if you want to lead extractor of metadata to the wrong direction, then you can modify it. The tool Exiftool can used to achieve both targets; whether to remove or modify.
root@bt:~/Desktop# exiftool -Comment='This is the demo' 1.jpg
1 image files updated
root@bt:~/Desktop# exiftool -a -u 1.jpg
ExifTool Version Number : 9.14
File Name : 1.jpg
Directory : .
File Size : 127 kB
File Modification Date/Time : 2013:01:27 22:38:39+05:00
File Access Date/Time : 2013:01:27 22:38:39+05:00
File Inode Change Date/Time : 2013:01:27 22:38:39+05:00
File Permissions : rw-r--r--
File Type : JPEG
MIME Type : image/jpeg
Comment : This is the demo
Image Width : 640
Image Height : 480
Encoding Process : Baseline DCT, Huffman coding
Bits Per Sample : 8
Color Components : 3
Y Cb Cr Sub Sampling : YCbCr4:2:0 (2 2)
Image Size : 640x480
root@bt:~/Desktop#
The example mentioned above shows how to modify the comment of an image; if you want to delete all the information from the metadata, then follow this syntax:
#exiftool -all= image.jpg
To remove software information from the Meta of an image (remember software information is also reveal important information), the syntax mentioned below can remove Photoshop Meta information.
#exiftool -Photoshop:All= image.jpg
The important phase to remove GPS information, so that the GEO location cannot be available for public, GPS information can be removed by using the syntax:
#exiftool -geotag= image.jpg
Conclusion
Metadata of data contains much useful information and it can be very dangerous from an information security point of view. It is also helpful for the forensic experts, so the bottom of the story is that the metadata is hidden and contains useful information that can help forensic experts and can be dangerous for the security experts.
References
http://www.computerbytesman.com/privacy/blair.htm
http://news.cnet.com/8301-17852_3-57414153-71/breasts-lead-to-arrest-of-anonymous-hacker/





