Comprehensive guide to Security+ domains (2024)
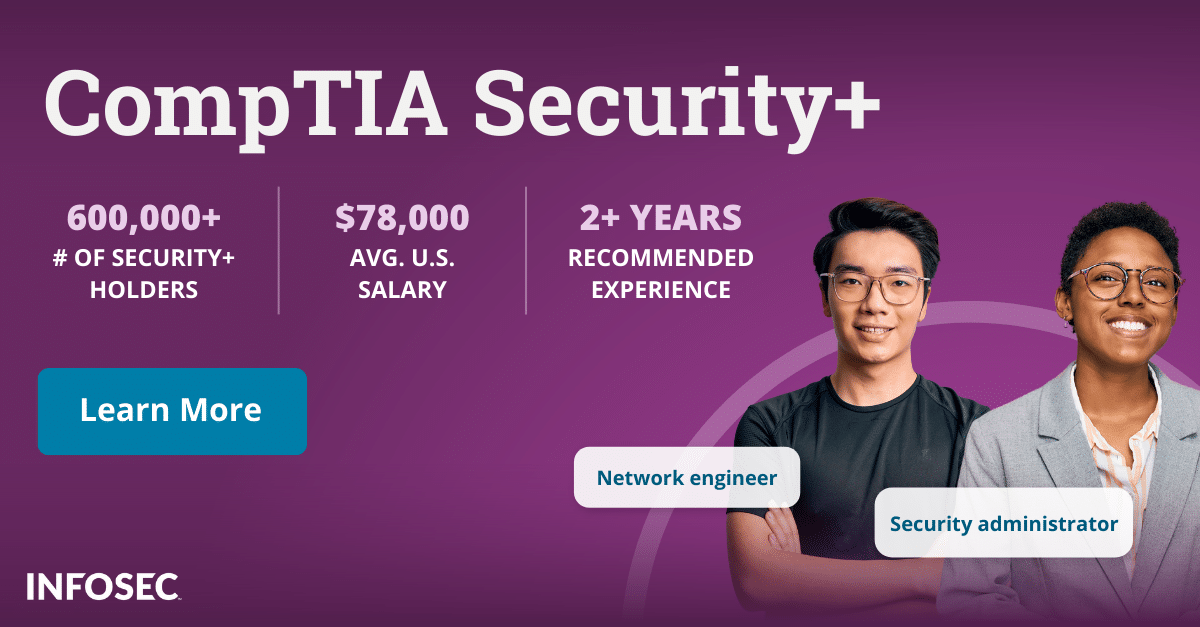
The demand for skilled cybersecurity professionals continues to grow. According to CyberSeek, there are only 72 cybersecurity workers for every 100 U.S. cybersecurity jobs. For those looking to validate their entry-level skills in the field and land one of those jobs, CompTIA’s Security+ is by far the most popular certification option with more than 700,000 professionals having earned the cert.
This entry-level certification is globally recognized and demonstrates to employers that you have the necessary knowledge and skills to identify, prevent and respond to cybersecurity threats in a real-world environment. Since its inception in 1999, the Security+ exam has undergone several revisions to keep pace with the changing cybersecurity landscape. The latest version, SY0-701, was released in November 2023 to address the latest cybersecurity threats and challenges and to focus on a more streamlined role.
Understanding the Security+ domains
The Security+ exam covers five core domains, each an important part of a well-rounded cybersecurity professional's toolkit. Here is an overview of what is covered in each:
1.0 General security concepts
This domain establishes the fundamental principles and terminology that guide every subsequent step. It demystifies key security concepts like confidentiality, integrity and availability (CIA) — the core pillars of information security. You'll also explore various types of security controls and gain a comprehensive understanding of security models.
2.0 Threats, vulnerabilities & mitigations
This domain explores the diverse nature of cyberattacks, including social engineering, malware, fishing, denial-of-service (DoS) and zero-day attacks. You'll learn about vulnerability management techniques and develop the skills necessary to assess risk and implement mitigation strategies.
3.0 Security architecture
In this domain, you'll learn about the intricate world of secure network design, exploring topics like network segmentation, demilitarized zones (DMZs) and secure routing protocols. Techniques for hardening systems and applications will be revealed, along with various access control mechanisms.
4.0 Security operations
This domain covers the daily practices of security monitoring and logging, providing you with the ability to identify potential threats through careful analysis of log data. You'll explore the world of Security Automation and Orchestration (SAO), learning about tools and techniques that automate routine tests for increased efficiency.
5.0 Security program management and oversight
The final domain addresses the strategic aspects of managing security programs and ensuring proper oversight. You'll gain a comprehensive understanding of relevant regulations and compliance requirements, ensuring your organization operates within legal boundaries.
Exam evolution — from SY0-601 to SY0-701 and beyond
The Security+ certification has evolved from SY0-601 to SY0-701, reflecting the skills and knowledge required for today's cybersecurity roles. The SY0-701 exam focuses on core cybersecurity skills and prepares candidates to proactively prevent cyberattacks.
Similarities between SY0-601 and SY0-701 |
Differences between SY0-601 and SY0-701 |
|
Skill level: Both exams identify early career cybersecurity skills at the two-year level. |
Exam objectives: SY0-701 has fewer objectives (28) compared to SY0-601 (35) due to a more focused job role in a maturing industry. |
| Exam domains: Both have the same number of exam domains, but some content has been rearranged. | Exam content update: 20% of the exam objectives in SY0-701 were updated to include current trends and threats, attacks, vulnerabilities, automation, zero trust, risk, IoT, OT and cloud environments. |
| Job roles: The related job roles for both exams are similar, with a focus on security administration. However, the work of a Security Administrator has become more defined, and the skills performed are identified more accurately. | Improved instructional design: Several exam domains and objectives have been reorganized and renamed to optimize the learning experience. |
| Governance, risk and compliance (GRC): The emphasis has shifted from the minutiae of specific regulations to a broader focus on reporting and communication. |
If you have already taken the SY0-601 exam, you will notice a greater emphasis on practical skills, including assessing security posture, securing hybrid environments and operating with an awareness of regulations and policies from the SY0-701 exam.
Choosing the right exam — SY0-601 to SY0-701
When CompTIA updates a certification exam like Security+, there is typically a six-month window where two versions the exam are available: the old exam and the new exam. With the recent update:
-
SY0-701 was released on November 7, 2023
-
SY0-601 does not retire until July 31, 2024
This window from November to June is to minimize disruption to those currently studying for the exam. If you’re preparing to get certified using 601 training materials, you have plenty of time to take the 601 exam and earn your Security+. However, you do have the option of taking either exam during the window. Just be aware that new exam versions usually differ by about 20% in the material they cover.
After July 31, 2024, everyone must take the 701 version until the next update, which is expected in Fall 2026.
Deep dive into Security+ topics
Now that you understand the framework provided by the five Security+ domains, let's explore deeper into the specific topics covered within each domain and their practical applications in real-world cybersecurity scenarios. You can also view the full Security+ 701 exam outline for even more details.
1.0 General security concepts
In this domain, you'll be tested on:
-
Types of security controls: Comparing and contrasting different categories and types of preventative, detective and corrective controls.
-
Security terminology: Understanding key terms like cryptography, access control and authentication.
-
The CIA triad: Applying the principles of confidentiality, integrity and availability.
-
Change management: Understanding the importance of the change management process and how it impacts security.
This domain equips professionals to:
-
Identify and communicate security risks and controls to stakeholders.
-
Implement access control mechanisms to enforce the CIA triad.
-
Deploy network security controls like firewalls and intrusion detection systems.
2.0 Threats, vulnerabilities & mitigations
The second domain will test your knowledge on:
-
Types of cyberattacks: Understanding common attack vectors like social engineering, malware and phishing.
-
Vulnerability management: Understanding different types of application, OS, hardware and other vulnerabilities.
-
Indicators of malicious activity: Analyze attacks related to malware, networks, cryptography attacks.
-
Mitigation techniques: Explain the different techniques used to secure an enterprise.
Real-world implementation of these concepts include:
-
Identifying suspicious emails and preventing phishing attacks.
-
Regularly patching systems and applications to fix vulnerabilities.
-
Responding to security incidents according to established procedures and recovering quickly.
3.0 Security architecture
Security architecture covers the following topics:
-
Architecture and infrastructure: Understand the security implications of different architecture models.
-
Applying security principles: Understand considerations for infrastructure, secure communications and access and effective controls.
-
Protecting data: Understand concepts and strategies around data types, classifications and methods to secure data.
-
Resiliency and recovery: Explain the importance of availability, multi-cloud systems, testing backups and more.
Candidates can apply expertise covered in this domain to:
-
Designing and implementing secure network architectures for your organization.
-
Follow best practices around secure confidential organizational data.
-
Ensuring business continuity by testing and updating your disaster recovery plans regularly.
4.0 Security operations
The Security operations domain will test your knowledge on:
-
Security monitoring and logging: Monitoring logs and events for anomalies and suspicious activity.
-
Security automation and orchestration (SAO): Automating routine tasks like vulnerability scanning and patching.
-
Security information and event management (SIEM): Analyzing security events and incidents in a centralized platform.
-
Identity and access management: Implement and maintain best practices around provisioning users, SSO, multifactor authentication and more.
Here are some of the practical applications of the topics covered in this domain:
-
Identifying and investigating security incidents effectively using log analysis tools.
-
Automating mundane tasks to free up time for strategic security activities.
-
Hardening servers, workstations and mobile devices to minimize vulnerabilities.
5.0 Security program management and oversight
This domain covers these topics:
-
Security policies and standards: Developing and implementing the rules users will use when dealing with technology.
-
Compliance requirements: Understanding and complying with relevant regulations like HIPAA and PCI DSS.
-
Risk management frameworks: Implementing frameworks like the NIST cybersecurity framework.
-
Security awareness and training: Educating employees about cybersecurity threats and best practices.
By mastering these topics, professionals can:
The impact of Security+ on cybersecurity careers
The CompTIA Security+ certification is more than just an exam; it's a passport to a rewarding and fulfilling career in cybersecurity. By showcasing your knowledge and competence, you unlock doors to a wide range of exciting opportunities.
With this certification, you can position yourself as a top candidate for entry-level security positions. Security+ opens doors to roles like:
-
Security Analyst: Identify vulnerabilities, analyze threats and implement security solutions.
-
Network Security Administrator: Configure and manage network security devices and systems.
-
Security Consultant: Assess security risks, develop security plans and recommend security controls.
-
Security Engineer: Design, implement and maintain secure networks and systems.
Security+ can serve as a springboard for career growth in cybersecurity. Having a Security+ certification can boost earning potential and is often listed as a requirement or preference in job postings.
This CompTIA certification also serves as a stepping stone to other advanced certifications offered by CompTIA, like PenTest+, CySA+ and CASP+. By building upon the Security+ certification, you can expand your knowledge and qualifications and open the door to even higher-paying positions.
Preparing for the Security+ exam
The CompTIA Security+ exam requires dedication, focus and preparation. With the right approach and resources, you can equip yourself with the knowledge and confidence to ace the exam. Here are some tips that will help:
-
Understand the exam objectives: This article will get you started, but thoroughly review the CompTIA Security+ exam objectives to understand the specific topics covered in the expected level of depth.
-
Create a study plan: Develop a structured plan that provides sufficient time for each domain.
-
Blog posts: Articles on Security+ study tips, the Security+ exam process, and other topics will guide you in preparing for the exam.
-
Security+ study guides: Books like The Official CompTIA Security+ Self-Paced Study Guide will allow you to learn at your own pace and become a handy reference.
-
Boot camps: Infosec's CompTIA Security+ Training Boot Camp will teach you all you need to know to pass the exam in five days and comes with an Exam Pass Guarantee.
-
Take practice tests: Regularly test your knowledge with practice exams. These will help you identify areas you need to study further and help you get used to the exam format. Infosec's CompTIA Security+ Training Boot Camp gives you unlimited practice exam attempts.
-
Practice the necessary skills: Don't just passively consume information. Actively engage with the material through hands-on labs and your own explorations.
-
Relax and stay confident: As the exam day approaches, make sure to rest and maintain a positive mindset. Confidence can greatly impact your performance. No matter your experience level, allow sufficient study time for topics you find most difficult. With smart preparation using these tips and trusted resources, you will be ready to demonstrate your Security+ competencies.
Security+ domains: Key takeaways
The CompTIA Security+ certification empowers you with the foundational knowledge and practical skills needed to thrive in the ever-evolving world of cybersecurity.
Here are some key takeaways:
-
Security+ equips you with the essential knowledge to identify, prevent and respond to a wide range of cyber threats and vulnerabilities.
-
The certification empowers you to work effectively in diverse environments, including cloud, mobile, IoT and OT ecosystems.
-
Security+ opens doors to exciting and rewarding career opportunities in cybersecurity, allowing you to command higher salaries and secure leadership positions.
The demand for skilled cybersecurity professionals is not going away, and the Security+ is a proven tool for more than 700,000 cybersecurity professionals.
Quick summary: FAQs
What is the difference between SY0-701 and SY0-601?
The main differences between SY0-701 and SY0-601 are:
-
Focus: SY0-701 places more emphasis on cloud security, security automation and orchestration, cryptography, threat modeling and security assessment and testing compared to SY0-601 and focuses on a more streamlined job role within a maturing industry.
-
Domain structure: While both versions have five domains, they are organized differently. This was done to improve the instructional design of the exam.
-
Number of objectives: SY0-701 has fewer objectives (28) than SY0-601 (35).
What's new in the Security+ domains for 2024?
Around 20% of the exam objectives were updated for 2024 to reflect the changing landscape of cybersecurity. These updates focus on current cybersecurity trends, including:
-
Hybrid environments
-
Operational technology
How long is SY0-701 valid for?
The SY0-701 certification is valid for a period of three years. This three-year window starts from the date you pass the exam. After this window, you must renew your certification to maintain its active status.
When is the next Security+ exam update?
CompTIA typically updates its Security+ exams every three years to align with the latest industry standards, and we can expect the next update to be in late 2026.