Security+ Domain #3 – Implementation [updated 2021]
Implementation is important for an organization’s security program. It can be seen as the moment of conception for a security system or technology as it is where the rubber meets the road. Without implementation, a new security initiative is nothing more than ideas on a Word document. Learning the nine objectives of domain 3.0, as well as the sub-objectives, will prepare you for the CompTIA Security+ certification.
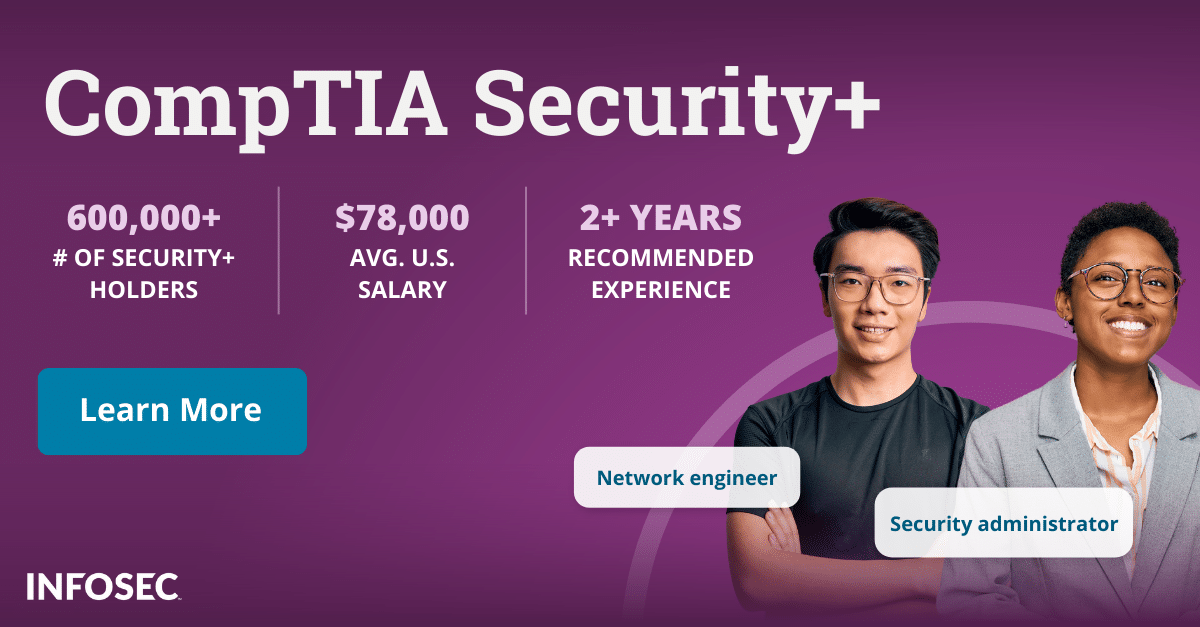
Become a SOC Analyst: get Security+ certified!
More than 47,000 new SOC analysts will be needed by 2030. Get your CompTIA Security+ to leap into this rapidly growing field — backed with an Exam Pass Guarantee.
New domains for SY0-601
We are currently on Security+ exam version SY0-601, and there has been an estimated 25% change in Security+ certification exam material since SY0-501. We now have five domains and the common body of knowledge (CBK) has gained an increased focus on cyberthreats, governance and operations concepts. Below is the Security+ domain lineup for the SY0-601 exam:
- 1.0 Attacks, threats and vulnerabilities
- 2.0 Architecture and design
- 3.0 Implementation
- 4.0 Operations and incident response
- 5.0 Governance, risk and compliance
Without further ado, let’s deep dive into Domain 3.0: implementation.
Domain 3.0 – implementation (objectives)
Below is a list of the objectives covered in Domain 3.0 on the CompTIA Security+ exam.
- Secure protocols
- Host or application security solutions
- Secure network designs
- Install and configure wireless security settings
- Secure mobile solutions
- Apply cybersecurity solutions to the cloud
- Identity and account management controls
- Authentication and authorization solutions
- Public key infrastructure
Secure protocols
Secure protocols cover two key areas: protocols and use cases. Protocols will test the candidate’s knowledge of the different security protocols that are in application today. These protocols range from DNS, SSH and HTTPS to LDAPS and POP/IMAP. Use cases focus more on the actual application of these security protocols. Candidates will be expected to know what security protocols are used for voice and video, email and web, routing and switching and even subscription services.
Host or application security solutions
Host or application security solutions focus on which security solutions are used for different hosts and applications. This objective tests candidates over five sub-objectives: endpoint protection, boot integrity, database, application security and hardening. Candidates will be expected to know the difference between antivirus, anti-malware and endpoint detection/response. You will also need to know boot security and UEFI concepts, what is hashing concerning a database, when to use fuzzing in application security, the difference between static and dynamic code analysis and how to harden systems with disk encryption.
Secure network designs
In the organizational work world, networks are as commonplace as computers themselves. As such, knowing secure network designs is necessary to build out a secure network for your organization. Since implementation is the name of the game for this domain of knowledge, candidates will be tested on how to implement load balancing, network segmentation, virtual private networks (VPN), port security and network appliances. Specifically, candidates will need to know the difference between active and passive load balancing, when they should use virtual local area networks (VLAN), layer 2 tunneling protocol, DHCP snooping, MAC filtering and when to use NIPS and NIDS.
Install and configure wireless security settings
Wireless security is a growing portion of information security and has garnered its objective within the implementation domain of knowledge. Candidates will be responsible for cryptographic protocols, authentication protocols, methods (of installing and configuring wireless security settings) and installation considerations. The interesting part of this objective is the attention paid to the various installation considerations that those who install the wireless security solutions have to keep in mind such as where to place the WAP within the job site.
Secure mobile solutions
With the prevalence of mobile devices, implementing secure solutions for said devices is a priority for many organizations today. This objective focuses on security solutions for mobile devices and covers four sub-objectives: connection methods and receivers, mobile device management, mobile devices and deployment models.
Candidates will need to know point-to-point vs. point-to-multipoint connections, the key concepts of mobile application management, micro SD hardware security module and when to use the corporate-owned personally enabled deployment model.
Apply cybersecurity solutions to the cloud
This objective is all about applying cybersecurity solutions to the cloud and is divided into two sub-objectives: cloud security controls and solutions. Candidates will need to know about high availability across zones, integration and auditing, CASB, application security and firewall consideration in a cloud environment.
Implement identity and account management controls
Sound information security calls for implementing identity and account management controls, so it should be no surprise that it would find its way into this domain. This objective is made up of three sub-objectives: identity, account types and account policies. Candidates should know the attributes of identity, how and when tokens and certificates are used, shared and generic accounts/credentials, access policies and account permissions. This objective also includes the concepts of geofencing, geolocation and geotagging.
Implement authentication and authorization solutions
Authentication and authorization are used by nearly every organization today and are at the heart of organizational information security. Therefore, proper implementation of authentication and authorization solutions is key for most organizations to function. Candidates will be responsible for the material within the three sub-objectives: authentication management, authentication/authorization and access control schemes. Be prepared to explain knowledge-based authentication, when to implement EAP and CHAP, as well as the differences between role-based access control and rule-based access control.
Public key infrastructure (PKI)
The final objective in this Security+ domain is public key infrastructure (PKI). This objective covers two main areas: PKI and concepts. Expect to know about key management, certificate authority (CA), intermediate CA, certificate attributes, subject alternative name and online vs. offline CA. Candidates should also be prepared to explain the concepts of certificate chaining, pinning, stapling and key escrow.
Learning the objectives of domain 3.0
One of the new domains in the Security+ certification exam is Domain 3.0, implementation. Implementation is a vital part of security that pulls away from the realm of theory and into practice. Using this deep dive into the domain will put you miles ahead in terms of creating your outline when you study for the Security+ exam.
For more on the Security+ certification, view our Security+ certification hub.
Sources
- CompTIA Security+ Certification Exam Objectives SY0-601, CompTIA Security+