Security+: Security implications of embedded systems [updated 2021]
The internet of things (IoT) is changing both how we live and how we do business. You can find embedded (or smart) devices everywhere, from the doctor’s office and the public transportation system, to the agricultural supply channel and national defense systems. Intel estimates that by the year 2020, the world will have 200 billion connected objects, up from 15 billion in 2015.
Embedded systems — computer technology integrated into everyday devices to perform a specific function — present a unique set of challenges. On the CompTIA’s Security+ exam, candidates will need to demonstrate their knowledge of how embedded systems impact security.
Embedded systems have many of the same security challenges, but each type of system adds another layer of complexity and unique factors. For a long time, manufacturers didn’t pay a lot of attention to the security of the embedded systems, partly because the security risks weren’t known.
But even for newer devices, security is often an afterthought. A major driver of this trend is the fact that these devices are small, so adding security would take away from functionality.
For the CompTIA Security+ exam, you’ll need to understand the security implications of different types of embedded systems. Here are some examples.
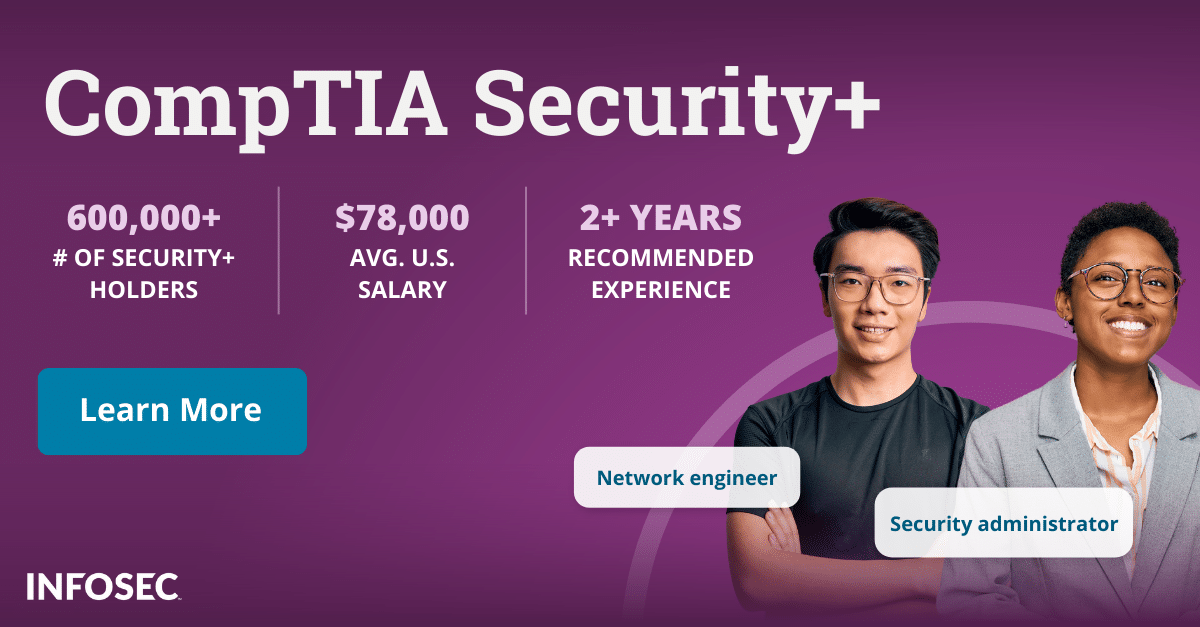
Become a SOC Analyst: get Security+ certified!
More than 47,000 new SOC analysts will be needed by 2030. Get your CompTIA Security+ to leap into this rapidly growing field — backed with an Exam Pass Guarantee.
SCADA/ICS
SCADA refers to supervisory control and data acquisition systems, which are used to manage industrial control systems (ICS). The use of ICS ranges from controlling manufacturing production to monitoring critical infrastructures such as power and water utilities.
Traditionally, ICS relied on passive defenses such as air gapping, separating them from the internet. Today, however, it’s hard to escape connectivity and operations are also becoming interconnected. Industrial entities are looking for more efficient ways to control operations and use real-time data, so they’re deploying more internet-connected embedded systems.
Industrial control systems are typically designed to function for a long time — and many were designed before security came to the forefront. So, they’re not only vulnerable but not designed to be easily patched, if at all. Malicious actors who may be more likely to target ICS, on the other hand, are often state-sponsored, so they have more resources to exploit weaknesses than the average cybercriminal.
Smart devices/IoT
Smart watches, fitness trackers, smart jewelry and garments — wearable technology can track and record every movement a person makes. When these devices get hacked, they can yield quite a bit of personal information.
From a consumer perspective, the biggest concern about wearables may be privacy. But wearable technology is also becoming more common in the workplace, as businesses adopt devices that monitor employees’ movements and performance. This kind of large-scale deployment of technology that is continuously moving around and in and out of the physical premises poses new risks to the enterprise.
Smart devices used for home automation — anything from thermostats and security cameras to smart refrigerators — also have various privacy and security implications. One eye-opening example of how malicious actors can use connected home technology and other devices was the 2016 massive distributed denial-of-service attack that took down numerous internet platforms around the world, including major providers of streaming, media and e-commerce services. A botnet (a network of computers infected with malware) commandeered as many as 100,000 IoT devices such as cameras and DVRs to bombard the servers of Dyn, a company that operates domain name systems, causing the company’s servers to go down — and much of the internet traffic with it.
HVAC
Once standalone units, HVAC (heating, ventilation and cooling) systems are now being connected into the corporate network to automate building controls. In many cases, third-party vendors are also involved in the process, which adds another layer of risk.
One example of this security risk was the massive 2013 Target data breach, which started with the compromise of an HVAC vendor. While the vendor didn’t control the HVAC systems, the vendor was connected to Target’s billing and project management system, which gave malicious actors a foothold into Target’s network.
Medical devices
The golden era of medicine has ushered in a healthcare delivery model where patients can be monitored in real time, patient records can be accessed instantly and care can be delivered remotely. Much of this can be done with the help of embedded systems, medical devices such as insulin pumps, pacemakers and MRI machines.
Like ICS, many of the medical devices were manufactured before security became a concern and updating their firmware or software must be done manually if it can be done at all. Imagine the hundreds or thousands of these devices inside a hospital — many healthcare organizations don’t even have good systems in place to keep track of this inventory, let alone manage the security of products that are made by many different vendors, each with a different operating system.
One unique issue with medical devices is that any kind of firmware changes in the past would have required recertification by the Food and Drug Administration (for the devices under FDA’s jurisdiction). The FDA has recently issued new guidance for manufacturers to address security risks, both for new and postmarket devices; however, that guidance is nonbinding.
Vehicles
Even the cars we drive are essentially computers on wheels — in fact, dozens, and dozens of tiny computers on wheels. Electronic control units are embedded with microprocessors that control critical functions like braking and navigation, and now many cars come equipped with internet connections as well.
Like any other code, software that runs vehicles can be hacked. For the most part, this capability is currently theoretical, but researchers have demonstrated that it can be done. The future security implications don’t only impact individual driver safety — as smart cities become the way of the future, vehicles will become interconnected as well.
Other embedded systems that the CompTIA exam covers include:
- SoC (system-on-a-chip) — integrated circuits, like a Raspberry Pi
- RTOS (real-time operating system) — these are used in things like automobiles and industrial equipment to run specific processes
- Printers, surveillance cameras and multifunction devices (MDFs): these all have security vulnerabilities yet are often overlooked by security managers
- Aircraft and UAVs (unmanned aerial vehicles): both have security risks because of embedded software
For information systems (IS) professionals, the implications of this IoT explosion are tremendous because the focus is no longer only on the network or perimeter. Embedded devices expand the attack surface and require a shift in the security strategy.
Some of the strategies used to mitigate the risks include:
- Network segmentation: partitioning the network into secured network zones so IoT endpoints could be assigned specific communication policies and privileges
- Secure password practices: ensuring default passwords are changed and password best practices are applied
- Web application firewalls (WAF): incorporating WAF solutions to prevent web-based attacks and protect HTTP (web protocol) connections
- Firmware updates: having a process in place for automated updates as well as periodically checking the manufacturers’ websites
Since IoT technology is in its early stages of development, we are only beginning to understand the security risks. As the industry matures, some of those issues may be solved in time, but the ever-expanding footprint that embedded devices create will always make security a challenge.
IoT is poised to become a mainstream part of doing business. Information systems professionals need to have a good foundation for understanding how to address IoT risks — but at the same time, their strategies will have to evolve along with the industry.