Security+: Incident response procedures [updated 2021]
As technology evolves, so do the security risks we face. Data breaches and cyberattacks are an everyday part of our lives, and businesses need to accept the fact that at some point they’ll have to deal with a security threat. If you’re a business owner, having an incident response plan in place is crucial, as it helps you and your team stay organized amidst the chaos of the attack and lets you contain it before it becomes too damaging. You need an action plan for everything from intrusions, cyber-theft, denial of service, fire, floods and other security-related events.
Things to consider while creating an incident response plan
A good incident response plan should help you deal with not just one but a vast array of crises that could potentially hurt your company. Your plan should describe each possible situation and outline the steps that need to be taken to limit the damage caused.
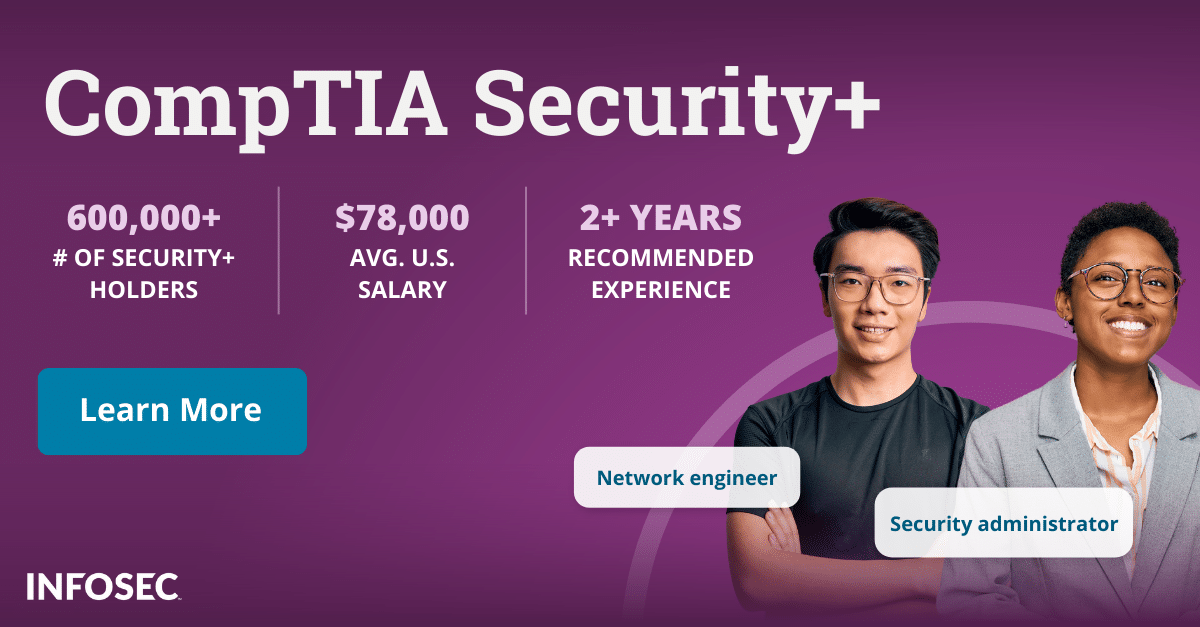
One effective way businesses can take pre-emptive action is by getting their core response team certified by the CompTIA. A CompTIA Security+ certification trains each individual on how to anticipate security risks and prevent them before they occur. In case an incident does occur, they will be prepared to resolve a wide variety of security issues.
Before putting an incident response plan together for your business, there are certain things that you need to consider and figure out beforehand.
- Categorizing and documenting incidents: having an incident classification structure in place is crucial to enabling swift identification and remediation of the incident. Classify any potential risks according to a category, type and severity. Remember to record and analyze each incident that does occur; this will also help refine your classification model and help contain similar future incidents efficiently.
- Roles and responsibilities: as soon as an incident occurs, your team needs to spring into action immediately. It’s crucial that you involve the right people and that they know exactly what their roles and responsibility are within the incident response plan.
- Reporting and escalation: being well prepared is half the battle won. Your team should have a strong plan with a comprehensive checklist to fall back on in case things go south. Think of it like a fire drill — once each team member knows exactly what they must do and who they should contact in each situation, all incidents will be swiftly addressed and escalated, leading to minimizing damage when a real threat strikes.
- Cyber incident response teams: the core cyber incident response team needs to have a very specific set of skills to combat each incident deftly. Their knowledge and expertise should span both technical and non-technical areas. It’s important to gauge whether your internal team has all the needed skills or if it makes sense to have an external team on standby.
- Exercise: all aspects of your incident response plan should regularly be tested. This can be done through table-top exercises which simulate real-world incidents. How your team performs in these exercises can be used to weed out loopholes and refine your plan.
The six steps of an incident response process
When it comes to information security, there are six common stages of incident response that need to be kept in mind when developing an incident response plan. Incident response is not a standalone action; it’s a process made up of several procedures, where the aim is to take a strategically planned approach to any security breach. To effectively cover every base and address the wide range of potential security threats, every plan should cover the following six steps.
Preparation
Some of the ways to be prepared with your own incident response plan are:
- Create and catalog incident response policies: establish policies and procedures for incident response management.
- Define clear communication channels: having a seamless line of communication is crucial both during and after an incident. Work out the most efficient communication channels and guidelines for your team.
- Train your team: ensure that all members of your incident response team are sufficiently trained and equipped to make quick decisions. Each incident response team is only as good as their plan because preparation is key to effective incident response.
- Review threat intelligence feeds: regularly review and analyze your threat intelligence feeds for any potential future threats.
- Regularly update your policies: have a plan in place to review and update your incident response policies annually to stay up-to-date with the threats.
Identification
From the moment you become aware that an incident has occurred, it’s important to answer a few crucial questions before doing anything else. What kind of incident has occurred? Has any data been leaked or lost? What is the level of severity? This will help you choose the best course of action according to your incident response process. The main emphasis of this phase is on detecting and reporting any potential security threats.
- Observe: train your team to always keep an eye out for anything that seems even mildly suspicious.
- Detect: once an incident is detected, it needs to be escalated through the predefined channels.
- Alert: through the initial findings, the threat needs to be analyzed and then categorized based on its severity.
Containment
This step aims to forcefully stop the threat and prevent any further damage from occurring. There are various ways to achieve this — deploying patches, stopping the outbound communication from the infected machine, powering off the servers etc. This phase is critical, and the strategy for containment depends totally on what is found during the identification phase.
- Coordinated shutdown: after identifying all the infected systems, turn all of them off together.
- Erase and reboot: format all the infected devices, change all passwords, update, patch all systems and review remote access protocols.
- Keep the evidence: be sure to back up all your logs and any other evidence related to the incident.
Eradication
After containing the incident, it’s time to eliminate the cause of the breach. This could be malicious code or any other type of threat that led to the incident. After a thorough forensic analysis, the malware will need to be removed, and all the weak points in the system will need to be patched and updated. Whether your team does this, or you outsource it to a third party, this step needs to be done thoroughly, so that no trace of the threat remains within the system.
Recovery
After the incident has been contained, it’s important to restore all your affected systems and services as soon as possible. But while trying to get things back up and running, be sure to continue monitoring all your activity, just to make sure that the problem has been fully resolved and the threat has been erased from your network.
- Patch and test: ensure that all systems have been tested after being restored.
- Monitoring: decide how long the system needs to be closely monitored post-incident for the same threat.
- Identify tools: are there any tools that can help ensure a similar incident doesn’t reoccur?
Lessons learned
This is one of the most important yet commonly overlooked steps of the incident response process. Now that you’ve successfully overcome the threat, the next step is to figure out how you can do an even better job the next time by avoiding any mistakes that were made this time. All information must be documented for future reference.
- Fill out the incident report: detailing out the minutes of the incident will help fine-tune your incident response plan and can be used to improve your plan.
- Keep your eyes open: closely monitor all activities post-incident, in case the threat resurfaces.
- Identify weak points: hold a post-incident meeting with your team to identify any incident response loopholes that need to be fixed.
The lessons you learn from the real incident will help fortify your systems against any future attacks. But one doesn’t have to wait for a security incident to take place to learn how to handle each situation thanks to certification exams like CompTIA Security+, which teach participants how to handle and contain all kinds of security threats. Hopefully, you won’t ever have to face a data breach, but it’s crucial to be prepared nonetheless.
For more on the Security+ certification, view our Security+ certification hub.
Sources
- How To Plan For Security Incident Response, Forbes
- 6 Phases in the Incident Response Plan, Security Metrics
- Creating an incident response classification framework, Digital Guardian