Security+: Implementing public key infrastructure [updated 2021]
Public key infrastructure (PKI) is a vital management tool for the use of asymmetric cryptography and digital certificates. A PKI involves components (certification authority, intermediate certificate, certification revocation list and so on), PKI concepts (stapling, pinning, trust models and so forth), certificate types (wildcards, san, code signing, email, root and more), and certificate formats (DER, PEM, PFX, P12 etc). The following sections will elaborate on these concepts in greater detail.
What are essential PKI components for Security+?
Security+ aspirants must be mindful of the following important PKI components.
Certificate authority (CA): a CA is the third-party trusted agency that issues digital certificates for verifying entities on the internet. Examples of the best certification authorities today include Symantec, VeriSign, GeoTrust, Comodo and Digicert. The CA can be either an external CA to the company, such as a commercial CA that charges for its service or an internal CA to the company, one that facilitates service to its workforce.
Generally, CA is responsible for the following duties:
- Generating, issuing and distributing the public key certificates
- Distributing CA certificates
- Generating and publishing certificate status information
- Allowing subscribers to request for revocation
- Having the ability to revoke public key certificates
- Maintaining availability, continuity and security of certificate issuance signing functions
Intermediate CA: an intermediate CA is a subordinate certificate authority issued by the trusted root to sign digital keys. Intermediate CAs help the root CA in distributing the workload of issuing and verifying the certificates.
Certificate revocation list (CRL): a CRL is a list of the serial numbers of digital certificates whose current status has been revoked. Various certification authorities maintain an online CRL that can be queried by inserting a certificate serial number. Additionally, a local computer maintains a local CRL and receives updates on the status of certificates (see Figure 1 below).
Figure 1: Certification Revocation List
Source: Microsoft WindowsCertificate signing request (CSR): online certificate status protocol (OCSP). Since CRLs contain a large list of serial numbers of digital certificates, it isn’t always convenient to search for the ones that have been revoked. Instead, it might be suitable to use an OCSP to determine whether a certificate was revoked. The OCSP looks up the specific certificate’s status in real-time. By employing the OCSP solution, the CA repeatedly transmits CRLs to every requesting computer and queries are current, immediate, and direct.
A CSR is an encrypted message that validates the information required by the CA for issuing a certificate. Once it is verified by the CA, CSR inserts the generated public key into the certificate, which is then digitally signed with the private key of the CA.
Certificate: a digital certificate is an attachment to an electronic message that enables an exchange of information over the internet using PKI.
Public key and private key: The Public Key and Private Key pair consist of two uniquely related cryptographic keys which typically consist of long randomly generated numbers. Even though two keys are related, you cannot derive the private key from the public key. The public key is shared publicly or openly with everyone and is used to encrypt the message. Conversely, the private key is kept private to its respective owner and is utilized to decrypt the message encrypted using the public key.
Object identifier (OID): an OID is a string of decimal numbers used to uniquely identify the objects (syntaxes, data elements and other parts of distributed applications). OIDs are usually found in SNMP, X.500 directories and OSI applications where uniqueness is crucial.
What PKI concepts do I need to know for Security+?
You will need to know the following vital PKI concepts for your Security+ exam.
OCSP Stapling: OCSP stapling is a variation of OCSP and is used to determine if a certificate has been revoked. OCSP stapling shifts the burden from the client to the web server, which sends queries to the OCSP responder server at regular intervals to check the status as to whether the certificate has been revoked.
Pinning: pinning is a security feature where a certain web server is linked with a public key to minimizing the risk of forged certificates.
Trust model: as the name suggests, trust is confidence or reliance on another person. A trust model refers to the relationship that exists between individuals or entities. For example, Bob must trust that a public key in Alice’s digital certificate belongs to her. Below, you will learn four types of trust models:
- Direct trust model: this model indicates that a relationship exists between two individuals because they know each other. The trust in a relationship indicates that they trust digital certificates of each other.
- Third-party trust model: in this model, two individuals trust each other’s digital certificates since they mutually trust a third party. In communications over the internet, the third party is usually the certificate authority. For example, in a courtroom hearing, the prosecutor and the defendant might not trust each other, but each of them can have trust in the judge (a third party) due to his impartiality.
- Hierarchical trust model: in this model, a single hierarchy is assigned with one master CA, called the root. A root signs all digital CAs using a single key.
- Distributed trust model: unlike the hierarchical trust model, a distributed trust model involves numerous CAs that sign digital certificates.
Key escrow: a key escrow is a storage process whereby a third party undertakes the responsibility to store private keys in an escrow, which is a centralized management system (see figure 2 below). In the event of a disaster, or when a key is lost, or a cyberattack occurs, a private key can be restored safely from the escrow. A key escrow system is inevitable where highly sensitive information is involved such as state or military secrets.
Figure 2: Key Achieving or Escrow System
What types of certificates are essential for Security+?
Certificate chaining: digital certificates are verified by a process known as a chain of trusts which is the trust relationship between the CAs — namely root CA and intermediate CAs that issue the digital certificates. A chain certificate is a list that shows all the certificates that have been signed at different hierarchical levels by the root CA and the intermediate CAs.
Below, you will learn the types of certificates that are essential for your Security+ exam.
Wildcard and SAN: the wildcard is a public key certificate that can be applied to multiple subdomains of a master domain. One of the principal usages of wildcards is for the security of websites with HTTPS. On the other hand, a subject alternative name certificate (SAN) is a web-server certificate capable of supporting multiple domain names in a single certificate.
Code signing and self-signed: a code signing is an act of digitally signing scripts and executables to affirm the software developer and ensure that the code has not been corrupted, modified or altered since it was signed. On the other hand, a self-signed certificate is signed by the same entity (individual or organization) who created it, rather than a trusted CA.
Email and user: An email certificate, also known as SMIME certificate, is the digital certificate that is employed to sign and encrypt email messages so that their secure transmission can be ensured over the internet. An email message signed with an email certificate can only be read by the intended recipient.
A user certificate is another type of digital certificate that is used for user authentication purposes. Common examples include smart cards or punch cards.
Root: the root certificate is the public certificate that identifies the root certificate authority. This certificate is highly effective, self-signed and sets the foundations of an X.509-based PKI.
Domain validation (DV): a DV is a certificate that can be assigned to a web server for SSL encryption. The CA confirms that the person who receives the DV has control over the domain linked with the SSL.
Extended validation (EV): an EV is the certificate used to provide a high level of authentication and security for HTTPS websites and software programs that prove the legal entity controlling the website.
What certificate formats are critical for Security+?
Distinguished Encoding Rules (DER): a DER is a binary format that is designed to transfer syntax for data structures. It is often associated with Java certificates.
Privacy-enhanced mail format (PEM): a PEM is a common format generally provided by CAs. It’s composed of numbers and letters and is supported across various platforms.
P12 or PKCS 12 (public-key cryptography standards #12): P12 is a binary format used to store a server certificate, intermediate certificate and a private key in one file that can be encrypted and having a PFX format with file extension .pfx and .p12. P12 files are usually used on Windows OS to import and export private keys and certificates.
P7B or PKCS 7 (public-key cryptography standards #7): a P7B is a cryptographic message-syntax standard associated with the .p7b file. Unlike P12, private keys are not included in a .p7b file.
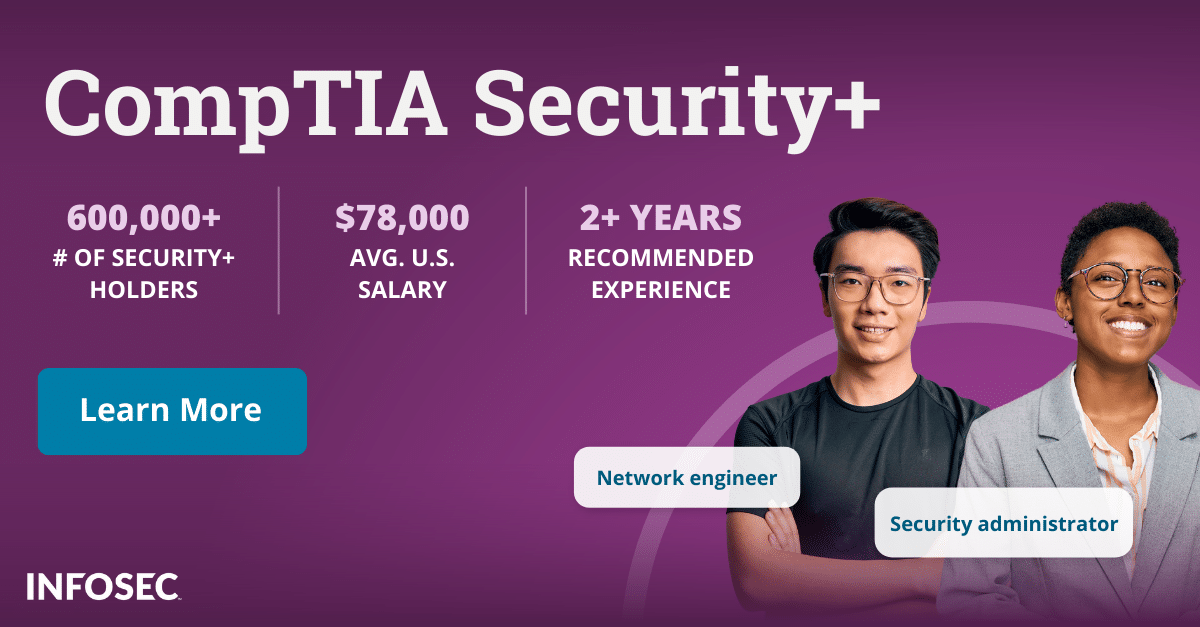
Are you a Security+ aspirant and looking for some help?
Infosec Institute offers a Security+ Boot Camp that teaches you information theory in a compressed time frame, and also reinforces the theory with hands-on exercises that help you “learn by doing.”
For more on the Security+ certification, view our Security+ certification hub. InfoSec also offers thousands of articles on all manner of security topics.