Security+: How to identify Indicators of Compromise and differentiate different types of malware [updated 2021]
Introduction
Indicators of compromise reveal malicious activity on a network or system as well as artifacts that indicate an intrusion with high confidence. The artifacts could involve the use of multiple sophisticated malware. Identifying indicators of compromise and differentiating different types of malware is an integral aspect 0f Security+ SY0-601 exam’s first chapter: "Threats, Attacks, and Vulnerabilities."
There is a push for Security+ exam candidates to understand the concepts in a well-structured, organized manner to clear the first section of the exam and go on to help their current/future employers streamline the processes used in determining, preventing, and reporting security-related events.
With that in mind, here’s how to analyze indicators of compromise and determine the type of malware.
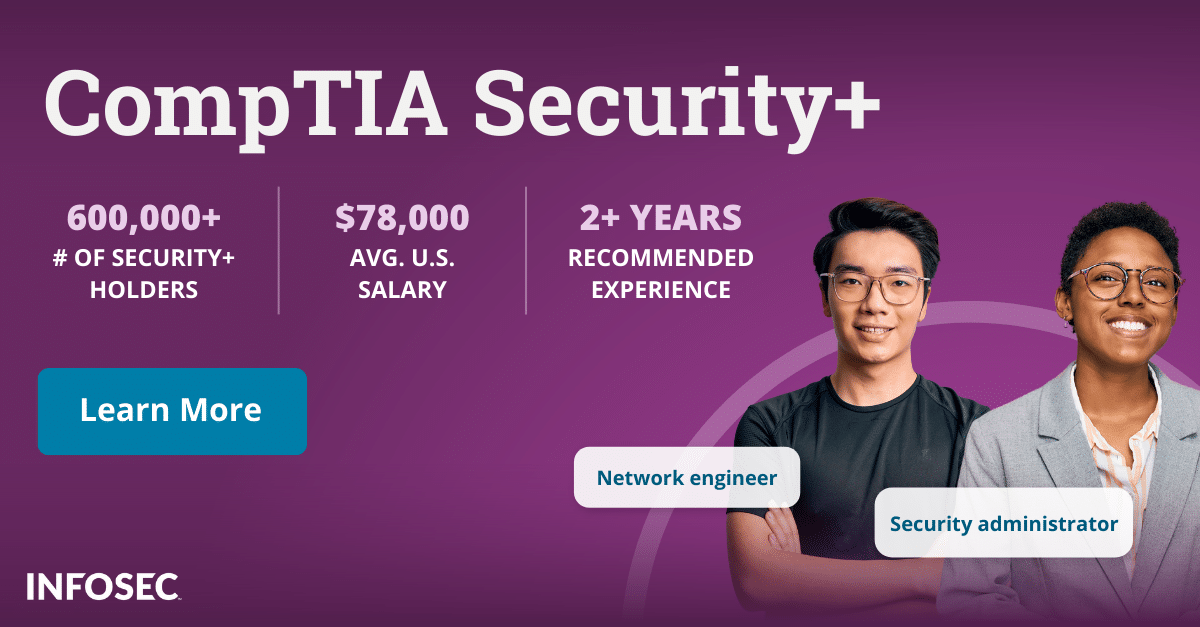
Become a SOC Analyst: get Security+ certified!
More than 47,000 new SOC analysts will be needed by 2030. Get your CompTIA Security+ to leap into this rapidly growing field — backed with an Exam Pass Guarantee.
Crypto-malware
Today’s organizations are on the lookout for any indicators of sensitive data being stolen or decrypted in a crypto-malware attack. Crypto-malware is stealthier than most other forms of malware, and most CPUs are not explicitly made to detect it, which could be detrimental to your system. If someone in your enterprise can’t launch a Microsoft Office document, he/she has saved on the company’s local system and sees nothing but random characters when they force open it to analyze it; there’s a high probability that the machine they're using is infected with crypto-malware.
Logic Bomb
Also referred to as a slag code, a logic bomb is designed to explode (or execute) under conditions such as a failure of a user to react to a command prompt or a lapse of a specific amount of time. After execution, it may be designed to erase critical files, display spurious text, or have other devastating effects. If an organization had someone in to do any custom programming and things went awry after a few weeks, it could be an indicator of logic bomb compromise. Custom programming gives programmers complete access to your system; just the kind someone who wanted to place a trap door, or a logic bomb would desire to have. Hence, it’s important to independently verify the work was done in good faith and correctively.
Ransomware
Several different indicators can help organizations to determine whether a ransomware infiltration has occurred. For instance, a company that has concerns about ransomware should monitor their systems for bulk file renames. Ransomware-based malware can be undertaken rapidly, and if a large number of files were renamed in a short span of time, this could be a visible indicator. Another indicator is when data files on your PC are encrypted, and the encryption process modifies the files, appending extensions to them. If the added extensions aren’t standard, it’s highly likely that a ransomware attack is on the horizon.
Trojan
These are self-contained programs that are created to mimic useful or necessary applications on your system you would never consider as risky. An indicator of compromise could be a message or a command prompt window that pops up and disappears quickly during the use of a program. Applications become suddenly unresponsive to usual commands can also indicate the presence of Trojan. Case in point: if a co-worker shows you a program he/she has been using for a while, and a command prompt opens and closes quickly while you’re being educated on its capabilities, there’s a likely chance that you’re seeing a Trojan malware, which your work colleague may or may not be aware of.
Worms
A type of malware that is capable of rapidly infected many systems on an enterprise network by transmitting copies of itself from one system to another via network connections. At first, they allowed hackers to disrupt network bandwidth, but have evolved to carry payloads (a piece of malware code created to inflict real, tangible harm). Payload-carrying worms can cause several forms of damage ranging from recording keystrokes to deleting Microsoft Office files. An indicator of compromise is a round of systems being infected, with infections occurring in different departments and in scenarios where users didn’t use any programs.
Keylogger
A type of surveillance technology used by cybercriminals to monitor and record keystrokes typed on a victim’s keyboard. Common goals of keylogger malware include stealing login credentials critical enterprise data, and personally identifiable information. In the past few years, keyloggers have become more sophisticated; they are also being used to track sites visited by the target, and only log keystrokes entered on domains of particular interest to adversaries. The indicator of compromise for this type of malware is relatively straightforward. You just must look out for any suspicious activity when it comes to your online accounts (personal and professional)., For instance, if you receive a notification from your email client stating someone accessed your account from outside your town of residence, it could be that your system is infected with keylogger malware.
Adware
Adware is a form of malware whose purpose is to generate money. Adware creators use different tactics to make revenue by showcasing ads forcefully. The malware can modify the victim’s system configuration to show them ads on their internet browser or pop-ups. Adware by itself isn’t a severe cause for concern but become the gateway for other malware, spyware, ransomware, etc. An indicator of compromise could be an employee of your firm experiencing issues with his/her browser. Every time he/she launches Chrome or Firefox, different pop-ups appear after every few seconds, regardless of the website being visited.
Virus
A malicious program that infects and damages a system such as a tablet, a smartphone, or a computer. It contains the ability to destroy data on the device, preventing it from booting up or using resources, resulting in slow down or malfunction. Indicators of compromise include the failure of applications and files to open on the enterprise system. Other includes include hardware (such as scanners) that no longer responds to users’ commands.
Spyware
Spyware is malicious software that collects information regarding a user’s or a group’s habits or activities on a system. If someone in your organization recently searched, and another unauthorized browser popped up to complete it for them, it could be a sign of spyware. If you try removing it, it returns immediately. Another indicator is a reduction in the systems’ connection speed. Since spyware functions in the background, it takes up valuable disk space and can cause severe performance issues.
Rootkit
It’s a software that’s commonly used to obtain root-level access and hide specific things from a system’s OS. One of its symptoms is that a system’s antivirus will keep turning itself off leaving it unprotected. Also, if you or someone within your company is seeing Blue Screens with White Text displaying Windows Error Messages and are continually rebooting, then a Rootkit infection is probable. Additionally, incorrect system clock and date could also be an indicator of rootkit compromise.
Bot
Bots refer to an automated malicious program that gathers information on the internet. Usually, they’re executed from compromised systems that are being remotely controlled by adversaries. An indicator of compromise is that you’re having issues downloading software antimalware software updates or visiting vendors’ sites. Bots often attempt to prevent antimalware software from functioning or being installed. Likewise, you could have issues with downloading operating system updates when hit by a malicious bot.
Backdoor
It’s a malicious program that is used to create a converted channel for aiding adversaries. It can be used to access and control the compromised system even through phones and other mobile gadgets. If you’re surfing the internet and suddenly a weird message appears stating you’re locked out of the PC, it could be a sign of a backdoor malware. Pop-up ads are another indicator; they distract the user from investing other symptoms, such as knowing why a message they didn’t send appeared in their sent message box on Facebook.
Final Verdict
By understanding indicators of compromise, the time from infection to the revitalization of systems can be significantly reduced. Moreover, organizations can use the knowledge to create a higher fidelity in their mitigation efforts, offer stakeholders a detailed picture of the potential intrusion, and provide greater assurance of IT security. Spreading this information internally can further complement direct integration into training programs and security executions.
Identifying indicators of compromise and malware is an integral aspect of the Security+ SY0-601 exam. For more on the Security+ certification, view our Security+ certification hub.