Security+ domain #1: Attacks, threats, and vulnerabilities [updated 2021]
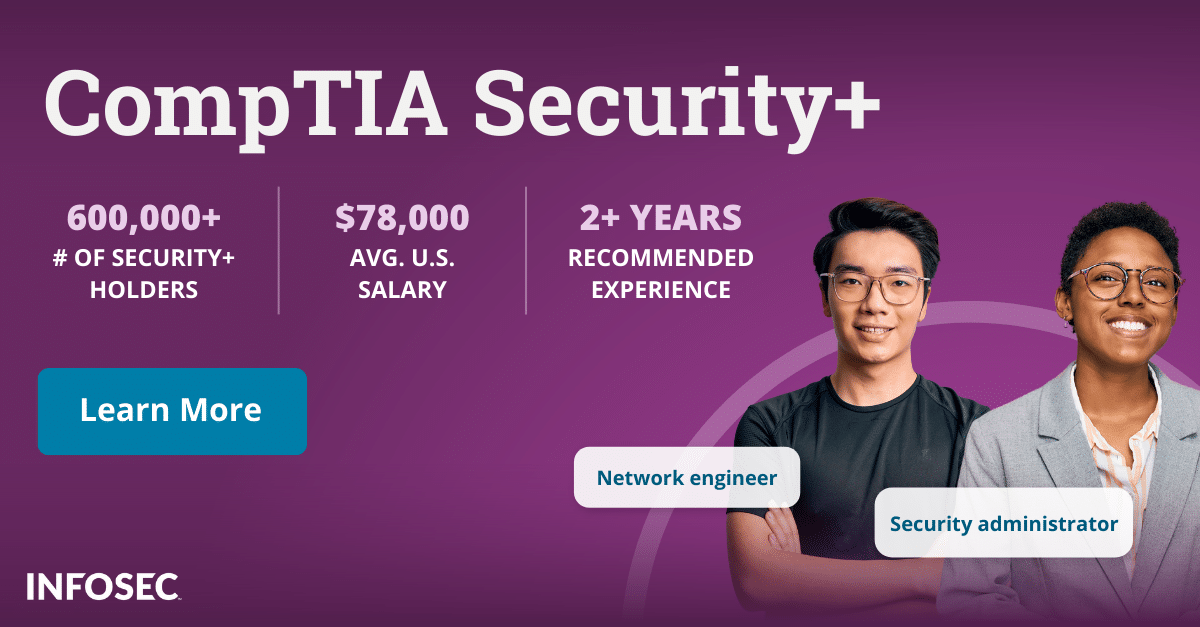
The first domain in CompTIA’s Security + exam (SYO-601) covers threats, attacks and vulnerabilities. This domain contributes 24 percent of the exam score. The Security+ exam’s objectives are covered through knowledge, application and comprehension, and the exam has both multiple-choice and performance-based questions. The performance-based questions are designed to test the candidate’s ability to troubleshoot problems in a simulated environment.
The objective of the treats, attacks and vulnerabilities module is to ensure you can understand and explain different types of security compromises, the types of actors involved, and the concepts of penetration testing and vulnerability scanning. The module covers the following six sections.
Security+ domain 1: Attacks, threats, and vulnerabilities
Attacks, threats, and vulnerabilities is the first of domain of five domains covered on the Security+ certification exam. The exam was last updated in Nov, 2020, and the updated exam subdomains include:
- Compare and contrast different types of social engineering techniques.
- Given a scenario, analyze potential indicators to determine the type of attack.
- Given a scenario, analyze potential indicators associated with application attacks.
- Given a scenario, analyze potential indicators associated with network attacks.
- Explain different threat actors, vectors, and intelligence sources.
- Explain the security concerns associated with various types of vulnerabilities.
- Summarize the techniques used in security assessments.
- Explain the techniques used in penetration testing.
Below is additional information on Attacks, threats, and vulnerabilities that will help you prepare for the Security+ certification exam.
Indicators of compromise and malware types
Malware is malicious software designed to gain access to or damage a computer or system without the user’s knowledge or consent. It’s usually delivered via an email attachment, or link to a malicious site or a legitimate site that’s been infected. Common malware includes:
Viruses:
This malware inserts itself into another program and then propagates from one computer to another, causing detriment on the infected systems.
Ransomware:
Designed to block access to a computer system, often for a financial payout, ransomware can also destroy files.
Trojans:
Typically disguised as legitimate software, Trojans can be used for a variety of tasks, from accessing data to inserting other malware.
Bots:
Derived from “robot,” this automated process can be used for malicious purposes to automate tasks such as opening a back door or stealing data.
Spyware:
Like the name implies, spyware can be used to monitor and transmit information without the user’s authorization.
RATs:
RATs, or remote access Trojans, are typically designed to gain complete control over a computer remotely, using techniques that make them particularly difficult to detect.
Types of attacks
Malicious actors employ a variety of attacks to compromise information systems, and will use any number of these to achieve their goals. The four categories that the Security + test requires candidates to understand include social engineering, application or service attacks, wireless attacks and cryptographic attacks.
Social engineering
This exploit can range from low-tech to very sophisticated, and is often used to describe deceptive techniques that trick the user into a specific behavior. Many forms of social engineering rely heavily on human interaction. Common social engineering techniques include:
Phishing:
Scammers impersonate an individual or entity to lure the end user into actions such as disclosing sensitive information, opening a malware attachment or clicking on a malicious link.
Spear phishing:
A form of phishing, this technique is more personalized and targets specific individuals or entities.
Whaling:
Another form of phishing, whaling targets high-ranking individuals such as managers and executives within the organization.
Application or service attacks
Rather than targeting humans, these types of attacks compromise an information system (IS) resource, such as a website, online service or a cloud-based app.
Wireless attacks
These include attacks on wireless systems such as secure WiFi networks and RFID (radio frequency identification) systems, used commercially for tracking objects.
Cryptographic attacks
These are attempts to find weaknesses and circumvent the security of cryptographic systems, which are used for secured, or encrypted, data and communication.
Types of threat actors and their attributes
To protect IS, you need to understand your adversary. Threat actors can be internal or external and have different motivations as well as sophistication levels and resources. Here are some examples:
Nation-state:
Responsible for a large number of high-scale and high-profile attacks, these actors are sponsored by nation-states and have a very high level of resources and sophistication. They can carry out advance persistent threats (APTs) that go undetected for months and even years.
Insiders:
Internal actors may act maliciously or simply be careful or negligent. They pose a major threat because it’s much easier for attackers to gain access to information systems via insider credentials.
Script kiddies:
This term refers to actors that lack their own skills to write malicious code and instead rely on programs or scripts created by others.
Penetration testing
White hats — also known as ethical hackers — use penetration testing to evaluate IS defenses. Penetration testing involves a special team — outside of the IS administrator or internal security team — that carries out an authorized, simulated attack using a variety of tools. Referred to colloquially as a pen-test, it’s different from vulnerability scanning because it actively exploits weaknesses in the system rather than searching for them.
Vulnerability scanning
Vulnerability scanning passively scans the system for weaknesses, typically on an ongoing or regular basis. Performed by internal security teams or a managed security service provider (MSSP), vulnerability scanning can also detect and alert to changes in the IS environment.
Vulnerabilities may result from, among other things, a lack of proper security protocols and procedures, and from misconfigured systems, both hardware and software. Certification candidates must be able to explain vulnerability scanning concepts while differentiating between intrusive and nonintrusive testing, as well as identifying common misconfigurations.
Impacts related to different vulnerabilities
The final section of the module has a broad range of topics focused around the candidate’s ability to explain the impacts associated with different types of vulnerabilities. While vulnerabilities differ in their impact, malicious actors may only need to exploit one to gain a foothold inside the IS. They’re simply looking for one weak link.
Examples of the vulnerabilities addressed on the test:
Embedded systems
When connected to the internet, embedded systems can be used to compromise IS, and while the number of embedded systems is growing rapidly, they often lack robust security protocols and are challenging to patch.
Zero-day vulnerabilities
These are security holes in either software or hardware that are not yet known to the developer, which means a publicly released patch is not available.
Improperly configured accounts
More likely a process rather than technical issue, improperly configured accounts can give users much higher access privileges than their jobs require. Problems can also result when accounts aren’t reconfigured after a user changes roles, or aren’t deleted at all.
Conclusion
The skills and knowledge that the threats, attacks and vulnerabilities module assesses are critical in today’s digital environment where organizations of all types and sizes collect, process and store data, making them attractive targets to bad actors. The expertise demonstrated on this exam is applicable to all sectors, whether you’re interested in working for a business, government agency or nongovernmental organization such as a nonprofit.
For more on the Security+ certification, view our Security+ certification hub.
Sources
- CompTIA Security+, CompTIA, Inc.