Security+ and the DoD 8570 [updated 2022]
DoD 8570 and How Security+ Fits in
The Department of Defense document DoD 8570.01-M (11/10/2015) provides guidance and procedures for the training, certification and management of the DoD workforce conducting Information Assurance (IA) functions. As stated in the document, it applies to the Office of the Secretary of Defense (OSD), the Military Departments, the Chairman of the Joint Chiefs of Staff, the Combatant Commands, the Office of the Inspector General of the Department of Defense, the Defense Agencies, the DoD Field Activities and to all other organizational entities within the Department of Defense.
It sounds like a mouthful, to be sure, but it all boils down to creating a common understanding of the responsibility of individuals to use the resources at hand to protect the security and integrity of vital information. More particularly, it applies to the DoD Global Information Grid (GIG), to enhance its protection and assure its availability only to appropriate information handlers. We keep the bad guys out and make sure only appropriately authorized good guys have access.
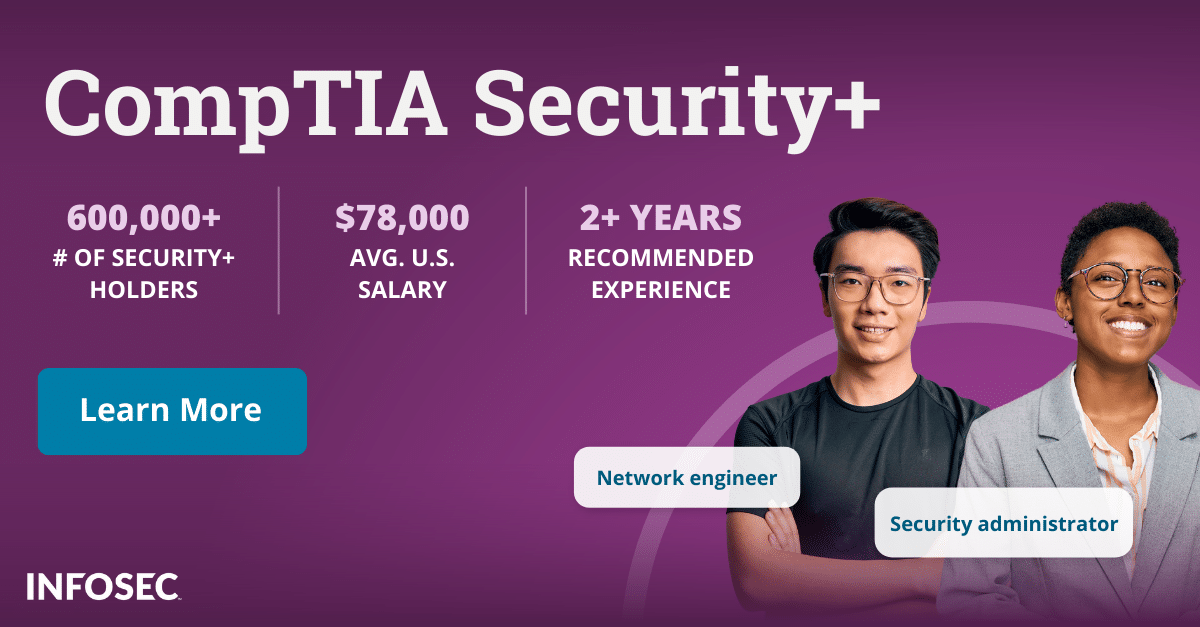
Become a SOC Analyst: get Security+ certified!
More than 47,000 new SOC analysts will be needed by 2030. Get your CompTIA Security+ to leap into this rapidly growing field — backed with an Exam Pass Guarantee.
Other primary functions include:
- establishing a baseline in technical and management Information Assurance skills;
- providing qualified IA personnel according to job category, specialty and level;
- verifying those skills via standard certification and testing; and
- continuously growing and augmenting the knowledge thus obtained.
A lot of reading…
Directive 8570 is, at the time of writing, a 96-page document that continues to expand as new requirements are developed. How does it attempt to cover the subjects mentioned above? What are its goals and objectives? What is the DoD's actual Cyber Strategy?
We'll find answers as we address these questions:
- How does Security+ fit in with the DoD 8570?
- What are the qualification requirements for the IA Workforce?
- What IA Levels include Security+ as a prerequisite?
DoD's Cyber Strategy
Origins
In 1961, the Space Task Group (STG) was desperately trying to launch a man into Earth orbit, playing catch-up with the (then) USSR under a great deal of pressure from the government of the day. Up until that point, all calculations for rocket trajectories, launch vectors, launch windows and go/no-go for reentry into the atmosphere were all calculated by computers.
And, no, not our wonderful, modern, silicon marvels. In this case we're talking about the West Area Computing Unit, an isolated, overlooked unit of the National Advisory Committee for Aeronautics (NACA—precursor to NASA) at Langley. It was composed entirely of college-graduated African American women mathematicians, who did all the immensely complex calculations by hand and by dint of long hours of prodigious effort.
To get John Glenn into space, NASA acquired an IBM 7090 mainframe, one of the very first. It helped, but wasn't quite up to the task at first, so the West Area Computing Unit still did the bulk of the work.
That computer could have been knocked out with the world's simplest computer virus, and no technician then alive would have had the ability to counteract it. Luckily computer viruses hadn't been invented yet and their naiveté did them no harm. That can no longer be said today.
The Mission Force
The DOD’s Cyber Mission Force structure employs ~6,200 cyber-operators split into three specific divisions which are responsible for:
- Defense of the DoD's own networks (68 teams);
- Protection of U.S. homeland and U.S. vital interests against cyber-attacks (13 teams); and
- Provision of full-spectrum cyber capabilities for military OPS (27 teams), along with 25 additional teams to provide support (as needed) for #1 and #3.
Unification
Each branch of the military was running its own cyber platform that was completely different from everybody else's iteration or design. The systems were redundant, poorly integrated, and had poor interoperability.
Ever since the issuance of the new strategy in April/2015, the intent has been to develop a unified platform that will bring everything together into a logical whole. Some good progress has been made.
As an example, the Standard Army Ammunition System (SAAS) got an update which eliminates much of the manual work, allowing management, shipment and deployment of ammunition to where it is needed. It all happens in a cloud-based environment with a familiar interface that is much easier to use (Microsoft Office-like). It also provides an enhanced ability to deny access to unauthorized individuals. It will be replaced with a wholly integrated system (still in development) in 2022.
Clear policy
Although the Pentagon had policies prior to 2011, they weren't made public except for some leaked documents that were supposed to be classified. By contrast, the 2015 document makes a point of addressing Pentagon cyber capabilities (both operational and offensive), not only to enhance transparency for the public, but to make international policy declarations and responses more tangible in terms of responses to attacks.
Irrespective of your political affiliation, recent events show that we're not bulletproof yet, though we're succeeding in making it more and more difficult for international criminals to breach our systems.
This includes a new See Something, Say Something policy for the Hack the Pentagon initiative (actually called the Vulnerability Disclosure Policy). Now there is a legal and protected method for ethical hackers to reveal weaknesse in the Pentagon Security system. Following on that, a Hack the Army initiative was launched with the same protection for security specialists to uncover weaknesses and report them.
Where You Come In
 Information Assurance Technical and Information Assurance Management (IAT & IAM, respectively) have specific requirements. Many people, companies and organizations that wish to do business with the DoD sometimes fail to realize that they must meet the requirements of 8570 as well, as a condition of doing business with the government.
Information Assurance Technical and Information Assurance Management (IAT & IAM, respectively) have specific requirements. Many people, companies and organizations that wish to do business with the DoD sometimes fail to realize that they must meet the requirements of 8570 as well, as a condition of doing business with the government.
A company that manufactures bulldozers that the military would buy would have to have some limited access to the military inventory systems, as well as payroll or accounting, in order to be paid for their work or products. They might need access to shipping and receiving manifests, scheduling for deliveries or any number of other points that could create a point of vulnerability in the network.
The military won't do business with a company that doesn't comply with 8570. It is simply self-protection. So even working in the public sector, if you are creating a product or service that might be useful to the DoD, you're putting yourself out of the running for that potential business or income if you're not compliant.
Public, Private or Government
CompTIA's Security+ is a DoD-approved 8570 baseline certification required for some position categories or specialties and levels.
If you're providing Information Assurance services, even if you're not currently doing business with the government, it behooves you to follow their certification requirements (or better) for your own protection, and against future need. Even working for someone else who, in turn, is supplying materiel or services for the government may require you to be compliant.
For compliance with 8570's Information Assurance Management (IAM) Level I positions you must have CAP (the (ISC)² Certified Authorization Professional), GSLC (GIAC Security Leadership Certificate) or Security+ CE (CompTIA Security+ Computer Environment).
In addition, Security+ CE, a CompTIA exam focusing on cybersecurity issues with an element of Continued Education, is suitable for those in a DoD IAM position Level 1: computing environment information assurance.
For compliance with Information Assurance Technical (IAT) Level II positions, any of the following, including GSEC (GIAC Security Essentials Certification), SSCP (the (ISC)² Systems Security Certified Practitioner), or, of course, the Security+ CE (CompTIA Security+) are required.
For those wishing to perform specialty work within the space, it should be noted that PenTest+ is valid as baseline certification for Cybersecurity service provider (CSSP) analyst, CSSP incident responder and CSSP auditor.
CompTIA Security+
The advantage is that Security+ covers both positions, but is also versatile in other ways. If you enjoy computer networking and want to diversify into Network Security, this is definitely the certification for you. Learning the finer points of Network Security will make you the first line of defense for any organization you work with or for.
You'll be managing access through account and infrastructure control, protecting data by encoding it with your cryptography skills. Your extensive knowledge of privacy laws will enable you to determine who should be allowed to access which information in the database, and which information must be utterly private and confidential.
As a bonus, if you already hold a Network+ or A+ certification, they are automatically renewed when you obtain or renew your Security+ certification. The rule is that you only have to certify or re-certify your highest certification, and the lesser ones are automatic.
Career Horizon
With continuing development you can become a Security Architect or Security Engineer, developing networks that are safe and secure, but still easy to use. You'll implement intrusion detection, encryption and, of course, firewalls to keep systems safe.
You may become a Security Consultant—the sort of person who comes in after the Security Architect and Security Engineer have created the original network—and advise how to increase protection or upgrade the network based on evolving needs.
The single greatest need for DoD 8570 is for Information Assurance Professionals (IAP). Just like hospitals, which have massive amounts of information about their patients that must be protected, the DoD also has a great deal of information which must remain secure.
The Takeaway
The demand for security professionals is only growing, so IAPs have a bright future ahead of them, keeping private things private while making sure that essential data, logistics and information are available to qualified users. Keeping the bad guys out is a full-time occupation. Military or otherwise, the Security+ certification is one of your best assurances of a long and satisfying career.
For more on the Security+ certification, view our Security+ certification hub.