Welcome to the World’s Largest Public Hacker Database
As a security researcher and information security enthusiast, I have always been interested with OSINT (Open Source Intelligence), and the profiles and biographies of white hats, black hats and hacktivists. I am very amused with some of the hackers' stories and contributions to the cyber world, not to mention the humorous truths about how they live their life. Through my constant research and Google adventures, I came across a site named SOLDIERX.COM, a website of the community called SOLDIERX.
SOLDIERX is a community of hackers, developers, phreakers, DEFCON goers (some members were speakers during the convention), penetration testers, security geeks, OSINT lovers, etc. Those who are trusted and are committed to the group's main goal of information insemination belong to the 'SOLDIERX CREW,' lead by the High Council President named 'RaT.' I will not be discussing the status and structure of their group based on what I have read in their forums but if you are really that interested, more information about how the group was formed can be found here which contains the history of the SOLDIERX community.

What should you learn next?

The SOLDIERX website has some cool pages and sections too like the Forums where registered users can share their innovative ideas, the Blog page where registered users can express their feelings, the Tools collection where projects and tools released by the SOLDIERX members under the SX Labs section can be found, including the security and vulnerability aggregators which can be seen on the right side of the website, and the Tutorials page.
But what really keeps me coming back to this website is their very own Hacker Database, also known as the SOLDIERX HDB. Alright I admit it! I love the tutorials in their website such as the new exploit tutorial entitled "Stack Smashing On A Modern Linux System," but the weekly dose of hacker database entries, the controversial and sometimes humorous information on some hacker profiles made me addicted to keep going back to their site.
The SOLDIERX HDB is the world's largest public hacker database on the net and is rumored to be rivaled only by the FBI's hacker database. Their hacker database contains a list of programmers, developers, black hats, white hats, security researchers, fake ethical hackers, hacktivists, packet kiddies, click kiddies, script kiddies, security professionals, heroes of computer revolution (Hello Steven Levy), hardware hackers, ch1xors (oh yes! although some people believe that they are non-existent), game hackers, and those who have embraced and embodied the hacker culture. Most entries (although not all) in the HDB can be considered hackers in accordance to Steven Levy's description of hacker ethics and principles:
- Access to computers—and anything which might teach you something about the way the world works—should be unlimited and total. Always yield to the Hands-on Imperative!
- All information should be free.
- Mistrust authority—promote decentralization.
- Hackers should be judged by their hacking, not bogus criteria such as degrees, age, race or position.
- You can create art and beauty on a computer.
- Computers can change your life for the better.
Anatomy of an HDB Entry
Now let me introduce you to how an HDB entry is written based on the sample screen shot I took of a certain hacktivist from China named y0c0 smart, who is also the leader of the Silic Group Hacker Army. I consider this HDB entry a dox!
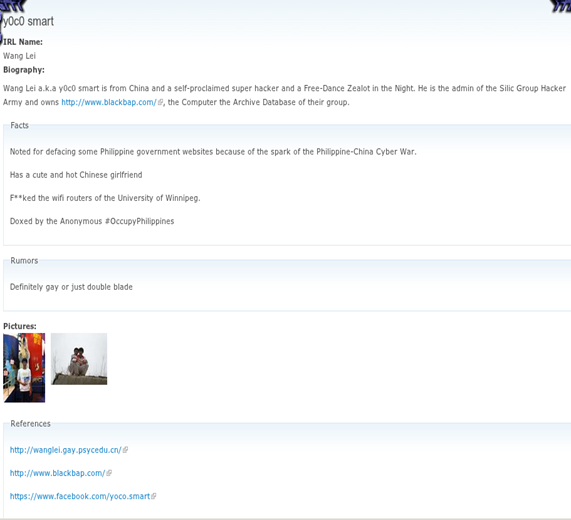
The first part of the page is the handle of the person in the entry which is obviously y0c0 smart. Below you can see the person's IRL (In Real Life) Name, the Biography which introduces the person's achievements or how he or she rose to fame, then the Facts which is a unique description or exceptional information of the person in the entry, the Rumor part which is often a humorous description or controversial information about the person in the entry which could possibly be true or false (I wonder how they got some of the rumor entries), and the References which contains the links of the person's information and detailed sources.
Sample Entries in the HDB
There are some good entries I have found in the SOLDIERX HDB that I like to be featured in this write-up, but I guess it will just make for a very long article that might bore you so I just made a short description of the biographies or entries that might interest you:
- Acid Phreak - one of the three founders of the hacking group Masters Of Deception (MOD).
- Andrew S. Tanenbaum - wrote the first open-source clone of UNIX, called MINIX.
- Anthony Desnos - the developer of Androguard, a set of tools for reverse engineering Android applications.
- Bernd Ulmann - the guy behind fafner.dydndns.org (a free OpenVMS cluster you can play with) which is a VAX 7000/820 (and thus a two processor VAX) running OpenVMS 7.2.
- Birdman - the creator of Taiwan's first widespread Trojan called BirdSPY.
- Bruce Schneier - an internationally renowned security technologist, cryptographer, computer security specialist, and author.
- Chanda Leir - the first ch1xor featured in the Phrack Magazine.
- Chen Ing-Ha - the creator of Chernobyl virus, one of the most damaging viruses of all time.
- Craig Heffner - The WPS (WIFI Protected Setup) vulnerability was independently discovered by this guy but Stefan Viehböck of Austria was the first guy who reported the vulnerability and released the information about it to US-CERT. He is also the guy behind 'reaver' and 'wash'.
- c0mrade - the handle of Jonathan James who was the first juvenile incarcerated for cyber crime in the US for the computer intrusion of the Defense Threat Reduction Agency, a division of the United States Department of Defense.
- DarkCoderSc - the coder or developer of DarkComer-RAT (Remote Administration Tool), Browser Forensic Tool, Mirage Anti-Bot, and other tools.
- Dark Dante - the handle of Kevin Lee Poulsen, a hacker turned journalist.
- Darkoperator - a Metasploit Community Developer and contributor at The Metasploit Project and the BackTrack Linux project.
- David L. Smith - the writer of the Melissa worm.
- Eric Steven Raymond - a.k.a ESR, the maintainer of "The New Hackers Dictionary" which is formerly known as the Jargon File.
- Fluffi Bunni - He has defaced security websites like SANS Institute, Security Focus, and Attrition.org, but was then arrested last April 29, 2003 in London while attending InfoSecurity Europe 2003.
- Fyodor - the author of the Nmap Security Scanner.
- Guido van Rossum - the Benevolent Father and creator of the Python programming language.
- HD Moore - the founder of the Metasploit Project.
- Ian Murdock - the founder of Debian Linux project.
- ioerror - the co-founder of the hackerspace 'Noisebridge' and known for his research into Cold Boot Attacks on encrypted systems in order to retrieve keys stored in DRAM, and for identifying a vulnerability in the Internet Public Key Infrastructure allowing the creation of rogue Certification Authority certificates trusted by all common web browsers.
- iSKORPiTX - the infamous mass website defacer from Turkey who, on 2006, was responsible for the biggest Mass Website Defacement in webhosting history. He has a lot of defacement notifications at Zone-H.
- Jericho - the owner of Attrition.org.
- Joanna Rutkowska - she is the leader of a team of researchers that released Blue Pill, the first virtualization-based rootkit with nested hypervisors support.
- Jonathan Brossard - a security researcher who created a proof-of-concept backdoor which he called Rakshasa that replaces a computer's BIOS and can compromise the Operating System at boot time without leaving traces on the hard drive.
- Julian Paul Assange - the founder of WikiLeaks.
- Keatron Evans - the Senior Instructor and Director of Training Services of Infosec Institute's Intense School, one of the writers of Infosec Institute, and one of the two lead authors of "Chained Exploits: Advanced Hacking Attacks From Start to Finish."
- Kyriakos Economou - one of the contributors of the Infosec Institute Resource page who wrote an article on how to bypass IObit Protected Folder's Authentication.
- Icamtuf - the handle of Michał Zalewski, a known vulnerability hunter and security researcher who exposed critical vulnerabilities in Microsoft's Internet Explorer and Mozilla Firefox, and who has also developed a lot of tools for Unix-like operating systems.
- Linus Torvalds - he initiated the development of the Linux Kernel after his frustration with MINIX.
- loganWHD - the lead developer of Social-Engineer.Org and the author of the best-selling book Social Engineering: The Art of Human Hacking.
- Marcin Kleczynski - the CEO and Founder of Malwarebytes.
- Meister - a Tunisian hacker and tools developer who is the owner of th3-0utl4ws.com.
- Michael Buen and Onel de Guzman - Who is really the author of the 'I LOVE YOU' virus? The said virus made history in the field of computer viruses because it swept through banks, securities firms, and web hosting companies and forced the Pentagon, CIA, the British Parliament, and most large corporations to completely shut down their mail systems. Check out these two entries which explain the story behind the lovebug which was completely misunderstood by the public.
- Nagareshwar Talekar - the founder of Security Xploded.
- OussamiO - the developer of the first Tunisian Remote Administration Tool called Lost Door.
- Raffaele Forte - the founder and lead developer of the BackBox Linux project.
- Sabu - the leader of the Anonymous group LulzSec.
- Sanjay/Jay Bavisi - the co-founder and president of EC-Council - the company behind the Certified Ethical Hacker (CEH) security certification.
- schiz0id - the website administrator, owner and maintainer of elite-hackers.com, a site intended as a joke for teenage hacker wannabes and script kiddies.
- Slug - the lead programmer of the first computer video game, Spacewar!
- Space Rogue - one of the members of L0pht until 2000 and ran the Hacker News Network (hackernews.com) during his time in L0pht.
- Sven Jaschan - the writer of Netsky and Sasser worms.
- th3j35t3r - a hacktivist known for his successful take downs of websites like Jihadi recruiting websites, WikiLeaks, 4chan, the Westboro Baptist Church, the hacker collectives Anonymous and LulzSec, Iranian President Mahmoud Ahmadinejad and a PsyOps hack of Libyan online newspaper where he inserted articles describing soldiers loyal to the regime defecting in droves.
- The Mentor - a member of the hacker groups Extasyy Elite and Legion of Doom and the author of the famous 'The Conscience of a Hacker' (Hacker Manifesto).
- Thomas Cannon - the founder of Santoku Linux project and known for the 'Android Data Stealing Vulnerability'.
- Trevelyn - the handle of Douglas Berdeaux, the founder of WeakNet Laboratories and the main developer of WEAKERTHAN Linux (a penetration testing distro).
- Tsutomu Shimomura - a Japanese-American scientist and computer security expert who really got pissed with Kevin Mitnick and was responsible for the track-down and capture of Mitnick.
- weev - an American computer security expert and an Internet troll whose computer security group, Goatse Security, was responsible for the incident in 2010 where millions of iPad users' email addresses were scraped from poorly-secured AT&T servers.
- Woz - the handle of Steve Wozniak, the co-founder of Apple Inc. and believed to be the first major troll in the computing age.
- Y0da - the developer of LordPE (a reverse engineering tool) and Y0da PE packer.
- Ying Kracker - a hot ch1xor from China who is included in the 'Top 5 Hottest and Sexiest Hackers in the World'.
- Zenofex - the founder of the GTVHacker group.
I hope you guys enjoyed reading the HDB entries that I have linked to in this article. There are still other entries that are more interesting which I may have missed but you can just browse through the pages of the Hacker Database and I wish you good luck with that. :)
Conclusion
I think the SOLDIERX HDB should be given honors by the OSINT community for one of the techniques used by the HDB curators which is open source intelligence based on the References part, because of the information collected from public sources like the media, forums, doxes, defacements, social media, blogs and other stuffs harvested from the net, and also for the public hacker database which is somehow educational and funny (because of the rumor section), and conforms to free information, just like what the SOLDIERX website says, "Nobody Can Stop Information Insemination".
References:

What should you learn next?
http://en.wikipedia.org/wiki/Hackers:_Heroes_of_the_Computer_Revolution






