Tax-Related Scams
US authorities are warning about a significant increase in the number of Tax-related frauds concomitantly the Tax season. The Internal Revenue Service (IRS) confirmed cyber criminals are intensifying their activity, adopting new techniques to monetize their efforts.

What should you learn next?
Security researchers and Government experts that are monitoring the fraudulent activities related to tax-related scams confirmed the increase of phishing activities in this period.
Since 1955, for people living in the United States, the Tax Day is April 15th. Due to Emancipation Day in Washington, D.C., (which is observed on the weekday closest to April 16), when April 15 falls on a Friday, tax returns are due the following Monday; when April 15 falls on a Saturday or Sunday, tax returns are due the following Tuesday.
This year, the Tax Day will be Monday, April 18th, for this reason, security experts believe that we are in a crucial phase in which crooks will try to deceive victims with malicious messages that pretend to be from the IRS.
In February, an IRS bulletin reported a 400 percent surge in tax-related phishing and malware incidents, in fact, the Government agency reported 1,026 malware and phishing incidents, compared to 254 this time last year.
The IRS is warning taxpayers of newer forms of attacks aiming victims into disclosing credentials to third-party tax preparation service accounts.
"The Internal Revenue Service renewed a consumer alert for e-mail schemes after seeing an approximate 400 percent surge in phishing and malware incidents so far this tax season." states the bulletin. "The emails are designed to trick taxpayers into thinking these are official communications from the IRS or others in the tax industry, including tax software companies. The phishing schemes can ask taxpayers about a wide range of topics. E-mails can seek information related to refunds, filing status, confirming personal information, ordering transcripts and verifying PIN information."
The IRS Commissioner John Koskinen defines "dramatic" the situation and invites taxpayers to watch out for scammers.
"This dramatic jump in these scams comes at the busiest time of tax season," said Koskinen. "Watch out for fraudsters slipping these official-looking emails into inboxes, trying to confuse people at the very time they work on their taxes. We urge people not to click on these emails."

Figure 1 - IRS Building
Fraudsters are intensifying their operations in this period; a common attack scenario sees victims receive an email containing links to the domain hosting an exploit kit, such as Angler EK, that serves malware to the visitors. In other cases, the attackers used malicious emails with attachments that include documents embedding malicious macros. Once the victims open the document and enable the macros, the embedded code drops a malware on the victim's machine, including dreaded ransomware like CryptoLocker, TeslaCrypt and Locky.
The IRS recently provided the following statistics on Tax-related fraudulent activities:
- There were 1,026 incidents reported in January, up from 254 from a year earlier.
- The trend continued in February, nearly doubling the reported number of incidents compared to a year ago. In all, 363 incidents were reported from Feb. 1-16, compared to the 201 incidents reported for the entire month of February 2015.
- This year's 1,389 incidents have already topped the 2014 yearly total of 1,361, and they are halfway to matching the 2015 total of 2,748.
Once cybercriminals obtain PII, they use corrupt tax preparation companies or online tax software to file fraudulent tax returns with the stolen identity information. The only legitimate information needed by crooks to file a fraudulent tax return is a name and social security number of the victims.
This data could be obtained in different ways, computer hacking, the online purchase of stolen PII, the physical theft of data from victims or third parties, the impersonation of government officials through phishing and vishing, the theft of electronic medical records, and OSINT researches.
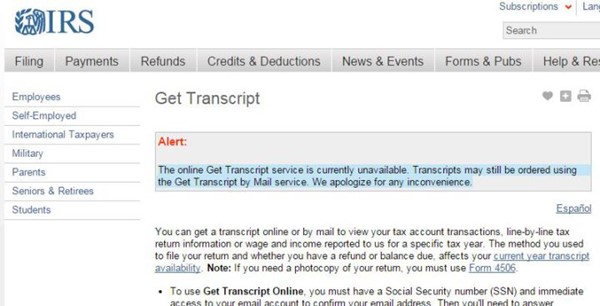
The "Get Transcript" Hack
Recently, IRS services were abused by cyber criminals, in May 2015 the Internal Revenue Service was breached by hackers that "used an online service provided by the agency" to access data for more than 100,000 taxpayers.
Following the incident, the IRS issued an official statement revealing that hackers exploited the "Get Transcript" service that in normally used by taxpayers to get a transcript online or by mail to view their tax account transactions.
To obtain a transcript online, the users have to provide a Social Security number and an active e-mail address. Once the e-mail address is confirmed as legitimate, the IRS procedure requests some questions about personal, financial, and tax information from the users before making the transcript available for the download.
The hackers bypassed the security screen requiring user information such as SSN, date of birth, and street address to access taxpayers' data.
The IRS counted more than 200,000 attempts, about half of them were successful. The IRS was forced to interrupt the service temporarily, officials at the Government Agency confirmed that the service was targeted by the hackers in a two-month period between February and mid-May.
"The online Get Transcript service is currently unavailable. Transcripts may still be ordered using the Get Transcript by Mail service. We apologize for any inconvenience." states the message on the IRS page.
Figure 2 - IRS Get Transcript Service
"In all, about 200,000 attempts were made from questionable email domains, with more than 100,000 of those attempts successfully clearing authentication hurdles," an IRS spokesperson said in a statement to reporters. "During this filing season, taxpayers successfully and safely downloaded a total of approximately 23 million transcripts."
In August 2015, the Internal Revenue Service provided an update on the incident, revealing that 334,000 taxpayers (more than three times it initially estimated) may be affected by the hack announced in May.
The data recently shared by the IRS has confirmed that the Agency detected roughly unauthorized attempts using 464,000 unique SSNs, and 101,000 attempts allowed crooks in generating PINs.
The U.S. Internal Revenue Service confirmed that cyber criminals abused the Electronic Filing PIN application running on irs.gov that allows taxpayers to generate a PIN that they can use to file tax returns online.
The Government Office hasn't provided further details on the attack neither revealed how hackers bypassed authentication mechanisms. In March 2015, the popular security expert Brian Krebs reported for first the risks related to the access to the IRS' transcript service.
The expert explained that someone had already registered through the IRS's site using his Social Security number and an unknown email address. The hackers had used the personal information of the taxpayers to get a refund direct deposit.
"If you're an American and haven't yet created an account at irs.gov, you may want to take care of that before tax fraudsters create an account in your name and steal your personal and tax data in the process." wrote Krebs on this blog.
Krebs and other security experts highlighted that the authentication mechanism implemented by the IRS service is based on the knowledge of user personal information (knowledge-based authentication). The problem with this kind of authentication process is that information used never changes, making possible for an attacker to gain them in various ways.
SSN numbers, email addresses, and other PII are very easy to acquire in the criminal ecosystem, numerous black markets in the Dark Web offer them. Data breaches of Anthem and CareFirst have made available on the criminal underground PII belonging to million customers.
"The IRS is continuing to conduct further reviews on those instances where the transcript application was accessed, including how many of these households filed taxes in 2015. It's possible that some of these transcript accesses were made with an eye toward using them for identity theft for next year's tax season," a statement form the IRS explained.
Tax-Related Phishing, it's a final rush
Experts at security firm Proofpoint are monitoring the recent wave of Tax-Related phishing campaigns and the Tactics, Techniques and Procedures (TTPs) used by threat actors.
The experts noticed a degree of sophistication and pervasiveness in the techniques implemented by the crooks in the wilds.
"Tax-related phishing is something of an annual phenomenon, but Proofpoint researchers are seeing a degree of sophistication and pervasiveness that sets this year apart," states a report published by the Proofpoint firm that analyzes tax fraud trends.
Cyber criminals are trying to exploit new habits of taxpayers, for example, their propensity to use mobile devices. Experts at Proofpoint discovered, for example, a mobile-optimized phishing site that appears as a legitimate tax. Meanwhile, several ISPs have already shut down some tax-related phishing sites hosted on major providers.
Criminal organizations are also conducting tax-related voice-phishing campaigns to obtain information to use in the fraudulent activities.
Adam Meyer, chief security strategist for SurfWatch, explained that his research has seen a surge in tax-related vishing attacks this year.
"They're filtering by name people who tend to have a foreign name to exploit their lack of English skills as well as the fact they likely they don't understand our tax system as well as people who have grown up with it," he says.
The principal ingredient for tax-related frauds are user data, due to a sustained demand for this precious commodity, criminal organizations are fueling the principal black markets in the dark web with this precious information.
Attackers are using this data to abuse of the IRS' electronic filing PIN verification system and file a fake return under on the victim's behalf and requesting the payment through a fraudulent bank account.
The FBI confirmed a significant increase of the Stolen Identity Refund Fraud (SIRF), which is the fraudulent acquisition and use of the Personally Identifiable Information (PII) of US persons or visa holders to file tax returns. Crooks send the fraudulent tax returns to bank accounts or pre-paid cards that they control.
Victims of this kind of crimes are specific categories of individuals like homeless and prisoners.
"SIRF is relatively easy to commit and extremely lucrative for criminal actors. While all U.S. taxpayers are susceptible to SIRF, over the past year, criminal actors have targeted specific portions of the population, including: temporary visa holders, the homeless, prisoners, the deceased, low-income individuals, children, senior citizens, and military personnel deployed overseas." states the FBI.
Experts at ProofPoint are worried by the availability of tax phishing kits that have reached a high level of quality.
These kits are available for sale in the principal black market places and implements some features that allow crooks to avoid detection.
"Sophisticated phishing kits custom-made for tax season dramatically boost threat actors across the spectrum to go after the taxpayers. Whether optimized for mobile (in the case of the fake tax preparation software) or "hiding in plain sight," these kits are powerful tools for cyber criminals. We even observed a kit correctly using SSL, leveraging the secure form-delivery capabilities of the particular service provider they used. Correctly signed certificates make the phishing sites harder to detect for end users, web browsers, and security providers, giving attackers a leg up during tax season—even with commodity kits." states ProofPoint.
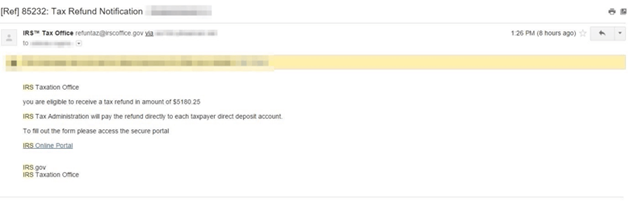
Figure 3 - Tax-related phishing email (Proofpoint)
W-2
phishing campaigns
This year, security firms and government agencies are observing some new worrying attacks targeting businesses with W-2 phishing campaigns. W-2 information could be used by fraudsters to file victim's taxes and request refunds in their name. Experts noticed a significant increase in W-2 phishing campaign because the W-2 information could be used by fraudsters to file victim's taxes and request refunds in their name.
Recently the popular security expert Brian Krebs revealed that cyber criminals tricked an employee at the data storage company Seagate Technology into giving away W-2 tax documents on all current and past employees.
The leaked documents include Social Security numbers, salaries and other personal data that could be used by criminals for illegal activities. This data would be used by hackers to file phony tax refund requests.
According to Seagate, the incident occurred on March 1st, but Brian KrebsOnSecurity was informed of the case from a former Seagate employee who received a written notice from the company.
"On March 1, Seagate Technology learned that the 2015 W-2 tax form information for current and former U.S.-based employees was sent to an unauthorized third party in response to the phishing email scam," announced the Seagate spokesman Eric DeRitis said. "The information was sent by an employee who believed the phishing email was a legitimate internal company request."
"When we learned about it, we immediately notified federal authorities who are now actively investigating it. We deeply regret this mistake and we offer our sincerest apologies to everyone affected. Seagate is aggressively analyzing where process changes are needed and we will implement those changes as quickly as we can."
DeRitis said to Krebs that several thousand former and current employees, anyway the number is less than 10,000.
Security experts and Government agencies are warning about email phishing scams targeting finance and HR personnel that spoof a letter from the organization's CEO requesting all employee W-2 forms.
On March 1st, the Internal Revenue Service issued an alert to payroll and HR professionals about the significant increase in the number of BEC attacks targeting W-2 and other tax related data.
BEC attacks rely on social engineering techniques that try to exploit the trust relationships among employees within the company.
In many cases, attackers spoof the email address of the CEO or CFO, anyway a person with authority, that can influence the employee receiving the message to act according to the instructions provided in the messages. No one wants to tell the boss no.
"The Internal Revenue Service today issued an alert to payroll and human resources professionals to beware of an emerging phishing email scheme that purports to be from company executives and requests personal information on employees." States the IRS's warning.
"The IRS has learned this scheme — part of the surge in phishing emails seen this year — already has claimed several victims as payroll and human resources offices mistakenly email payroll data including Forms W-2 that contain Social Security numbers and other personally identifiable information to cybercriminals posing as company executives!
"This is a new twist on an old scheme using the cover of the tax season and W-2 filings to try tricking people into sharing personal data. Now the criminals are focusing their schemes on company payroll departments," said IRS Commissioner John Koskinen. "If your CEO appears to be emailing you for a list of company employees, check it out before you respond. Everyone has a responsibility to remain diligent about confirming the identity of people requesting personal information about employees."
According to the Salted Hash, the list of victims of the illegal practice in the first months of 2016 is very long and includes the following companies:
March 2016:
- Seagate Technology (March 1)
- Snapchat (March 1)
- Central Concrete Supply Co. Inc. (March 1)
- Main Line Health (March 1)
- Turner Construction Company (March 2)
- Actifio Inc. (March 2)
- Billy Casper Golf (March 3)
- Evening Post Industries (March 3)
- DataXu Inc. (March 3)
- Information Innovators Inc. (March 3)
- York Hospital (March 4)
- Acronis (March 4)
- Moneytree (March 4)
- General Communications Inc. (March 4)
- Advance Auto Parts (March 7)
- Applied Systems Inc. (March 7)
- eClinicalWorks (March 7)
- LAZ Parking (March 9)
- Endologix Inc. (March 9)
- ConvaTec Inc. (March 9)
- Care.com (March 10)
- Foss Manufacturing Company (March 11)
- Mitchell International Inc. (March 11)
- Matrix Service Company (March 11)
- SevOne (March 14)
- PerkinElmer, Inc. (March 15)
- SalientCRGT (March 15)
- Netcracker Technology Corporation (March 17)
- Lanyon Solutions Inc. (March 18)
- Dynamic Aviation (March 18)
- CareCentrix (March 21)
- Lamps Plus and Pacific Coast Lighting (March 23)
- Sprouts Farmers Market (March 23)
February 2016:
- BrightView (February 3)
- Magnolia Health Corporation (February 3)
- Polycom (February 5)
- WorkCare (February 18)
- Mercy Housing (February 19)
- Pharm-Olam International (February 23)
- AmeriPride Services Inc. (February 25)
January 2016:
- Robert Rauschenberg Foundation (January 25)
Since January, the experts also noticed several Tax-related data breaches that affected some organizations at the end of 2015, including TaxAct (January 11), TaxSlayer (January 29), TurboTax (February 10), Lewis, Kisch & Associates, Ltd. (March 7).
"With tax filing season in the United States well underway, scammers who specialize in tax refund fraud have a new trick up their sleeves: Spoofing emails from a target organization's CEO, asking human resources and accounting departments for employee W-2 information." wrote Brian Krebs in the blog post.
The U.S. Federal Trade Commission (FTC) tracked a 47% percent increase in identity theft complaints in 2015, and tax refund frauds represents a significant portion of the complaints.
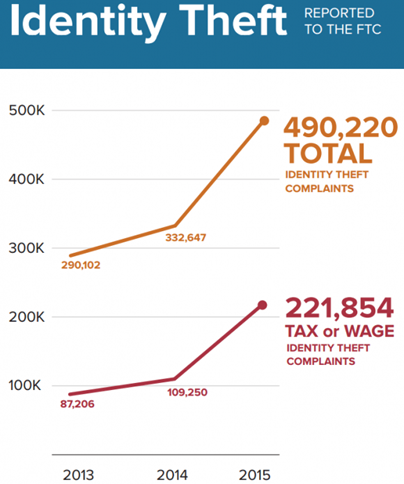
Figure 4 - Identity Theft data (U.S. Federal Trade Commission (FTC))
If you want to avoid being a victim of Tax refund frauds, give a look at the post "Don't Be A Victim of Tax Refund Fraud in '16."
Taxpayers have to be careful; cyber criminals will do everything to steal their money.
References
http://securityaffairs.co/wordpress/45712/cyber-crime/irs-tax-fraud.html
http://securityaffairs.co/wordpress/44732/cyber-crime/irs-surge-tax-related-incidents.html
http://securityaffairs.co/wordpress/45108/cyber-crime/w-2-phishing.html
http://securityaffairs.co/wordpress/45108/cyber-crime/w-2-phishing.html
http://krebsonsecurity.com/2015/03/sign-up-at-irs-gov-before-crooks-do-it-for-you/
http://krebsonsecurity.com/2016/03/seagate-phish-exposes-all-employee-w-2s/
http://krebsonsecurity.com/2016/02/phishers-spoof-ceo-request-w2-forms/#more-33969
https://www.irs.gov/Individuals/Get-Transcript
http://www.ic3.gov/media/2016/160323.aspx
https://www.proofpoint.com/us/threat-insight/post/Gone-Tax-Phishing-Till-April-18th
http://www.proofpoint.com/us/threat-insight/post/Fraud-Feeds-Phishing-in-Tax-themed-Email-Campaign
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.