Pimp my Chrome
You might be wondering about the title. Let me tell that you shall have your answer by the end of this story.
Hacking has been considered as a mysterious act of 0s and 1s that can either make you or destroy you. Along these lines, things have been simplified to a large extent after the growth of Y2K syndrome and web technologies. This is an effort to simplify certain things that can help you in your pen-testing cycle.
The Google Chrome has a lion's share in the worldwide usage statistics by W3Schools. Close to half the world's internet population depends on Google Chrome for browsing the World Wide Web.
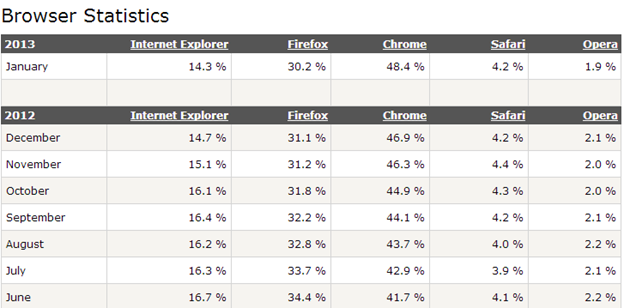
Courtesy- http://www.w3schools.com/browsers/browsers_stats.asp
With over 48% of the world's population depending on this lightning-fast browser, it's time for us to explore various possibilities of navigating the web in a new way. The Chrome Web Store has an amazing collection of browser add-ons which can be used on a regular basis for your pen-testing scenarios, or as a new window of understanding of the web for a novice. The following sections describe how to go about pimping your favorite browser!
1. Web Developer Add-on
A simple, yet very important, extension in your browser can yield a lot of help when performing security tests. A web developer add-on brings along with it various options as shown in the screenshot.
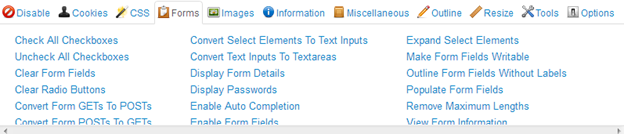
The above screenshot shows only the Form Section of this add on. You can also Disable Javascripts if you feel you need more safety when browsing online. This prevents you from XSS attacks and the likes. The most important thing is the Forms tab. This displays the hidden elements in a web page. This can particularly be used when performing CSRF attacks. If you happen to see hidden token information, and that token is not implemented well, then this information can be used to cause CSRF (Cross Site Request Forgery) attacks.
2. Chrome who is and Ip address and Domain information

Who.is is a fingerprinting protocol that comes in handy when you need to get the domain information about a website. The job is made easier by this plugin. Just visit the site, and click on the icon, and it opens the complete who.is information about a particular website in a new tab. The information you get can range from personal email ids, postal addresses, technical admins and company admins. These details can aid a lot in Social Engineering and makes attacks a lot easier!
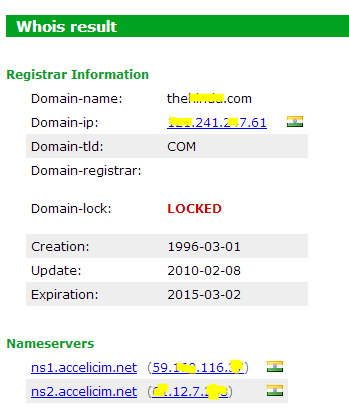
For this particular website it reveals a lot of personal information, so I choose not to present the other details here.
3. Edit this cookie
One of the favorite exploits of all time is injecting scripts that can extract cookie-information and provide us a session access to the victims account. This particular plugin does just that! This facilitates editing cookie values and add new cookies to the browser.
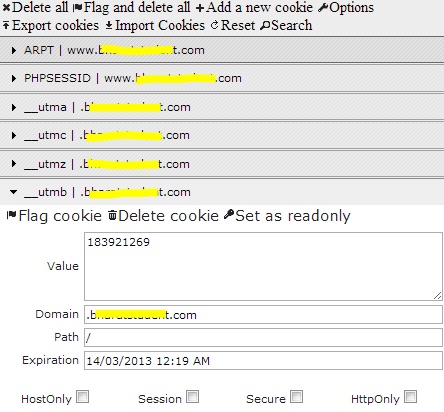
The above-mentioned screenshot is from a site vulnerable to Cross Site Scripting. Here, the user can extract cookie information from the XSS injecting string and use this add on to get logged in as the victim and use his session live!
4. Port Scanner for all hosts
Many a times we browse websites and would like to get a little naughty. Instead of firing nmap for a basic test on all the port that are open, this add on just does the task of simple port scanning and generate a compact report about various services that are open and their respective port numbers. Just click the icon in your chrome browser to get the following output.
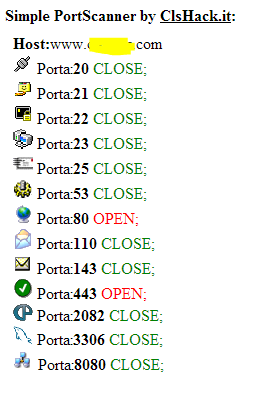
Port scanning comes handy when you need to perform a vulnerability/Risk assessment of a corporate network. Surely, nmap scan is always preferred over a browser plugin. But, for getting started with a quick round of pen-test, what can get better than this?
5. HTTP Headers
Http headers are a great value to a dedicated attacker when it comes to automating the attacks. The header information by itself isn't very harmful, but it surely gives the attacker the information about the web server configuration like OS, server and other important details. This plugin makes this information readily available to you by just adding this to your browser.
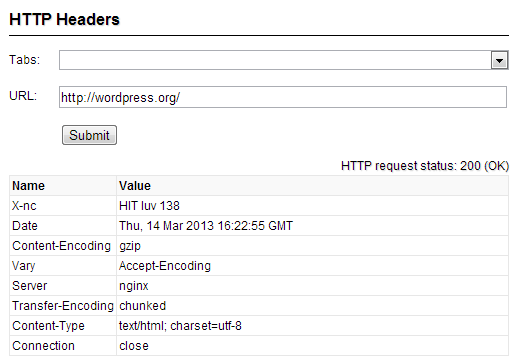
One of the most basic information can be got here, that Wordpress is using nginx server. This particular information is critical, as most of us are aware that nginx had a severe Denial of Service Vulnerability in the past. So, the major intention here is that there are certain server configurations which allow automated attacks to yield. As an administrator it's wise to prevent as much information disclosure as possible to safeguard oneself from attacks. Some other types of headers like X-content-type can lead to potential Cross Site Scripting attacks, if they are set to no sniff option. Similarly X-Frame header lets the web page decide whether or not any content within iframe tags needs to be rendered. A poorly configured web server with no X frame validation leads to click jacking attacks.
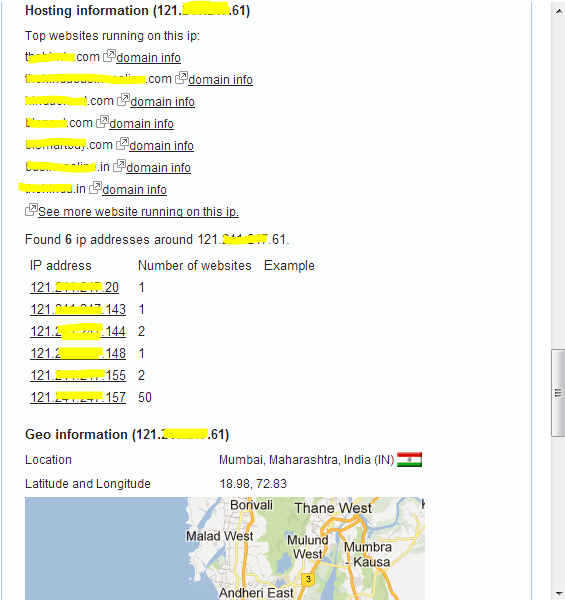
6. IP address and domain Information
I must say this is aquick and dirty tool – one stop shop for the quick information gathering about any web server. Let's check what information can be got from this fabulous add-on.
Network Information: In this category, the add on provides all the details like reverse DNS, IP range, subnet, ISP name and even address.
SPAM database Lookup: Here, various SPAM databases are probed to see if this web site is involved in spamming. And it provided us with Listed/Not Listed result.
Block List: Look up and Whoisinformation: As shown earlier, this tool also provided Whoisinformation, but along with Whoisinformation, this tool also provides added functionalities.
Hosting Information: The add-on also lists the top websites that are hosted on this particular IP address, and tells number of websites running under each IP addresses.
Geo Location Information: The best part about this is that it provided the latitude and longitude co-ordinates of most closely proximate area around the web server.
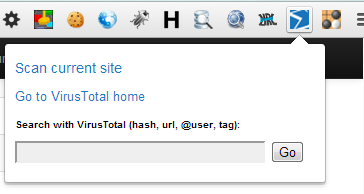
7. VT Chromizer
This is an add-on to your browser that lets you browse virus free. With over 35 scan engines, you can be sure to get a confirmed result about the status of the site you are browsing. Download the plugin from the Google's Chrome store, and just choose the scan current site option. The add-on also provides facility to check for URLs, hashes etc. and compare it with its database. This plugin can be considered as one of the most useful plugins when you encounter a suspicious file.
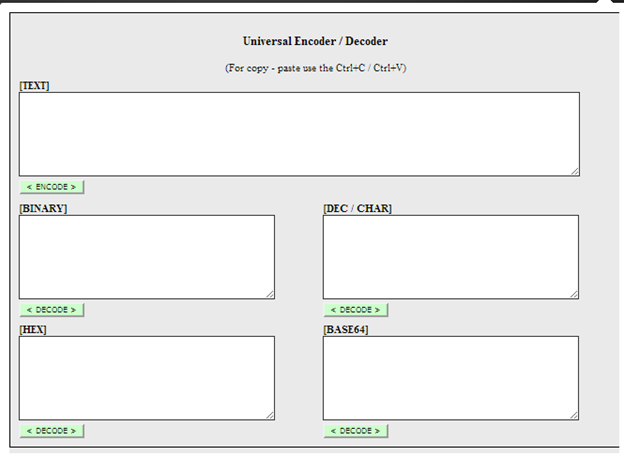
8. Universal Encoder-Decoder:
When performing web application security testing, we need to test for various vulnerabilities like Cross Site Scripting, Cross Site request forgery attacks, and other OWASP top 10 bugs. The developers are sharp to add filters to evade these special strings from playing dirty with the victim. This add-on helps an attacker (web security tester here) to try to evade filters and help the developers secure the design and architecture of the application.
The most important use of this tool comes when playing Capture the Flag events. The Cryptography rounds can be sometimes as simple as binary/hex/base64 mixture used intelligently to confuse the player. This tool supports all the above formats for your perusal.
9. Firebug lite
Firebug Lite is the chrome version of Firebug for Firefox. This add-on is a very helpful tool for developers as well as security enthusiasts. For the security researchers, this add-on helps detect persistent javascripts within the HTML source code injected by the attackers. For the developers, it helps understand the CSS, DOM based functionalities right from the source. This will eventually lead to improved architecture of the overall web application.
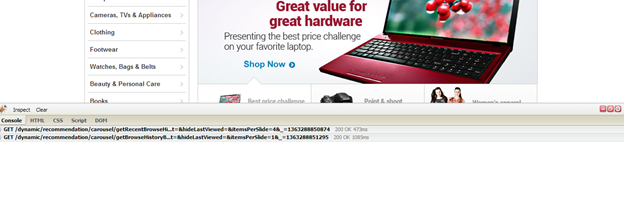
As you can see, the upper middle is the web page and the lower middle is the firebug window.

FREE role-guided training plans
In this article, we have seen some of the important add-ons to Google Chrome that can enhance your web experience and also help you stay secure online. As said, Google Chrome has emerged as the most-used web browser according to the survey shown in the beginning of this story. For Firefox users, we have a browser called Mantra that is designed keeping security geeks in mind. It is wonderful with a huge collection of browser plugins and add-ons to perform web application security testing.





