Incident Response and Forensic Martial Arts with Helix
Helix3 is a live CD for doing computer forensic investigation and incident response. It is built on top of Ubuntu and comes in both free and commercial forms. This article will cover working with the free Helix Live CD. You can download the live CD from: https://www.e-fense.com/store/index.php?_a=viewProd&productId=11
I am currently using Helix 2009R1 for the demonstration.
Learn Digital Forensics
Here is the list of tools that we will be covering as a part of our forensic investigation and incident response:
- Adepto
- GtkHash
- Xfprot
- Retriever
- VirusScanner
Adepto
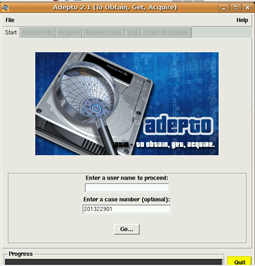
One of the first steps when we do an incident response is to secure the hard disks/storage to bring it back to the lab for investigation. We never do our investigation on the original copy, so it is advisable to make a bit-by-bit copy of the image that has to be analyzed. So now suppose we do not have hardware imagers: We can use Helix to make a bit-by-bit copy of the hard disk. The tool we will use is Adepto.
We simply boot the Helix Live ISO and open Adepto.
So right now I am trying to clone a USB with another USB to use for my forensic investigation.
Here is all the information about the USB that I am trying to copy:

Now let us move on to Acquire to mention the source and destination along with the hash verification we wish to use and then press Start.

We now check on the logs to see the acquire process. This shows us that the hash verification of the image was successful with our device.
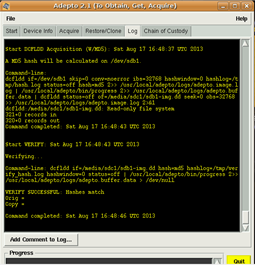
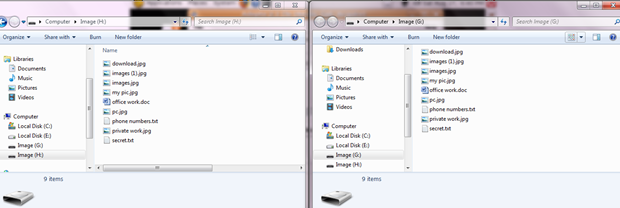
Now let us clone our device with our new USB drive for our forensic investigation. Just put in the source and the destination devices and press Clone.

It takes some time for the disks to be cloned and then we can check both the devices. You can see that the device has been cloned and we have an exact image to work on during our forensic investigation.
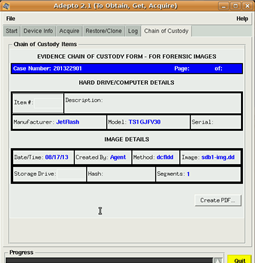
We also have the option to create a chain of custody for the case of events which happened during the cloning and to have a PDF report as well.
Autopsy
We already covered the use of Autopsy in detail in the SANS SIFT article here.
GtkHash
GtkHash is a GUI tool for calculating MD5 and SHA1 hashes for the purpose of integrity checking.

Xfprot
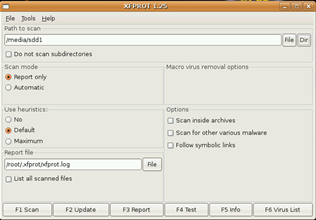
For help during investigations for virus/rootkit detection, we may make use of Xfprot. So let us set the destination and start our scan:
Our scan is completed and there were no infected files in here, as you can see in the report:
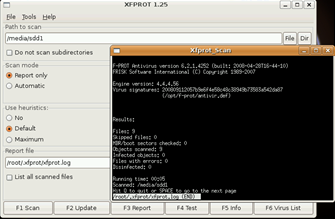
You may update the antivirus before running the scan by pressing Update. Hence this is an easy way of detecting viruses/malwares in our forensic image.
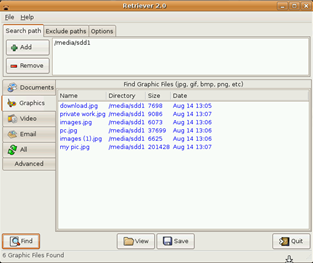
Retriever 2.0
This is a small, simple tool to categorize and search for data such as images, documents, and videos separately and then to forensically investigate each of them. It is pretty simple to use. I would suggest using this tool if you wish to do a general investigation with a free tool.
So I simply load by image in the Retriever tool and press on Find. It found one document in the documents section.
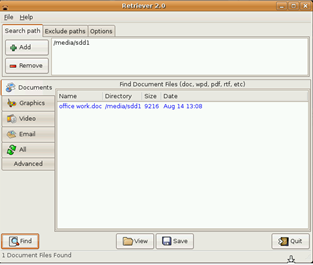
Let us find some graphics. We press Find:
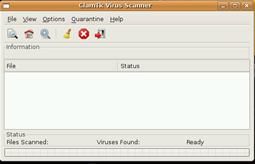
ClamTk Virus Scanner
We also have a ClamTk virus scanner for checking for viruses and malwares on the forensic image.
There are a few other tools in Helix Live CD that are not as effective if we compare the time we spend on doing the actual investigation through them, compared to the other more effective tools.
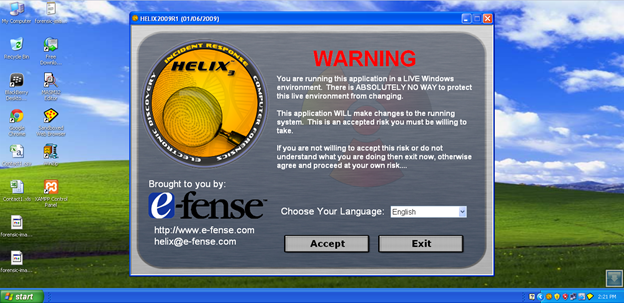
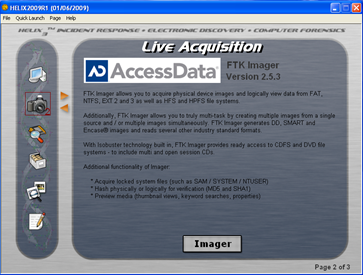
Now let us move to the Windows Toolkit of Helix. For this, simply boot your Windows and put in the ISO. Below you can see the interface of Helix for Windows. Also it is strictly suggested not to use the Helix Windows version on the actual system you are investigating (during forensic investigation), since it will make changes to the integrity of the system. Hence it is advised to work on the copy of the forensic evidence.
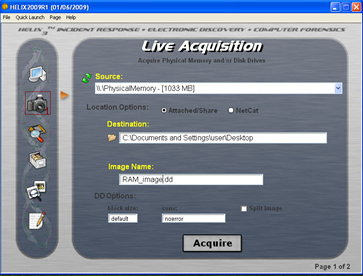
Live Acquisition
This tool may be used to take a live memory dump or to acquire the physical hard drive of the systems for imaging. We can later use tools such as Volatility
https://resources.infosecinstitute.com/memory-forensics-and-analysis-using-volatility/
for doing the advanced memory forensics on the captured memory.
FTK Imager
We also have the famous FTK Imager bundled up with Helix for our investigations.
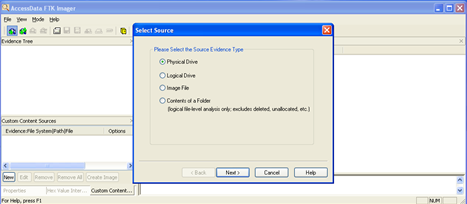
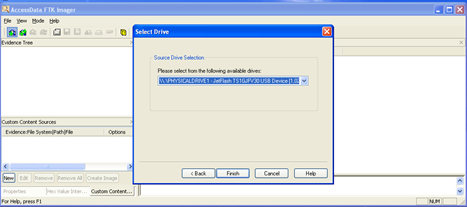
Using this is pretty simple. We add the evidence to be investigated and to be imaged as shown below. Here we have a physical USB drive attached to our system, which is a copy of the forensic evidence.
We added the evidence item successfully to the FTK Imager and now you can see the items contained within the evidence in a tree view. Also notice that the crossed file (new file), which is the deleted file from the USB, can also be seen here. FTK Imager also gives us a view of the file contents below.
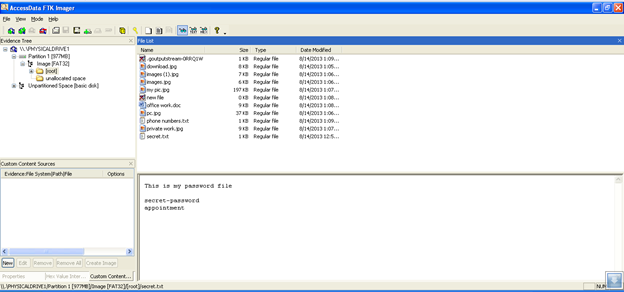
This is an extremely simple tool to use from the point view of forensic analysis and definitely an effective one. We have a hex editor as well and can view the files in hex for small traces of programs/chats/executables.
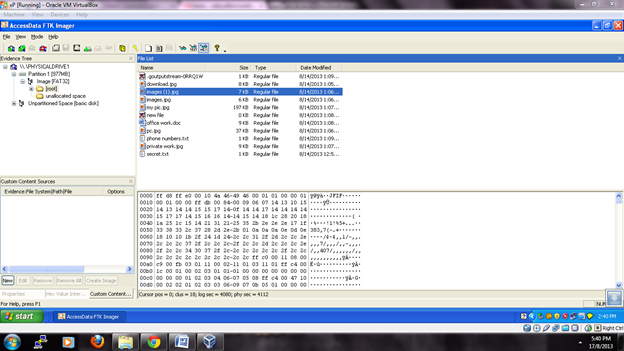
We can even create a disk image, capture RAM, and do a lot of things with the FTK Imager. It also has the option to export images and keep them for further reference.
Next we move on to the Browse Contents feature of Helix. We can browse the whole system and any suspected items during an incident response using this tool as well as get minor details about them.
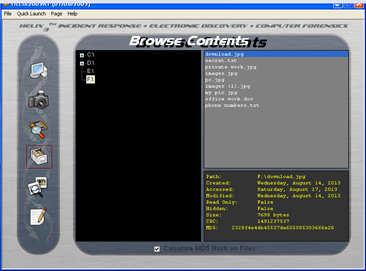
We also have a scan pictures tool which allows us to scan images/graphics during an incident response.

Helix also has a way to manage your notes during the investigation, using the Notes tool that allows you to bookmark important points during an investigation.
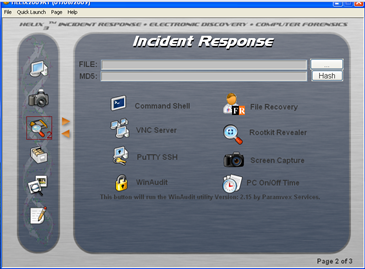
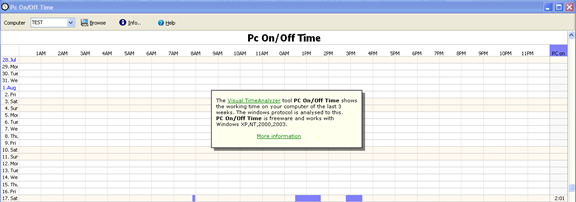
We have some small but very important tools as well to manage our investigation needs, including a command shell, file recovery tools, VNC server for remote access to the system, Rootkit Reveler, Putty for SSH access, screen capture, WinAudit, PC On/Off Time
File Recovery
The file recovery tool helps us to recover files that might have been deleted by the suspect for malicious purposes.
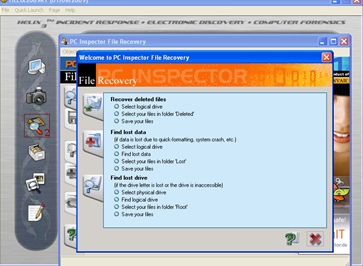
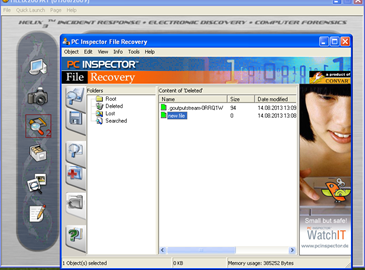
Let us select a suspect drive for finding deleted files. We can see that it has detected two files that have been deleted. This tool also has a cool feature for doing a cluster-based range search to find deleted items.
It has a cool utility to give the computer timeline of system activity. This may help us to gather traces of information about the computer activity.
There is another list of small tools, mainly for incident response, as shown in the figure below:
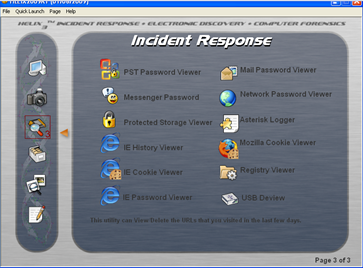
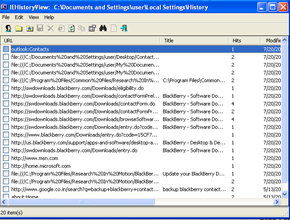
Now this helps an investigator to easily get a lot of information, such as IE history, cookies, and saved passwords.
This will also be helpful for you if the suspect system has a messenger installed. There is a general tendency to save passwords with the messenger only. The messenger password viewer helps to find these out for further investigation of chats of the suspect.
References
http://www.forensicswiki.org/wiki/Helix3
Learn Digital Forensics
https://www.e-fense.com/store/index.php?_a=viewProd&productId=11




