How Edward Snowden protected information … and his life
Who is Edward Snowden?
Edward Snowden is the man who changed the history of the Internet; he revealed information on the largest and most secret surveillance program implemented by the U.S. Government.
Snowden is a 29-year-old technical assistant for the Central Intelligence Agency who has worked at the National Security Agency for the last four years. He has also worked for various defense contractors; his last job was with Booz Allen Hamilton.

What should you learn next?
Edward Snowden decided to reveal his identity, according to The Guardian, exposing his person to serious risks, the U.S. government was seriously embarrassed by the revelation of the man that confirmed that surveillance activities involved also other governments such as the British one.
Snowden's declarations to The Guardian and the Washington Post have shocked American public opinion. The country was divided between supporters and opponents, U.S. citizens found themselves asking questions about issues of security and privacy and wondering what was the right compromise between the two requirements. The U.S. government is defending the surveillance program; it is considered by authorities a necessary activity of intelligence to prevent other terrorist plots and Obama's administration confirmed that the debated data collection has already prevented terrorist acts.
During an interview with The Guardian, Snowden revealed that he is concerned about being persecuted by the U.S. government, and his concerns are legitimate, considering other cases like Bradley Edward Manning, the U.S. Army soldier who was arrested in May 2010 in Iraq on suspicion of having passed classified material to the website WikiLeaks. Edward Snowden fears that the government will persecute him for disclosing top secret documentation on an extensive surveillance program known as PRISM.
Snowden escaped from the U.S. by going to Hong Kong. He went to the Chinese territory because he believes it is independent and has "a strong tradition of free speech."
"I've left the room maybe a total of three times during my entire stay," he said.
The disclosure started with the publication of the secret court order to Verizon Communications, but that was just the tip of the iceberg; all the principal U.S. IT companies are supporting the surveillance program PRISM. The surveillance architecture monitors every activity on the Internet and accesses data from companies such as Microsoft, Google, Facebook, and Apple.
Today, Snowden is blocked in the transit area of Moscow's Sheremetyevo International Airport, although journalists have been unable to spot him.

Figure 1 - Moscow's Sheremetyevo International Airport
In the area are located three terminals and it includes both the V-Express Capsule Hotel and one wing of the Novotel, as well as the detention rooms reserved for refugees and others with uncertain immigration status who wait to be admitted to the country or shipped back to their place of departure.
Figure 2 - Edward Snowden Interview
The awareness of being a moving target
Snowden knows very well the world of intelligence and the way the secret services of his country operate; that's why he decided to go to the daylight and to attract all this hype around him, it is necessary for his survival. Snowden considered the decision to make public news on the PRISM surveillance program for a long time and he has certainly adopted all necessary countermeasures to hide his network of contacts, disseminating false information on his intentions and storing in a secure place the information gathered that represents his life insurance.
The belief that Snowden decided to reveal details of his past activities in the intelligence sector led the security community to commit some serious errors. He probably received great support from hacktivist movements that sustained him in difficult moments. Don't forget that the young technician was aware of the consequences of his decision.
Why has nobody spoken before now of possible accomplices outside of U.S. intelligence? And what if his accomplices are personnel of U.S. intelligence? It's my opinion that Snowden has received support to organize the disclosure of the information and its storage in a secure place.
During the interview with The Guardian, Snowden admitted that he has a clear idea of his future and the way his life was changing.
"I could be rendered by the CIA, I could have people come after me." "We've got a CIA station just up the road in the consulate here in Hong Kong, and I'm sure," "that they're going to be very busy for the next week, and that's a fear I'll live under for the rest of my life."
But Snowden is considered a mine of information, especially for foreign intelligence. He knows the secret systems and the name of actors involved in surveillance program; the access to this information represents a serious menace to homeland security. The man had access to an impressive amount of secret data and confidential documents and nobody has a real idea of which information he kept for himself.
For information about how to secure your data, check out our CCNA training, Ethical Hacking training and CISSP training courses.
The access to the same information from a foreign government could have serious repercussions. That's why it is certain that Snowden has adopted the necessary measures to prevent uncontrolled data disclosure.
Snowden still remains at a Moscow airport, thanks temporary asylum from the Russian government that later invited him to leave the country, denying political asylum to avoid interference with the relationship with the U.S. government. Snowden's Russian lawyer, Anatoly Kucherena, confirmed the intention of the man to leave the Russia, but the news is not reassuring for U.S. authorities, who fear the possibility that he could exchange information to receive help in avoiding arrest and capture.
The Guardian published a collection of emails between former New Hampshire Sen. Gordon Humphrey and Snowden, in which the technician remarked that that it's impossible for information in his possession to be obtained by hostile governments.
Former two-term GOP Senator Gordon Humphrey of New Hampshire emailed Edward Snowden
yesterday [emphasis added]:
Mr. Snowden,
Provided you have not leaked information that would put in harm's way any intelligence agent, I believe you have done the right thing in exposing what I regard as massive violation of the United States Constitution.
Having served in the United States Senate for twelve years as a member of the Foreign Relations Committee, the Armed Services Committee and the Judiciary Committee, I think I have a good grounding to reach my conclusion.
I wish you well in your efforts to secure asylum and encourage you to persevere.
Kindly acknowledge this message, so that I will know it reached you.
Regards,
Gordon J. Humphrey
Accordingly, Mr. Greenwald sent this to the whistleblower, thanking him for exposing the astonishing surveillance program and at the same time preserving the information that would disclose the details of the PRISM program. Following is Snowden's reply:
Mr. Humphrey,
Thank you for your words of support. I only wish more of our lawmakers shared your principles - the actions I've taken would not have been necessary.
The media has distorted my actions and intentions to distract from the substance of Constitutional violations and instead focus on personalities. It seems they believe every modern narrative requires a bad guy. Perhaps it does. Perhaps, in such times, loving one's country means being hated by its government.
If history proves that be so, I will not shy from that hatred. I will not hesitate to wear those charges of villainy for the rest of my life as a civic duty, allowing those governing few who dared not do so themselves to use me as an excuse to right these wrongs.
My intention, which I outlined when this began, is to inform the public as to that which is done in their name and that which is done against them. I remain committed to that. Though reporters and officials may never believe it, I have not provided any information that would harm our people - agent or not - and I have no intention to do so.
Further, no intelligence service - not even our own - has the capacity to compromise the secrets I continue to protect. While it has not been reported in the media, one of my specializations was to teach our people at DIA how to keep such information from being compromised even in the highest threat counter-intelligence environments (i.e. China).
You may rest easy knowing I cannot be coerced into revealing that information, even under torture.
With my thanks for your service to the nation we both love,
Edward Snowden
A passage in the above email highlights the impossibility of accessing Snowden's information without his consent; presumably he has encrypted it, limiting access only to a restricted number of individuals in possession of the encryption keys. This is a possibility, and I have explicitly used the plural because I am convinced that the keys have been shared in very difficult times by Snowden with someone who is assigned the task of disseminating information in case of accidents and adverse events that could affect the young technician.
In a single-step encryption the key used to encrypt document represents the "single point of failure" of the system; obtaining it, the entire information could be revealed, so the principal problem for Snowden was to distribute the responsibility of data maintenance among many individuals.
It is likely Snowden, or anyone who has helped him, has thought of an onion encryption scheme. In every layer could be stored encrypted information and a reference to the owner of the encryption key for those levels.
To avoid that, the encryption chain could be blocked by the absence of one of participants; the information could be encrypted separately by two individuals, in this way in the same level there will be always two copies of the same data enciphered with public keys of two individuals. Both individuals could decrypt the documents with their private keys. The encrypted data in reality are also another couple of enciphered containers.
This is just an idea and possible variants are theoretically infinite.
Figure 3 - Onion Encryption scheme
A similar schema could be efficient only if many accomplices are involved in the conservation and eventual disclosure of data, but it could be too complex to realize for obvious reasons.
Another element to consider is how the files could be spread in the event that Snowden is killed. A totally automated process for the disclosure of information is a possibility, but it is more likely that other people are involved to start the process.
"If something does happen to [Snowden] all the information will be revealed and it could be [the U.S. government's] worst nightmare."
According some intelligence experts, the U.S. technician hid the classified documents before fleeing Hong Kong for safety reasons; the news was also reported by the Sunday Times, which cited an informed source.
According to the popular paper, Snowden left behind at least four laptops containing secret intelligence reports when he set off for the Hong Kong airport. It also remarked that copies of encrypted files could be stored in his safety deposit box.
Glenn Greenwald, The Guardian journalist Snowden first contacted in February, revealed that Edward Snowden "has taken all necessary precautions to distribute the precious documents to individuals all around the world, with the purpose that the archives will inevitably be published in case of incidents."
According to Greenwald, people in possession of these files "cannot access them yet because they are highly encrypted and they do not have the passwords." This confirms the use of an encryption system. Greenwald also added, "If anything happens at all to Edward Snowden, he told me he has arranged for them to get access to the full archives." Greenwald confirmed that Snowden has no intention to reveal technical information, specifications or blueprints to other states.
Assuming that Snowden has used a single password to encrypt the secret documents the question is: "How would he arrange to send it to unlock encrypted files if he is operating alone?"
In this case there is a concrete suspicion that that man received the support of at least another individual. Another possibility is the deployment of an automated process that, for example, periodically checks whether a condition is satisfied that will make it necessary to send the key to a list of people who are in possession of the archives.
Deep web or cloud computing?
Where has Snowden hidden the secret archives?
Another fascinating hypothesis is that the young whistleblower has provided to a restricted number of individuals key findings for stolen information and instructions on how to access to the overall amount of leaked data.
At this point it is crucial to understand where is possible to hide information on the Internet away from prying eyes. The Deep Web is one of most secure place where Snowden could have hidden the confidential documents. The Deep Web (or Invisible Web) is the set of information resources on the World Wide Web not reported by normal search engines.
According to several researchers, the principal search engines index only a small portion of the overall web content; the remaining part is unknown to the majority of web users, and it is exactly the obscurest part of the web that intelligence uses to hide secret information and services.
The U.S. Naval Research Laboratory promoted the Tor project. "Tor" is the acronym of "The onion router," a system implemented to enable online anonymity. Tor client software routes Internet traffic through a worldwide volunteer network of servers hiding users' information, eluding any monitoring.
Snowden is aware of the potential of the project and it is possible that alone, or with the help of other whistleblowers, he has created a hidden service for the provisioning of the secret information.
According to security experts, Edward Snowden used the Tor network to send information about the surveillance program PRISM to both the Washington Post and The Guardian in June 2013.
Without complicating our lives, it is possible to create a server on which files can be stored in encrypted format. The authentication could be implemented in various ways, depending on the level of security desired; for example, it is possible to allow access to the user only if he is in possession of a digital certificate on his machine. The files could all be encrypted and the certificate could be also used as a container to hold the keys to decrypt the information.
If the clear web seems to have no more secret for intelligence agencies, the Deep Web is totally different from.
The NSA is building a Utah data-mining facility to monitor overall communications traffic; according to security experts, the Utah data center's purpose is also to penetrate and gather the data hidden in the "deep web," normally not available for public browsing.
"... The data stored in Bluffdale will naturally go far beyond the world's billions of public web pages. The NSA is more interested in the so-called invisible web, also known as the deep web or deepnet—data beyond the reach of the public. This includes password-protected data, U.S. and foreign government communications, and noncommercial file-sharing between trusted peers. 'The deep web contains government reports, databases, and other sources of information of high value to DOD and the intelligence community,' according to a 2010 Defense Science Board report. 'Alternative tools are needed to find and index data in the deep web … Stealing the classified secrets of a potential adversary is where the [intelligence] community is most comfortable.' With its new Utah Data Center, the NSA will at last have the technical capability to store, and rummage through, all those stolen secrets. The question, of course, is how the agency defines who is, and who is not, 'a potential adversary.'"
The Tor network isn't the unique opportunity for a whistleblower like Snowden; I2P could represent a valid alternative According to the official definition, "I2P is a scalable, self organizing, resilient packet switched anonymous network layer, upon which any number of different anonymity or security conscious applications can operate."
In an I2P network the "hidden" component is represented by an application executed by the node, and of course the path followed by the information to reach the destination.
Have you ever read about eepSites?
An eepSite is a website that is hosted and anonymously accessible through a proper setting of web browser HTTP proxy to use the I2P proxy (typically it listens on localhost port 4444) for browsing the site.
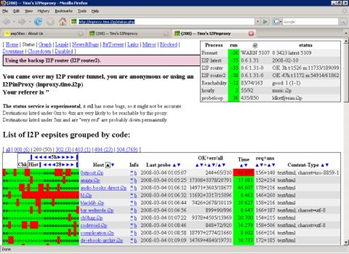
Figure 4 - eepsite installation procedure
Installing an eepsite application on a server, it is possible to emulate the behavior of an ordinary web server, with the primary difference that a site on I2Ps Darknet is hidden from prying eyes because nobody has any idea of where the server runs.
The last hypothesis, in my humble opinion less likely, is that Snowden has hidden his file somewhere in the cloud. In this case, the question is: Which cloud has Snowden used?
The young technician is aware that practically every cloud service, such as Dropbox, Microsoft's SkyDrive, or Box.net, hosted within the United States, even if it has European or non-U.S. data centers, is under complete control of his government. The unique alternative is represented by a private cloud infrastructure, but the effort and the cost to distribute and maintain these architectures can simply not be sustained by a limited number of persons. We must consider that, just after Snowden's revelation, U.S. secret services have unleashed a veritable manhunt analyzing, as far as possible, any previous relationship and movement of the young man.
Probably the setup of these types of infrastructures would have left some traces in the network that would not escape to the U.S. intelligence.
Conclusion
This post has the unique intention to introduce a couple of the infinite possibilities that a man who has worked for the intelligence for several years has to hide secret documents. Probably he used a complex service in the hidden web or perhaps he has hidden the precious data in a sever hosted in an unknown server farm; what is important is that the man has guaranteed his survival in this way... Snowden never dies since his data remain secret, when they become public it will be too late.
Let us hope that the information does not fall into the wrong hands!
References
http://www.guardian.co.uk/commentisfree/2013/jul/16/gordon-humphrey-email-edward-snowden
http://www.foreignpolicy.com/articles/2013/07/18/what_if_snowdens_laptops_hold_no_secrets?page=0,1
http://english.ruvr.ru/news/2013_06_30/Snowden-hid-NSA-files-in-Hong-Kong-for-safety-media-5535/
http://www.popsci.com/technology/article/2013-06/hey-edward-snowden-how-was-your-weekend
http://www.eepsite.com/Content/HowTo/Setup_I2P_Win.htm

FREE role-guided training plans
https://resources.infosecinstitute.com/anonymizing-networks-tor-vs-i2p/





