Expected Ransomware Evolution in Coming Years
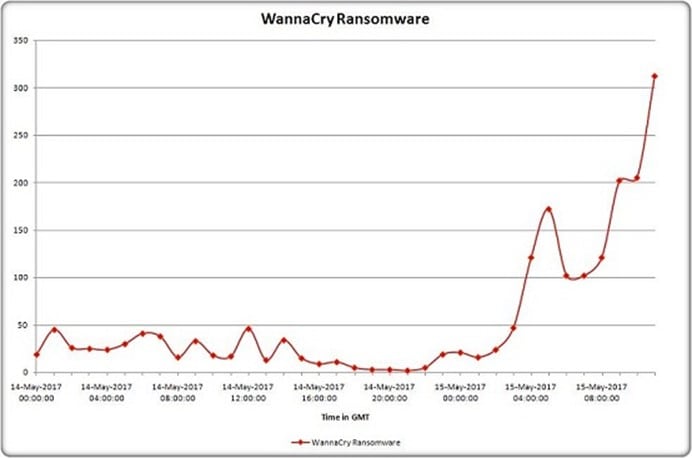
The tech world has been stricken with digital assaults this year and ransomware has been at the focal point of everything. So far, this year we have seen two record-softening attacks occur up to a matter of months. In May the WannaCry ransomware contaminated a huge number of PCs, disturbing doctor's facilities, banks, and organizations. At that point in late June, we had another attack, this time malware which was named NotPetya, this adaptation of ransomware caused pandemonium crosswise over Ukraine, Russia, and numerous different nations.
So, basically what is Ransomware? Ransomware is a noxious program that resembles a PC infection. It's intended to filter your hard drives and encode the greatest number of documents as it can, this leaves the client unfit to open their critical records and information. The records are in fact still there, and you need to pay a total (the payoff) to open and access your unique documents.

FREE role-guided training plans
Ransomware was the most impending danger of 2016, demonstrated FBI reports. Overall, 4,000 ransomware assaults happened every day in 2016, as per a report from the FBI in June 2016. What's more, the reason it's so predominant is that it works.
A current IBM X-Force thinks about demonstrates that 70% of organizations tainted with ransomware paid to access their information. A similar source expresses that one of every two business administrators overviewed has encountered ransomware attacks in the working environment. One out of two administrators say they paid over $10,000 to recover their information, and 20 percent paid over $40,000. With ransomware being so productive, there is no uncertainty it will keep on being a danger in 2017, demonstrates a report from security firm MalwareBytes.
This issue doesn't appear to be backing off at any point in the near future and innovation is just propelling each day. Ransomware models are altering and creating in the wander economy, shows late reports. New strains are flying up unendingly, and they are winding up more advantage masterminded. As more business people pay the installment instead of losing access to their data, the industry is modifying and discovering better ways to deal with money extortion.
What Businesses are Being Targeted?
The IBM examine likewise demonstrated how ransomware cybercriminals are beginning to go for the big fish. Just 29% of private ventures overviewed have involvement with ransomware attacks, contrasted with 57% of medium size organizations. As indicated by IBM, end users will likewise fork up Bitcoin to recover their information, however not as much as organizations. 50% of end users said they paid cash when hit with ransomware. This isn't to imply that end users are not a target – but it looks like cybercriminals are becoming savvier regarding marketing.
Evolution of Ransomware for Maximizing Profits:
New ransomware strains are developing by the thousands every day. There are many to the point that itis difficult for security specialists to stay aware of removal techniques. Ransomware models are additionally adjusting to the market and ending up more pay situated.
- Ransomware that includes the threat of information disclosure:
This development is likely because ransomware attacks against U.S. associations have hit a noteworthy obstacle — excessively few U.S. organizations are paying the payment.
Witnessing their achievement in different markets (both among buyers and in whatever is left of the world), there clearly exists more available market if the danger can be extended past information encryption and destruction. This implies finding an approach that is not addressed by countermeasures that organizations accept ensure their information: reliable data backup.
- Focusing More on Quantity than Huge Payoff:
Most ransomware battles have been engaged at endeavoring to degenerate expansive amounts of individual systems, led similarly as a mass email showcasing impact; Send out a massive blast of phishing messages with ransomware payloads and expect that while the larger part will flop, there will be a modest bunch of ready victims per campaign. Pile up on a sufficiently substantial number of endeavors and that little level of fruitful attacks begins to add up to real money.
The objective of these mass battles is to settle on the choice to pay however much of an easy decision as possible to as many victims as conceivable. Keeping the payment low, by and large fluctuating amongst $300 and $700 per attack, has generally made it a sensible alternative to dodging a lot of work or downtime.
- File-less Ransomware:
The most widely recognized ransomware delivery procedure is phishing messages with malicious attachments, as it has been for the most recent few years. Infected Microsoft Office reports that use macros keep on being a prominent decision, as do JavaScript attachments, which are regularly camouflaged as other attachment types.
These procedures have been prevalent to the point that even humbly experienced security groups are finding a way to keep their AV refreshed, filter out malicious file attachments, and manage blending of open and private email accounts on association resources. Cybercriminals are likewise mindful of these preventative measures, and we see modern systems for ransomware delivery that bypass recognition because of file-less ways to deal with the virus.
For instance: We recently witnessed another variation of Kovter, a malware family known for click-fraud and ransomware that uses JavaScript and PowerShell to insert its executable components into areas inside the Windows registry. This enables it to gain persistence and maintain a strategic distance from file-scanning antivirus and antimalware software because there is no record to filter.
The eventual fate of Ransomware:
Besides focusing on bigger organizations for more cash, ransomware will likewise get more complex, demonstrates a report by Fortinet. The report gathers a number of security threats and patterns for 2017 and shows that assaults will scale exponentially in 2017. Furthermore, the best approach to do that, of course, is automation.
"Automated attacks introduce an economy of scale to ransomware that will allow hackers to cost-effectively extort small amounts of money from large numbers of victims simultaneously, especially by targeting online IoT devices," shows the report.
Ransomware will likewise adjust to showcase patterns and begin to target cloud innovation and Internet of Things devices, demonstrate security specialists from McAfee. More IT masters begin trusting their data to the cloud and introducing IoT devices in a business setting.
All reports demonstrate that ransomware advancement will make it a considerably greater danger than the prior year. In this condition, managed service providers remain the fundamental warriors on the bleeding edge of the ransomware wars. The best way to crush the scourge is to be outfitted with a fail-safe backup system that will permit quick restoration and access to critical information. So don't be the next ransomware victim – keep a backup (or two, or three, ideally off-site). Nobody is too little to be a target.





