Dangerous DDoS (Distributed Denial of Service) on the rise
Introduction
Contrary to what you might believe, DDoS (Distributed Denial of Service) attacks are considerable, a serious cyber threat able interrupt a web service provided by an organization causing serious consequences. The methods of attacks could be adopted for various purposes by different entities, for example a group of cyber-criminals could conduct a similar attack for extortion, or a group of hackers could use a similar approach to express social dissent.
The article proposes an overview of principal DDoS techniques implemented by attackers in various contexts analyzing real case studies. The article will propose statistics and technical data related to news events concluding with a look at possible technological evolution of techniques.

What should you learn next?
DDoS attacks are of course cybercrime . Individuals voluntarily take part in the offensives that constitute violations of the laws of individual countries. The problem is that despite a global acceptance of the crime the different legislation and territorial jurisdictions leave these actions unpunished.
Inside a DDoS attack
DDoS attacks are conducted with the primary intent of targeting a network resource. A typical scheme of attack involves a large number of compromised machines that target the same objective causing the interruption or suspension of web services it provides. The attackers try to obtain saturation of the resources available to the targets that are flooded by legitimated traffic that they are not able to process. If the attack succeeds, it consumes the resources of the target, usually causing the slowdown in services provided or even its complete blockage.
It must be clear that Denial-of-Service attacks are considered violations of the Internet Architecture Board's Internet proper use policy, an ethic manifesto for Internet use. The IAB is the committee charged with oversight of the technical and engineering development of the Internet by the Internet Society (ISOC).
Classification of DDoS
As described the term DDoS describe a distributed cyber-attack that attempts to make web resources and/or services it provides unavailable to users. The term is very generic because various types of Distributed Denial of Service exist that could be grouped in three main categories:
- Protocol Attacks –The attacker's goal is to saturate server resources of the targets or those of intermediate communication equipment (e.g. Firewalls, load balancers). The attack exploits network protocol abusing the victim's resources destined to its implementation. The category includes SYN floods, fragmented packet attacks, Ping of Death, Smurf DDoS and more.
- Volume Based Attacks –The attacker's goal is to saturate the bandwidth of the target. The category includes ICMP floods, UDP floods and other spoofed-packet floods.
- Application Layer Attacks – The attacker's goal is to affect target applications. Usually these attacks target HTTP trying to exhaust the resource limits of Web services. Application Layer Attacks target specific Web applications making requests that tie up resources deep inside the affected network. This type of attack is insidious because is hard to detect. They don't involve large volumes of traffic and require fewer network connections with respect to other types of DDoS. The category includes Slowloris, Zero-day DDoS attacks, DDoS attacks that target Apache, Windows, or OpenBSD vulnerabilities and more.
Once the categories are defined, it is necessary to introduce the metrics used to compare the strength of the attacks. The Protocol Attacks magnitude is measured in Packets per second. Volume Based Attacks magnitude are measured in bits per second (Bps). Meanwhile, for Application Layer Attacks, the magnitude is measured in Requests per second.
The attack
To understand the DDoS attacks better, they are analyzed individually by most popular type of attack according to the classifications proposed.
Protocol Attacks
The most popular types of attacks belonging to the Protocol category are the SYN floods, fragmented packet attacks, Ping of Death, and Smurf DDoS. Let's look at a short description for each method.
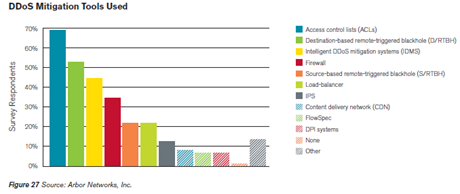
SYN Flood – A SYN flood DDoS attack is one of most popular types; it exploits a flaw in the TCP "three-way handshake" connection sequence:
The attacker floods the target with SYN requests in an attempt to consume enough server resources to make the system unresponsive to legitimate traffic. It can either not send the expected ACK, or by spoofing the source IP address in the SYN, causing the server to send the SYN-ACK to a spoofed IP address that will not reply with an ACK because it hasn't started the handshake with SYNC.
The server will wait for the ACK for a specific time. Of course large numbers of half-open connections will saturate resources on the server resulting in a denial of service to legitimate traffic.
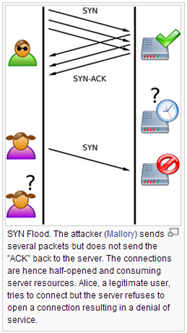
Figure 1 - SYN Flood DDOS Attack
Ping of Death – The attacker sends a malformed or specifically crafted ping to the victim. Normally a ping is 32 bytes, and many systems could not handle a ping packet size larger than the maximum IPv4 packet size (65,535 bytes). Sending a ping of this size could crash the target computer. Generally, a large IP packet is split across multiple fragments. The recipient reassembles the packet and this can cause a buffer overflow if the memory allocated in the packet is not sufficient.
Volume Based Attacks
UDP Flood – Attackers flood random ports on a remote host causing the victim to repeatedly check for the application listening on that port, and (when no application is found) reply with an ICMP Destination Unreachable packet. For a large number of UDP packets, the victim will be forced into sending many ICMP packets, eventually leading it to be unreachable by other clients. The attackers may also spoof the IP address of the UDP packets, hijacking ICMP return packets elsewhere. The software UDP Unicorn can be used for performing UDP flooding attacks.
ICMP (Ping) Flood – The ICMP flood overwhelms the target resource with ICMP Echo Request (ping) packets. The attackers send huge quantities of packets without waiting for replies to saturate outgoing and incoming bandwidth. Since the victim's servers will often attempt to respond with ICMP Echo Reply packets, this results in a significant overall system slowdown.
Application Layer Attacks
Slowloris is a HTTP GET-based attack. A limited number of machines, or even a single machine, can disable a Web server by sending partial HTTP requests. Slowloris sends more HTTP headers, never completing a request. Once all sockets on a victim's server is taken up by requests sent, the Web server becomes inaccessible. Slowloris is used to attack hosts running Apache, dhttpd, Tomcat and GoAhead WebServer. Recently various versions of Slowloris module have been found in botnets. A version of the popular module has been also created as plug-in for SpyEye Malware.
DNS Amplification attack
In this first couple of months of 2012 we have assisted to an escalation of cyber-attacks made by groups of hacktivists, first Anonymous, that have hit main institutions and agencies all over the world. The modus operandi of the group is now well known, attacks that have crippled many victims were mainly of DDoS type, in this way the group has made many web sites inaccessible.
For a long time now, in the Internet has persistently circulated the news of a possible attack on a global scale that has as its goal to bring down the entire Internet's Domain Name System (DNS) called a "troll" by members of Anonymous. Until today much of the success of the operation made by the group is related to two main factors, the surprise effect and the critical mass of supporters engaged in the actions. This means that in addition to conventional tools for DDoS (e.g. LOIC) it's normal to expect the genesis of new methods of attack.
What would be an effective and attractive attack technique for the group of hacktivist?
A highly efficient method is known as DNS Amplification Attacks, although known for years, could be extremely damaging to the current structure of the internet. Let's examine it in detail.
The Domain Name System (DNS) is implemented through a treelike system of delegations. A recursive process is used to follow the chain of delegations, starting at the Root zone, and ending up at the domain name requested by the client. A recursive name server may need to contact multiple authoritative name servers to resolve a given name. In a secure scenario, a recursive name server should only accept queries from local, or authorized, clients but in reality, many recursive name servers accept DNS queries from any source. Unfortunately, some DNS implementations enable recursion by default, even when the name server is intended only to serve authoritative data. A name server that provides recursion to non-local users is dubbed "open resolver".
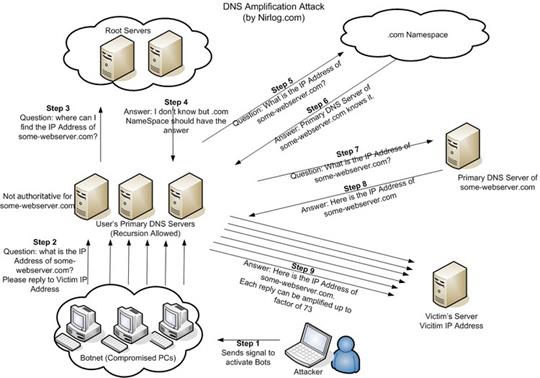
Figure 2 - DNS Amplification Attack
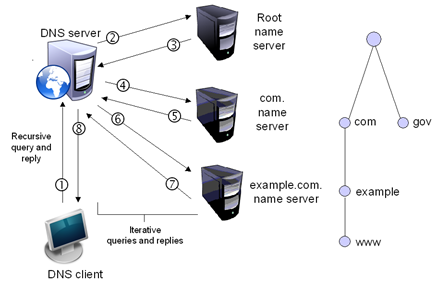
The DNS system has a hierarchical structure. At the top, there are the "root" nameservers containing information on where to find the nameservers responsible for the next level down in the hierarchy (e.g. ".com" and ".org" and ".uk"). In turn, those nameservers contain information about the next level of the hierarchy and so on.
If a user needs to resolve the name securityaffairs.co, his client sends the request to the DNS server. The root server will provide info regarding the ".co" and info regarding the next level in the structure "securityaffairs" domain. The "securityaffairs" nameserver is then able to provide the actual binding from the logical name and related IP address. Resuming a recursive process is used to follow the chain of delegations, starting at the Root zone, and ending up at the domain name requested by the client. A recursive name server may need to contact multiple authoritative name servers to resolve given name (e.g. www.net.compsci.googleplex.edu).
Figure 3 - Recursive name resolution
In an attack scenario, an ill-intentioned user could employ a Botnet to send spoofed address queries to an Open Resolver causing it to send responses to the spoofed-address target. In this way, the Resolver became the cyber gun against the victims for which we have spoofed the address. Operating on a DNS ROOT server this way is called "recursive mode." A client sends the request to the DNS server for the entire name then leaves it to perform all the necessary requests (either recursive or iterative) on its behalf.
There is also another mode to resolve a logical name called "interactive mode." In this case, the resolver first queries the root nameservers for the top-level domain's nameservers, then queries the top-level domain's nameservers for the second level domain's nameservers, and so on. The resolver contacts the different nameservers directly to make the complete translation.
The response to a DNS query can be considerably larger than the query itself. In the best (or worst) case, a query of just a few dozen bytes can ask for every name within a domain and receive hundreds or thousands of bytes in the response. Each request sent to a DNS server includes a source address to which the reply should be sent, but this IP address can be spoofed, in this way is, a request can be sent from one IP address, but the DNS server will think it was sent from a different address replying to it.
The attack method is really efficient if we consider that typically a DNS query consisting of a 60-byte request that can be answered with responses of over 4000 bytes, amplifying the response packet by a factor of 65. In literature, there are several variants of the attack. One of them includes a query only for the root name servers, the home of the Internet's root DNS servers. Because there are a large number of root name servers, and because the implementation of DNS-SEC has added certificate data to root server responses, the data returned for each request is about 20 times larger than the request packet.
The attack method is really powerful, in fact sending a small amount of data that composes a DNS request, it is possible to redirect large quantity of data to a spoofed address. So sending a large number of requests to the server it is possible to flood the victims with the replies. The different size between the dimension of the request and related response is called the "amplification" factor and the technique is known as the "DNS amplification attack."
Which are the main effects of this kind of attacks?
A DNS recursion attack is essentially an amplification DoS attack. There are several related effects like:
- DNS servers configured to provide recursion receive the spoofed requests and generate replies to the spoofed address (i.e., the victim). The performance of these systems may be negatively affected when processing the spoofed requests.
- The spoofed DNS requests query the root name servers, part of the internet's critical infrastructure, indirectly affecting them.
- The traffic then traverses the internet backbone, affecting the internet service provider and any upstream providers until it reaches the intended target.
- The intended target receives large amounts of inbound DNS replies that could consume all available resources on its route, depending on available bandwidth. Even if the traffic is reduced through rate limiting or other bandwidth throttling measures, the attack could affect other legitimate business along the path of the attack.
How to avoid this type of attacks?
- It's simple. It is enough to disable recursion as recommended by US-CERT bulletins, but as usual this setting for DNS is ignored. Given enough servers that enable recursion, large quantities of traffic can be produced from relatively modest numbers of queries. The Internet Engineering Task Force has proposed a best practice to solve the problem, an approach to "ingress filtering" of packets, called BCP 38, that would block forged traffic like DNS amplification attacks. But the proposal hasn't moved very far forward since it was first submitted in 2000. The best countermeasures against DNS amplification must be taken on server side do not return replies to "." queries and return shorter responses, reducing the amplification process. Another option is the limitation of DNS requests to authorized clients.
DDoS attacks … present threat
Recent events have demonstrated how much dangerous and destructive a DDoS attack could be. It represents one of the most feared offensive forms for its ability. To have a clear idea of its impact, let's analyze the data provided by principal security firms specialized in attack mitigation such as Prolexic and Arbor Networks.
A last quarterly report published by Prolexic related to Q1 2013 revealed that volume, duration and frequency of DDOS attacks have significantly increased during the first quarter of the current year. What is really concerning is the average attack bandwidth detected that was of 48.25 Gbps, eight times superior to the data related to the attacks during the last quarter of 2012 characterized by a bandwidth averaged at 5.9 Gbps.
The case that most of all shocked public opinion and security community is the DDoS attack that hit Spamhaus, a European anti-spam firm, which drafts and commercializes blacklists containing principal sources of email spam, the DDoS peaked at over 300Gbps becoming the largest in history according Prolexic.
Analyzing the data provided by Prolexic, we to note that 11% of attacks against a company's customers had an average bandwidth of more than 60Gbps and about 25% of DDoS has limited capabilities with a bandwidth of under 1Gbps, the figures confirm the increased capability of the attackers that demonstrated the ability to conduct large-scale attacks even more organized.
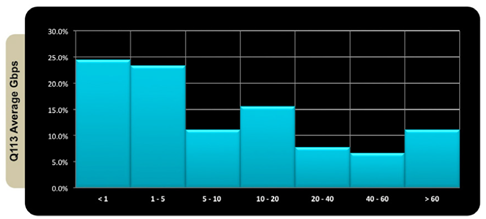
Figure 4 - Q1 2013 Average bandwidth
A first look at statistics provided by Prolexic reveals that DDOS attacks in Q1 2013 increased by 1.75 percent over the previous quarter of 2012 and by 21.75 percent over the same period of last year showing a concerning progression, more than a third of all attacks targeted the infrastructure layer.
"What defined this quarter was an increase in the targeting of Internet Service Provider (ISP) and carrier router infrastructures," Prolexic said.
The attackers are organizing the DDoS using large botnets. According principal security firms, these malicious infrastructures are increasing in number and dimension, giving to the opportunity to reach so scary results. Security experts revealed that attackers tend to adopt offensives that compromised servers instead of PCs.
Another factor highlighted by Prolexic is that also packet-per-second (pps) rate of attacks is increased reaching an average of 32.4 million pps during the first quarter of the year. This is fundamental if it is considered that a high packet-per-second rate can interfere with the routing operation affecting networking equipment of ISPs and DDOS mitigation providers.
The Prolexic reports states:
" Most mitigation equipment tends to be limited by pps capacity,not Gbps. But it's not just mitigation equipment that struggles against these high pps attacks. Even routers that carry traffic to the mitigation gear have trouble with packet rates at this level. As a result, we are entering a situation where simply moving such a large amount of attack traffic to a scrubbing center can be problematic. This has resulted in an increase in the null routing (black holing) of traffic by carriers and ISPs, which is obviously not a viable or acceptable long-term strategy for clients"
Analyzing top sources for DDoS attacks in Q1, China retains #1 position as the leading origin for the feared offensives, it accounted, in fact, for 40.68 percent of botnet sourced activities and was followed by the U.S. at 21.88 percent, Germany at 10.59 percent and, surprisingly, Iran with 5.51 percent.
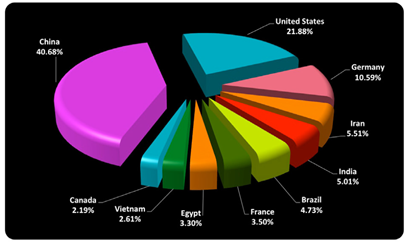
Figure 5 - Top source for DDoS attacks in Q1 2013 (Prolexic)
" Prolexic has seen a steady pattern of country sourced botnet traffic across many quarters. Iran though, has not been included in the top 10 source countries before. It is expected that countries with the largest network infrastructures would have more incidents of botnet infection, so the appearance of Iran at number four definitely stands out."
Cyber-criminals, and more in general attackers, try to benefit from countries having vast and extensive infrastructures, but also another factor influences the diffusion of botnet in this country such as the lack of proper response to cyber threats and the presence of a large number of machines not updated that host vulnerable applications. It's clear that in similar scenarios is quite simple to arrange a DDoS attack; malicious attackers could easily arrange a botnet "creating an ecosystem of DDoS-as-a-Service."
Another interesting overview of evolution of DDoS attacks during 2012 has been provided by Arbor Networks, a company which sells network security and network monitoring software, in the last annual report titled "Arbor Networks' eighth annual Worldwide Infrastructure Security Report" it also confirmed that application layer and multi-vector DDoS attacks are continuing to evolve.
Attackers have improved their tactics turning to sophisticated, long-lived, multi-vector attacks difficult to defend against and require layered defenses for successful mitigation.
Arbor reported that the largest attacks tracked by survey respondents appear to have decreased from their 2010 high of 100 Gbps, to 60 Gbps in both 2011 and 2012. However, average tracked attack sizes have continued to grow over the past 12 months as reported in the following pictures:
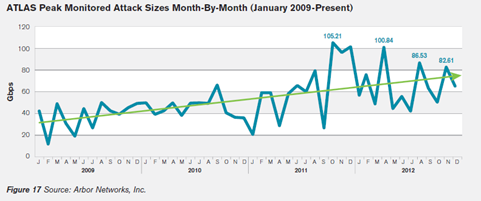
Figure 6 - Peak monitored Attack Sizes (Arbor Networks)
Early in 2013 Security firm Radware also published the 2012 Global Application and Security Report that confirmed the alarming data presented by Prolexic and Arbor. The Radware ERT observed hundreds of DoS/DDoS attacks each year and confirmed that 2012 attacks were characterized by an increased complexity.
The company developed the Advanced Persistent Threat (APT) Score, a scoring system that enables ranking APT attacks methodically by their severity. Each attack is assigned an APT score between 1 and 10 (10 being the most powerful), based on three factors:
- Attack duration – the longer the attack lasts, the higher its APT score.
- Number of attack vectors – a higher number of detected attack vectors increases the APT score. Attack vectors include the different attack methods used, such as HTTP attack, DNS flood, SSL garbage flood, etc.
- Attack complexity – the more complicated the attack vectors, the higher the APT score. For example, a SYN Flood gets a relatively low score; a slow rate attack gets a higher score; and an exotic attack that is rarely seen gets the highest score.
The following chart demonstrates the increased complexity of DoS and DDoS attacks observed by security experts at Radware.
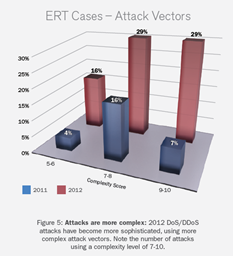
Figure 7 - Attacks complaxity 2012- Radware report
Interestingly, the evaluation proposed by Prolexics on the type of DDoS attacks detected in Q1 2013 the mainly hit network infrastructure, around 76% percent of the malicious traffic that was mitigated by Prolexic came in the form of Layer 3 and 4 protocols, whereas the remaining 24% percent were application attacks (Layer 7).
Data related to fall and winter of 2012 demonstrated a high activity in the underground market, attackers would target DDoS-as-a-Service websites that utilized booter scripts. The majority of the popular DDoS-as-a-Service websites would utilize the same public PHP scripts.
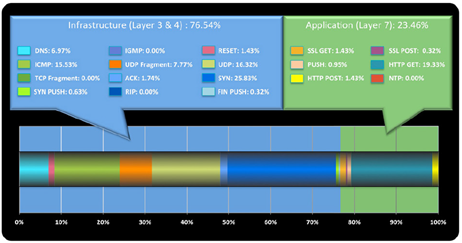
Figure 8 - Prolexic DDoS Type Q1 2013
As shown in the above graph Infrastructure attacks were mainly of SYN floods type (25.83 %) also due to the fact that many of botnets have SYN flooding capabilities. An increasingly popular method of sending UDP attack traffic has been through the use of booters, which are PHP scripts deployed on web servers.
Application DDoS attacks were monopolized by HTTP GET floods (19.33%) attributable to the fact that the majority of commercial and public DDoS kits make use of GET floods as their standard method of attack.
The phenomenon most interesting is the increase of over 200 percent for DNS Attacks respect Q1 2012 that impacted mainly large organization with huge infrastructures. One of the principal problems is the proliferation of improperly configured DNS servers exploited by attackers with well-known attack methods actually gained strength with the availability of fast and inexpensive bandwidth.
The majority of public DNS servers are owned and managed by Internet service providers (ISPs) or principal Internet companies such as Google. These entities usually support multiple data centers and often find it valuable to run their own public DNS. Execution of their own public DNS server allows enterprises to perform a set of adjustments such as set TTLs, flush updates, build multi-site, high-availability configurations and make other parameter tuning.
The side effect is that the configuration of the DNS could have security repercussions. It must be designed to be highly reliable and avoid that attackers could illegal use it for DDoS activities.
Dedicated botnets represent the primary cyber threat. A DDoS bots can request zone transfer files from thousands of DNS servers at once, using a source IP address of the site that intend to attack, in this scenario as explained before the misconfigured DNS servers then send the zone files back to the target network, often overwhelming the target's Internet bandwidth and knocking the site offline.
To have an idea of the number of vulnerable DNS servers, consider that the Open DNS Resolver Project claims that they have scoured the Internet and have identified over 25 million open DNS servers that "pose a significant threat."
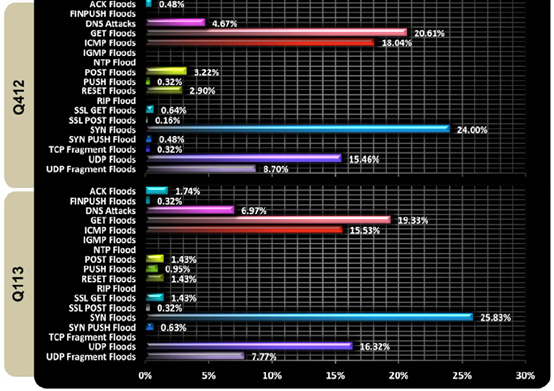
Figure 9 - DDoS type for Q113 and Q412 (Prolexic)
Introduction on DDoS mitigation
Detection of a DDoS attack is the most important phase for threat mitigation. Limiting the damage and containing the threat is essential. There are several methods to identify a DDoS and various security firms offer a wide set of network devices for the purpose.
Some network devices implement "reputation watch" sentinel that analyzes the traffic real time searching for anomalies based on known malicious pattern. These appliances detect the cyber threat and its origin in real time, scanning for malicious traffic generated by automated botnet, and trying to ban bad IP addresses "on-the-fly."
Many systems are able dynamically to provide an automatic changing in the network context to block incoming malicious traffic and also are able to apply discriminant on it based on the country of origin.
There are several appliances on the market used for DDoS mitigation, following a short list of systems using for DDoS detection:
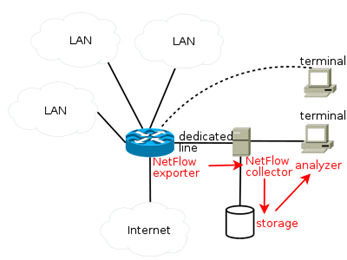
Figure 10 - NetFlow Architecture
NetFlow analyzers – The NetFlow protocol is a network protocol developed by Cisco Systems for collecting IP traffic information and it is recognized as a standard for traffic analysis. Network devices (e.g. Routers) that support NetFlow are able to collect IP traffic providing detailed statistics. The component that performs traffic analysis of the NetFlow architecture is named "collector" and usually is implemented by a server. Cisco standard NetFlow version 5 defines a flow as a unidirectional sequence of packets that all share of the following 7 values: Ingress interface (SNMP ifIndex), Source IP address, Destination IP address, IP protocol, Source port for UDP or TCP, Destination port for UDP or TCP, and IP Type of Service. Analyzing in automated way, the flow is able to detect in real time a DDoS event localizing the sources of attacks.
SNMP-based tools - SNMP-based tools are used to collect traffic from network devices such as switches or routers supporting SNMP protocol. These tools consist of two components, the collector used to collect SNMP data and the "Grapher" to generate HTML formatted output containing traffic-loading image that provides a live and visual representation of the network status and traffic trends. These traditional SNMP-based traffic-monitoring tools are really effective to detect traffic anomalies, such as an unexpected increase, that may indicate an ongoing attack. From a security perspective collected data sometimes might be either too coarse to detect anomaly and need further analysis.
Deep packet inspection - DPI devices perform deep packet filtering examining both the data part header of packets composing the traffic once they pass an inspection point. The DPIs are used for various purposes such as:
- Protocol non-compliance detection.
- Virus detection.
- Spam monitoring.
- Intrusions and attack detection.
A DPI configured in the proper mode would detect the DDoS packets and filter them out.
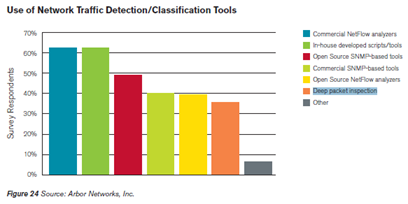
The following graph shows their engagement according the report provided last year by Arbor Networks, with classic Commercial Network Analyzers, as shown the number of open source systems used to mitigate the attacks is a marked increase.
Figure 11 - Network Traffic Detection - Arbor Networks
Detection has been just of phase of DDoS mitigation, once discovered an ongoing attack it is necessary to adopt a proper strategy and tools to mitigate its effects, and despite their functional and operational limitations, ACLs continue to be the most widely used tools according the principal security firms. Other possible methods to mitigate a DDoS attack are: Intelligent DDoS mitigation systems (IDMS), Destination-based remote triggered blackhole (D/RTBH) a filtering technique that provides the ability to drop undesirable traffic before it enters a protected network and Source-based remote triggered blackhole (S/RTBH) technique allows an ISP to stop malicious traffic on the basis of the source address it comes from and FlowSpec. The following graph is related to data published in the last reports of the Arbor Networks Firm:
Figure 12 - DDoS mitigation Tools (Arbor Networks)
The majority of organizations have implemented best current practices (BCPs) in critical network infrastructure security, such as the following:
- Authentication for BGP, IGPs
- Separate out-of-band (OOB) management network
- iACLs at network edges
- BCP38/BCP84 anti-spoofing at network edges
DDoS and underground … monetization of attacks
When the DDoS topic is introduced, it's immediately linked with the most popular tools available for these types of attacks, such as the popular LOIC. We must consider that the underground offers plenty of interesting software and services that could be acquired at reasonable prices.
Recent DDoS attacks have demonstrated the impact of these type of offensives on private corporations and institutions, too many entities are still vulnerable to Denial of Service attacks and cybercrime is trying to monetize it. The principal ways to monetize a DDoS attack observed are:
- Conduct DDoS for extortion purposes.
- Renting of DDoS services.
- Sale of DDoS bot agents for constitution of dedicated botnets.
New vendors daily propose malicious code, exactly like in every market exist well known vendors with an excellent reputation, meanwhile new actors try to conquer the black market with ingenious proposition on the black market.
Vendors sell products to facilitate the cybercrime activities and monetize their products in the shortest time to avoid to be tracked by security firms and law enforcement. Dancho Danchev, one of the greatest experts on research on the cyber-criminal underground has explored the black market several times for offers of tools and malware to arrange DDoS attacks.
At the end of last year he reported the offer of the DIY IRC-based DDoS bot, a malicious code that since its discovery has been continuously improved, the first version was in fact an IRC-based release, but the agent improved evolving into a HTTP-based one.
What surprised the security experts in the first phase was the fact that the agent used the Internet Relay Chat (IRC) as a centralized command and control infrastructure, another singular thing is that a malware author would not offer you access to a managed IRC server to be used as command and control server. In those cases, the author of this IRC-based bot appeared to be using a largely outdated and easily detected C&C communication process. The bot was very light, just 23kb that has standard anti-debugging mechanisms built-in, plus features allowing the update the code to a newer version.
It was easy to provide an improvement with regard to the communication channel with the C&C, an improvement that has come in timely with HTTP-based release.
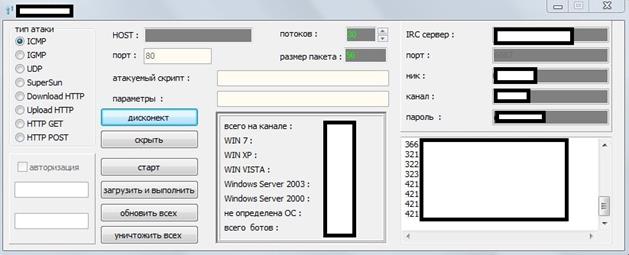
Figure 13 - DIY IRC-based DDoS bot
The malicious application appears very efficient, it supports 10 different DDoS attack types, but what is very singular is that the application once infected its victims is able to remove competing malware such ZeuS, Citadel, or SpyEye.

Figure 14 - DIY HTTP-based DDoS
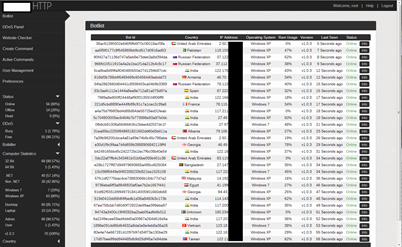
Figure 15 - DIY HTTP-based DDoS Admin Panel
The malicious code is also surprising for its price. According Danchev the IRC version is sold for $100 while the HTTP version goes for $300. As we has seen in the last months cyber-criminals are able to propose a completed offer proposing also bullet proof hosting and managed services IRC, respectively in this case for $15 and $10.
The case presented the demonstration of how it is simple to arrange a DDoS attack thanks to the cyber-criminal offer on the underground that includes all necessary to arrange a powerful offensive.
The offer is improved daily thanks to feedback of buyers, and represents lifeblood for the continuing attacks.
DDoS trends and forecasts … concerns related IPv6
As seen the statistics suggest a sensible increase in Application level attacks already discusses in previous paragraphs, other opportunities for attackers are offered by the introduction of IPv6 networks. According a recent survey published by the Arbor Networks firm, eighty percent of respondents have partial or full IPv6 deployments already in place with most using dual-stack as a migration mechanism. Security experts are convinced that DDoS attack could be strengthened around 90% in IPv6 when compared to the traditional IPv4 offensive. Technically IPv6 introduces six optional headers, such as the Routing header, that could be used to force a packet transit on through routers, making possible that the attack packets could transit between the routers endlessly suturing the network with forged packets and can lead to a powerful DDoS attack. IPv6 has also another powerful feature that could be exploited, the mobile IP that has been introduced in the last version of the protocol to allow a user to change his geographical location moving to different networks maintaining a single IP address. This is achieved by the extension headers provided in IPv6. The original IPv6 address is stored in the extension header whereas an additional temporary address is maintained in the IP header. The temporary address keeps changing when the user is mobile but the original IP address remains unchanged. An attacker can easily change this temporary IP address and carry out spoof attacks.
Conclusions
The motivation behind a DDoS attack could be varied. Hacktivism is most probable, but cybercrime is also interested in these offensive techniques for extortion.
Conducting a DDoS attack is not difficult today, The tools and infrastructures are available in the underground market, and small gangs and structured criminal organization are showing an increasing interest. Recent DDoS attacks provide an indication of the presence of more complex and complicated organizations that are organizing to attack targets such as banks, financial institutions, and private businesses.
In the past, we have discussed the dreaded RBN, the largest cyber-criminal organization ever. You have to wonder if something similar has not been operating for some time. It is possible that a new cyber-criminal organization is operating on a global scale with serious consequences.
DDoS attacks are largely adopted also for cyber warfare to hit the critical infrastructures of a foreign country, with this offensives state-sponsored hackers could be induced to hit the financial institutions of a nation causing popular unrest in the target country. The diffusion of botnets, and also the introduction of IPv6, represent a further factor that could amplify the magnitude of the cyber threats and the frequency of this type of attacks. DDoS attack is evolving, and both private and government sectors are menaced.
Underestimating the threat could be very dangerous!
References
http://ww.prolexic.com/e/9892/WI5QAX/ddb2w/209936146
http://ww.prolexic.com/e/9892/TVdz2G/ddb2y/209936146
http://blog.webroot.com/2013/05/03/new-irchttp-based-ddos-bot-wipes-out-competing-malware
http://www.arbornetworks.com/research/infrastructure-security-report
http://www.radware.com/Resources/rclp.aspx?campaign=1630844
http://www.cyberwarzone.com/your-dns-server-helping-ddos-attacks
https://www.owasp.org/images/4/43/Layer_7_DDOS.pdf
http://www.incapsula.com/ddos/ddos-attacks

FREE role-guided training plans