Cyber Security During The Holidays
Introduction
It's the holidays, a key time for cybercrime that exploits the bad habits of unaware internet users. Attackers can defraud and monetize their actions with little effort. During the Christmas holidays, more than other times of the year, a growing number of internet users make and plan their shopping online, through mobile and social networks.
IBM estimates an significant increase of purchases made on mobile devices that account for 16.5% of all online sales. Mobile traffic made up nearly 30% of online holiday shopping. The downside, in term of security is that cybercriminals will develop more malicious apps, or will intensify phishing campaigns over mobile and social networking platforms.

FREE role-guided training plans
A growing number of services for online shopping are offered on those platforms and IBM anticipates a significant increase of cybercrime, mainly related to computer scams and identity theft.
Researchers at Tenable, a Columbia, Maryland company that provides security solutions for online networks, confirm that more than any other time of the year, cybercriminals try to take advantage of the holidays to target online shoppers vulnerabilities. It has been estimated that there will be about $5.4 billion in losses during this period of the year resulting from stolen credit and payment card information.
According to an annual survey conducted by Deloitte Consulting in New York, more people than ever are planning to buy their Christmas presents online this year. US consumers will spend $61.8 billion on e-commerce in November and December, registering an increment respective of the previous year of 15%. Online shopping is very attractive to people. It's very easy and convenient, especially during the holidays, thanks to special offers on all kinds of products.
Big box retailers are prepared for the wave of online shoppers. In the majority of cases, they have redesigned their mobile sites, launched new apps, and are offering some consumers customized shopping experiences on social networks and mobile platforms.
IBM Digital Analytics stated that its real-time tracking recorded a 17.5% increase in online sales compared with last year. Retailers aren't the only ones that benefit from an increase in online shopping. Cybercriminals consider the holidays to be a profitable period to concentrate their activities. It's essential for internet users to consider the risks related to online shopping and avoid behaviors that could expose them to fraud.
Online stores and retailers are able to mitigate cyber threats, to guarantee safe shopping and promptly react to any possible incident.
1. Pitfalls during the holidays
During the holidays there are environmental circumstances that could further expose Internet users to the menace of cybercrime.
-
Be aware of holiday phishing, especially on mobile devices. During that period, the number of malicious emails that serve malware as an attachment or that contain a links to compromised websites increases. Mobile platforms and social media are becoming a privileged channel to spread phishing messages. Phishing messages propose special offers, taking advantage of the holiday period that's characterized by a spike of online shopping. As usual, cyber criminals attack customers of banks and other financial institutions by asking victims to confirm information related to their account for security purposes. SMiShing, a variant of phishing that exploits Short Message Service (SMS) systems instead of email to send malicious messages, is a growing threat as well.
Smishing messages direct victims to visit a website or call a phone number, at which point the person being scammed is enticed to provide sensitive information, such as credit card details or banking credentials. Malicious shipping notifications belong to this category of scam. Cybercriminals use it to send out fake messages to update customers on the status of their shipments. Usually, these messages include a malicious link or carry malware. During the holidays, internet users place numerous orders online, and the likelihood that they wait for shipping notifications is high. That's why this scheme of attack is very efficient, especially during the holidays.
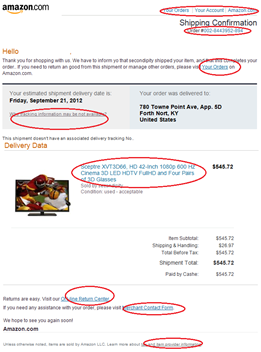
Figure - Fake notification message
-
Holidays are party time. Private events or company holiday parties are very common during this period. The Wall Street Journal estimates 9 out of 10 companies will throw some kind of holiday party this year, inviting personnel and participants via email, and requesting to complete a form to confirm their participation. Spoofed invitations present another great holiday-themed attack opportunity for cybercriminals to craft phishing emails.
-
Wi-Fi hotspots are dangerous hunting grounds for hackers. Users aren't aware of the risks they are exposed to once they're connected to insecure networks. The last Norton 2013 report highlighted potentially risky behavior on insecure Wi-Fi. The majority of users access their social network accounts (56%) and personal email (54%), and around 29% access their bank accounts, while many make online purchases (29%). That data gives an idea of the exposure users have on insecure Wi-Fi, but what's really worrying is that more than a third of them don't adopt any defensive measures, and incur bad habits during navigation (e.g. sharing passwords, not logging off after having used a public WI-FI connection.) Almost every Wi-Fi hotspot is insecure. Doing online shopping on them can lead to exposing user accounts to identity thieves and scams. Be aware, antivirus and similar software won't protect you on an open network, hackers are over your shoulders.
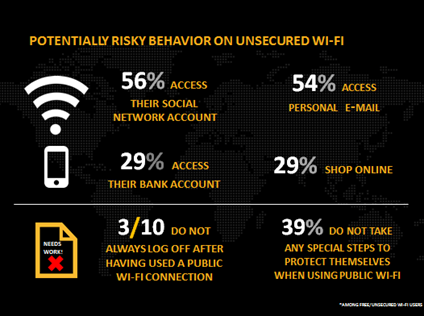
Figure - Norton Report 2013 WiFi Unsecure Use
-
Password hacking is a very common practice. Cybercriminals use different techniques to try to steal account passwords from users. Social engineering, phishing and brute force attacks are very popular, especially during the holidays. Users usually adopt weak passwords, and unfortunately, in many cases they don't protect services and devices with secret codes. The problem is especially serious on mobile devices. Users don't use a PIN to protect them, and in the majority of cases they use simple passwords due the difficulty of memorizing them, or typing them on the software keyboard offered by the mobile OS. According a 2013 survey conducted by McAfee, 36% of smartphone users don't use passwords to protect devices from unauthorized access.
-
Christmas party scams lead to identity theft and money losses. The holidays are a period in which is quite easy to find any kind of offer, especially through social networks. Often fake offers for gadgets such as iPhones, iPads and SmartTVs attract victims through fraudulent websites. Scammers exploit holiday shopping frenzies to spread bogus offers on attractive products thought spam campaigns via mail or through social networks. These deals spread malicious links to compromised websites that serve malware, or could contain malicious attachments. Security firm Bitdefender Labs observed an increasing number of fraudulent websites such as fake hotels and fake banks, reproducing legitimate emails to lure visitors during the holidays.

Figure - Christmas fake offer
-
Malicious holiday apps are software specifically designed for holiday shopping. They generally include features to steal victim's credentials and data, or to take complete control of a user's handset, causing incoming calls and messages to redirect, or to call premium numbers. A survey by the National Retail Federation states that over half of smartphone owners and six out of ten tablet owners plan to use their devices for holiday shopping. That's a great opportunity for cybercriminals offered by this period of the year. "Many consumers use more than 10 apps on their devices during a typical week, a lot of which keeps them logged into their accounts – including email, text, banking, and social media – for long periods of time. Software from online app stores used for holiday shopping may look legit. It may even have company endorsements. But it could be carrying malware designed to steal your personal data and make charges to your accounts. " More sophisticated malicious apps are used for banking fraud and are able to by-pass two factor authentication mechanisms.
-
Numerous websites offer full-version downloads of popular games or holiday-themed games. In reality, these applications serve malware. This type of scam could hit mobile users as well as desktop systems. Many sites offering full-version downloads of Grand Theft Auto or the popular apps like Angry Birds, are trojanized with tools commonly available on the underground market.
-
Fake charities are another weapon in the arsenal of cybercriminals. During the holidays, people are willing to donate more than at any other time of year, and cybercriminals take advantage of victims' generosity. The scammers set up bogus charity sites to receive donations. In some cases, cybercriminals replicate legitimate charity sites to steal credentials and other personal information from users.
-
Electronic greeting cards and romance scams are other cyber threats that become serious during holidays. E-cards that look legitimate could be used by attackers to serve malware or malicious links to compromised websites. Smartphone, tablets and PCs are devices exposed to that type of attack. In romance scams, the hackers can use photos, emails and even text messages pretend to be a member of a dating website.
2. Stay safe online
Law enforcement and numerous organizations are sending alerts to internet users, warning them about cyber threats that are particularly serious during the holidays. The US nonprofit consumer watchdog organization Consumer Reports have recently warned about online purchases regarding Cyber Monday sales, and more about special offers and discounts for the holiday season.
Bad habits, absence of defense mechanisms, and a lack of awareness of major cyber threats expose users to the risks of fraud.
The following are a few suggestions to help to increase the level of security of users' online experiences, especially during holiday shopping.
- Manage your passwords with care. Never share them, and adopt strong secret codes. Never use easily guessed words in your password. Use strong passwords, including a mixture of numbers, numbers, and special characters. It's a good habit to use different passwords for multiple web services. That assures that a cybercriminal who breaks into one account can't gain access to all your other online accounts.
- Use different email addresses for any shopping sites to limit likelihood of seeing all accounts compromised in the case of a data breach of one of your online retailers.
- Verify the online reputation of the e-commerce sites you access.
- Avoid online shopping on insecure wireless networks such as free Wi-Fi hotspots.
- Conduct online shopping on secured networks, even if you are on your domestic network, making sure your Wi-Fi is properly protected.
- Don't click on suspicious links. Never open unknown files or download items from unknown sources. That behavior is essential for unsolicited mails that propose special deals.
- Be careful to lookat the URL of sites you visit to avoid to visiting a copy of legitimate websites managed by criminals. Variations in spelling or a different domain (for example, the malicious site may use .net instead of .com) could deceive you. Pay attention to the protocol used by your retailers. Look in the address box for https:// before providing any personal or credit card information.
- It's a good habit to keep track of all your online orders.
- Periodically visit your banking accounts, verifying the list of transactions, and check the account balance.
- Don't download apps for your mobile device from unknown sources. Always use official app stores like the Apple App Store, Google Play and the Amazon App Store. Malicious apps could serve malware, and could be used by cybercriminals to steal sensitive information, bank accounts, and interfere with your holiday shopping. Be careful of "permissions" granted to any application you run on your device, any application must have only necessary permissions. Always check the reputation of the app, looking for the feedback in the comments section of official stores.
- If possible, make purchases with a credit card instead of a debit card. Using a credit card allows you to dispute any fraudulent charges.
- Use a secure device for your online shopping. Be sure that the software you use (e.g. browsers, mobile apps) and the OS are up to date. Install antimalware solutions on PCs and mobile devices, and check if they're running correctly.
Conclusions
At the time of writing, ENISA has published its annual Threat Landscape Report that confirms web based attacks are predominant in respect of other cyber threats. Cybercriminals use malicious URLs as the primary vector to serve malware, meanwhile Java is the most exploited application.
" It has been observed that there is a shift from Botnets to URLs as means of malware distribution. Java remains the most exploited software, to infect a web site. In addition, attackers use code injection attacks to create malicious URLs."
In 2013, malware diffusion was very high. Malicious codes was mainly derived from previous versions, thanks to the use of toolkits for their customization.
Obviously, the holidays represent an important opportunity for cybercriminals to serve the above cyber threats. This period in particular is ideal to deceive users with special offers and serve malicious code.
To reduce exposure to the above threats, follow the above suggestions and either way, report fraud immediately to law enforcement. The fight against cybercrime is challenging, and sharing knowledge about cyber threats and incidents is essential to recognize menaces.
References
http://www.privatewifi.com/hacked-for-the-holidays-how-shopping-online-leads-to-cybercrime/
http://www.net-security.org/malware_news.php?id=2641
http://www.net-security.org/secworld.php?id=16031
http://www.bbc.co.uk/news/technology-25200338
http://www.symantec.com/about/news/resources/press_kits/detail.jsp?pkid=norton-report-2013
http://www.emc.com/collateral/analyst-reports/h12493-ar-2013-ecommerce-cyber-crime-report.pdf
http://www.sacbee.com/2013/12/02/5961590/cyber-monday-shoppers-avoid-getting.html
http://www.net-security.org/secworld.php?id=16075&#
https://www.dhs.gov/blog/2013/11/29/stay-safe-while-shopping-online-cyber-monday
http://www.privatewifi.com/hacked-for-the-holidays-how-shopping-online-leads-to-cybercrime/
http://www.networkworld.com/news/2013/120313-eight-tips-for-more-secure-276531.html
http://robertsiciliano.com/blog/2013/11/28/7-tips-to-a-secure-mobile-device/

FREE role-guided training plans
http://robertsiciliano.com/blog/2013/11/27/cyber-monday-launches-black-hat-shopping-season/




