Anonymizing Activities in the Digital World using TOR
Introduction
When it comes to anonymizing activities in digital world, it can be referred to in various ways. Researchers might take it to identify various malicious activities and for back trailing, whereas hackers can anonymize their activities so as to build up a cover around their malicious activities. These anonymizing activities can really increase the work of researchers, as they can't trust the attributes mentioned in the logs like IP address, user agent, etc. as such attributes will only give you false information.
In this article series, we will learn about anonymizing activities from very basic level to an advanced level.

FREE role-guided training plans
Anonymity with TOR
The Onion Router, widely known as TOR, is famous for staying anonymous on the Internet. Tor is a network of computers around the world that forward requests in an encrypted manner from the start of the request until it reaches the last machine in the network, which is known as an exit node.
From the last node the TOR network, the request is decrypted and sent to the destination server. Thus exit nodes are the first nodes and last nodes in the TOR network for receiving and sending traffic from and to the original and destination server. Thus, to the destination server all traffic seems to come from the exit node in the TOR network, thus hiding the IP address of the original sender. Even the other systems in the TOR network cannot determine location either, because they are essentially forwarding traffic with no knowledge of where it actually originated. The responses to original requests will return to the system, but as far as the TOR network is concerned, a request is just another hop along the way.
SOCKS server
TOR works with the SOCKS protocol, so it is worth talking about SOCKS. A SOCKS server establishes a proxy TCP connection with another server on behalf of the client and then routes all the traffic back and forth between the client and the server. It works for any kind of network protocol on any port. SOCKS Version 5 adds additional support for security and UDP. The SOCKS server does not interpret the network traffic between client and server in any way, and is often used because clients are behind a firewall and are not permitted to establish TCP connections to servers outside the firewall unless they do it through the SOCKS server. Most web browsers for example can be configured to talk to a web server via a SOCKS server.
Because the client must first make a connection to the SOCKS server and communicate which host it wants to connect to, the client must be "SOCKS enabled". SOCKS uses a handshake protocol to inform the proxy software about the connection that the client is trying to make, and then acts as transparently as possible, whereas a regular proxy may interpret and rewrite headers.
Comparison of SOCKS and HTTP
As can be inferred from the above text about SOCKS, its function is similar to that of HTTP. But there is a significant difference between SOCKS and HTTP, as SOCKS operates at one level lower than HTTP proxying. HTTP allows forwarding TCP connections, whereas SOCKS can also forward UDP traffic and work in reverse. Let's understand the difference with an example:
- SOCKS: Suppose User 'A' wants to connect with User 'B' over the Internet, but a firewall between them is restricting users to connect with each other. User 'A' connects to a SOCKS proxy in his network, which opens a connection through the firewall, and a communication channel between User 'A' and 'B' is achieved.
- HTTP: Suppose User 'A' wants to download a web page from web server 'B', but because of presence of a firewall between them, User 'A' is not able to do so, so User 'A' connects to an HTTP proxy, and in turn A's browser communicates with the proxy in exactly the same way that it would directly with B's server if that was possible, meaning it sends a standard HTTP request header. The HTTP proxy connects to B's server, and then transmits back to 'A' any data that B's server returns.
TOR hidden services
TOR is also being used to hide websites and other servers. This works by using what is called an associated onion address rather the website's original IP address. This model is more secure than the original TOR model traffic, since hidden services do not use exit nodes. Communication is encrypted end to end. Below are some of the TOR hidden services.
TOR weaknesses
Although TOR is a strong way to anonymize activities in digital world, the TOR network has some weakness too. Below are some of the weakness that the TOR network has:
- The TOR network is subject to eavesdropping attack. Since the TOR model involves exit nodes and traffic from exit node to destination node is not encrypted, eavesdropping attacks are possible. One possible solution to this is to always access the HTTPS version of service.
- TOR exit node block: Some of the websites block traffic if the last node is a TOR node, thus reducing the functionalities for TOR users.
- TOR is also vulnerable to traffic analysis attack, correlation attack, sniper attack, etc.
TOR configuration
TOR can be easily installed in the system and after connecting with the TOR network, user can anonymize his activities. Consider the following commands to use in Ubuntu.
- Install TOR as root: apt-get install tor
- Check for IP address of the system without TOR
- Install TOR bundle from TOR website
- Extract the content and run the .exe
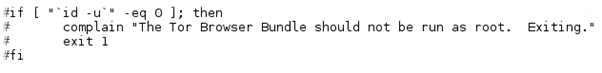
- If you are running as root, then the system might display an error by saying that "TOR cannot be run as root". To overcome this, open the file in a text editor and comment the following lines:
- After this start, the TOR bundle .exe and notice the IP address. The IP address should not be the same as your machine's IP.
So in this article, we have learnt about what is TOR, how it is different from HTTP, and how easy it is to install and configure TOR in a machine. In the next article, we will learn about some more ways of anonymizing.





